In what way is a virtual machine useful? It allows users to create a backup. It allows users to run multiple OS on a single computer. It connects multiple users. O It increases internet speeds.
In what way is a virtual machine useful? It allows users to create a backup. It allows users to run multiple OS on a single computer. It connects multiple users. O It increases internet speeds.
Chapter14: Security, Troubleshooting, And Performance
Section: Chapter Questions
Problem 6DE
Related questions
Question
Transcribed Image Text:A memphisvirtual.instructure.com
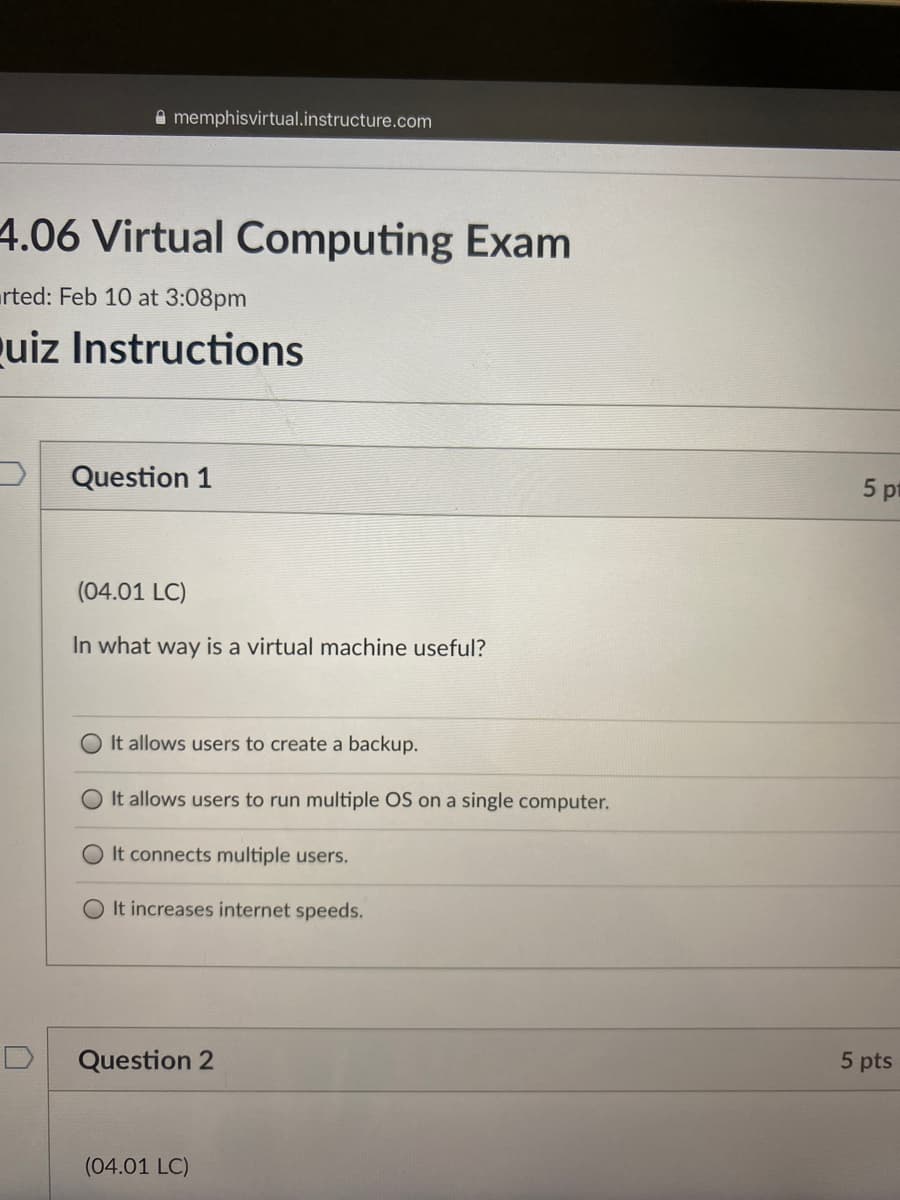
4.06 Virtual Computing Exam
rted: Feb 10 at 3:08pm
uiz Instructions
Question 1
5 pt
(04.01 LC)
In what way is a virtual machine useful?
It allows users to create a backup.
O It allows users to run multiple OS on a single computer.
O It connects multiple users.
O It increases internet speeds.
Question 2
5 pts
(04.01 LC)
Expert Solution
Step 1
Problem Introduction:
In what way virtual machine is useful
See below step for answer.
Sort answer is : it allows users to run multiple os on a single computer.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning