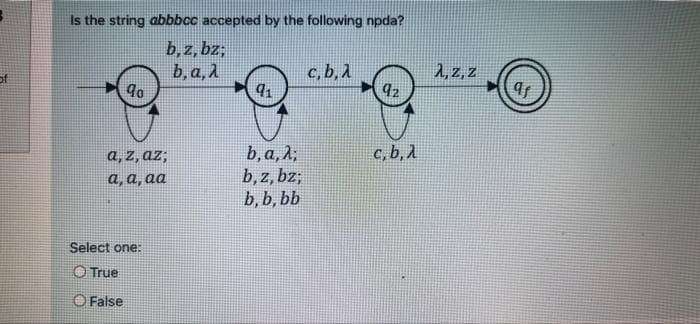
Is the string abbbcc accepted by the following npda? b,z, bz; ь, а, 1 c, b, 1 92 2, z, z c, b, A a, z, az3; а, а, аа b, a, λ, b, z, bz; b, b, bb Select one: O True O False
Q: Create -commerce
A: The program is written in HTML and CSS. Check the program screenshot for the correct indentation.…
Q: To improve performance, your organization has elected to clone its product database over multiple…
A: INITIATION: It is occasionally necessary to copy a database from one computer to another, whether…
Q: What distinguishes the TPC from the SPEC in terms of its emphasis?
A: SPEC and TPC: The Transaction Procession Council (TPC) is a non-profit organization that creates…
Q: A computer production company "HP" wishes to produce three types of electronic devices type A, B and…
A: Code: A=[4 2 4];B=[2 6 2];C=[2 4 6];…
Q: 1. depends on pseudo code described algorithm below find primes up to N in java rogramming language.
A: Code: import java.util.Arrays;public class FindPrimes { public static void printPrimeUpto(int N){…
Q: Your task is to take the list from the user and then print all the elements which appeared at even…
A: The Python Code is: # Initialising List nums = [] print("Enter 10 Numbers: ") #Loop to get 10…
Q: Which application is used to setup IPsec between two computers and how is it done?
A: The following will be determined: What application is used to establish an IPsec connection between…
Q: Computer Science 5-Using a table similar to that shown in Figure 3.10, calculate 35 divided by 11…
A:
Q: What is 360 degree feedback? Write It's features. How valid do you believe it be?
A: 360 degree feedback is a special type of mechanism for getting reviews for an employee.
Q: In what circumstances do you think assembly language code should be used in the creation of an…
A: Assembly language : An assembly language is a low-level programming language used to communicate…
Q: What benefits and problems does the corporate sector confront as a result of the paradigm change…
A: Paradigm ShiftTo begin, Consider the following definition of paradigm shift: It represents a…
Q: Why Python is an excellent programming language for machine learning and artificial intelligence.
A: Python is the best programming language for research and development in machine learning and…
Q: What are the flaws in a secret cryptography technique's design?
A: Institution: The fact that a single key is utilized for both encryption and decryption is a…
Q: This section will discuss the OSI layer, its operations, and the protocols that operate at each…
A: Introduction: The Open Systems Interconnection (OSI) model is a seven-layer diagram that represents…
Q: why More than sample rate (samples/sec), bit depth (sample size) affects the size of digital sound…
A: Introduction: Hardware and software are the two components of a computer system. The actual and…
Q: What exactly do the terms "digital data" and "digital device" refer to?
A: Definition: A computer or microcontroller contained in a physical item of equipment. A smartphone,…
Q: What is the most critical phase in the data science process?
A: Analyzing and interpreting data is a critical stage in data science.
Q: Extend the language and compile
A: Extend the language and compiler to accept initialized declarations such as int i = j + 32; Doing…
Q: Why is it not necessary for a program to be totally defect-free before being provided to its…
A: Introduction: It is not required to be defect-free before it is supplied to its clients since it is…
Q: In a new application program, how would you determine whether to utilize an ORM framework or a…
A: Introduction: JDBC stands for Java database connectivity and it is an application programming…
Q: What exactly is multimode fibre (MMF)?
A: Introduction: Multimode fiber is an optical fiber that is used for short-distance communication,…
Q: Some databases employ magnetic disks in such a manner that only the outside tracks are utilised,…
A: Advantages of using outside tracks for processing: The data transmission rate of the disc will be…
Q: Explain the stack pointer register in simple terms
A: Below diagram of stack organization (for 64- word stack )will exactly show the purpose , motive ,…
Q: What primary InfoSec functions would you recommend for a small organization with three full-time…
A: The InfoSec program is responsible for developing, implementing, and maintaining an information…
Q: Distinguish between private and public-key cryptography. Include examples of when and why you may…
A: The data or information is encrypted and decrypted using the private key. The sender and receiver of…
Q: Write a C++ program to print the count of word (the) as a separate word in a file named…
A: Please upvote. I am providing you the correct answer below.
Q: You've learned about numerous black box testing approaches including performance testing, stress…
A: Performance Testing : Performance testing is a kind of software testing that determines a software…
Q: With respect to 8051 microcontroller, the programming address of TF0 and IEO of a timer control…
A: Solution : The 8051 Microcontroller Special Function Registers serve as a control table for…
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: According to the information given:- We have write a program to read 2 string sp_top and sp_bottom…
Q: 2. Using suitable command encode the message "Your Name" by using matrix A given below: [1 2 31 A =…
A: Find the required code in matlab and output given as below :
Q: lease review this SQL trigger and let me know why instead of just updating the CS_Loyalty level for…
A: First, let's understand how the trigger works? A trigger is a unique form of stored system that…
Q: Explain and list the features of Ubuntu Server in terms of server operating systems.
A: Introduction: Ubuntu is an operating system based on Linux. It is intended for use with PCs,…
Q: Write a void function named squarelt that takes one double variable as a reference parameter and…
A: #include <stdio.h>//function squarelt//that takes reference of variable number//and replace…
Q: What does "reduced" mean in terms of a computer's limited instruction set?
A: Introduction: When compared complicated instruction set computers, the instruction set architecture…
Q: Q3/ Suppose a movie theater has 36 seats, laid out in a rectangular six rows by six seats. Let the…
A: Use if-else to check row and seat and print price accordingly.
Q: How are truly distributed systems modeled?
A: gdfn A distributed system uses resources from different system located on multiple networks.…
Q: Explain what a normalized finite number is in a few of sentences.
A: Solution:-
Q: Explain how functional dependencies may be used to indicate: • The entity sets student and teacher…
A: Justification: A functional dependence is an attribute-to-attribute link. We may get the value of…
Q: What effect does the remapping of damaged sectors by disk controllers have on the retrieval rate of…
A: When there is no written or accessible format on a disc sector as a result of some irreversible…
Q: n between computer and network security and the many types of malware. Is there a virus kind that,…
A: Introduction To ensure confidentiality, integrity, and availability in a system environment, a user…
Q: Design a program using a console application in java NetBeans, named studentMarksReport that will…
A: Student class: student no test result assignment result exam result constructor should accepts…
Q: What is the structure of the DRAM cache?
A: DRAM Cache organization: DRAM reserves have emerged as an essential new layer in the memory chain to…
Q: Assume a user establishes a new relation r1 that has a foreign key that points to another relation…
A: Foreign key: It is a collection of attributes in a table that relates to another table's primary…
Q: Why would a page fault try to continue execution at the current instruction?
A: When a page fault occurs, control is shifted to the instruction that is now being executed.In…
Q: Explain what occurs if an exception isn't caught in Java.
A: Introduction: In Java, an exception is an occurrence that disrupts the usual flow of programme…
Q: In comparison to hardware-defined networking, what are the two most significant benefits of software…
A: Networking: It is defined as the process of establishing contact and exchanging information with…
Q: Write a python program that will produce the count of apples in each pile. To do this, I want you to…
A: What is Loop Sometimes we need to run…
Q: In what circumstances did the RISC architectural concept come to be developed?
A: RISC (Reduced Instruction Set Computer): RISC architectures are a significant advancement in the…
Q: What are the benefits and drawbacks of various access methods based on random access? Why does the…
A: Time is not fixed for sending the data: Multiple Access Protocol The Data Link Layer is in charge…
Q: Explain how to decode an instruction in a few words.
A: Stage of decoding: The decoding process helps the CPU to figure out what instruction is being…
Step by step
Solved in 2 steps with 1 images

- - Consider CFG G = ({S}, {a, b, c}, R, S) where R = {S → SbbS | SacS | a}. Show how the string abbaacabba - What cause ambiguity?dont dont dont copy existing one strict waring answer only sure else skipTy for ur answer. I have a different sequence: is ther a reason u "prioritice" g before b or is it both right?
- Is ~p→(q biconditional p) a tautology, a contingency, or a contradiction? Is (p→q)∧(q→p) logically equivalent to ~(p→q)∨(q biconditional p)?Construct truth table and identify if it’s tautology, contradiction, or contingency. (a) [(p V q) ∧ r] → [(p V r) ∧ (q V r)] (b) ((p → r) Ʌ (r → q)) → (q → p)Determine whether the following is true or false. Please cite the brief explanation so that I can know why is it true or false. A) 1 ∈ {{1},{2},{3}} B) A\B = A ∩ B^c C) The contrapositive of p -> (p V ¬p) = (¬p∧ q) -> ¬p
- i need answer of all. if any answer will be skipped, your answer will be rejected. only complete answer will be accepted. b) Make a truth table for the statement ¬P ∧ (Q → P). What can youconclude about P and Q if you know the statement is true? a) Make a truth table for the statement (P ∨ Q) → (P ∧ Q). c) Make a truth table for the statement ¬P → (Q ∧ R).Construct a truth table for (p ∨ ¬ q) ∨ (¬ p ∧ q) Use the truth table that you constructed in part 1 to determine the truth value of (p ∨¬q) ∨ (¬ p ∧ q), given that p is true and q is false. Determine whether the given statement is a tautology, contradiction, or contingency. p V (~p V q) ~ (p ∧ q) ~p V ~qDetermine the validity of the following arguments using truth tables. Which confluence of truth values shows its invalidity? 1. A ⇒BB ⇒A -----------∴A ⇒B 2. (E ∨R ) ∧(E ∨T)R ∧T ------------∴E 3. (O ∨P) ⇒JO ∨¬JP ∨¬JO ⇔¬P -----------∴J ∧¬J
- According to some political pundits, a person who is radical (R) is electable (E) if he/she is conservative (C), but otherwise is not electable.1. Which of the following are correct representations of this assertion?1. (R∧E)⟺C2. R⇒(E⟺C)3. R⇒((C⇒E)∨¬E)2. Which of the sentences in (a) can be expressed in Horn form?What is the Left-most & Right-most Derivations For the CFG: E => E+E | E*E | (E) | F F => aF | bF | 0F | 1F | e Derive the string a*(ab+10) from G:Q3) Solve each of the following: a) (0 10011000 10000100010100110000000)Floating Point = (?)2 b) If A = 10101010, B = 01010101, and C = 00110011, then find X = A ∨ B ∧ ¬C c) Create a truth table for the Boolean function Y = ¬(A ∧ Β). d) Using the value –128, write it as an integer literal in decimal, hexadecimal, and binary formats that are consistent with MASM syntax. e) Write the real number –7.823 × 10-38 as a real number literal using MASM syntax.

