In which normal form (unnormalised, first normal form, second normal form or third normal form) is each of the below? Clearly motivate your answer
Q: Set Deduction 1 Suppose that the follow set relations are true:
A: Set relations are true
Q: Explain the difference between eq?, eqv?,and equal?.
A: equal: It is used when user wants to test whether the two lists,vectors are equivalent eqv: It is…
Q: Give difference between independent, dependent and logical data mart.
A: To be determine: Give difference between independent, dependent and logical data mart.
Q: t was stated that deadlock cannot occur for the situation reflected in Figure 6.3. Justify that…
A: Given: Justify your claim that the situation depicted in Figure 6.3 cannot result in stalemate.
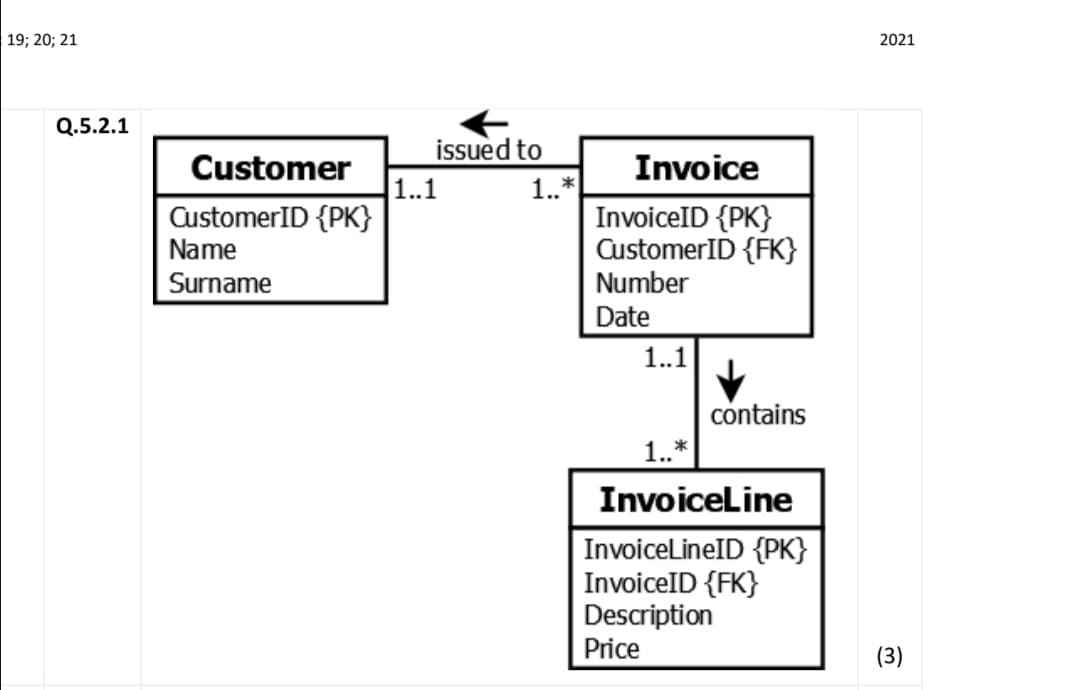
Q: Transform the given ERD (given on next page) into Relational Model.
A: Given: Transform the given ERD (given on next page) into Relational Model.
Q: What is the difference between EL(a, b) and EL(b, a)?
A: EL(a,b) and EL(b,a) are two function calls in which EL(a,b) passes a as first argument and b as…
Q: (b) use the drawing conventions in the lecture notes. Translate the following ER diagram into a…
A: We have to translate given ER diagram into relational model.
Q: Assuming the roles of president and secretary cannot be filled by the same person, how many…
A: If any event occurs either in m OR n ways , the number of ways event can be occurred be m+n. When…
Q: ormali
A: Denormalization is the process of introducing redundant data that has already been computed to an…
Q: Using a non-book example, define the words functional dependence and determinant.
A: The answer is provided below.
Q: We have a ternary relationship below:
A:
Q: What is the rationale for normalising first and then denormalizing?
A: Answer:
Q: If P is the primary key of schema R, we must have P -> R. True or
A: If P is the primary key of schema R, we must have P -> R. --> True
Q: Develop a BasicMOST analysis of the sequence of activities for the table
A: Exactly is BasicMOST: One of the most famous examples of MOST is BasicMOST. It is really often also…
Q: ed both explanation as well as solution..
A: I have answered below:
Q: PQ → TY ii. P → QR iii. QST → R iv. STR → P From the above functional dependencies, using…
A: Given:- i. PQ → TY ii. P → QR iii. QST → R iv. STR → P From the above functional dependencies,…
Q: Contrast the terms normal form; normalization?
A: Answer: Normal Form: 1. This is used to reduce or avoid the redundancy in database tables. 2. Here,…
Q: Explain why you've chosen to employ consistency of degree two. What are some of the drawbacks of…
A: The following is the answer to the previous question: Degree two consistency is a lesser consistency…
Q: Explain with an appropriate example in the relational model.
A: Introduction: A relational model is a database that stores and makes available connected data…
Q: What is the difference between Regression and Classification? List at least 5 points in a tabular…
A: The difference between Regression and Classification is as follows:
Q: of using functions of
A: Higher-order functions will be functions that accept functions as argument. It is utilized in…
Q: Q2/ For the DSA signature algorithm, show the process of key generation, signing and verification by…
A: DSA algorithm Digital signatures algorithms are used to detect whether the data is modified by…
Q: Is the recurrence relation fn=fn-1+f2n-2s a linear homogeneous recurrence relation? Provide reason…
A: PLEASE DO SUPPORT FOR MY EFFORTS THANKS! ANSWER: not the given equation is not a linear…
Q: Explain the notation {Pre} Code {Post}. Explain in your answer the difference between total and…
A: The answer is given below. "Pre" denotes a presumption made at the start of the execution. It's…
Q: Just what does it imply when people talk about the CAP theorem? In what ways is it possible for…
A: NoSQL: NoSQL databases (aka "not only SQL") are non-tabular and store data differently than…
Q: Give unsigned compare conditions between two variables i.,e (i - j)?
A: The Answer is in below Step:-
Q: Draw relational model
A: Note: There are multiple questions are given in one question. According to the rule, you will get…
Q: What is the closed form solution to the following recurrence relation? Please use the iteration…
A: Here in this question we have given recurrance relation and we have to use iterative method to solve…
Q: For each of the following pairs of expressions, give instances of relations thatshow the expressions…
A: Equivalence relation An equivalence relation on a set S is defined as a relation on S which holds…
Q: From worksheet sheet4, in cell B8, find the model of car with id T3 using Vlookup) from the Table 4.…
A: Syntax for Vlookup is =VLOOKUP(lookup_value,table_range,column_index,lookup_range) lookup_range is…
Q: Mapping er dig to Relational Model
A: The Answer is
Q: Use truth table to determine whether the argument to be valid or invalid. Indicate which columns…
A: Given premises: p p↔q r Conclusion: p→r
Q: Explain why the above table is not in First Normal Form
A: Note : As per guidelines we are authorized to answer 1st question when multiple questions are…
Q: Convest ? NAA to NHA
A:
Q: Investigate the possibility of reducing the number of rules due to excluding some (check the…
A: Lets discuss the solution in the next steps
Q: Describe the rationale for the usage of consistency of degree two. What are the drawbacks of this…
A: Degree 2 consistency: A transaction that maintains consistency to the degree 2 level is separated…
Q: we use the phrases "complete and consistent"?
A: complete: Having all parts or elements ,lacking nothing,whole,entire,full complete set of Mark…
Q: All the methods for checking the serializability should be discussed with well drawn schedules and…
A: To identify the schedules which is nonserial, a concept called serializability is used. It will…
Q: Odd? Even? Neither?
A: The solution to the given problem is below.
Q: an you explain what the difference is between normalization and denormalizati
A: Lets see the solution.
Q: Consider the following database and its schema and write relational algebra expression to retrieve:…
A: Doing with MySQL query
Q: Following diagram is the confusion matrix for multi classification. Find the precision and recall. 7…
A: Confusion matrix: For classification process, a confusion matrix is used to access the performance…
Q: Fit the following data below using Cubic Regression. Terminate if Ea ≤ 0.0001
A: Concept: In the cubic regression model, we deal with cubic functions, that is, polynomials of degree…
Q: 5.1 In which Normal Form is the above table? Explain how you arrived at your answer. 5.2 Explain the…
A: 5.1 Primary key for the given relation is {InvoiceNo,ProductNo} But the given relation contains…
Q: Q2 / For the DSA signature algorithm, show the process of key generation, signing and verification…
A: Solution:
Q: What is the degree of relationship?Give an example of a relationship of degree three
A: DEGREE OF RELATIONSHIP - The particular number of type of entities which participate into a given…
Q: step by step with proper explanation.
A: I have solved below the following question:
In which normal form (unnormalised, first normal form, second normal form or
third normal form) is each of the below? Clearly motivate your answer
Step by step
Solved in 7 steps with 7 images

- 1. a) When a function is called in a given running program, an _____________ is created in the stack section of the virtual address space of the program that stores all the variables local to the function 1.b) Will the code below change the value of x? Explain why your answer is correct. All codes in c++ #include <iostream> using namespace std; void change(int); int main() { int x = 10; change(x); cout << "x = " << endl; return 0; } void change(int n1) { n1++; }python 8.7 LAB: Writing append and search methods (singly-linked list)Given main.py and a Node class in Node.py, complete the LinkedList class in LinkedList.py by writing the append() and search() methods. The search() method should return the Node whose data value matches a given key, and None if the key is not found. The search() method should also set the position of each Node searched in the LinkedList, starting with 1. Ex: If the input is: 12 23 59 37 923 212the output is: 12 found in list at position 1.If the input is: 12 23 59 37 923 268the output is: 68 not found in list.I need answer question pls Project Operations Write a JAVA program that will maintain a phone directory using a Linked-List. The program should be able to perform the following operations: 1) Add persons details (first name, last name, phone number, city, address, sex and email) to the phone directory, where phone numbers in the directory have to be unique. (Note: each person record will store in one node in the linked-list and insert each person to the last) 2) Delete any person details by a given phone number. 3) Update telephone number by providing person first name. 4) Display all details of persons from a phone directory. 5) Search telephone number based on person first name. (Note: use sequential search to find all telephones for the given first name) 6) Sort all persons in the phone directory ascending based on person first name. (Note: use bubble or selection sort to arrange the entire phone directory) Project Outputs The output has to display a menu of choices. Then the…
- File system implementation: a. Given a flename in a directory’s data block, how does OS locate the data block of a fle? b. Compare between direct pointers and indirect pointers in referencing data blocks. c. Given a 6GB fle, identify the number of index level needed when using indirect pointer.2.2.14 Combining sorted queues. Create a static function that accepts two sorted queues as parameters and returns a queue formed by merging the queues into sorted order. 2.2.15 Mergesort from the bottom of the queue. Create a bottom-up mergesort implementation using the following method: Create N queues, each containing one of the things, given N items. Make a queue out of the N queues. Then, repeat Exercise 2.2.14's merging process on the first two queues, and finally, reinsert the combined queue.Repeat until there is just one queue in the queue of queues.6.Need ri Write a JAVA program that will maintain a phone directory using a Linked-List. The program should be able to perform the following operations: Add persons details (first name, last name, phone number, city, address, sex and email) to the phone directory, where phone numbers in the directory have to be unique. (Note: each person record will store in one node in the linked-list and insert each person to the last) Delete any person details by a given phone number. Update telephone number by providing person first name. Display all details of persons from a phone directory. Search telephone number based on person first name. (Note: use sequential search to find all telephones for the given first name) Sort all persons in the phone directory ascending based on person first name. (Note: use bubble or selection sort to arrange the entire phone directory.
- Write about navigation and configuration/com- attacked by web s patibility testing. Write about navigation and configuration/com- attacked by web s patibility testing.1. Build a web crawler function that starts with a URL representing a topic (a sport, your favorite film, a celebrity, a political issue, etc.) and outputs a list of at least 15 relevant URLs. The URLs can be pages within the original domain but should have a few outside the original domain.17-14 C++ Instructions Write the definition of the function moveNthFront that takes as a parameter a positive integer, n. The function moves the nth element of the queue to the front. The order of the remaining elements remains unchanged. For example, suppose: queue = {5, 11, 34, 67, 43, 55} and n = 3. After a call to the function moveNthFront: queue = {34, 5, 11, 67, 43, 55} Add this function to the class queueType. Also, write a program (in main.cpp) to test your method.
- Make an argument that supports the use of deep access rather than shallow access; attempt to avoid making an argument that centres around performance. This may be done by making an argument that supports the use of deep access rather than shallow access.Q__3.. ...Design a data structure that follows the constraints of a Least Recently Used (LRU) cache. Implement the LRUCache class: LRUCache(int capacity) Initialize the LRU cache with positive size capacity. int get(int key) Return the value of the key if the key exists, otherwise return -1. void put(int key, int value) Update the value of the key if the key exists. Otherwise, add the key-value pair to the cache. If the number of keys exceeds the capacity from this operation, evict the least recently used key. The functions get and put must each run in O(1) average time complexity. Example 1: Input ["LRUCache", "put", "put", "get", "put", "get", "put", "get", "get", "get"] [[2], [1, 1], [2, 2], [1], [3, 3], [2], [4, 4], [1], [3], [4]] Output [null, null, null, 1, null, -1, null, -1, 3, 4]... Code inly--+).8.13 LAB: Library book sorting Two sorted lists have been created, one implemented using a linked list (LinkedListLibrary linkedListLibrary) and the other implemented using the built-in Vector class (VectorLibrary vectorLibrary). Each list contains 100 books (title, ISBN number, author), sorted in ascending order by ISBN number. Complete main() by inserting a new book into each list using the respective LinkedListLibrary and VectorLibrary InsertSorted() methods and outputting the number of operations the computer must perform to insert the new book. Each InsertSorted() returns the number of operations the computer performs. Ex: If the input is: The Catcher in the Rye 9787543321724 J.D. Salinger the output is: Number of linked list operations: 1 Number of vector operations: 1 Which list do you think will require the most operations? Why? Main.cpp: #include "LinkedListLibrary.h"#include "VectorLibrary.h"#include "BookNode.h"#include "Book.h"#include <fstream>#include…

