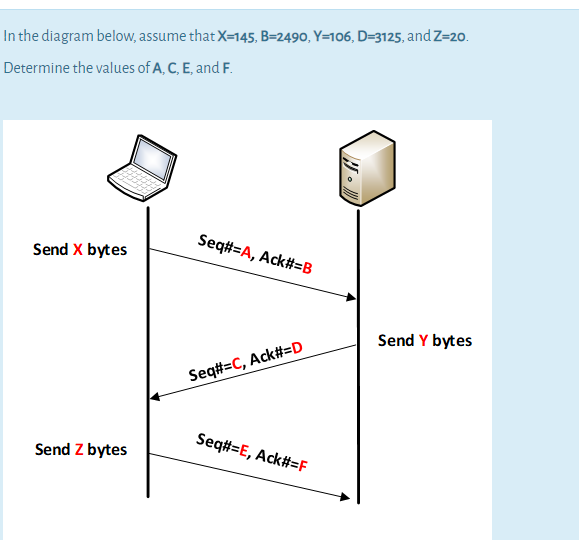
In the diagram below, assume that X-145, B=2490, Y=106, D=3125, and Z=20. Determine the values of A, C, E, and F. Seq#=A, Ack#=B Send X bytes Send Y bytes Seq#=C, Ack#=D Seq#=E, Ack#=F Send Z bytes
Q: An IP address is also represented by this format: 192.168.10.0/24. What do you call the /24? O a.…
A: ANSWER IS C network address A network address is any logical or physical address that uniquely…
Q: b) The distance between a sender and a receiver of a data communication system is 1400 km and the…
A: Go-Back-N ARQ is a specific instance of the automatic repeat request protocol in which the sending…
Q: 3. The following character encoding is used in a data link protocol: A: 01000111; B: 11100011; FLAG:…
A: The transmitted for four-character frame is given below: A B ESC FLAG (01000111 11100011 11100000…
Q: a digital communication system with the following specifications: Pbe=0.05, (n,k) block coding with…
A: It is defined as a element of a standardized code or protocol. Each code word is assembled in…
Q: A wireless LAN uses polling to provide communications between 10 stations and a central base…
A: Answer :- (e) 39.96 Mbps
Q: Suppose the sender and the receiver agree to use the bit pattern 01111110 to mark the beginning and…
A: The process of putting extra bits to data frame is call bit stuffing. Here we simply put some extra…
Q: 3. (b) A sender needs to send the four data items Ox1236, OXABCC, OX03BC, and OXEEEE. To avoid…
A: Four data items are: 0x1236 0xABCC 0x03BC 0xEEEE 0x is the prefix that is used to denote the data…
Q: 2. , A string encoded with H(12,8) SECDED is received as 0x500 Is it in error? Which bits are in…
A:
Q: Consider the following: the latency of an interconnect is 2 seconds, and the bandwidth is 64 bytes…
A: transmission time = Latency + (packet length)/(bandwidth)
Q: Cyclic Redundancy Check (CRC) is used to detect errors in longer messages. Suppose you want to…
A: We are going to find out value of T(x) which will be sent, we are given message as M(x)=10111010 and…
Q: The technique of temporarily delaying outgoing acknowledgements so that they can be hooked onto the…
A: - Question provided here wants to know which technique of temporarily delaying outgoing attachment…
Q: a. Suppose you have the following packet with the bits: 01111001 11001111 and 11110011 10011000.…
A: a) Given packet with bits are : 01111001 11001111 and 11110011 10011000 Checksum is calculate…
Q: Consider the PPP byte stuffing method. What are the contents of the following received sequence of…
A: PPP is a character oriented version of HDLC Flag is 0x7E (01111110) Control Escape 0x7D…
Q: Suppose the sender wants to send the following bit stream by using bit stuffing. What would the…
A:
Q: A sender needs to send the four data items 0x1236, 0xABCC, 0x03BC, and 0xEEEE. To avoid confusion,…
A: a) Given four information things are 0x1236, 0xABCC, 0x03BC, and 0xEEEE Allow us to work out the…
Q: 3.(a) What is minimum hamming distance? Why are redundant bits added by the sender? Name two error…
A: Given: What is the shortest hammering distance? Why does the sender include superfluous bits? Name…
Q: Q3) If the polynomial X3 +1 is used to generate the CRC FCS for the message x6+x4+x3+1. Use the…
A: FCS (Frame Check Sequence) is an error-detecting code that is being added to the frame in a…
Q: How may the interval between bytes be different in asynchronous transmissions?
A: Introduction: The time between bytes is "changeable" in Transmission because of its asynchronous…
Q: Q6 (a) Suppose we want to transmit the message 1011 0010 0100 1011 and protect it from errors using…
A: Note:- As per our guidelines we can solve one question. CRC is cyclic redundancy code which is used…
Q: 6. If CS= 1A2FH and IP= CB3AH, show: and Calculate: The logical address, The offset address, The…
A: Option A and D are correct answer Sice both are same
Q: A messaging system reads message as 4-digit positive integer d1d2d3d4 and stores encoding of the…
A: Algorithm: Start READ n Set i=4, j=0 and e=0 Compute: rem=n%10; Compute: e=e+(rem+i)%3 *…
Q: In a communication system, all message signals and their frequency values are given in the table…
A: Huffman Coding Huffman coding provides codes to characters where length is proportional to the…
Q: Compute CBC-MAC for a message of 16 bits, “8642” (in Hexa). Assume a block size of 8 bits with an…
A:
Q: ation D are router R. received by 200 bytes S.C.
A:
Q: Q2) A DMS sends a message with alphabet size equal to 6 symbols at 100 symbols/secs. Symbol k is…
A: According to the information given:- We have to calculate the information rate and the transmission…
Q: The following character encoding is used in a data link protocol: A: 01000111; B: 11100011; FLAG:…
A: a) Character count: - 00000101 01000111 11100011 11100000 01111110 b) Flag bytes with byte stuffing:…
Q: MCQ 2712: The technique of temporarily delaying outgoing acknowledgements so that they can be hooked…
A: the answer is given below:-
Q: A bit string, 0111101111101111110, needs to be transmitted at the data link layer. What is the…
A: Actually, Bit stuffing is the insertion of non information bits into data
Q: 4) Suppose we have to transmit a list of five 4 bit numbers that we need to send to a destination.…
A:
Q: 4. Suppose we have to transmit a list of five 4 bit numbers that we need to send to a destination.…
A: Each 1 or 0 in a binary number is called a bit. A group of 4 bits is called a nibble
Q: XYC.A7. The telephone. line has 4 KHz bandwidth. What is the maximum number of bits, we can send…
A: yor question is . the telephone line hase 4khz bandwidth then what is the maximum number of bits. we…
Q: val between bytes be different in asynchronous transmission
A: the solution is an given below :
Q: What is/are the advantages and disadvantages of adding more redundancy bit in a message?
A: Advantages By adding redundancy bit decreases the bit error rate. Requirements of the backchannel…
Q: Time it takes a message to travel from one end of a network to the other Select one: a. Jitter b.…
A: Here have to determine correct option about time for message to travel one end to other end of…
Q: Suppose you have the following packet with the bits: 01111001 11001111 and 11110011 10011000. What…
A: According to the Question below the solution: As per our guidelines we are supposed to answer only…
Q: he following questions are true or false, and you should explain your answer to them in a few words:…
A: Ans:- True First, we will see what is SR Protocol? SR Protocol is a selective repetition technique…
Q: Suppose computer A is sending a message to computer B. The datalink layer is using a sequence number…
A: As No of bits required for sequence number are 3 So possible Sequence number are: 000, 001, 010,…
Q: A 3400-byte datagram needs to cross a network with an MTU of 800 bytes. i. How many fragments are…
A: Given: 3400-byte datagram needs to cross a network with an MTU of 800 bytes. So, how many…
Q: A sender needs to send the four data items 0x1236, 0xABCC, 0x03BC, and 0xEEEE. To avoid confusion,…
A: i. Checksum at sender side:- Step 1:- Add all the given data segments:- 0x3456 + 0xABCC + 0x02BC,+…
Q: bandwidth if the input message has the following frequencies (5 kHz, * ?4.5 kHz and 3.9 kHz) 605 O…
A: 600
Q: 5.c How many bytes would it take to store original message? How many bytes does it take to store the…
A:
Q: 18. If the broadcast address is 172.16.9.255, then the corresponding network address may be ( )? O A…
A: If the broadcast address is 172.16.9.255, then the corresponding network address may be ( )? A.…
Q: Assume the following parameters for Go-Back-N (GBN): a) N = 5 b) Round Trip Time (RTT) = 10…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: For each of the following sets of codewords, please give the appropriate (n,k,d) designation where n…
A: First of all one must know what the codeword is , it is an element of the standardized code or the…
Q: Given AL=85(H), AH=00(H), BL=35(H), CS=0100(H), SP=0102(H), show and explain execution results of…
A: Following is the explanation of the above instructions: 1. ADC AX BX ADC means add with carry , ADC…
Q: In asynchronous transmission, the gap time between bytes is _______.
A:
Q: Suppose you are designing a sliding window protocol for a 1-Mbps point-to-point link to a stationary…
A:
Step by step
Solved in 2 steps

- Extend Example 7-36 to write (store) the string below of 28 characters into EEPROM locations starting at address 0x003F. Write one character at a time.MSG[ ] = “All the best for your Final Exam!”// Task 3 // For this function, you must return the largest power of 2 that // is less than or equal to x (which will be positive). You may // not use multiplication or some sort of power function to do this, // and should instead rely on bitwise operations and the underlying // binary representation of x. If x is 0, then you should return 0. unsigned largest_po2_le(unsigned x) { return x; }PLEASE EXPLAIN THE PROBLEM BEOW AND THE ANSWER Given the following structs, how many bytes would a single A take up? Answer in decimal only. struct A { char* str1; char ch; int* i, j; B a, b, c; }; struct B { A* a; }; Answer =
- Write a program that asks the user to enter and integer number and read it. Then ask him to enter a bit position (between 0 and 31) and display the value of that bit. srlv $s1,$s2,$s3 s2 = 3210 = 0000 0000 0000 1000 0000 0000 010 00002 s3 = 18 Bit = 10 1 = 00000000000000000000000000010000 2 = 00000000000000000000000000001000 3 = 00000000000000000000000000000100 4 = 00000000000000000000000000000010 5 = 00000000000000000000000000000001 S1 = 00000000000000000000000000000001 1 = 00000000000000000000000000000001 $t0 = 00000000000000000000000000000001 = x.1 = x AND $t0,$s1,1Convert the given text below to Asynchronous Data Form. Assume each character has odd parity. There will be 1 start bit and 2 stop bits, the start bit is represented by 0 and stop bit is represented by 1. Convert this message “BSCpE” to ADF. Do not forget to write the idle in the beginning of ADF.In this assignment you will practice using bitwise operators as well as binary, decimal, and hexadecimal representations. Given the following numbers: A = 0110 1100 B = 1100 0011 C = 1111 0000 D = 0000 1111 1.1 Questions Write the result of the following expressions in a plain text le. Write the answer in binary, hexadecimal, and decimal (unsigned integer). 1. A & B 2. A | B 3. A ^ B 4. A & C 5. A | C 6. A ^ C 7. A & D 8. A | D 9. A ^ D 10. B & C 11. B | C 12. B ^ C 13. C & D 14. C | D 15. C ^ D
- add x5, x5, x8Every binary digit must be either 0 or 1 or X. If it appears in multiple bits, then you must input multiple bits, e.g.: 0011xx11Control Signal: Value7 Show the locations of the following data in the data segment, and the data. (ASCII of 'H' = 68h, 'e' = 65h, 'I' = 6Ch, 'o' = 6Fh ) NUMBERS DB 12h, 27h, 33h NUMERS2 DW 12h, 25h, 44h ORG 10H MESSAGE DB 'Hello' ORG 25H MEDIAN DB 72 For example DS:0000 12Transform the pseudocode below into C++ codes. BEGININPUT rateINPUT hoursGrossPayrate x hoursDeductionGrossPay x 0.05NetPayGrossPay – DeductionEND
- 1. Suppose (27.625 base 10) is represented using IEEE754 Single Precision Floating Point Format. What is the Mantissa? 2. Suppose (27.625 base 10) is represented using IEEE754 Single Precision Floating Point Format. What is the exponent? Choices: 110111011101110110111010000000000000000110111010000000000000000100000110111011000000000000000000Write a program that asks the user to enter and integer number and read it. Then ask him to enter a bit position (between 0 and 31) and display the value of that bit.(MIPS) srlv $s1,$s2,$s3 s2 = 3210 = 0000 0000 0000 1000 0000 0000 010 00002 s3 = 18 Bit = 10 1 = 00000000000000000000000000010000 2 = 00000000000000000000000000001000 3 = 00000000000000000000000000000100 4 = 00000000000000000000000000000010 5 = 00000000000000000000000000000001 S1 = 00000000000000000000000000000001 1 = 00000000000000000000000000000001 $t0 = 00000000000000000000000000000001 = x.1 = x AND $t0,$s1,1a) Assume 185 and 122 are unsigned 8-bit decimal integers. Calculate 185 – 122. Is there overflow, underflow, or neither? b) Assume 185 and 122 are signed 8-bit decimal integers stored in signmagnitude format. Calculate 185 + 122. Is there overflow, underflow, or neither? c) Assume 185 and 122 are signed 8-bit decimal integers stored in signmagnitude format. Calculate 185 - 122. Is there overflow, underflow, or neither?

