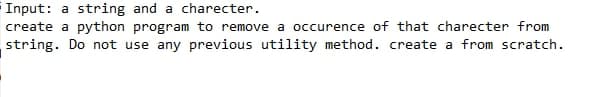
Input: a string and a charecter. create a python program to remove a occurence of that charecter from string. Do not use any previous utility method. create a from scratch.
Q: What's the difference between overridden methods in Java and those that aren't overwritten?…
A: Inspection: According to the question, the Java system allows for overriding and overloading…
Q: Provide an illustration of how each of the three characteristics of big data may be used to the data…
A: Big Data: Big Data is organised, semi-structured, or unstructured data created by mobile, online…
Q: 45.Given the prefix form % C* + AB/D E what is the root operation? A. + (Addition) B.…
A: Here you can see the given prefix is % C*+ A B/D E , theirs basic logic So, as we all known that the…
Q: DEFAULT STORAGE (INITIAL 500K NEXT 200K MAXEXTENTS 20 PCTINCREASE 15) Excel's Future Value financial…
A: The EXCEL financial function FV (rate, nper, pmt, [pv], [type]) can be used to calculate extent size…
Q: Outside of the administration of processes, what are the other two roles of the operating system…
A: The two important roles of OS are given below:
Q: When it comes to big data, what types of difficulties do clients often encounter
A: Introduction Big data is a method of gathering, storing, and analyzing large datasets, as well as a…
Q: 100n +5 € 0 (√) 100n +5 € O(n) _©_1+2+…+n-1+ne0(n) 4logn+n² FQ (n.)
A: Here in this question we have some expression in asymptomatic notation form.and we have asked that…
Q: Discuss a handful of Linux's features using your own words, if you are able to and if it is…
A: Please find the answer below :
Q: In this section, you will get familiar with the fundamentals of computer operating systems (OS)
A: The operating system (OS): The operating system (OS) is in charge of the computer's software and…
Q: What are some of the ways computers have advanced since the 1950s?
A: Intro The most significant advancement in computer technology from 1950 to 2021 is that older…
Q: Describe the network monitor 3.1 software, including its functionality and the many fields in which…
A: Network Monitor 3.1 software: Microsoft's Unclick software. *Download, install, and run are free.…
Q: What are the key differences between real-time and non-real-time operating systems and how do they…
A: Given: Real-time and non-real-time operating systems have different characteristics. A real-time…
Q: C++ programming Write a program to find the number of spaces to be inserted in the string input such…
A: Write a C++ program to find the number of spaces to be inserted in the string input such that no two…
Q: I would appreciate it if you could supply me with a list of the top five vulnerabilities in my…
A: Network security: Network security vulnerabilities are defects or weaknesses in the system's code,…
Q: In what ways might we anticipate seeing the framework for ethical reasoning used in the workplace in…
A: Given: In the future, what kind of employment will the ethical reasoning framework be used for?
Q: The way in which "facts" are presented in the media could be affected by the dredging of data.
A: Data dredging: Data fishing is another name for this practise, along with data spying and hacking.…
Q: As a person who has the ability to motivate and inspire technical people, you are known as explain?
A: Required: If you have the ability to motivate technically savvy people to perform up to their full…
Q: Examine the similarities and differences between mobile devices and cloud computing, as well as the…
A: Intro Similarities : Both are wireless to access any data. You can access data from anywhere. Both…
Q: C++ Chapter 7 - 1D Array - The 3n + 1 problem please solve the question new solution, don't copy…
A:
Q: The administration and troubleshooting of a network may be accomplished with the help of a number of…
A: Networking systems: Standard utilities and tools assist manage and diagnose network issues. In order…
Q: Could you help tell me the names of the three most common frequency bands used in wireless…
A: Intro Frequency Band: The lowest section of the electromagnetic spectrum, known as radio…
Q: How exactly can you do a requirements analysis for a training program using an online learning…
A: Start: Companies undertake need-gap analyses to determine the skills needed for competitive success,…
Q: In C++ language, every line of code must end with a semicolon. (True or False).
A: As per the question statement, We need to state true or false. Note: As per bartleby guidelines, I…
Q: Programming Practice Problem in C (Arrays and Strings): Implement substringList() that will produce…
A: #Code #include <stdio.h>#include <string.h>//main functionint main(){//initialize…
Q: It is important to look at the Access and Authentication aspects of Information Security.
A: Authentication and system access: Access to the system: Access control is a security approach that…
Q: Several experts in the field of cybersecurity argue that fingerprinting is unethical and infringes…
A: Intro Finger Print is unethical because it can steal by the third party and do some suspicious work…
Q: Find out how a user communicates with the mobile and desktop operating systems and compare the…
A: When it comes to user interaction, the following are the differences between mobile and desktop…
Q: Write a java program using nested loops to display the following patterns: b) 1 22 333 4444 55555
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT…
Q: The subject is software quality assurance testing. Assume you're working on a university system's…
A: Software testing: Software testing is defined as "the technique of examining and confirming that a…
Q: A "security breach" is the term used to describe an attack on a computer system.
A: Security breach: Any action that might put the safety of the data at risk is considered a security…
Q: Karnaugh maps and standard forms. For this function: F (A,B,C,D)= Σm (0,1,2,5,8,9,10) Do the…
A: The given function is : F (A,B,C,D)= Σm (0,1,2,5,8,9,10) The above is canonical sum of product form…
Q: What exactly is the function of SUS in Linux, and why is it so essential?
A: Given: The system that is presently being used to update Linux is known as SUS, which stands for…
Q: About the best case, worst case, and average case, which one of the following is NOT true? In…
A: 1. About the best, worst case, and average case, which one of the following is not True? "In…
Q: Use Python to find the regression equation of f(x) and write a code to find the values of a and b…
A: Task : Given the dataset. The task is to find the values of a and b using exponential data fitting.
Q: Many computer systems support race situations. Consider an organization's accounting system in which…
A: Intro For the most part, A race condition happens inside the basic segment. In OS terms basic…
Q: It's possible that having so many different kinds of information technology in the workplace will…
A: Integration and the whole firm perspective: It is difficult to obtain consensus on the requirement…
Q: What are some of the roles that a firewall plays? What sets it apart from other things? What use…
A: Dear learner, I'll do my best to address your question, and I hope you're doing well. Thank you very…
Q: What are the drawbacks of business networking, and what can be done to offset them? A number of…
A: Introduction: The disadvantages of corporate networking will be discussed, as well as some potential…
Q: Question 11 Explain the difference between Ethernet and Wi-Fi protocols used in LAN
A: Ethernet is primarily a standard communication protocol used to create local area networks. It…
Q: Describe how the computer architectures developed by Harvard and von Neumann vary from one another.
A: Computer Architecture The term Computer architectures refer to a set of rules stating how computer…
Q: Wireshark
A: Network traffic: Network traffic is also called as data traffic. It is the amount of data moving…
Q: In the business world of today, the phrase "big data" refers to a component of the information…
A: Introduction: In today's environment, big data has become an integral aspect of any organization's…
Q: In a medium-sized firm, at least three additional departments, including human resources, have…
A: Encryption: The purpose of having broad plans in place is to provide clarity to your…
Q: What precisely does the word "data mining" entail, and what different sorts of information may be…
A: Intro Tracking patterns Tracking patterns is a basic data mining technique. It entails detecting…
Q: What is the future of dependable software development?
A: Introduction: Many systems rely on software to function. Software is now the foundation of much more…
Q: The microkernel of the operating system is accessible for any design criteria that may be required.…
A: Intro Object-Oriented Programming: Object-Oriented Programming (OOP), and how does it function?…
Q: What is the function of the remote interface in the context of RMI implementation? Which…
A: To be determined: When it comes to the RMI implementation, what exactly is the purpose of the remote…
Q: Where should an anti-virus application be installed on a computer network with two servers and…
A: Given: The first of three security levels is necessary. An effective firewall that can prevent…
Q: What happens if I install a firewall on my PC and disable the Traffic Analysis and Traffic Alerts?
A: A firewall is very important for security as an anti-virus system. The firewall prevents malware…
Q: How does one go about developing the microkernel for an operating system, and what are some of the…
A: Given: What is the overarching philosophy that the microkernel adheres to? What is the most…
Step by step
Solved in 2 steps with 1 images

- INSTRUCTIONS: Write a Python script/code to do the given problems. EMOTIFY PROBLEM: Create a function that takes a string and returns a string with its letters in alphabetical order. Example: alphabet_soup(“hello") - ehllo alphabet_soup(“hacker") – acehkrTake a string from user and swap the, will the. And print the new string In pythonPython:Abbreviate the given string. But the string may contain some words(e.g. prepositions) that you need to ignore in the abbreviated form. Check the given examples input: 'islamic university of technology'output: 'IUT' input: 'Laser Interferometer Gravitational-Wave Observatory'output: 'LIGO
- Code in python : function that gives length of string.public static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current stringPython: Write a program that will take the string "Complication" and concatenate each successive letter, appending it to the existing string until the word is finished, The output should be as follows: C Co Com Comp Compl Compli Complic Complica Complicat Complicati Complicatio Complication Perform the program using a for and a while loop.
- Solve in Python: Write a program that removes all digits from the given input. Ex: If the input is: 1244Crescent the output is: Crescent The program must define and call the following function that takes a string as parameter and returns the string without any digits. def remove_digits(user_string)public static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current string.This problem is an exercise in Java string manipulation. For some mysterious reason, the Java String type does not come with a reverse method. The canonical way to reverse a Java string str is to first convert it to mutable StringBuilder, reverse its contents, and convert the result back to an immutable string, that is,str = new StringBuilder(str).reverse().toString(); Here's the tester it must pass: @Test public void testPancakeScramble() throws IOException {// Explicit test casesassertEquals("", P2J3.pancakeScramble(""));assertEquals("alu",…public static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current string. This problem is an exercise in Java string manipulation. For some mysterious reason, the Java String type does not come with a reverse method. The canonical way to reverse a Java string str is to first convert it to mutable StringBuilder, reverse its contents, and convert the result back to an immutable string, that is, str = new StringBuilder(str).reverse().tostring(); A bit convoluted, but does what is needed without fuss or muss. Maybe one day the Java strings will come with the reverse method built in, just like the string data types of all sensible…
- In Python, strings are mutable. True or FalsePython problem To decipher a code we must make a program that performs certain operations on the input string. -If they find 3 equal letters in a row, you must replace them with the next letter in the alphabet.-If you only find 2 equal letters in a row, you must replace them with the previous letter in the alphabet.-The comma must be removed-The period should be left and a space added after it.-All other characters should be left as isNote that in this case after the "Z" is the "A", and therefore before the "A" is the "Z". Given a string S, execute the operations described above, until no more can be executed. For example: GHHGP, OOOMMZAAZ => GGGPPLZZZ => HELLO EntryThe input will be a single line containing the string S. The string only includes uppercase letters of the English alphabet and special characters. DepartureYou must print the resulting string in double quotes ". Examples Input Example 1 LLLENTTA, JDDD OBCCBUMMTO!Output Example 1 "HIDDEN MESSAGE!" Input Example 2…TAKE A LIST OF STRING FROM THE USER AND COUNT THE NUMBER OF UNIQUE ELEMENTS WITHOUT USING THE FOR, WHILE, Do-WHILE LOOPS. PREFERRED PROGRAMMING LANGUAGE: JAVA/C++



