information was taken. Upon further investigation that the server has now two admins, Precious and unknown individual named Teeh Mang. What possible malware infected the server? * It is possible that a Email Phishing malware was deployed in order to gain admin privileges O It is possible that a Worm malware was deployed in order to gain admin privileges O Option 5 O It is possible that Precious is the real imposter and Teeh Mang is the real admin O It is possible that a Rootkit malware was deployed in order to gain admin privilege
information was taken. Upon further investigation that the server has now two admins, Precious and unknown individual named Teeh Mang. What possible malware infected the server? * It is possible that a Email Phishing malware was deployed in order to gain admin privileges O It is possible that a Worm malware was deployed in order to gain admin privileges O Option 5 O It is possible that Precious is the real imposter and Teeh Mang is the real admin O It is possible that a Rootkit malware was deployed in order to gain admin privilege
Chapter7: Microsoft Edge
Section: Chapter Questions
Problem 3EYK
Related questions
Question
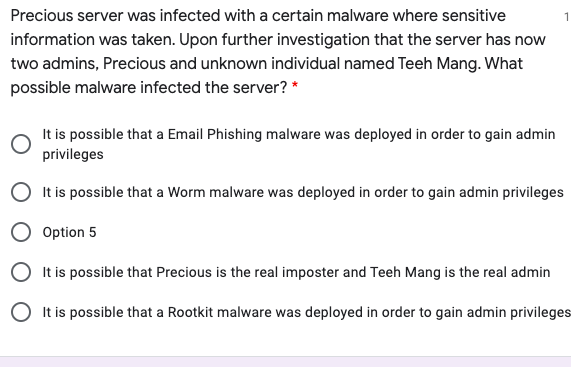
Transcribed Image Text:Precious server was infected with a certain malware where sensitive
1
information was taken. Upon further investigation that the server has now
two admins, Precious and unknown individual named Teeh Mang. What
possible malware infected the server? *
It is possible that a Email Phishing malware was deployed in order to gain admin
privileges
It is possible that a Worm malware was deployed in order to gain admin privileges
Option 5
O It is possible that Precious is the real imposter and Teeh Mang is the real admin
O It is possible that a Rootkit malware was deployed in order to gain admin privileges
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage