JAVA PROGRAM JFRAME FORM please help on what code should I use to get these jframe forms:
Q: Incident response guidelines specify an incident team's components and how they are used in an…
A: The four critical components are listed below to describe the framework of an incident response…
Q: In other words, what is the purpose of a web page?
A: The answer is as follows.
Q: Exactly what does interrupt latency include and how does it relate to the amount of time it takes to…
A: Start: What interrupts latency is and how it relates to the time it takes to switch between contexts…
Q: Consider how reporting systems, data mining systems, and Big Data systems differ. What do they have…
A: The distinctions between reporting systems, data mining systems, and big data systems are as…
Q: Q4: Based on RSA algorithm, if the private key is . Encrypt m-31. I
A:
Q: Write Pascal code to print odd numbers between 1 to 100 Print 5 numbers in each line
A: Odd number is the one which is not divisible by 2. So in this program we have to print odd numbers…
Q: When it comes to the software development lifecycle, what are the stages of the waterfall model? It…
A: Definition: The waterfall model is a standard paradigm used in the system development life cycle to…
Q: Recognize the key features of prototype, Agile, object-oriented, mobile, and user development life…
A: The systems development life cycle encompasses planning, analyzing, designing, developing,…
Q: Q1/ Write a program in C++ by using function to remove the spaces before and after the entered text,…
A: Please find the answer below :
Q: Choose one of the Base Cases you created in Spring Breaks "R" Us Travel Booking Case Study , that…
A: Please find the detailed explanation in the following steps.
Q: Isn't an interruption, by definition, a stoppage? There are no hardware interruptions for these kind…
A: Interrupt : A signal to interrupt the current process or any situation that causes the program to…
Q: Compare Round-robin (RR) algorithm and the Shortest process next (SPN) algorithm for scheduling…
A: Compare Round-robin (RR) algorithm and the Shortest process next (SPN) algorithm for scheduling…
Q: Identify the many ways in which conventional email may be used to launch denial-of-service attacks.…
A: A denial of service (DoS) attack is a kind of cybercrime in which a website is made useless by the…
Q: Create a one dimensional array that contains the following: "Cath, Donna, Anna, Bob, Mae". Write a…
A: I give the code in C# along with output and code screenshot
Q: The spiral model is one of the many software process models mentioned in the research but seldom…
A: Software Development: Software development is a set of computer science activities concerned with…
Q: Is there a way to exchange information in an incident response strategy at your company?
A: Start: A blueprint is a detailed strategy or plan of action. The overall architecture comes first in…
Q: Based on the following dataset create a decision tree Day Weather Temperature Humidity Wind Play? 1…
A: Decision Tree :
Q: Make five recommendations for increasing email privacy in an organization after reading this chapter…
A:
Q: 666.68 Do not add any extra 0 after the last significant non-zero digit. N16 = Submit Request Answer…
A: As per our guidelines we are supposed to answer three subparts of a question. Kindly repost other…
Q: How to turn the following matrix into the expected outcome dictionary in python? matrix =…
A: Solution: Python code: import numpy as np # Matrix 4 x 4 matrix = np.array([[0, 1, 1, 0],…
Q: What is meant by the term "process" in this context? List and explain each of the five types of…
A: Introduction: To explain the process, the states of the process, and context switching. A process is…
Q: We'll go through the most significant information system issues to be aware of, as well as the most…
A: Here are the 5 most common IT problems and how to solve them.1. Lack of Staff (Internal) Security…
Q: Describe the risks, threats, and vulnerabilities commonly found in a System/Application Domain
A: The Proposed Application of a Structure: The part of realty upon which a program system is designed…
Q: Why estimating time and cost is critical. What you find problematic about project time estimation.…
A: Estimating time and cost is important to the project: Cost estimating enables you to do what you…
Q: Explain briefly what process starvation in priority scheduling entails, as well as how to avoid it.
A: Scheduling algorithms are used to schedule processes inside an operating system.
Q: 1. Developing a simple guessing game The program automatically selects a value within a range and…
A: We have to write a simple number guessing game in Python for the given scenario.
Q: For a system with eight interrupt resources, how do you implement parallel priority interrupt…
A: Interrupt Hardware: A hardware interrupt is a signal received by a programme from any of a range of…
Q: Construct a Context Free Grammar (CFG) for a language L = {wcWR| where w € (a, b)*, R is denoting…
A: Given: We have to Construct a Context Free Grammar (CFG) for a language L= { WCWR | where w…
Q: n what sense does the term "control structures" refer to?
A: answer is
Q: What does it mean when a block of code can only be performed by a single process at a time?
A: Given: What is the critical region on the mapA crucial zone is a portion of code that can only be…
Q: There are a number of things that go into the maintenance costs of a computer system.
A: Cost of maintenance Keeping an information system up-to-date is a substantial expenditure. Nearly…
Q: What are the advantages of health-care websites for individuals? What are the differences between…
A: The Web is the abbreviation for the World Wide Web. On the internet, the term is quite popular.…
Q: Make a list of at least ten measures to keep your network safe from malicious and damaging assaults.
A: Malware infestations can be disastrous for businesses. Malware can inflict substantial financial and…
Q: I'm trying to create a program in python and need assistance in creating it. Here's what I'm trying…
A: Solution: Python Code: def main(): # Declare the local variables sm = 0 cnt = 0…
Q: In software development, what is the connection between cohesiveness and coupling? How can logical…
A: Cohesiveness is a term that refers to the interdependence of the module's components. Coupling…
Q: Victor, a level 200 undergraduate student in AIT remarked that array elements can be accessed in…
A: Actually the answer is YES, because all 200 undergraduate students of AIT array elements are denated…
Q: To connect patient monitoring devices to EHRS safely and reliably, what steps must EHR software…
A: The question is how can patient monitoring devices can be connected safely and reliably to EHR or…
Q: Be able to point out the most important parts of the computer system. Are all mission-critical…
A: The mission critical system: A mission critical system is a computer, electrical, or…
Q: Interrupt service routines are different from other types of service routines.
A: In this case, the "interrupt" is handled by an interrupt service procedure. What an "interrupt" is…
Q: Inquire about how library 4.0 technologies are influencing present library services at academic…
A: Please find the detailed answer in the following steps
Q: Explain why wiretapping and sniffing are classified as passive threats.
A: The passive: Agentive passive and non-agentive passive, or passive with and without an agent. The…
Q: Big Bob’s Construction has many construction sites where computers running Windows 10 Pro are…
A: To connect computers located at remote locations, a wide connection along with a cheap and reliable…
Q: Throughout the semester, we defined Methodologies and SDLC. Explain the SDLC and how it relates to…
A: GIVEN: The Software Development Life Cycle, or SDLC, is a mechanism for quickly generating…
Q: Six components of an information system should be recognised, outlined and specified.
A: Six components of an information system should be recognised, outlined and specified. Answer: The…
Q: What are the advantages of having a company-wide incident response strategy?
A: Introduction: A network security incident response plan is a collection of instructions that IT…
Q: Comparing all potential network topologies requires a table.
A: Introduction: This topic asks to develop a table comparing all potential network topologies. A…
Q: High Availability vs. Fault Tolerance: What's the difference?
A: JUSTIFICATION: A twin-engine aero plane is a fault-tolerant system, meaning that if one engine…
Q: In information literacy, there is a distinction between theory of information literacy and model of…
A: Specific type of analysis that tests for nuanced differences: A hypothesis is a broad statement that…
Q: Individuals and organizations build various data structures and algorithms to solve real-life…
A: The Answer is in step-2.
Q: Why have microblogging systems grown in popularity despite the existence of conventional blogging?
A: Conventional: complying or adhering to established norms, as of conduct or taste. related to…
JAVA
please help on what code should I use to get these jframe forms:
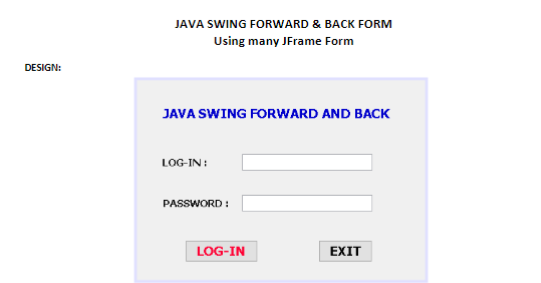
Step by step
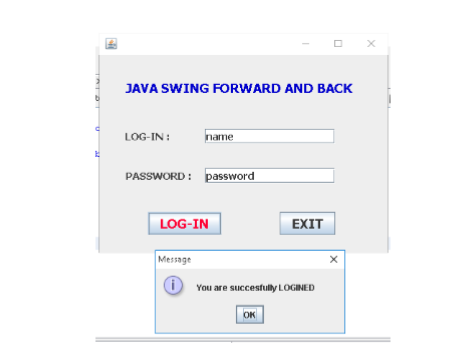
Solved in 4 steps with 7 images

- Urgent i need your help! I want you to set the username = admin and password =123456 and then when i log in there another frame will pop up and say "Successfully Login!" Ps.Use Java Programming.10q import java.awt.GridLayout;import java.awt.*;import javax.swing.*;public class Trial { public static void main(String[] args) { JFrame frm = new JFrame ("PASSWORD ENTER"); JLabel lb1Name = new JLabel("USERNAME: "); JPasswordField value = new JPasswordField(); JLabel lb2Pass = new JLabel ("PASSWORD: "); JTextField txtName = new JTextField(20); lb1Name.setFont(new Font("consolas",Font.BOLD,20)); txtName.setFont(new Font("consolas",Font.PLAIN,20)); txtName.setHorizontalAlignment(JTextField.CENTER); lb2Pass.setFont(new Font("consolas",Font.PLAIN,20)); lb1Name.setBounds(50,100,80,30); lb2Pass.setBounds(50,150,80,30); frm.setLayout(new GridLayout(1,2,5,5)); frm.add(lb1Name); frm.add(txtName);…What potential performance issues are their with the below Java program? Java source code: package application; public class JavaConcurrency { private static final Object lock = new Object(); private static boolean isCountingUpDone = false; public static void main(String[] args) { Runnable countUp = () -> { for(int i = 0; i <= 20; i++) { synchronized (lock) { System.out.println("Thread 1: " + i); if (i == 20) { isCountingUpDone = true; lock.notifyAll(); // Notify thread 2 to start counting down System.out.println("\nThread 1 complete\n"); } } try { Thread.sleep(400); // Slow down thread } catch (InterruptedException e) { Thread.currentThread().interrupt(); } } };…Hi there, I have to write apache kafka in java for 3 consumers. Currently I have code for 1 but i am struggling to make it to 3 consumers. Can anyone change it so that it runs with 3 consumers. consumer.java is as follows import org.apache.kafka.clients.consumer.ConsumerRecord;import org.apache.kafka.clients.consumer.ConsumerRecords;import org.apache.kafka.clients.consumer.KafkaConsumer;import java.time.Instant;import java.util.ArrayList;import java.util.List;import java.util.Properties;import java.time.Instant;public class Consumer {public static void main(String[] args) {Properties properties = new Properties();properties.put("bootstrap.servers", "localhost:9092");properties.put("key.deserializer", "org.apache.kafka.common.serialization.StringDeserializer");properties.put("value.deserializer", "org.apache.kafka.common.serialization.StringDeserializer");properties.put("group.id", "test-group");KafkaConsumer<String, String> kafkaConsumer = new KafkaConsumer<String,…
- What would pseudocode look like for the following Java application? Java source code: package application; public class JavaConcurrency { private static final Object lock = new Object(); private static boolean isCountingUpDone = false; public static void main(String[] args) { Runnable countUp = () -> { for(int i = 0; i <= 20; i++) { synchronized (lock) { System.out.println("Thread 1: " + i); if (i == 20) { isCountingUpDone = true; lock.notifyAll(); // Notify thread 2 to start counting down System.out.println("\nThread 1 complete\n"); } } try { Thread.sleep(400); // Slow down thread } catch (InterruptedException e) { Thread.currentThread().interrupt(); } } };…Check out the Java API: https://docs.oracle.com/javase/8/docs/api/. Go to the FileInputStream class of the java.io package. Write down the last method in the method summary list (returntype methodName(param list)Java program doesnt work please help. import java.applet.*; import java.awt.*; import java.awt.event.*; public class Truck extends Applet implement ActionListener { int x,y,z; int t1,t2: Button b1,b2; String msg=" "; void slep() { try { Thread.sleep(100); } catch(Exception ex) { } } public void init() { t1=0; t2=1; X=20; y=60; setLayout(new FlowLayout(FlowLayout.CENTER)); Label 1=new Label("webeduclick"); b1=new Button("Forward"); add(b1); b2=new Button("Stop"); add(b2); b1.addActionListener(this); b2.addActionListener(this); } public void start() { } public void actionPerformed(ActionEvent e) { String s=e.getActionCommand(); if(s.equals("Stop")) { msg=" "; repaint(); } } public void paint(Graphics g) { setBackground(Color.green); z=getWidth(); Color c1=new Color(20.160.200); Color c2=new Color(200.60.200); g.setColor(c1); g.drawline(0,y+75,z,y=75); g.setColor(Color.yellow); g.fillRoundRect(x,y+20,100,40,5,5); g.fillArc(x+90,y+20,20,40,270,180); g.setColor(Color.orange);…
- Dijkstra's algorithm Weight Class Implementationlanguage : C++ Note : Skelton Files Provided Please check the linksproject Details:https://ece.uwaterloo.ca/~dwharder/aads/Projects/5/Dijkstra/ Files:https://ece.uwaterloo.ca/~dwharder/aads/Projects/5/Dijkstra/src/ Please provide clear and complete solution for thumps up.New JAVA code can only be added to Client.java file between lines of grey code (or between lines 2 and 4, as seen in image).What advantages do File System websites have over HTTP websites? What makes encapsulation and inheritance different from one another?
- What are the advantages of an HTTP website versus a file system website? When it comes to encapsulation and inheritance, what are the differences?What is the security of the data types exhibited in the below Java program? Java source code: package application; public class JavaConcurrency { private static final Object lock = new Object(); private static boolean isCountingUpDone = false; public static void main(String[] args) { Runnable countUp = () -> { for(int i = 0; i <= 20; i++) { synchronized (lock) { System.out.println("Thread 1: " + i); if (i == 20) { isCountingUpDone = true; lock.notifyAll(); // Notify thread 2 to start counting down System.out.println("\nThread 1 complete\n"); } } try { Thread.sleep(400); // Slow down thread } catch (InterruptedException e) { Thread.currentThread().interrupt(); } } };…1.)Why is this code not thread safe? 2) What issues could arise if it is not fixed? 3) How you would fix it using what you learned about synchronization? You must write lines of code or fix lines of code that already exist in the file for full credit. mport java.io.ObjectInputStream; import java.io.ObjectOutputStream; import java.io.Serializable; import java.net.ServerSocket; import java.net.Socket; import java.util.ArrayList; import java.util.function.Consumer; import javafx.application.Platform; import javafx.scene.control.ListView; public class Server{ int count = 1; ArrayList clients = new ArrayList(); TheServer server; private Consumer callback; Server(Consumer call){ callback = call; server = new TheServer(); server.start(); } public class TheServer extends Thread{ public void run() { try(ServerSocket mysocket = new ServerSocket(5555);){ System.out.println("Server is waiting for a client!"); while(true) { ClientThread c = new ClientThread(mysocket.accept(), count);…

