Information First name: |Last name: Email Address: The Information you provide will be used in accordance with the terms of our Privacy Policy -Global Preferences Unsubscribe from All: Suspend Email for 90 Days: Delete All My laformation: O Receive an email outside of these subscription parameters? Contact Us for more information on why you received this communication Submit
Information First name: |Last name: Email Address: The Information you provide will be used in accordance with the terms of our Privacy Policy -Global Preferences Unsubscribe from All: Suspend Email for 90 Days: Delete All My laformation: O Receive an email outside of these subscription parameters? Contact Us for more information on why you received this communication Submit
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter1: An Introduction To Information Systems In Organizations
Section: Chapter Questions
Problem 2.2CTQ
Related questions
Question
Apply external styling to the form in the diagram below using html and css
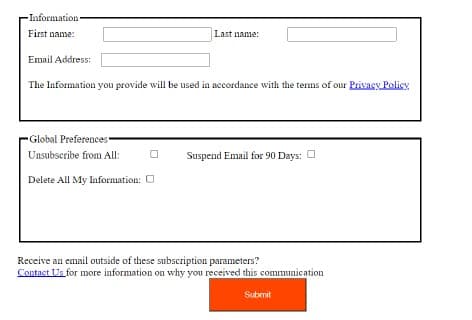
Transcribed Image Text:-Information
First name:
Last name:
Email Address:
The Information you provide will be used in accordance with the terms of our Privacy Policy
Global Preferences
Unsubscribe from All:
Suspend Email for 90 Days: O
Delete All My Information: O
Receive an email outside of these subscription parameters?
Contact Us for more information on why you received this communication
Submit
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,