java language Schedule the People class In main file, create an object of class People Make the showPeople method call
Q: How are centralized and parallel/distributed databases different?
A: Answer is given below:
Q: Determine the key benefits and challenges offered by information systems in Ghana's educational…
A: Introduction: There are several benefits of information technology for the education industry.When…
Q: In a stack, items are added and deleted only at one end, referred to as the of the stack.
A: Introduction Stack:- The Stack is a linear data structure that follows a particular order in which…
Q: What is user authentication and how it is important to get access control of the system? Explain in…
A: 1) Authentication is the process of identifying users that request access to a system, network, or…
Q: Provide two benefits of implementing virtualization on a network as a networking technology.
A: The above question is solved in step 2 :-
Q: Why are server-level file permissions important? How secure are they? How do they work? What are the…
A: Answer: We have to write the why file permission are important. and how they can secure. and how…
Q: Identify security principles in the design of data access. (Cryptography and information system…
A: When creating a system's security mechanisms, the security design principles are taken into account.…
Q: An HRD interventionist should let the school know that a training needs analysis is crucial to their…
A: Analysis is the first phase of software development. A customer asks a software development team to…
Q: Explain? is the title given to someone who has the ability to motivate and excite technical…
A: A subject matter expert (SME) is a person who has in-depth knowledge and proficiency in a particular…
Q: How can you assess how successfully interpersonal skills are employed while planning and delivering…
A: It is the sort of communication skill we utilise on a regular basis, such speaking, listening,…
Q: What kind of worries and challenges arise from the use of an unintegrated information system?
A: Introduction: Computer failure and loss are key issues resulting in unnecessarily high costs and…
Q: What steps do employees take to ensure that knowledge is not lost? Assume a company has previously…
A: In the supplied case study, both the good and bad features of the KMS structure, in addition to the…
Q: Algorithm for Expectiminimax using alpha-beta pruning and fail-soft enhancement.
A: Alpha-Beta pruning is an optimization method for the minimax algorithm rather than a brand-new…
Q: How does a compiler deal with an inline member function of a class?
A: In C++, when the meaning of the part work is given with in the meaning of the class. then, at that…
Q: Cyber security professionals may use several methods to affect change.
A: Explanation: Experts in cyber security may take part in order to advocate change. Cybersecurity is…
Q: Write a PHP code to the total current for the intrinsic semiconductor after taking current due to…
A: Required:- Write a PHP code to get the total current for the intrinsic semiconductor after taking…
Q: It is necessary to submit a proposal for a security awareness program. All relevant elements must be…
A: Propose a security programme. It should be a polished, complete item with all key parts.…
Q: Shouldn't this section provide a brief summary of the two operating system components that most…
A: System software: An operating system manages and maintains devices including smartphones, tablets,…
Q: Provide two benefits of implementing virtualization on a network as a technology. networking
A: Answer is given below:
Q: Investigate the difficulties that information systems encounter utilizing available technology and…
A: This issue addresses the challenges that are presented by the fact that information systems are so…
Q: A In addition to just sprinkling the lawn. It tries to handle pumping water with the turnOnWater…
A: The answer is
Q: Learn more about penetration testing. When it comes to information security?
A: Introduction: A penetration test, or pen test, identifies, tests, and highlights security…
Q: Authentication enables organizations to keep their networks secure by permitting only authenticated…
A: Introduction: What purposes does authentication serve? Consider the benefits and drawbacks of…
Q: The idea of normalisation is one that database professionals pay great attention to. Whether you're…
A: Introduction: Normalization involves building tables and defining connections between them according…
Q: Consider the following hypothetical situation: An exception is thrown by a function. What are the…
A: GIVEN: Consider the following hypothetical situation: An exception is thrown by a function. What…
Q: Q.14 Encrypt the message "PAY" using Hill cipher with the following key matrix and show the…
A:
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Introduction: In computing, a local area network (LAN) collects small computers or other workstation…
Q: How does a compiler deal with an inline member function of a class?
A: A compiler is a special program that converts source code into machine code. A function is a named…
Q: How to Define methods on a class?
A: If instead we define methods directly on the class, we’d paint ourselves into a corner.Here’s what…
Q: What types of concerns and problems arise from the use of a fragmented information system?
A: Hello student The answer will be in next step :-
Q: Because switches, routers, and cabling are all "building blocks" of data transmission networks, how…
A: Two or more computers are joined to a computer network to share information and resources. The…
Q: Obtain a DFA equivalent to the NFA given below:
A: Here from question Deterministic finite automata for the given nondeterministic finite automata
Q: Assuming a 32-bit word, how many bits are required to address a 4M x 16 main memory if a. Main…
A: The solution is given below for the above given question:
Q: Teachers need to be aware of the benefits and limitations of utilizing educational information…
A: Information systems for education: An information system is a group of linked elements that…
Q: A reliable technique for choosing cybersecurity products should be created.
A: Introduction: Cybersecurity product selection has 4 steps:Needs-basedSpend risk-adjusted Portfolio…
Q: What is a downgrade attack, and how can you fight back against it?
A: Introduction: Downgrade attack: It's a type of computer system or communication protocol…
Q: Define the risk from the network/OS system's point of view. What are some examples of hazards that…
A: Introduction: An operating system designed specifically for a network device, such as a switch,…
Q: Create a function that returns the sum of all odd numbers from 5 to 70. 1- function sum_odd(){ 2 var…
A: code:- int sum_odd(){ int sum=0; for(int i=5;i<=70;i++) { if(i%2!=0)…
Q: Assign sum_extra with the total extra credit received given list test_grades. Iterate through the…
A: The python program is given below:
Q: Question 5 Computer Science What does the following code fragment write? i = 1 for c in 'hello':…
A: The code will print the letters in the string 'hello', the number of letter printed will be based on…
Q: Is it necessary to safeguard switches, routers, and cabling in order to maintain data transmission…
A: Introduction:- A computer network is a system that connects two or more computers together for the…
Q: (c) The human visual system (HVS) is more sensitive to luminance than chrominance. Chroma…
A: In his study, chroma subsampling's impact on subjectively assessed criteria for perceived video…
Q: How can you help an employee that isn't working to their full potential?
A: Introduction: Bring additional clarity to their perspective. In order to be of assistance to them in…
Q: Algorithm for Principal variation search using negamax
A: The answer is given in the below steps for your reference.
Q: Identity theft is the most prevalent kind of cybercrime. How can hackers take your identity, and…
A: Thieves looking to steal your identity might potentially listen in on you reading your credit card…
Q: Describe benefits of REST over SOAP.
A: INTRODUCTION: SOAP and REST: Both web service communication technologies are REST (Representational…
Q: How to check if the word in two different lists matches. If we have a list of words, for example:…
A: In step 1, I have provided answer with PYTHON CODE In step 2, I have provided CODE SCREENSHOT…
Q: AB 00 01 11 10 00 0 1 1 。 01 1 1 1 1 CD 11 1 1 1 。 10 D 1 1 。
A: Map C.D C.D C.D C.D A.B 0 1 1 0 A.B 1 1 1 1 A.B 1 1 1 1 A.B 0 1 0 0 Map Layout…
Q: The information security plan of a corporation is a project strategy, but how does this happen?
A: Explanation: The design, selection, and execution of all security policies, educational and training…
Q: Explain what Unix data structures are affected when an open() call is used on a device file. How is…
A: What Unix data structures are impacted by an open() call on a device file is the matter at hand. How…
java language
Schedule the People class
In main file, create an object of class People
Make the showPeople method call
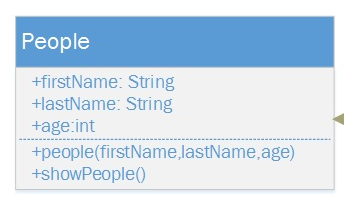
Step by step
Solved in 4 steps with 3 images

- Alternate Character DisplayWrite a method that accepts a String object as an argument and then returns the alternate characters as substring starting from index 0. For instance, if the string argument passed is “GREAT”, the method should return “GET”. Demonstrate the method in a program that asks the user to input a string and then passes it to the method.Sentence Capitalizer Create an application with a method that accepts a string as an argument and returns a copy of the string with the first character of each sentence capitalized. For instance, if the argument is "hello. my name is Joe. what is your name?" the method should return the string "Hello. My name is Joe. What is your name?" The application should let the user enter a string and then pass it to the method. The modified string should be displayed.Look at the following statement: String city = "Asheville";Rewrite this statement so that city references a StringBuilder object instead of a String object.
- public static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current stringLili and Bibi has just graduated from highschool. They’re now in the same university.As both are bestfriends since kindergarten, they chose to share a dormitory room. Rightbefore the first day of college, they both live in the same room.Lili and Bibi both like to read. Each of them has collections of their favourite books. Ofcourse they brought them there. Each book has descriptions: ID(integer), title(string),and author(string). Lili has N books, while Bibi has M books. They both sorted thebooks by its ID in ascending order. Sadly, there are only one bookshelf in the dormitoryroom. They both want to organize their books in one bookshelf, Of course in a sorted IDin ascending order. However, they consider the ID as the first priority of sorting factors,if two books has the same ID, they sort it by its title lexicographically in ascending order.Two books with the same ID may have a different title or author. Lili doesn’t have twobooks with the same ID, neither does Bibi. But they both…public static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current string.This problem is an exercise in Java string manipulation. For some mysterious reason, the Java String type does not come with a reverse method. The canonical way to reverse a Java string str is to first convert it to mutable StringBuilder, reverse its contents, and convert the result back to an immutable string, that is,str = new StringBuilder(str).reverse().toString(); Here's the tester it must pass: @Test public void testPancakeScramble() throws IOException {// Explicit test casesassertEquals("", P2J3.pancakeScramble(""));assertEquals("alu",…
- Instructions: 1. This java program is for an application that stores the author (Writer) data of some books and emails. 2. getAuthors() method get the list of authors and store it in a String array. 3. addAuthors() method is used to add an author anytime for book or email. 4. getDate() method get the date of the book or email. 5. getTitle() method can be used to get the title of the book. 6. getSubject() method is used to get the Subject of the email. 7. getTo() method is used to get the information about the mail to whom it is sent. 8. All get methods need to return the values in the corresponding instance variables. 9. Scanner class can be used to set the data for the variables. The programmer can give his/her own methods to set the instance variablesWord Separator Create an application that accepts as input a sentence in which all the words are run together but the first character of each word is uppercase. Convert the sentence to a string in which the words are separated by spaces and only the first word starts with an uppercase letter. For example, the string "StopAndSmellTheRoses." would be converted to "Stop and smell the roses."A string object is ______ which means its contents cannot be changed. Select one: a. Absolute b. Immutable c. Undisputable d. Irreversible
- Vowels and Consonants Create an application with a method that accepts a string as an argument and returns the number of vowels that the string contains. The application should have another method that accepts a string as an argument and returns the number of consonants that the string contains. The application should let the user enter a string, and should display the number of vowels and the number of consonants it contains.Subject - Data Structure Please help me to debug my error. Thank you in advance! import java.util.Scanner;public class LinearSearchDemo { private static int linearSearch(int[] numbers, int key) { for (int i = 0; i < numbers.length; i++) { if (numbers[i] == key) { return i; } } return -1; // not found } // Main program to test the linearSearch() method public static void main(String[] args) { int[] numbers = { 2, 4, 7, 10, 11, 32, 45, 87 }; System.out.print("NUMBERS: "); for (int i = 0; i < numbers.length; i++) { System.out.print(numbers[i] + " "); } System.out.println(); Scanner scnr = new Scanner(System.in); System.out.print("Enter an integer value: "); int key = scnr.nextInt(); int keyIndex = linearSearch(numbers, key); if (keyIndex == -1) { System.out.println(key + " was not found."); } else { System.out.printf("Found %d at index…Create a function that tallies the number of times a phrase appears in a string. The function's output should be a number. Don't presume that a single space divides words, and that a string can contain punctuation. Create the method so that it can accept a String input or a StringBuilder object.

