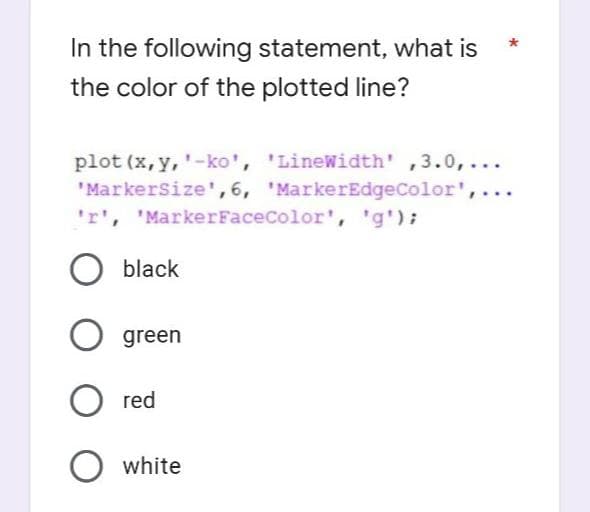
In the following statement, what is the color of the plotted line?
Q: What are the advantages and disadvantages of using the internet as a storage medium? Is using the…
A: Computing in the cloud: The Internet, often known as "the cloud," is responsible for distributing…
Q: Develop your knowledge not just of social media blogging but also of cloud computing and other…
A: Introduction: Learn more about blogging on social media, cloud computing, and related topics.
Q: A simple network could make use of either static or dynamic routing. The issue that has to be…
A: Using both static and dynamic routing: Using either static or dynamic routing may provide the…
Q: What do data scientists really do? Are there certain educational requirements for data scientists?
A: Given: Can you describe what precisely a data scientist does for a living? What kinds of degrees…
Q: Rational Unified and Classical Waterfall models are compared to determine which is superior.
A: - We have to talk about which model is better in comparing the waterfall model with rational unified…
Q: What opportunities, if any, does having access to the internet provide to those with various kinds…
A: Obtaining Access to the Internet: Because to the internet, the lives of those who are blind or have…
Q: The answer seem to be like copied from some other place.
A: The Web 2.0 refers to the second generation of internet services, which focused on the enabling the…
Q: Write a program to set zero in the lower triangular of a given matrix a(4,4). For example array…
A: We have to print zero in the lower triangular of given matrix a(4,4): given nested for loops to…
Q: It's critical to think about data backup and recovery from a variety of perspectives.
A: the capacity to use various retention rules, exclude material, utilise various storages, create…
Q: Byte is equal to ..............Bit 12 6 4 128 8 O O O
A: Byte is a unit of information storage
Q: Reading blogs is an excellent way to educate yourself on topics such as cloud computing, social…
A: In the branch of computer science known as peer-to-peer social cloud computing, computing resources…
Q: Write a program to merge two arrays of 8 elements for each sorted in descending order. For i = 1 To…
A: The question is to choose the correct option for the given question.
Q: A simple network could make use of either static or dynamic routing. The issue that has to be…
A: Static and dynamic routing: While routes in dynamic routing are changed automatically, those in…
Q: Educate us on the meaning of a challenge-and-response authentication mechanism, if you please…
A: Given: Challenge-response authentication is a group of protocols used in the field of computer…
Q: O O 1-If I = J Then 2-H(I, J) = (1 + J-1) 3- Elseif 4-H(I, J) = 1 5-End If 6-Next J, I 1-If I = J…
A: If else loop is used to check one condition if expression is true then true statement block will…
Q: a java program - A Libary book rental syst
A: Program Approach: 1- As mentioned in the assignment library rental book system, created a…
Q: Get familiar with cloud computing as well as blogs that deal with social networking.
A: Definition: Applications, servers (both physical and virtual), data storage, development tools,…
Q: its not calculating and plase remove the console output
A: In this question we have to write a JavaScript function to calculate BMI value where the function…
Q: Is cloud security compromised by a data breach? The following are a few possible responses to this…
A: Data breach: Information theft, ransomware, phishing, password guessing, viruses, malware,…
Q: Discuss briefly any four user-initiated actions that can be performed using a graphical user…
A: Introduction: GUI is an abbreviation for Graphical User Interface. It is the interface in which…
Q: How likely do you think it is that a data breach will have an influence on cloud security in the…
A: Given: Each succeeding organization is aware of common data security threats and confident in its…
Q: pes the phrase "scalability" have any relevance whe out computers?
A: Introduction: Adding more nodes or machines, you can increase your system's output through…
Q: You will be responsible for developing a comprehensive testing strategy when you take on this…
A: Software testing : Having filled in as software developers for countless years, we get to have…
Q: Take a look at the many types of access control systems and how they differ. Distinguish between the…
A: Three categories may be used to group access control frameworks: Role-based access control,…
Q: To get the most out of a gaming system, you should run Windows 8 on top of a machine with built-in…
A: Explanation: We need the following specifications to be met by a graphics card: Improves the overall…
Q: Locate the keyword that is used in the process of joining columns having the same column names but…
A: Natural join: An implicit join clause is created for you by a NATURAL JOIN operation based on the…
Q: As a result of this difference, the LEA instructions are far more powerful than the OFFSET operator.
A: Inspection: Guidance from the Local Education Authority The address that is provided in the first…
Q: pros and cons of using a cloud-based backup system
A: What are the pros and cons of using a cloud-based backup system?
Q: Provide examples of session hijacking tactics. Assaults like these need a strong defence.
A: Given: The act of seizing possession of anything that is not legally yours, such as an aero plane,…
Q: Which regions and zones can help improve the robustness, performance, availability, and resilience…
A: Given: If they have a device that can connect to the internet, users of cloud computing may access…
Q: Analyze the similarities and differences between the software development methodologies of Waterfall…
A: Overview: Consider the Rational Unified process, which differs from waterfall processes in that the…
Q: Is it possible to prioritise a large number of jobs with the same importance?
A: Introduction: Many firms have successfully rebuilt their data shadow systems, which has necessitated…
Q: What is the difference between the Internet of Everything (loE) and the Internet of Things (IoT) in…
A: IOE VS IOT: The Internet of Everything (IoE) is the intelligent connectivity between people,…
Q: When using Windows 8 on a gaming machine that already has a video card installed and has room for a…
A: Given: You must create a gaming PC from scratch to ensure that it will satisfy your demands. You…
Q: Examine the advantages of using Direct Memory Access over Interrupt Driven I/O.
A: Introduction: Direct memory access refers to the method of transmitting data without using the CPU…
Q: Do you believe that those who are disadvantaged in any manner, whether physically or…
A: The TCP/IP protocol stack is used by the worldwide network of linked computer networks known as the…
Q: This code create the one dimension array (B) contains the positive value of two .dimension array…
A: Solution:: Option (4) is the correct answer. int k=0; for(int i=1; i<=4; i++) { for(int…
Q: The resources sought by those who are stuck are made available to those who have been notified that…
A: Introduction: A deadlock occurs in an operating system when a process or thread enters a waiting…
Q: Rational Unified and Classical Waterfall models are compared to determine which is superior.
A: Answer: First and foremost, the waterfall model is a sequential model, therefore the software…
Q: What year and region saw the emergence of the Internet of Things?
A: The Internet of Things: The term "Internet of Things" (IoT) refers to a network of actual physical…
Q: In this side-by-side comparison, the Rational Unified paradigm is placed against the Classical…
A: SDLC includes these two models: Cascade programming involves substantial advance planning and…
Q: In terms of data backup and recovery, what are some of the most crucial factors to keep in mind?
A: The speed and precision are the most crucial factors: Planning is carried out during the data backup…
Q: What are some of the problems that firms face while moving to the cloud? What are the disadvantages…
A: answer is
Q: Which two instructions are executed by the User State Transfer utility?
A: Introduction: This tool consists of two command-line applications, scanstate.exe and loadstate.exe,…
Q: Write a program to merge two arrays of 8 elements for each sorted in descending order. For i = 1 To…
A: According to the information given:- We have to choose the correct option to satisfy the code.
Q: for i=1:4 for j=1:4 a=5; a=a+5; end end
A:
Q: In your opinion, how crucial is data quality to the success of data warehouses? If access to…
A: Given : In the context of data warehousing, how important do you think it is for data quality to be?…
Q: Where do Harvard and von Neumann stand in relation to one another in terms of computer architecture?
A: Von Neumann Architecture: The "Von Neumann Design" is a digital computer architecture that stores…
Q: Can persons with disabilities utilise the Internet? Which emerging technologies will aid people with…
A: Given: People's who are blinds or have low vision's benefits greatly from the internet. Because of…
Q: I need help making a code in python that: 1. The program asks for the unit value of a product 2.…
A: Here our task is to write a python program for the mentioned task. Algorithm Decalre variable…
Step by step
Solved in 2 steps

- Assuming I have a Pixel, called px, write the code to change its contents to its greyscale equivalent.you need to write a code/program to do image filtration or convolution of 2 noise filters. Please submit a report on the assignment.1.0 Introduction -Please state a simple objective - what you want to study based on the choice of the filter2.0 Method3.0 DiscussionI am having trouble on figuring out how to tackle this test case, below is my code and image one is the test case I am having trouble at(since it will tested automatically, i dont have the testcase.) image two is the main method, plz debug and fix it. Provide the screenshot of the code and output when finsih. import java.util.*;import java.io.*; public class TweetBot { private List<String> tweets; private int index; public TweetBot(List<String> tweets){ if(tweets.size() < 1){ throw new IllegalArgumentException("need contain at least one tweet!"); } this.tweets = new ArrayList<>(tweets); } public int numTweets(){ return tweets.size(); } public void addTweet(String tweet) { tweets.add(tweet); if (tweets.size() == 1) { index = 0; }} public String nextTweet() { if (tweets.size() == 1) { index = 0; return tweets.get(0); } else {…
- In this lab, you will use a timer to animate the movement of a heart image to the location where the mouse clicks, as shown below. In jacascript, please! The given web page shows a heart image. When the user clicks anywhere in the page, the startAnimation() function is called. startAnimation() determines where the user clicked and calls moveImage() with the clicked (x, y) coordinate. moveImage() moves the heart 1 pixel in the direction of the given (x, y) coordinates. Make the following JavaScript modifications using clearInterval() and setInterval() where appropriate: In startAnimation(), add an if statement that stops the timer with the ID timerId if timerId is not null. In startAnimation(), start a timer that calls moveImage(clickX, clickY) every 10 milliseconds. Save the timer ID in the timerId variable. Add an if statement in moveImage() that stops the timer with the ID timerId if (imgX, imgY) is equal to (centerX, centerY). Also set timerId to null. After the…I already saw a solution to this problem here, but it is not correct The edge-detection function (detectEdges) described in Chapter 7 and shown below returns a black and white image. Think of a similar way to transform color values so that the new image is still in its original colors but the outlines within it are merely sharpened. def detectEdges(image, amount): """Builds and returns a new image in which the edges of the argument image are highlighted and the colors are reduced to black and white.""" def average(triple): (r, g, b) = triple return (r + g + b) // 3 blackPixel = (0, 0, 0) whitePixel = (255, 255, 255) new = image.clone() for y in range(image.getHeight() - 1): for x in range(1, image.getWidth()): oldPixel = image.getPixel(x, y) leftPixel = image.getPixel(x - 1, y) bottomPixel = image.getPixel(x, y + 1) oldLum = average(oldPixel) leftLum = average(leftPixel)…Write a program that displays the flashing text “Welcome,” as shown in Figure 9.30a–b. (Hint: To make the text flash, you need to repeatedlydraw it on the canvas or alternately delete it. Use a Boolean variable to control the alternation.)
- To use geolocation in a JavaScript program, you must call thegetCurrentPosition()method on thegoogle.maps.Markerobject and pass in a callback function to run when the device’s coordinates are successfully retrieved. Select one: True FalseIs it possible to create a surface plot, using the same data?Please answer the problem in the screenshot. Please use the methods in the second screenshot.
- Please do not give solution in image format thanku Which of the following declarations matches the call to IsLetter? String strText = txtInput.Text; bool blnLetter = IsLetter(strText); public IsLetter(bool strInput) public String IsLetter(String strInput) public bool IsLetter(String strInput) public bool IsLetter(String strInput, bool result)Implement the "paint fill"feature seen in several picture editing products.To put it another way, if you have a screen (represented by a two-dimensional array of colours), a point, and a new colour, Fill in the surrounding area until the colour shifts away from the original.In the free edition of Google Sketchup, can I transform a picture from 2D to 3D? If this is the case, then how? Then what other options are there?



