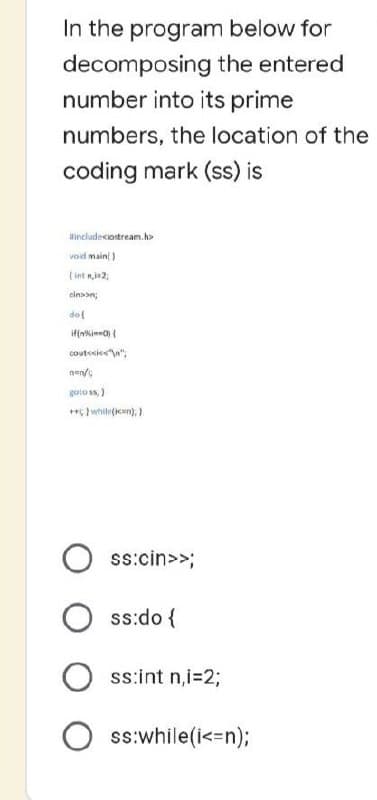
In the program below for decomposing the entered number into its prime numbers, the location of the coding mark (ss) is #include void main() (int n,2, cinson; dol if(n) { cout<<<<"\n"; nen/ goto ss;) +*; while(i); } ss:cin>>; Oss:do { Oss:int n,i=2; Oss:while(i<=n);
Q: Take into account the benefits and drawbacks of using wireless technology. At the very least,…
A: Introduction: This is a fast method for establishing highly secure social connections or exchanging…
Q: 1. Which statement(s) is/are true? C strings can be manipulated per character. C++ string can be…
A: The question has been answered in step2
Q: 25. What's the result of this line of code? string x = "123" + 45 O168 O "168" O "12345" compiler…
A: Given, string x = "123" + 45 we need to provide output for this.
Q: The phrases "complete" and "constant" are sometimes used interchangeably, but what do these words…
A: Given: The requirement analysis step of the software development process is very important since the…
Q: Write a program that accepts five numbers from the user and displays the lowest to the highest…
A: Here c++ program which takes 5 integer values and then print smaller and Langer values in given…
Q: The Linux and Windows netstat tool lists active network connections. Explain how to use this command…
A: Use the "netstat" command to: The phrase "network statistics" may be abbreviated to "netstat," which…
Q: The Linux kernel has included three new features. Is the release more secure as a result? What's the…
A: Linux kernel : Linux kernal is the core of the operating system Linux. It is a…
Q: Which of the following is not characteristic of a relational database model? A. Tables
A: The relational model for database management is an approach to managing data using a structure and…
Q: Identity theft is one of the most common online crimes.. There are several ways that identity…
A: Answer: An identity thief may hear you read your Visa number over the phone, buy it on the dark web…
Q: Describe many session hijacking strategies. Can you tell me whether there are any possible…
A: Introduction: Session hijacking is a sort of attack that allows unauthorized access to authorized…
Q: When developing software, one should think about the advantage sing a step-by-step method rather…
A: Introduction: Software is far too complex and unpredictable to design totally ahead of time, but…
Q: Given the dependency diagram below, create the set of dependency diagrams that would represent the…
A:
Q: There are five main changes between Windows 7 and Windows 10
A: Inspection: A crime committed via the internet or electronic equipment like a computer system is…
Q: The process of developing software and modelling software are not the same thing. The role that each…
A: Methodology for the Development of Software: In software engineering, the division of the…
Q: Create a little expert system in order to solve the challenge of analysing traffic accidents. You…
A: Introduction: After identifying a goal and a problem to tackle, the agent starts a search operation…
Q: No, I don't know of any non-free Linux firewalls listed in the presentation.
A: A firewall is a software or hardware component that prevents unauthorized network access. It…
Q: (4) char chArray[] = {'E', T, 'C', 'D', 'F', 'F'}; (5) int a 5, b-7, c; after the statement…
A: Correct General statement for any array in C is <datatype> <variable_name>[] =…
Q: Is there a way to explain how Ubuntu started as a branch of a Linux distribution?
A: 1) Linux is an operating system similar to that of Windows is an operating system The term operating…
Q: 3. Which statement(s) is/are true regarding structures in C++? A structure may contain arrays. A…
A: Please refer to the following step for the complete solution of the problem above.
Q: If you use your credit card to make an online money transfer, you are required to inform your…
A: Launch: Here Are Eight Ways to Prevent Fraud When Using Your Credit Card Online (1) You may reduce…
Q: Write C++ program, using for loop statement to print the following pattern: 1#2#3#4#5 #6 #7#8…
A: C++ code given below:
Q: Because there are no wireless networks accessible for the air interface between phones, antennas,…
A: Introduction: It is a computer network in which wireless data channels are used to connect network…
Q: Contrast the following terms: a. supertype; subtype b. generalization; specialization c. disjoint…
A: Disclaimer: “Since you have posted a question with multiple sub-parts, we will solve the first three…
Q: Check out how Ubuntu stacks up against other Linux distributions. My thought is the finest because…
A: This is something that has to be determined right now. Ubuntu comes out on top when compared to…
Q: Concerns have been raised over users' ability to maintain their privacy while utilising social…
A: Since the advent of the first social networking sites in the early 2000's, social networking sites…
Q: 2. Electric Bill: Write a program that will calculate and show bills of the Manila Electric Company.…
A: The code is given below.
Q: What exactly is the StreamWriter object?
A: The StreamWriter is mainly used for writing multiple characters of data into a file. After…
Q: Web page content can include O text O images audio & video all of the above
A: The answer is given below.
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Introduction: The merits and downsides of hardware and software firewalls, software tools, and how…
Q: Subject: Operating Systems The sizes of pages and page frames are often identical. Search academic…
A: page is a district of virtual location space, and a page outline is an area of actual memory. 1.A…
Q: Identify a crucial person of your team in system development. With the help of proper…
A: introduction: When done correctly, team development has the potential to cultivate an imaginative…
Q: The Linux kernel has included three new functions. The release's safety may be affected in any way…
A: The Linux kernel is the operating system's central processing unit. It is a multitasking,…
Q: Send a packet to a host using the fixed route assuming that you are utilising it. between two…
A: Start: The term "delays" refers to the amount of time that the processing packet takes to complete.…
Q: The quality of pictures may be affected by both frame and line rates.
A: Introduction: An image's quality is influenced by several factors, including frame rate and line…
Q: How can you tell whether a certain Linux distribution is the basis for Ubuntu Linux?
A: Introduction: Ubuntu is not only a complete Linux operating system that is distributed without…
Q: The comparison of Ubuntu to other Linux distributions should be made. What makes your idea the…
A: This must be determined at this juncture. Ubuntu triumphs over other well-known Linux variants when…
Q: In your perspective, which stage in the process of developing software is the most important, and…
A: Given: Which of the typical software development process stages, in your opinion, is the most…
Q: 05. Write C++ program to compute the value of Z according to the following equations: 6x + log(x) :…
A: logic:- read value of x. if x<0 display (6x+log(x)) else if x==0 display cos(x)+1 else…
Q: Take into account the benefits and drawbacks of using wireless technology. At the very least,…
A: Wireless technology: Wireless technology allows two or more entities to communicate across long…
Q: There are five main changes between Windows 7 and Windows 10
A: Windows 7 is a significant arrival of the Windows NT working framework created by Microsoft. It was…
Q: 6 Consider converting the following NFA to an equivalent DFA. 0 90 91 1 a The number of states in…
A:
Q: A language used to express algorithms in computer understandable form is… A. Assembly language B.…
A: A. Assembly Language
Q: There are many aspects that need to be taken into account while designing a software system.
A: Given: An input is any piece of data that is taken into consideration by a computer. The data that…
Q: Instructions A positive integer n is called prime if n > 1 and the only factors of n are 1 and n. It…
A: In this problem we need to design a program to check the prime factor for the give number using c++.…
Q: Hypothetical metal has an FCC crystal structure. If its density is 22.4 g/cm3, and atomic weight is…
A: According to the information given:- We have to calculate the hypothetical metal's radius on the…
Q: During each step of the process, what are the most important factors for system developers?
A: When designing new systems, system developers encounter several difficulties. They have to manage a…
Q: Write flowcharts to find factorial of a given 100 numbers?
A:
Q: One of the most common types of illegal activities that may be carried out through the internet is…
A: Identity Theft: An identity thief may hear you read your Visa number over the phone, buy it on the…
Q: Explain the reasons why testing the correctness of a programme against a formal specification isn't…
A: Finite-state machines represent systems in model checking, and this finite-state model is tested…
Q: define non-technical cyberattacks and their effects
A: Non technical cyber attacks are the attacks in which the attackers uses social engineering methods.…
Step by step
Solved in 2 steps

- Please use java Part 2. Library Class Implement a class, Library, as described in the class diagram below. Library must implement the Comparable interface. The compareTo() method must compare the branch names and only the branch names. The comparison must be case insensitive. The equals() method must compare the branch names and only the branch names. The comparison must be case insensitive. Be sure to test the equals() and compareTo() methods before proceeding. Library - state: String - branch: String - city: String - zip: String - county: String - int squareFeet: int - int hoursOpen: int - int weeksOpen: int + Library(state: String, branch: String, city: String, zip: String, county: String, squareFeet: int, hoursOpen: int, weeksOpen: int) + getState(): String + getBranch(): String + getCity(): String + getZip(): String + getCounty(): String + getSquareFeet(): int + getHoursOpen(): int + getWeeksOpen(): int + setState(state: String): void + setBranch(branch:…Computer Science Please refactor the constructors to reduce code duplication using the call this(), with the proper parameter. Thank you! LatencyAnalysis(WarpInterface warp) { this.latencyReport = new Description(); this.program = warp.toProgram(); this.workload = warp.toWorkload(); this.programTable = program.getSchedule(); this.nodeIndex = program.getNodeMapIndex(); } LatencyAnalysis(Program program) { this.latencyReport = new Description(); this.program = program; this.workload = program.toWorkLoad(); this.programTable = program.getSchedule(); this.nodeIndex = program.getNodeMapIndex(); }JAVA PROGRAM ASAP *********** THIS PROGRAM MUST WORK IN HYPERGRADE AND PASS ALL THE TEST CASES. Please create a program BECAUSE IT IS. MY HOMEWORK ASSIGNMENT with the following parts which are down below: The left index is inclusive and the right index is exclusive. 1. public static void bubbleSort(int[] array, int left, int right) { // your code here } 2. public static void insertionSort(int[] array, int left, int right) { // your code here } 3. public static void selectionSort(int[] array, int left, int right) { // your code here } Test Case 1 Please enter a space separated list of numbers to sort or type QUIT to exit:\n4 3 2 1ENTERSorting first half of the array using Bubble Sort algorithm:\n3 4 2 1\nSorting second half of the array using Bubble Sort algorithm:\n4 3 1 2\nSorting the array using Bubble Sort algorithm:\n1 2 3 4\nSorting first half of the array using Insertion Sort algorithm:\n3 4 2 1\nSorting second half of the array using Insertion…
- Main Class Implement a main class that implements our ParkingOffice.java class. Parkingoffice.java public class ParkingOffice {String name;String address;String phone;String parkingOfficeName;List<Customer> customers;List<Car> cars;List<ParkingLot> lots;List<ParkingCharge> charges; public ParkingOffice(){customers = new ArrayList<>();cars = new ArrayList<>();lots = new ArrayList<>();charges = new ArrayList<>();} public String getParkingOfficeName(){return this.parkingOfficeName;} /* to implement the desired park function */ public String park(Date date,String ParkingPermit,ParkingLot pl){ /* to have the amount paid during the transaction forthe specified parking lot */double amount=pl.amount;/* to have the date on which the parking lot is booked */String onDate=date.toString();/* to know the permit id */String permitId=ParkingPermit;/* to print the transaction receipt */String s="Amount paid on date: ";s=s+onDate;s=s+" is…error on python code: File "/root/sandbox/MyMotorcycleClassProgram.py", line 11, in <module> motorcycleOne = Motorcycle(90.0)TypeError: Motorcycle.__init__() takes 1 positional argument but 2 were given from Vehicle import Vehicle # Write the Motorcycle class here class Motorcycle(Vehicle): def__init__(self): Vehicle.__init__(self) self._sidecar = sidecar defset_sidecar(self,sC): self._sidecar = sidecar defget_sidecar(self): returnself._sidecar defaccelerate(self,mph): ifself._speed + mph >self._max_speed: self._speed =self._speed + mph else: print("This motorcycle cannot go that fast.")IN HASKELL PROGRAMMING LANGUAGE PLEASE In case you do not know it: the game is played on a 3x3 grid that is initially empty. Two players are playing, by alternatingly making moves. A move by a player places their token (an X for player 1, an O for player 2) into a cell that was empty. We are using algebraic notations for indexing the positions in the board, with A,B,C indexing the columns and 1,2,3 the rows. Specifically, these coordinates would be used in the implementation for moves made by a human player. If the X X O Figure 1: Sample board position same token appears 3 times in any of the three columns, three rows or two main diagonals the game is over and that player wins. If the grid is filled without that happening the game is a draw. For the depicted board, we have Xs in positions C3 and A2, and an O in position B1. It would be O’s turn to make a move; a legal move would be C2, but it is not a good move, because X can force a win by responding A1. O cannot force a win, but…
- Use java programming language 1.1 Create a Student Object project. Create a Student class and use the provided UML diagram to code the instance fields, constructors and methods. Note: The module mark is the average of the participation mark and the examination mark - calculate this using the calcModuleMark() method. The determineStNumber() method should compile a student number with the first 3 letters of the student's name, a '#' symbol, and a 3-digit randomly generated number (make use of a for-loop to concatenate these 3-digits). The stNumber data field should be set in the constructor by calling the determineStNumber() method. The toString() method must compile a string to display the student number, participation mark, examination mark, and module mark, formatted in table format. Student number PMark EMark MMark Mar#9186 81 64 72.00 1.2 Create a testStudents class. Do the following: -Write a static method called display() which receives…C#: PLease add inheritance and polymorphism in the code. And display the vehicle/s. Thanks!using System;using System.Collections.Generic;using System.Linq;using System.Text;using System.Threading.Tasks;namespace DemoApplication{ public class Vehicle { protected int VehicleID; protected string VehicleName; public void SetTutorial(int pID,string pName) { VehicleID=pID; VehicleName=pName; } public String GetVehicle() { return VehicleName; } } public class VehicleDetails:Vehicle { public void RenameVehicle(String pNewName) { VehicleName=pNewName; } static void Main(string[] args) { VehicleDetails VD=new VehicleDetails(); VD.RenameVehicle("CarName:Audi"); VD.RenameVehicle("Number of doors:4"); VD.RenameVehicle("Number of wheels:4"); VD.RenameVehicle("Maxspeed:180 KMPH"); VD.RenameVehicle("Fuel capacity:50 lts"); Console.WriteLine(VD.GetVehicle()); Console.ReadKey(); } }}create a UML class diagram for the following Java Code: public class SudokuSolver { publicstaticfinalint SIZE =9; publicbooleansolveSudoku(int[][] board){ for(int row =0; row < SIZE; row++){ for(int col =0; col < SIZE; col++){ if(board[row][col]==0){ for(int number =1; number <= SIZE; number++){ if(isValid(board, row, col, number)){ board[row][col] = number; if(solveSudoku(board)){ returntrue; }else{ board[row][col] = 0; // backtrack } } } returnfalse; } } } returntrue; } privatebooleanisValid(int[][] board,int row,int col,int num){ for(int i =0; i < SIZE; i++){ if(board[row][i]== num || board[i][col]== num || board[row - row % 3 + i / 3][col - col % 3 + i % 3] == num) { returnfalse; } } returntrue; } publicstaticvoidmain(String[] args){…
- import components.naturalnumber.NaturalNumber;import components.naturalnumber.NaturalNumber2;import components.simplewriter.SimpleWriter;import components.simplewriter.SimpleWriter1L; /*** Program with implementation of {@code NaturalNumber} secondary operation* {@code root} implemented as static method.** @author Mati Desissa**/public final class NaturalNumberRoot { /*** Private constructor so this utility class cannot be instantiated.*/private NaturalNumberRoot() {} /*** Updates {@code n} to the {@code r}-th root of its incoming value.** @param n* the number whose root to compute* @param r* root* @updates n* @requires r >= 2* @ensures n ^ (r) <= #n < (n + 1) ^ (r)*/public static void root(NaturalNumber n, int r) {assert n != null : "Violation of: n is not null";assert r >= 2 : "Violation of: r >= 2"; double lowEnough = 0;double tooHigh = n.toInt();double power = 1.0 / r;double value = Math.pow(tooHigh, power);double guess = (1.0) * tooHigh / 2; while ((int) guess !=…Please solve in JAVA only You are in charge of the cake for a child's birthday. You have decided the cake will have one candle for each year of their total age. They will only be able to blow out the tallest of the candles. Count how many candles are tallest. ExampleCandles = [4,4,1,3]The maximum height candles are 4 units high. There are 2 of them, so return 2. Function DescriptionComplete the function birthdayCakeCandles in the editor below. birthdayCakeCandles has the following parameter(s):• int candles[n]: the candle heights Returns• int: the number of candles that are tallest Input FormatThe first line contains a single integer n, the size of candles[].The second line contains n space-separated integers, where each integer describes the height of candles[i]. Constraints• 1 ≤ n ≤ 105• 1 ≤ candles[i] ≤ 107 Sample Input 043 2 1 3 Sample Output 02 Explanation 0Candle heights are [3,2,1,3]. The tallest candles are 3 units, and there are 2 of them. import java.io.*;import…Writing the setbank functionsSetbalanceSetaccontIn order to enter the creditcard data instead of entering it into the constructor functionand execute it in the main class public class CreditCard { private String customer; private String bank; private String account; protected double balance; public CreditCard(String cust,String bk, String acnt,double initialBal) { customer=cust; bank=bk; account=acnt; balance=initialBal; } public CreditCard(String cust, String bk, String acnt) { this(cust,bk,acnt,0.0); } public String getCustomer() { return customer; } public String getBank() { return bank; } public String getAccount() { return account; } public double getBalance() { return balance; } // Update methods: public void charge(double price) { // make a charge balance += price; } public void makePayment(double amount) { // make a payment balance -= amount; }…

