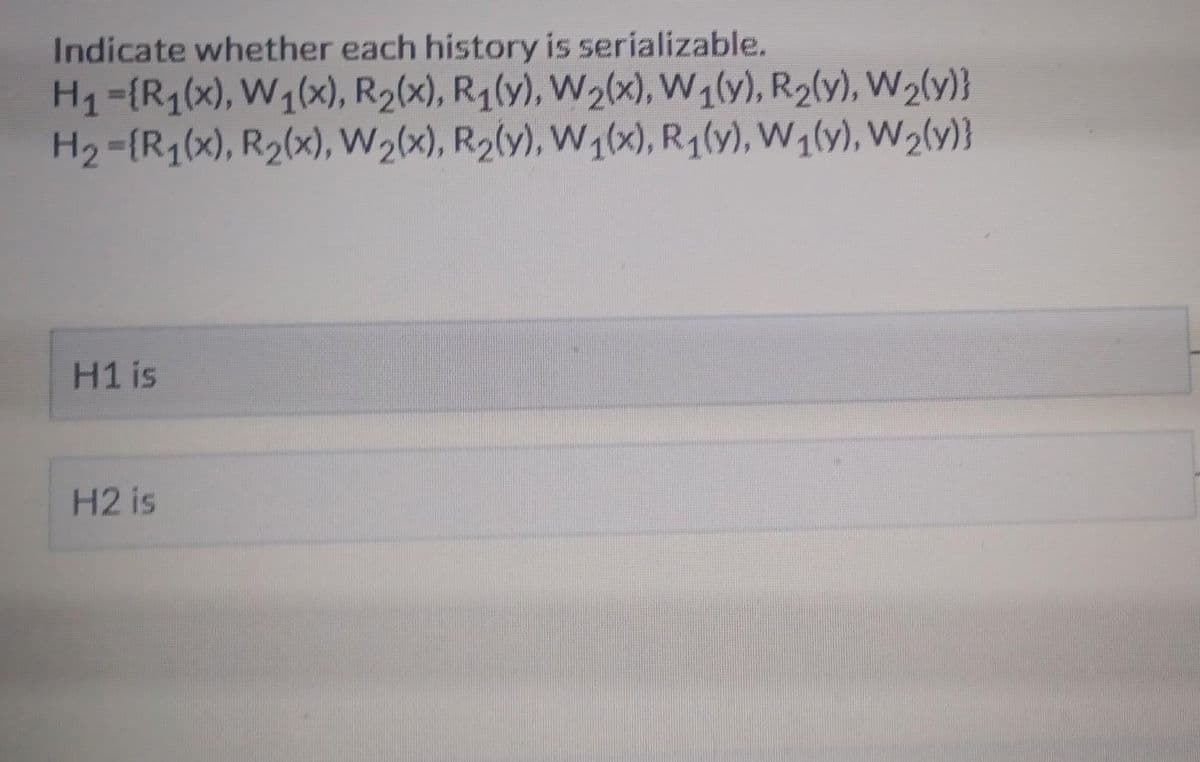
Indicate whether each history is serializable. H₁ ={R₁(x), W₁(x), R₂(x), R₁(y), W₂(x), W1(y), R₂(y), W₂(y)} H₂={R₁(x), R₂(x), W₂(x), R₂(y), W1(x), R₁(v), W₁(y), W₂(y)} H1 is H2 is
Q: You may be wondering, "Why bother with a technical analysis?" Explain how it is used, why it is…
A: Introduction: Technical analysis is a method. Valuation Methods When evaluating a company as a…
Q: 5 Which of the following diagrams are technology agnostic, meaning they do not depend on a specific…
A: All these options are related to data base handling structure and important concept for organization…
Q: For example, what does a perceptron network model entail? How could this model be used for…
A: The model for the training algorithm suggests: A convolution model is a continuous learning strategy…
Q: Write a program on python that simulates the toss of a six sides die. What is the ratio of the…
A: Write a program on python that simulates the toss of a six sides die.
Q: The principle of "divide and conquer," in which analysis and design should consistently place…
A: Algorithm Split and Conquer. Algorithmically, the architecture is meant to take a large input, break…
Q: How is it decided what image from the Image List will be shown in the PictureBox, and what value is…
A: ImageList: It is a control component that enables you to keep track of the amount of photos utilised…
Q: The Internet is now crucial for exercising one's right to freedom of speech. As a result, many…
A: Internet provides amazing prospects for "speakers" in the broadest sense.Political candidates,…
Q: Fixing the computer disk error caused by incorrect CMOS settings. Will you please elaborate on that?
A: Introduction: In the next response, I will talk exactly how the CMOS settings were entered…
Q: I was wondering, what are the negative aspects of business networking? In addition to describing the…
A: If company-wide networking is unavailable, servers, applications, and devices cannot connect.…
Q: Show the difference in the interaction of rules, data and answers in machine learning and classical…
A: Please find the answer below :
Q: Which features should a compiler have to guarantee that the code it produces is valid and efficient?…
A: Compiler writers have instructions. These factors assist compiler developers construct a reliable…
Q: When should you avoid stalemate by jumping right to the solution? No handwritten submissions, and no…
A: When multiple processes are stalled waiting for a shared resource, a deadlock has occurred. The…
Q: Is there an alternative to constructing your own data center and filling it with Windows or Linux…
A: In-house data centres At-house data centres store a company's own servers, networking devices, and…
Q: How relevant are rules about who can and cannot enter a certain area, anyway, in the modern world?…
A: A security technique called access control restricts who or what may access resources in a computer…
Q: Values, not references, are accepted in Java's method arguments. What does this imply, specifically?
A: Methods in Java may either return a value or do nothing at all, giving us the flexibility to design…
Q: Explain why the star schema could be preferable than the snowflake form and why. Which one is more…
A: The Star schema is in a more de-normalized form and hence tends to be better for performance. Along…
Q: Examine the parallels and distinctions between Governance and Management as they pertain to the…
A: Introduction: In the context of information system auditing, contrast governance and management.…
Q: Identify one predicate device that is currently approved, and that device may not necessarily be…
A: Introduction Predicate device: A predicate device (PD) is a medical device that is currently…
Q: Mention a future killer application in computer science. Justify why it is a killer application.
A: Dear Student, The answer to your question is given below -
Q: The swap replacement policy the replaces the newest page in memory is Least Recently Used (LRU) Last…
A: As per policy, first three subparts can be answered once. Ans.1 The swap replacement policy the…
Q: Prove that the Satisfiability Problem for 4-conjunctive normal form formulas is N P complete.
A:
Q: Can a single process become stuck in a snag during execution? The reasoning behind your answers is
A: Dear Student, The answer to your question is given below -
Q: Can a single process become stuck in a snag during execution? The reasoning behind your answers is…
A: A deadlock occurs when many processes seek to access a resource that is already in use by another…
Q: Create a single tape Turing machine that has the alphabet a, b, c and null. This Turing machine…
A: Check below mention step 2 detail explanation
Q: With the Model-View-Controller architecture in mind, is it possible to completely alter the…
A: A typical software design paradigm for implementing user interfaces, data, and controlling logic is…
Q: Don't just cite performance gains when arguing in favor of deep access over shallow access; instead,…
A: Introduction: From the standpoint of a programmer, provide a defenses for using deep access as…
Q: Explain the idea of copy-on-write to me.
A: When a parent process creates a kid' Not all parent process pages must be replicated. Only…
Q: Your task is to design, develop a computer game of your choice. Your program must be original, user…
A: I have develop a program for number guessing game. I have provided C++ CODE along with CODE…
Q: Why not try out Sun Solaris's user and kernel threading? Can you explain the pros and cons of…
A: Explanation: The Sun Solaris os, a Unix operating system, was created by Solar Micro Systems. The…
Q: meaning of the double lines arc
A: The diamond symbol is used to denote relationship between two entities. Double Diamond shows that…
Q: Discuss the logistics of storing and retrieving schedule management system files.
A: A file management system maintains files. It organises computer files. File management systems are…
Q: 3. Draw a flowchart and a java program that computes the student's grade using the formula use by…
A: - We need to work on score program in java.
Q: elect one topic that is of particular interest to you. Perform additional internet research on that…
A: Introduction: SQL, or Structured Query Language, is a strong and adaptable programming language that…
Q: The Internet has developed into a vital instrument for expressing one's free speech, and it is…
A: Introduction: Internet is a computer-to-computer network. Millions of smaller networks transfer data…
Q: For what purposes does protected mode employ the "access rights byte"?
A: INTRODUCTION: The ability to read, write, alter, delete, or otherwise access a computer file; change…
Q: How and why do you think it's important for systems administrators to make backups?
A: Introduction Backups: The practice of making and keeping copies of information that can be utilized…
Q: Can you explain what an ADT is and how it functions to complete tasks? Is it possible that there are…
A: Introduction: As a mathematical concept, ADT can stand in for many different kinds of information.…
Q: Create a structure called car with the following members: • Make • Model • Year • Mileage Create a…
A: algorithm:- declare structure car with data members as make, model , year and mileage. In main…
Q: If you get an error message on your computer, what would you do to fix it?
A: Introduction: A mathematical error code alerts the system. It may help you find a solution. To solve…
Q: Detail the variations in UNIX/Linux and Windows' implementations of the concept of least privilege.
A: Explanation: The permission of computer resources that may only be accessed by the people to whom…
Q: Thoroughly explain why it is preferred to use an external stylesheet instead of an internal style…
A: Thoroughly explain why it is preferred to use an external stylesheet instead of an internal style…
Q: Suppose a computer using a 4-way set associative cache mapping scheme has a 20-bits memory address…
A: Here in this question we have given 4 way set associative cache mapping Memory size = 20 bit Block…
Q: Please explain the pros and cons of employing an internal static analysis.
A: At specified locations in the code, it may identify flaws. Certified software assurance developers…
Q: Question 11 mah .given the linear array AAA (5:50), BBB (-5:10), CCC (18) (i) find the number of…
A: Introduction: given the linear array AAA (5:50), BBB (-5:10), CCC (18) (i) find the number of…
Q: Complete the TODO function by converting the TPR equation into code so that we can compute the TPR…
A: Complete the TODO function by converting the TPR equation into code so that we can compute the TPR…
Q: To what extent can Deadlock Prevention only function if certain conditions are met?
A: Vital Factors To achieve standstill, it is necessary to meet the following four conditions: Mutual…
Q: When someone says "many processes" as opposed to "many threads," what exactly do they mean? I'd like…
A: Introduction: What does the phrase "many processes" really imply, as opposed to "many threads"?…
Q: Tell me about your experience using email. How many clicks do I need to do before my email is sent…
A: Introduction: This definition states that a mental model is an intuitive perception that a user has…
Q: Provide an explanation of how Project Benefits are realized. Detail the five (5) overarching,…
A: Introduction IT Enterprise: Hardware and software created specifically to satisfy the needs of a…
Q: Hello please solve the below in C++. I used the code provide by a Bartleby expert and I was marked…
A: The source code of main.cpp #include <iostream>using std::cout;#include "Rational.h"…
Step by step
Solved in 2 steps

- Take, for instance, an airline database using a technique called "snapshot isolation." If the airline's overall performance is enhanced, then non-serializable executions may be tolerated.Take, for instance, an airline database using a technique called "snapshot isolation." If the airline's overall performance improves, non-serializable executions may be tolerated.Is it conceivable that a single process may get stuck in a stalemate state? Justify your replies.
- How does encapsulation and decapsulation occur in the OSI model, and why is it important for data transmission?Even though there are supposed to be seven in the OSI reference model, that's not necessarily the case. Why would we want to use fewer layers if we can avoid it? Is there anything that may go wrong if we used fewer layers?Suppose (X[mX]+Y [mY ]) > 0. What can you infer about each of the four subproblems (namely, (X1, Y1), (X1, Y2), (X2, Y1), and (X2, Y2))? Clearly identify the ones that do not have to solved anymore, and those that still have to be solved. Briefly justify.
- A chain of many-to-one connections may be used as the building blocks for the construction of a link like the second course. Does the connection have a limit of many-to-one cardinality because of the limits imposed by the main key and the foreign key? What gives you reason to think that to be the case?(2)How many safe sequences are there for the above snapshot? Briefly justify your answer. (3)If P1 requests an additional instance of each of A and C, that is, P1's request becomes (2, 4, 6), will this request result in a deadlock? If the answer is no, give a safe sequence. If the answer is yes, identify the processes that will be involved in the deadlock. Show your work.10. Describe the behaviour of the following machine, which begins with a blank tape, with the machine in configuration α. Configuration Behavior m-config symbol operation final m-config α none R P1 β α 1 R P0 β α 0 HALT none β 1 R P1 α β 0 R P0 α
- Provide a case in favor of deep access as opposed to shallow access from the perspective of a programmer; try to sidestep a discussion of performance.There are distinctions between hard and symbolic linkages.iIllustrate how a binary semaphore can be used to implement mutual exclusion among n processes.

