#include int main() { int END VAL = 0; double miles, gallons, mpg; while (1) ( printf("How many miles did you drive? Enter 0 to quit: "); scans ("%lf", &miles); if (miles 1 END_VAL) { printf("How many gallons of gas did you use? "); scans ("%lf", &gallons); mpg miles/gallons; printf("Your mpg is %.21f", mpg); printf("\n"); } else { printf("End of program"); break; return 0;
#include int main() { int END VAL = 0; double miles, gallons, mpg; while (1) ( printf("How many miles did you drive? Enter 0 to quit: "); scans ("%lf", &miles); if (miles 1 END_VAL) { printf("How many gallons of gas did you use? "); scans ("%lf", &gallons); mpg miles/gallons; printf("Your mpg is %.21f", mpg); printf("\n"); } else { printf("End of program"); break; return 0;
Chapter7: Microsoft Edge
Section: Chapter Questions
Problem 2EYK
Related questions
Question
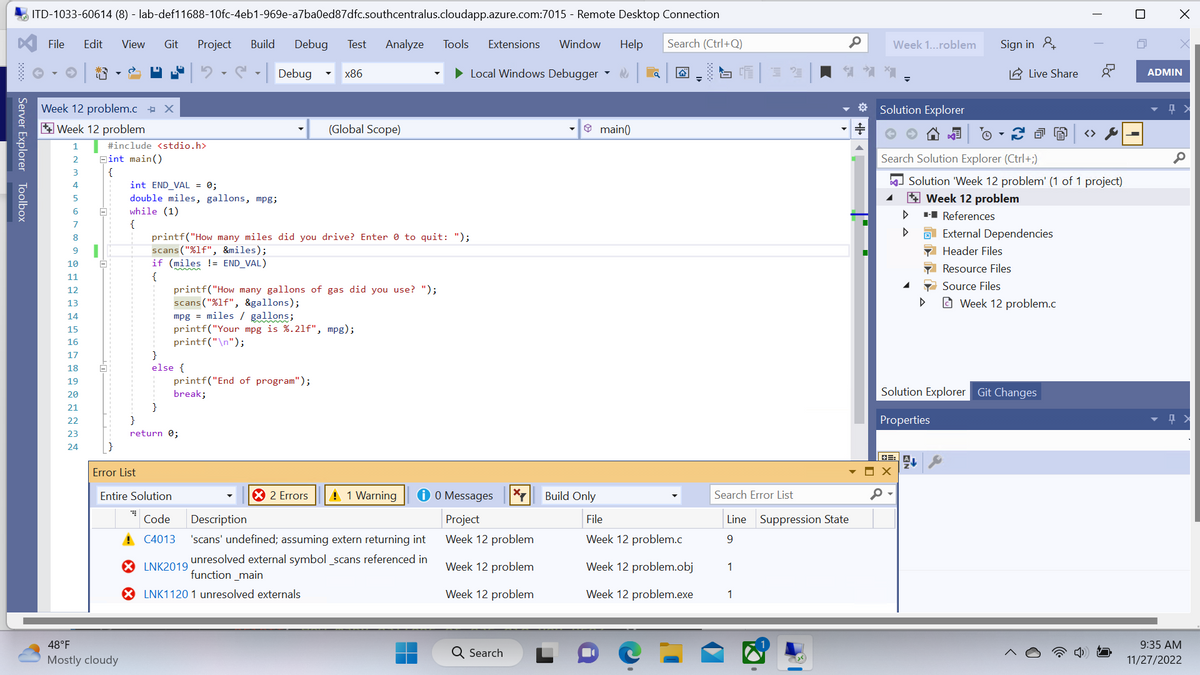
Please fix the errors and warning, scanf does not work and I am using 2019 visual studio.
Transcribed Image Text:Server Explorer Toolbox
ITD-1033-60614 (8) - lab-def11688-10fc-4eb1-969e-a7ba0ed87dfc.southcentralus.cloudapp.azure.com:7015 - Remote Desktop Connection
Search (Ctrl+Q)
File Edit View Git Project Build Debug Test Analyze Tools Extensions Window Help
Debug
► Local Windows Debugger
Week 12 problem.c X
Week 12 problem
1
2
5
6
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
ते
#include <stdio.h>
Eint main()
{
int END_VAL = 0;
double miles, gallons, mpg;
while (1)
{
48°F
Mostly cloudy
Error List
printf("How many miles did you drive? Enter to quit: ");
scans ("%lf", &miles);
if (miles != END_VAL)
{
}
else {
}
printf("How many gallons of gas did you
scans ("%lf", &gallons);
mpg = miles / gallons;
printf("Your mpg is %.21f", mpg);
printf("\n");
printf("End of program");
break;
}
return 0;
x86
Entire Solution
Code
! C4013
(Global Scope)
");
X 2 Errors ! 1 Warning i 0 Messages *7
Project
Week 12 problem
Week 12 problem
Week 12 problem
Description
'scans' undefined; assuming extern returning int
unresolved external symbol_scans referenced in
function _main
XLNK1120 1 unresolved externals
XLNK2019
Q Search
Build Only
▼
main()
File
Week 12 problem.c
Week 12 problem.obj
Week 12 problem.exe
SCE 32
Search Error List
Line Suppression State
9
1
1
0
Week 1...roblem
* Solution Explorer
#
4
Sign in
Search Solution Explorer (Ctrl+;)
X
Live Share
External Dependencies
Header Files
Resource Files
Source Files
Solution 'Week 12 problem' (1 of 1 project)
Week 12 problem
■-■ References
Week 12 problem.c
Solution Explorer Git Changes
Properties
T
Foc
x
ADMIN
0
Q
9:35 AM
11/27/2022
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage