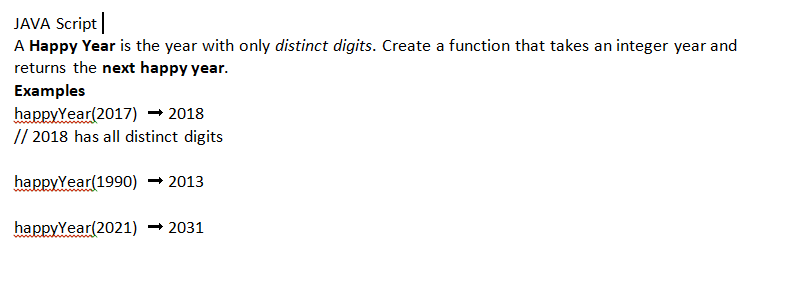
JAVA Script A Happy Year is the year with only distinct digits. Create a function that takes an integer year and returns the next happy year. Examples happyYear(2017) 2018 // 2018 has all distinct digits happyYear(1990) ➡ 2013 happyYear(2021) 2031
Q: Write a C++ program to read in 10 prices (function getprices). Then write function caldiscount to do…
A: Here is c++ program. The output is working correct. See below steps
Q: Suppose a firewall is configured to allow outbound TCP connections but inbound connections only to…
A: A firewall is a network security system that monitors and controls incoming and outgoing network…
Q: IN JS Someone has attempted to censor my strings by replacing every vowel with a *, 1*k* th*s.…
A: In this problem we are provided with a censored string and a string of the censored vowels. Need to…
Q: 'Hello" should use a character array of length A. 5 B. 6 C. 7 L to store.
A: Using Python3 language for the validation of the answer.
Q: Where does Windows store deleted files when you use File Explorer or Windows Explorer to remove them…
A: Where does Windows store deleted files when you use File Explorer or Windows Explorer to remove…
Q: Describe the function that is served by each layer of the OSI model when it comes to security.
A: In this question we have to describe the function that is served by each layer of the OSI model in…
Q: What does "design workstation" mean? Use examples and figures to illustrate the subject.
A: The answer is written in step 2
Q: What possible use may a motherboard power connection in the SATA type serve?
A: SATA Serial ATA (Serial Advanced Technology Attachment or SATA) is an order and transport…
Q: Determining the owner of the files in the recycle bin requires you to search for a users
A: Logon name is correct answer
Q: Write a struct that defines a binary tree node
A: In C, we can use structures to represent a tree node. We can use classes as a component of other…
Q: JAVA Programming Write a function that returns true if you can partition an array into one element…
A: Algorithm - Take one string as input. Now use the below logic if(count==1) return false;…
Q: When should data be kept in conventional files?
A: Introduction A record of the bosses' design deals with the procedure for inspecting and making data…
Q: What are the 3 rules of defensive programming?
A: Introduction A computer program is a bunch of guidelines that are run on a computer to do specific…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: Answer- TCP/IP stands for Transfer Control Protocol/ Information Protocol. During a data transfer,…
Q: What circumstances make using conventional files for data storage effective?
A: Data storage which refers to the files and the documents that are used to recorded in the digitally…
Q: Argument 1 All cancer medications are toxic substances. Therefore, it is false that no cancer…
A: Aristotelian standpoint interprets propositions about things that actually exists. They convey…
Q: Declare a structure type in C++ named Marks, with the following members: subject : a string value…
A: Here, Student is a structure and it consists of another structure Marks as its member. So values of…
Q: Which of the following gdb commands allows you to display the source code you are debugging? A.…
A: B. list
Q: Assume an 8088 is executing a program in which the probability of a program jump is 0.1. For…
A:
Q: A memory system consists of a cache and a main memory. It takes 25ns to access the cache, and 100ns…
A: Answer the above question are as follows
Q: Who are the people involved in the phases of Waterfall Model
A: Answer: waterfall models is old method's that is used to sequentially manage the projects. Itis…
Q: s meant by the term "Symmetric Multiprocessing" (SMP)?
A: Introduction Symmetric Multiprocessing: Multiple processors working together to process data using…
Q: What is a virtual machine (VM) defined as? Is there a reason I would want to use a virtual machine?…
A: A Virtual Machine, also shortened as VM, is the same as any other physical computer, such as a…
Q: what use Linux may have in any element of rocket technology.
A: Linux is used extensively in rocket technology. It is used in the development and deployment of…
Q: Where does Windows store deleted files when you use File Explorer or Windows Explorer to remove them…
A: The question is Where does Windows store deleted files when you use File Explorer or Windows…
Q: common OS invader classes in br
A: Intruder: As we know Intruders have publicized threats to security things and generally referred to…
Q: Assume you need to store book data in a structured manner. Either more books should be added, or…
A: The answer is given in the below step
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: I have mentioned answer in below steps (a) 000000100000001100000101 Carry = 0; Zero = 0;…
Q: Report key similarities and differences between HTML and XML with the use of examples to distinguish…
A: NOTE: AS PER THE BARTLEBY GUIDELINE IF THERE ARE MULTIPLE QUESTION THEN WE ARE ALLOWED TO ANSWER ONE…
Q: What are the many entry points that might be exploited by malicious software to get access to a…
A: Here we have given a brief note on entry points that might be exploited by malicious software to get…
Q: Sequence diagram for uber eats
A: - We have to give the sequence diagram for uber eats.
Q: IN JS Someone has attempted to censor my strings by replacing every vowel with a *, 1*k* th*s.…
A: In this problem we are provided with a censored string and a string of the censored vowels. Need to…
Q: Elaborate on any five advantages of alpha testing.
A: alpha testing Alpha testing is the earliest process of evaluating whether a new product will…
Q: Explain in detail the various strategies that may be used to prevent OS invaders.
A: The various strategies that may be used to prevent OS invaders are
Q: Why and how do numerous Linux commands behave in the same way on Macs and Linux systems,…
A: Linux is the most popular open-source operating system, and it is also one of the most well-known.…
Q: Considering the c++ program below, and [4, 5, 8, 3] as user inputs, answer the following questions:…
A: We need to answer the questions based on given C++ code.
Q: 3 A computer consists of a processor and an I/O device D connected to main memory M via a shared bus…
A:
Q: Dissertate on WebGL and OpenGL ES.
A: Points on WebGL 1. WebGL stands for Web Graphics Library. This library is used to generate…
Q: What fundamentally distinguishes the telephone network from the Internet?
A: In the given question the internet and telephone networks are both switched networks, with circuit…
Q: Expand each of the following summation. one term for each Value of R. Simplify each term as For…
A: 1) The answer for given summation will be: =1 + 2 + 4 + 8 + 16 + 32 + 64 + 128
Q: How will we be affected by the Internet of Things (IoT)? Describe a smart gadget or app using an…
A: IoT stands for Internet of Things which is the concept driven by the devices which can be operated…
Q: Consider a system employing interrupt-driven I/O for a particular device that trans- fers data at an…
A: I have mentioned answer in word based image format , please find in below a) :
Q: When would you suggest RADIUS or Kerberos be used instead of tacacs+?
A: Users that need access to a network are sent to the Tacacs+ server, which stands for terminal access…
Q: Produce a Turing Machine state diagram that decides the following language. You do not need to show…
A: Given: La = {anbn : n>=0} Logic to build turing machine for La is : step1) start reading input,…
Q: Think about how cloud computing encourages open innovation.
A: Introduction: Cloud computing enables a diverse variety of service delivery options. This includes…
Q: What are the many programmes I may use to backup Windows 10? Also, please explain the main…
A: answer is
Q: Give a brief explanation of what machine language is. What are the causes of the inability of…
A: To Do: To describe machine language. Machine Language: Machine language is a collection of numerical…
Q: Where exactly are the weaknesses in the security architecture located?
A: Security architecture forms the foundation of a good cyber security strategy.
Q: Many commands in Linux work exactly as they do in Linux, but why and how does this happen?
A: INTRODUCTION The Linux operating system is a piece of software that sudden spikes in demand on top…
Q: Provide an explanation of what it is and how it relates to cloud and fog computing.
A: Cloud Computing - Delivering hosted services through the internet is referred to as "cloud…
Step by step
Solved in 2 steps with 1 images

- This is a question of Ocaml: *) (* An employee is a tuple of name, age, and boolean indicating marriage status *)type employee = string * int * bool(* 1. Write a function that takes an employee, and prints out the information in some readable form. *) (*let print_employee_info t =*)The greatest integer function is defined by int(x) = the greatest integer that is ....................For example, int(2.5) = ................ int(-2.5) = ............... and int(0.5) = ...................solve all the program in java 1. Write a Java program to print 'Hello' on screen and then print your name on a separateline.Expected Output:HelloDonald Trump2. A school has following rules for grading system:a. Below 25 - Fb. 25 to 45 - Ec. 45 to 50 - Dd. 50 to 60 - Ce. 60 to 80 - Bf. Above 80 - AAsk user to enter marks and print the corresponding grade.3. Create a function that takes two numbers as arguments and returns the GCD of the twonumbers.Examplesgcd(3, 5) ➞ 1gcd(14, 28) ➞ 14gcd(4, 18) ➞ 24. Given an integer, create a function that returns the next prime. If the number is prime,return the number itself.ExamplesnextPrime(12) ➞ 13nextPrime(24) ➞ 29nextPrime(11) ➞ 11// 11 is a prime, so we return the number itself.5. Write a Java program that takes two numbers as input and display the product of twonumbers.Test Data:Input first number: 25Input second number: 5Expected Output:25 x 5 = 125 6. Write a Java program to print the sum (addition), multiply, subtract, divide and…
- function myCompose(f,g){// TODO: return (f o g);// that is, a function that returns f(g(x)) when invoked on x.}In python I have N unique coupons that are included in boxes of the cereal being sold. A consumer wins the contest after collecting N coupons. I seek to simulate the contest with the function couponTrial(N,debug), where ? is the number of coupons and debug is a flag that is set when the function is being debugged. It must include the function and imports the Python random number generator.Computer Science In python, how do I make a function that will initiate a round of a game, in a game where there's a total of three rounds total, and the first person to win 2 rounds win.
- Create a function sumofAllOdd(s,e) that will return the sum of all odd numbers in a range of inputted numbers s (starting number), e(ending number). For example: Test Result sumofAllOdd(22,55) sumofAllOdd(5,10) Answer:(penalty regime: 10, 20, ... %)Write a function hello(name), which prints "Hello" followed by the value of name. For example, hello('James') would print "Hello James". Write a program that asks the user for their name, and then uses the function to greet the person.1. Implement function postal() that takes 6 inputs: a first name (as a string) a last name (as a string) an address (as a string) a city (as a string) a state (as a string) a zip code (as an integer)and then prints a mailing address in 3 lines as shown below.>>> postal('Ljubomir', 'Perkovic', '243 S Wabash Ave','Chicago', 'IL', 60304)Ljubomir Perkovic243 S Wabash AveChicago, IL 60304
- 1 - Nuclear Power Plant (python) The nuclear powerplant at Threeyedfish will automatically run a program to print a warning message when the reactor core becomes unstable. The warning message reads: NUCLEAR CORE UNSTABLE!!! Quarantine is in effect. Surrounding hamlets will be evacuated. Anti-radiationsuits and iodine pills are mandatory. Since the message contains crucial information, it should be printed three times. To do this, write a function that prints this message. This function has to be used three times.Create the function that takes a list of dictionaries and returns the sum of people's budgets. Examplesget_budgets([ { "name": "John", "age": 21, "budget": 23000 }, { "name": "Steve", "age": 32, "budget": 40000 }, { "name": "Martin", "age": 16, "budget": 2700 }]) ➞ 65700 get_budgets([ { "name": "John", "age": 21, "budget": 29000 }, { "name": "Steve", "age": 32, "budget": 32000 }, { "name": "Martin", "age": 16, "budget": 1600 }]) ➞ 62600Write a function palindromes that accepts a sentence as an argument. The function then returns a list of all words in the sentence that are palindromes, that is they are the same forwards and backwards. The language is in Python. Guidelines: punctuation characters .,;!? should be ignoredthe palindrome check should not depend on case Example: >>> palindromes("Hey Anna, would you prefer to ride in a kayak or a racecar?") ['Anna', 'a', 'kayak', 'a', 'racecar']

