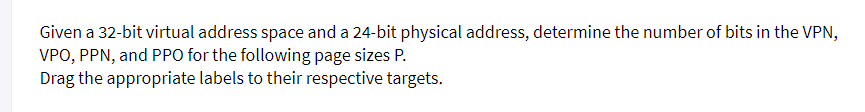
irtual address space and a 24-bit physical address, determ PPO for the following page sizes P.
Q: How can Access Security Software protect your data?
A: Access security software is designed to protect data by controlling and monitoring who can access…
Q: Simulate in R the delta variation by SIR model. - Produce the code in R
A: Please check out the coding below
Q: How can Direct Memory Access (DMA) increase system concurrency? Is there a barrier to technological…
A: Computer Memory:It is the physical devices which is used to store data, instructions and program…
Q: How does one attain "digital literacy"?
A: This means having the skills to use and navigate digital technology, such as computer, smartphones,…
Q: Why wouldn't email providers monitor client messages?
A: Email is used to send a lot of private, confidential, and professional information. Thus it ought to…
Q: python
A: # import the turtleimport turtle# make the turtle objectt = turtle.Turtle()# make the turtle speed…
Q: Data security and privacy may seem incompatible.
A: Given,Data security and privacy may seem incompatible.
Q: What do we know about database architectures and schemas? Why bother starting a database?
A: What is database: A database is a structured collection of data that is organized and stored in a…
Q: Determine which data security best practises to implement. (Digital privacy and encryption)
A: Data protection has become a dangerous concern inside the modern cardinal age. As more and more…
Q: Is cloud-based collaboration technology deployable in various settings? How can cloud collaboration…
A: Cloud-based collaboration technology refers to the use of cloud computing platforms and tools to…
Q: When using JavaScript, what kinds of events might you expect? Make use of the onclick event by…
A: Your answer is given below.
Q: Suggestions for the company Design or choose a system to help the company solve its main…
A: In the given question, we are asked to design or choose a system to help the company Almarai in…
Q: Linux rocketry apps.
A: There are several Linux applications available for rocketry enthusiasts. Here are a few popular…
Q: What malware do you think is most dangerous and why
A: Ransomware is considered one of the most dangerous forms of malware due to its ability to cause…
Q: Give six PLD programmable connection process technologies.
A: HiProgrammable Logic Devices (PLDs) are integrated circuits that can be programmed and configured to…
Q: Compare popular server OSes.
A: Operating systems are vital server infrastructure components as connection points for hardware and…
Q: Document hashing. Hash tables, collision detection, and temporal complexity. Hashing app. Any native…
A: The process of creating a unique digital fingerprint, or hash, from a document or file based on its…
Q: Please describe the InfoSec course curriculum in computer science.
A: The answer is given below step.
Q: There are still a lot of unknowns about operating systems and how they do what they are supposed to…
A: An (OS) is a critical software constituent that manages central meting out unit hardware and provide…
Q: Learn about virtualization's language, operating system, and hardware impacts.
A: In this question we have to understand to learn about virtualization language, operating system and…
Q: he idea of computing everywhere is interesting, but how does it actually work?
A: The concept of computing everywhere refers to the integration of computing capabilities into various…
Q: Why not train everyone and start utilising the new computer system instead of potentially…
A: When implementing a new computer system, it may appear rational to train everyone in the…
Q: Most practical computer systems don't follow the OSI model's layer count. Computer system…
A: The Open System Interconnection (OSI) model is pictorial that standardizes the function of a network…
Q: This chapter covers WiMAX. Recent articles explain WiMAX technology. List commercial barriers and…
A: In wireless networking, WiMAX stands for Worldwide Interoperability for Microwave Access. The…
Q: Explain CentOS's advantages.
A: CentOS (Community Enterprise Operating System) is a free and open-source Linux distribution in light…
Q: Compare popular server OSes.
A: A server (OS) is a software layer on a server that allow application to boundary with hardware and…
Q: Which factor is most crucial before switching to a batch-processing system? You may explain your…
A: Processing transactions in a group, often known as a batch, is called batch processing. Once batch…
Q: Define "technical documentation" first. Is there a table comparing and contrasting the four most…
A: Technical documentation refers to the written materials that provide detailed information about a…
Q: Explain your software development metrics. Is it necessary to describe every little detail?
A: What is software development: Software development is the process of designing, coding, testing, and…
Q: 4.) Suppose that a sender and a receiver are using ARQ to perform reliable data delivery. If we…
A: GivenSuppose that a sender and a receiver are using ARQ to perform reliable data delivery. If we…
Q: Draw an overall activity diagram in draw.io format based on the scenario given (screenshot it to me)…
A: Answers:-The activity diagram for the student subject registration process can be outlined as…
Q: Discover which industries use web technology and examine its development, testing, and maintenance…
A: Web technology has become integral to various industries, enabling businesses to reach wider…
Q: First things first, we need to come up with a working meaning of virtualization and distinguish…
A: The basic idea of virtualization in computer discipline allows for the imitation of actual hardware…
Q: Information Security Access and Authentication subsystems must be considered.
A: Access and Authentication subsystems are crucial elements in IS. admission ensures that simply…
Q: Why is encapsulation necessary in object-oriented development?
A: Encapsulation is necessary in object-oriented development for data protection, modularity, code…
Q: What causes cabled connections to be quicker than wireless ones?
A: Cabled associations, like Ethernet, are typically more speedily and more reliable than Wireless ones…
Q: Can you please explain the DFA and NFA?
A: Given,Can you please explain the DFA and NFA?
Q: Write a SQL query that retrieves the names and email addresses of all students who are enrolled in…
A: Step 1: Create the table students with the attributes student_id, name, email, major, and…
Q: Your computer science professor advised you to compare object-oriented system components to ordinary…
A: Object-oriented system components are the fundamental building blocks of object-oriented…
Q: Mafiaboy's online investigation methods He didn't want his website's creation revealed. I'm curious…
A: Mafiaboy, a notorious hacker, gained notoriety for his high-profile cyberattacks in the early 2000s.…
Q: rite names of two character codes used to represent text data in memory
A: In the world of computer programming, various character encoding schemes are used to represent text…
Q: OS middleware advantages. Document distributed and network operating system competence.
A: 1. Middleware in Operating Systems: Understanding the ConceptMiddleware in operating systems serves…
Q: lease give background information to understand the authentication challenge-response procedure.…
A: In the realm of digital security, the authentication challenge-response procedure plays a vital role…
Q: Identify each authentication's risks and provide a solution. Bob compares a hashed password against…
A: Risk: The main consequence associated with this authentication method is that an attacker could…
Q: Why are new systems expensive and dangerous?
A: The costs and dangers of new computer systems are frequently substantial. Significant funds must be…
Q: Multiprocessor systems provide adaptability. Though advantageous, this feature increases system…
A: Systems with a lot of processors, from time to time called parallel computer or equivalent…
Q: We DFS the directed graph Gd, where G is the depths-first tree/forest. G will be cycle-free if all…
A: Directed graphs are essential data structures in computer science that model a wide range of…
Q: No responsible individual in your audience would deny the importance of software engineering and…
A: Software engineering and quality assurance play crucial roles in the development and maintenance of…
Q: What long-term planning may produce legacy systems? When is replacing a system component cheaper…
A: software development, long-term planning plays a crucial role in determining the fate of systems and…
Q: Firewalls affect network and internet security. Define the phrase, then use facts and examples to…
A: What is Firewalls: Firewalls are security devices or software that act as a protective barrier…
posting so so so many multiple times dont dont dont answer if not 100% sure else will send compliant to bartleby team for sure very strictly telling dont dont waste my question and dont dont answer very strict warninggg
Step by step
Solved in 3 steps

- Given a 32-bit virtual address space and a 24-bit physical address, determine the number of bits in the VPN, VPO, PPN, and PPO for the following page sizes P. Drag the appropriate labels to their respective targets.Suppose the virtual address width is 32 bits. Also suppose that the virtual and physical page size is 4Kbytes. If the physical address limit is 220, what is the number of bits in the Physical frame part of the physical address?Assume a 32-bit virtual address and 4 MBs of memory (i.e., DRAM). If the page size is 1 KB, then what is the size of the page table (ignoring any permission or other overhead bits)?
- In an architecture with 18 bits of "virtual address" width, "page size" is given as 1024 bytes and "physical address" width is given as 15 bits. TLB has a “2-way set associative” structure and contains a total of 16 data blocks. What is the TLB Tag field width in this architecture? A) 4 B) 5 C) 6 D) 7 E) 8Determine the number of page table entries (PTEs) that areneeded for the following combinations of virtual address size(n) and page size (P):Assume a 32-bit address system that uses a paged virtual memory, with a page size of 2 KB, and a PTE (Page Table Entry) size of 1 B. Answer the following questions, assuming a virtual address 0x00030f40 a. What is the virtual page number (VPN) and the offset in binary for the given virtual address? b. How many virtual pages are there in the system?
- Consider a logical address space of 256 pages with a 4-KB page size, mapped onto a physical memory of 64 frames. a. How many bits are required in the logical address? b. How many bits are required in the physical address?Fill in blank Suppose that linear page table is used where the memory addresses are 12-bit binary numbers and the page size is 256 bytes. If a virtual address in binary format is 101000011100, then the VPN (virtual page number) in binary format will be ---------Suppose that a machine has 38-bit virtual addresses and 32-bit physical addresses.(a) What is the main advantage of a multilevel page table over a single-level one?(b) With a two-level page table, 16-KB pages, and 4-byte entries, how many bits should be allocated for the top-level page table field and how many for the next-level page table field? Explain.
- Consider a logical address space of 512 pages with a 2-KB page size, mapped onto a physical memory of 64 frames. How many bits are required in the logical address?Assume a 32-bit address system that uses a paged virtual memory, with a page size of 2 KB. Answer the following questions, assuming a virtual address 0x00030f40 A. What is the virtual page number (VPN) and the offset in binary for the given virtual address? B. How many virtual pages are there in the system?Suppose you have a byte-addressable virtual address memory system with 16 virtual pages of 64 bytes each and 4-page frames. Assuming the following page table, answer the questions below: Page # Frame # Valid bit 0 2 1 1 3 1 2 - 0 3 0 0 4 1 1 5 - 0 6 - 0 7 - 0 A. What physical address corresponds to the virtual address 0x42? Answer should be in hexadecimal number. (if the address causes a page fault, answer as "page fault" with the proper explanation) B. What physical address corresponds to the virtual address 0x72? Answer should be in hexadecimal number. (if the address causes a page fault, answer as "page fault" with the proper explanation) C. What physical address corresponds to the virtual address 0x84? Answer should be in hexadecimal number. (if the address causes a page fault, answer as "page fault" with the proper explanation)

