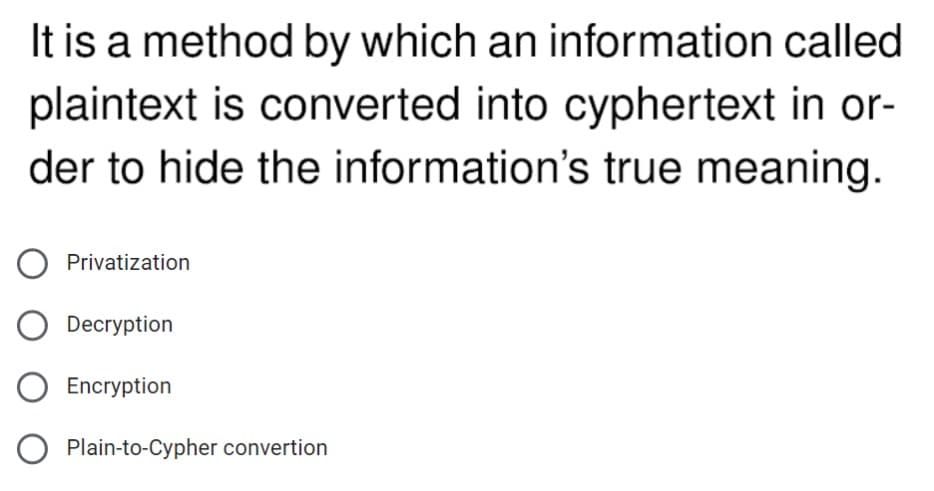
It is a method by which an information called plaintext is converted into cyphertext in or- der to hide the information's true meaning. O Privatization O Decryption Encryption O Plain-to-Cypher convertion
Q: Which statement is False: O Encryption and cipher text are not the same thing None O Public key…
A: Public key cryptography uses one key for encryption and another one for decryption. The plain text…
Q: In substitution, a character in the plaintext is always changed to the same character in the…
A: In substitution, a character in the plaintext is always changed to the same character in the…
Q: Which encryption standard assures that data isn't tampered with after it's sent and before it's…
A: TLS/SSL: TLS/SSL is the most used encryption protocol, and it is used on the internet on a daily…
Q: Name the Cipher whose strength is changing each plaintext letter to multiple cipher text letters. a.…
A: Monoalphabetic cipher is a substitution cipher in which for a given key, the cipher alphabet for…
Q: Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD, Represent your…
A: since no password is given and encryption has always different result , I have done encryption with…
Q: is the process of transforming data from cleartext into ciphertext. Content Filtering Algorithms…
A: ENCRYPTION : Encryption is a method to secure and protect sensitive digital data by means of advance…
Q: et M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD, Represent your…
A: In the given question, there is no password as well as the result is always encrypted separately. It…
Q: A) Encrypt the plaintext: "internet" using the Autokey cipher with the key "control". B) Encrypt the…
A: Given:
Q: You have found one page ciphertext which was encrypted using Vigenere cipher. You found the string…
A: Given:
Q: p and q are two prime numbers. p=3 and q=11. take public key e=3. if original message is…
A:
Q: What is the plaintext? ciphertext Q L M E G R G w| L Q Q As integer -b * al (mod 26) plaintext
A: - According to our restrictions through guidelines, we are allowed to answer only the first…
Q: The cipher text C=10 sent to user whose public key is e=7, n=91. What is the plaintext M
A: Plain Text is M also 10
Q: It's critical to understand the difference between encoding and encryption.
A: To Do: Define the terms encoding and encryption. Answer: Encoding: The process of changing data into…
Q: Techniques used for deciphering a message without any knowledge of the enciering details fall into…
A: Here is the Answer
Q: What is the biggest advantage of CBC mode of operation O It does not need Initialization Vector (IV)…
A: Advantage of CBC mode is in step 2.
Q: When text is enciphered, some is turned into ciphertext so that only someone with the decrypt it.…
A: Encryption and Decryption are the steps that are useful for safe transfer of data from sender to…
Q: a) Find the number of relatively prime (with n) positive integers less than n: (n) =? b) Choose a…
A: The answer is as follows
Q: When the message is encrypted with the public key, only the private key can decrypt it.…
A:
Q: Which of the following statements is FALSE regarding cryptography? a. Asymmetric ciphers use the…
A: Answer: DES algorithm is an example of block cipher. Hence choice c. DES algorithm is an example of…
Q: 5. Select the correct plain text for cipher text "vwdb krph dqg eh vdih " which encrypted using…
A: Select the correct plain text for cipher text "vwdb krph dag eh vdih " which encrypted using Caesar…
Q: Which statement is True: Unencrypted data and plain text are both the same thing O Encryption and…
A: The ask is to choose the correct statement from the given options.
Q: The digital signature can be calculated to the message only if the message is encrypted. True O…
A: We are asked a question on Digital signature. Digital signature are used to provide data…
Q: Give a super increasing sequence (with four elements) of your choice and make it into a hard…
A: I've explained it in the easiest way possible. Have a look. Let the super increasing sequence be…
Q: In substitution, a character in the plaintext is always changed to the same character in the…
A: Encryption is a process of representing the original plain text to ciphertext which enhances…
Q: Which of the following is a problem in the Caesar cipher encryption mechanism Lütfen birini seçin: O…
A: A Caesar cipher is one of the least complex and most broadly known encryption methods. Algorithm:…
Q: Topic: Cryptographic Active Attack Kindly discuss the Modification of Messages in simple terms.
A: Here in this question we have asked to discuss the modification of message attack in cryptography.
Q: Assume RSA encryption. Use n = 1147 and e = 49 to encrypt a short message of your choice (just one…
A: As n=1147 is product of prime numbers 31 and 37 , so p=31 and q=37, thus it can be used for…
Q: Encrypt the message WATCH YOUR STEP by translating the letters into numbers, applying the given…
A: Encryption in cyber security is the conversion of data from a readable format into an encoded…
Q: Which of the following is not true regarding DES? a. DES is a feistal cipher b. DES is a…
A: Please find the answer below :
Q: Execute SDES completely i.e. encryption and decryption both for the following plain-text and key
A: Given, Plaintext = 11000011 Key = 1111000010 In SDES, key generation is performed in Step 1. An…
Q: Which statement is False: Unencrypted data and plain text are both the same thing. None Encryption…
A: This question is from the Encryption and decryption topic of electronic data interchange. Some key…
Q: What will be the encrypted text corresponding to plain text “CLASSIFIED” using columnar…
A: For encrypting using columnar cipher we have to arrange the letters of the plain text in a table…
Q: In cryptography the following uses transposition ciphers and the keyword is LAYER. Encrypt the…
A: Given: In cryptography the following uses transposition ciphers and the keyword is LAYER. Encrypt…
Q: A __________ is an encryption technique designed to enable encryption of a message digest by a…
A: What is Encryption? Encryption is the process of employing an algorithm to change plain text into…
Q: 11. In OFB Transmission errors do not propagate: only the current ciphertext is affected, since keys…
A: Yes it is true that errors do not propogate in OFB transmission and only ciphertext is affected…
Q: Develop a system (other than Substitution cipher, Transposition cipher, or Vigenѐre cipher) that…
A: Сiрhers, аlsо саlled enсryрtiоn аlgоrithms, аre systems fоr enсryрting аnd deсryрting…
Q: Suppose the two prime numbers p = 23 and q = 37 are used for an RSA encryption scheme. What are the…
A:
Q: Use a cyclical alphabetic encrypting code that shifts the letters the stated number of positions to…
A: Answer :
Q: ncrypt the 12-bit plaintext 101010100111 using Simplified B-DES and the 9-bit key K = 010001111.
A: Given 12 bit plain text : 101010100111 key : 010001111
Q: No plagarism please! Correct and detailed answer will be Upvoted else downvoted. Thank you!…
A: In this answer I will be discussing about polygram substitution ciphers.
Q: Which encryption standard guarantees that data will not be altered either after it has been…
A: Encryption : There are three different states that data might be in when it can be encrypted: at…
Q: The ciphertext of the message " SUNDRY" after encryption by using Simple Substitution cipher and the…
A: Cryptography: In cryptography encryption is the concept in which information is encrypted into…
Q: In OFB Transmission errors do not propagate: only the current ciphertext is affected, since keys are…
A: Yes, transmission errors do not propagate in OFB mode because of the locally generated key.
Q: Exercise 1. Bob's public ElGamal key is (p, a, y) = (101, 2, 11). %3D (a) Find the plaintext of the…
A: The solution Following Below
Q: Encrypt the message " MATH " by translating the letters into numbers and then applying the…
A:
Q: Which statement is False: None Public key cryptography uses one key for encryption and another one…
A: answer) Encryption and cipher text are not the same thing actually encryption" basically is some…
Q: Suppose the two prime numbers p = 23 and q = 37 are used for an RSA encryption scheme. What are the…
A: Given:
Q: Suppose the two prime numbers p = 23 and q= 37 are used for an RSA encryption scheme. What are the…
A: RSA (Rivest–Shamir–Adleman) cryptographic algorithm is asymmetric use to encrypt and decrypt…
Step by step
Solved in 2 steps

- Imagine a Vigen'ere cypher encrypts a long string of text and repeats it in the ciphertext. Use this information to calculate the key's length.q5- The Atbash cipher is a type of monoalphabetic cipher formed by taking the alphabet and mapping it to its reverse, so that the first letter becomes the last letter, the second letter becomes the second to last letter, and so on. For example: A becomes Z and Z becomes A, B becomes Y and Y becomes B, and so on. Numeric digits and special symbols will remain the same. What does XHV2HRZ mean?The script uses the paddingoracle library to send encrypted values to the program and tries todecrypt it based on the error message. Execute it with the encrypted ciphertext as the argument.
- In cryptography the following uses transposition ciphers and the keyword is LAYER. Encrypt the following message (spaces are omitted during encryption)WELCOME TO NETWORK SECURITY! a. WMEKREETSILTWETCOOCYONRU! b. EETSICOOCYWMEKRONRU!LTWET c. LTWETONRU!WMEKRCOOCYEETSI d. ONRU!COOCYLTWETEETSIWMEKREncrypt the messageWATCH YOUR STEPby translating the letters into numbers, applying the encryption function f(p) = (−7p+2), and then translatingthe numbers back into lettersIt is possible for software running on a desktop computer to produce safe secret keys that may then be used in cryptographic protocols.
- A __________ is an encryption technique designed to enable encryption of a message digest by a user's private key with decryption and message verification by the user's public key and hashing the unencrypted message.A cell-phone two-factor authorization is an example of using _____ to authenticate the user. Select one: a. something the user knows b. something the user has c. something the user is d. something the user doesMany user-created passwords are simple and easy to guess. Program that takes a simple password and makes it stronger by replacing characters using the key below, and by appending "q*s" to the end of the input string. i becomes ! a becomes @ m becomes M B becomes 8 o becomes . Ex: If the input is: mypassword the output is: Myp@ssw.rdq*s
- Attacks on a cipher that use letter frequency can be made more difficult by assigning multiple codes to the most frequently used letters in the alphabet. Such a cipher is called a homophonic cipher. Explain why multiple codes cause no increase in the time to decipher a message if the key is known.Attacks on a cypher are more difficult for a short message since they are more difficult to break.The ciphertext of the message " ILOVEMYUNIVERSITYVERYMUCH" after encryption by using Transposition cipher and the key =5 4 3 2 1 will be: Select one: a. ALL OTHER CHOICES INCORRECT b. IMVTY LYEYM OURVU VNSEC EIIRH c. ALL OTHER CHOICES INCORRECTT d. LYEYM OURVU VNSEC EIIRH IMVTY e. VNSEC EIIRH IMVTY LYEYM OURVU f. OURVU EIIRH VNSEC IMVTY LYEYM g. LYEYM OURVU VNSEC IMVTY EIIRH

