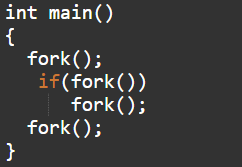
int main() { fork(); if(fork()) fork(); fork(); }
Q: Create an algorithm and a flowchart that will output all the prime numbers between 2 numbers. Use th...
A: Algorithm for Prime Number between two number i.e. Prime number are those number which has only two...
Q: l can deliver V
A: VoIP (Voice over Internet Protocol)VoIP (Voice over Internet Protocol) or internet telephony is the ...
Q: 1 get input n 2 set a variable num = 1 3 if num <= _(1)_, goto step 4, otherwise go to step 11 4 set...
A: This will be n because we only want to check from 1 to n, not after that. So when num exceeds n, we ...
Q: Perform the following Infix expressions to Prefix, Postfix and Binary Tree (for visualization) 1. x...
A: Infix expressions to Prefix, Postfix and Binary Tree
Q: ccurs in a at a position which is greater than or equal to start, and less than end. You must valida...
A: Code: import java.util.*;class ContainsInRange{ public static boolean validate(int arr[],int x,in...
Q: Trace through what values are stored in each variable as the code executes and what values will be d...
A: inputs : country = Nassau credits = 10 ========= Program: ========= country = input('Enter the ...
Q: 8 Choose the correct option(s). There may be multiplê correct choices. For every loop, we can replac...
A: For every recursive function, we can replace it with a loop with equivalent program flow. A recursiv...
Q: Create an algorithm and a flowchart that will output the Fibonacci series up to a given number. Use ...
A: Step 1: Start Step 2: declare variables a, b, c, i Step 3: assign initial values to a = 0, b = 1, ...
Q: the Root Bridge is elected in Spanning Tree Protocol. b) Explain how the root port (RP) is selecte...
A: Unnecessary links are used to provide a backup copy where one link goes down but the Inactive link c...
Q: A file concordance tracks the unique words in a file and their frequencies. Write a program that dis...
A: Introduction: A file concordance tracks the unique words in a file and their frequencies. Write a pr...
Q: For each of the following simulation applications identify one discrete and one continuous-change st...
A: arrow_forward Step 1 Before identifying which variables are discrete and which are continuous, let i...
Q: To declare an interface named A with two generic types, use a. public interface A(E, F) { } ... b. p...
A: Given:
Q: Explain the components of the spheres of security paradigm in detail. Each component should be expl...
A: The spheres of security paradigm were originally proposed by Michael Witte and Michael Nollwitz in 1...
Q: Morning fam:) Would truly appreciate for your help on this one. Given the parameters : a = 22, b = ...
A: One of the algorithms used to generate false random numbers is Linear Congruential Generator.
Q: Suppose you were to open a shift register component. Inside you would notice two (2) registers. Iden...
A: Ans: You were to open a shift register components ,inside it noticed that it has two internal regist...
Q: establish a method for selecting cybersecurity items on the market'
A: INTRODUCTION: The technique of securing systems, networks, and programs from digital threats is kno...
Q: Create a single-page web application such that it reads a request parameter given in the URL that sp...
A: The program is written in HTML, CSS and Javascript. Check the program screenshot for the correct ind...
Q: e a program to take input a 4 X 4 matrix using a user defined function and print the
A: Lets see the solution.
Q: Five forms of DoS attacks are listed below.
A: EXPLANATION AND ANSWER: Denial of Service (Dos) attack : A denial of service attack is an aggressive...
Q: short answer Tell me why most of mobile carriers separate the Phone Plan Enrollment Process and Mont...
A: What is Mobile Carriers ? A telecommunication service provider who provides having...
Q: Explain the components of the spheres of security paradigm in detail.
A: Introduction: Information security is primarily concerned with preventing unwanted access to data. I...
Q: In the same way Write a C# program to check whether : inputted number is positive or negative
A: Lets see the solution.
Q: Prove that the language L = {{M,N): M, N are TMs such that (M) E L(N) iff (N) E L(M)} is undecidable...
A: The language L = {(M, N): M, N are TMs such that (M) ε L(N) iff (N) ε L(M)} is undecidable. M is in...
Q: Explain your personal knowledge of In-House Development in your own words.
A: Answer : A group of individual dwellings or apartment houses typically of similar design are usuall...
Q: JAVAFX: Allowed functions for drawing (Ellipse2D,CubicCurve,QuadCurve,Arc2D) [draw all of these shap...
A: In questions with many questions, we must answer one. Here is an implementation.
Q: Given the following recurrence relations, what is the expected worst-case time complexity
A:
Q: Write a program that takes in a positive integer as input, and outputs a string of 1's and 0's repre...
A: The while loop is used to iterate a part of the program repeatedly until the specified Boolean condi...
Q: How are data communicated between components?
A: 1. Data communication is the exchange of data between two devices through a transmission medium. In...
Q: write code to determine if the first character in an input string str is an uppercase character.if t...
A: - We have to code for the uppercase checking problem. - We are using C++ here.
Q: What exactly is the Internet Explorer Box Model Bug, and how does it impact you?
A: Introduction: The Internet Explorer box model vulnerability is a well-known flaw in the implementati...
Q: In this state diagram, are they anything you would consider incorrect and why ? a verb E. C do: a ve...
A: Actually, given question regarding state diagram.
Q: What is the difference between a Microsoft Access database and an Excel spreadsheet based on their c...
A: Introduction: Spreadsheet in Microsoft ExcelMicrosoft Excel is used to show the data in horizontal a...
Q: When going through a section, try the Self-check exercises. The solutions are given at the end of ea...
A:
Q: Choose the correct option(s). There may be more than one correct option. 1. Structuring large progra...
A: 1. Structuring large programs may involve separation of function prototypes and definitions. 2. Stru...
Q: below an OSPF topology (Figure 2). Identify all types of routers in this OSPF topology. d) What is...
A: As per guidelines, we can only solve one question at a time . Hence resubmit the question for furthe...
Q: Write code in java to solve the following problems. Question 1: Most important Class in Customer Rel...
A: The get method is used to obtain or retrieve a particular variable value from a class. A set value ...
Q: What are the Consequences of a Lack of Communication Devices?
A: Introduction: A communication device is a piece of hardware that can send an analog or digital signa...
Q: In this c++ program. Create a flowchart and algorithm. Source Code: #include using namespace std; ...
A: Flow Chart of Reverse a number
Q: IP addressing technique subnets a subnet to make smaller subnets?
A: Here we have to answer the IP addressing technique that subnets a subnet to make smaller subnets.
Q: explain how linkedlist different from arrays.
A: Given :- Explain how Linked list is different from array .
Q: What are the most significant characteristics of a computer processor?
A: Introduction: The logic circuitry that listens to and executes the fundamental instructions that ope...
Q: Insert the missing part of the code below to output the string.
A: The above program is for printing the string in java . For printing a string in java we use System.o...
Q: Q9) To store/represent a 3D sphere as model-based computer graphics object in my computer I need a m...
A: Introduction: Parametric Equation of an Ellipse: The parametric formula of an Ellipse - at (0, 0) wi...
Q: at aspect of any company, product or team interests you m
A: Lets see the solution.
Q: Static analyzer write code python read text and check Do the attributes (e.g., data type and size) ...
A: The answer as given below;
Q: Write a python code (i) code to interface A0 of NodeMCU with MQ-02. (ii) Initialisation steps for ...
A: # import module import os # scan available Wifi networks os.system('cmd /c "netsh wlan show networks...
Q: Consider the main memory with capacity of 3 frames assume that the page of process are referred in t...
A: Here in this question we have 3 frame and pages of the process are referred.and there we are using t...
Q: Java Consider the following class definition for an array-based stack implementation: pubic clas...
A: import java.util.Scanner; class Stack{ private int[] m_array; private int m_index; ...
Q: 15. In this c++ program. Create a flowchart and algorithm. Source Code: #include using namespace ...
A:
Computer Science
Find the total number of created processes with the parent and draw a tree diagram explaining it.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images


