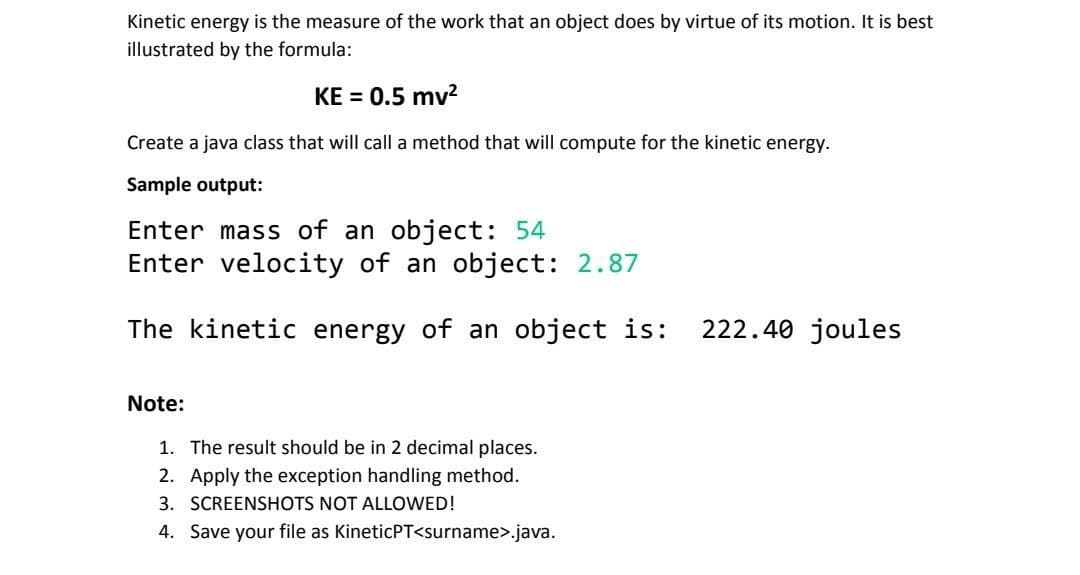
Kinetic energy is the measure of the work that an object does by virtue of its motion. It is best illustrated by the formula: KE = 0.5 mv² Create a java class that will call a method that will compute for the kinetic energy. Sample output: Enter mass of an object: 54 Enter velocity of an object: 2.87 The kinetic energy of an object is: 222.40 joules
Q: The industry currently favors connection-based protocols, so please provide a succinct explanation…
A: Introduction: All source-to-destination packets follow the same path. It's not required to use the…
Q: Is it true that an expert system, in contrast to database management programs, lacks a graphical…
A: The primary distinction between an expert system and a standard database with information on a…
Q: Analyze how planning and delivering a training session affects the application of interpersonal…
A: Introduction: It is the type of capacity we use to communicate in daily life, such as speaking,…
Q: Indicate the types of data that are not covered by the Security Rule.
A: Security Rule: What is it?It's a rule that sets national guidelines for safeguarding people's…
Q: 802.11 is a packet based communication system. What structures should exist in the packets to ensure…
A: Introduction: The IEEE 802 collection of technical standards for local area networks (LANs) includes…
Q: Will upvote! Find the memory address of the next instruction executed by the microprocessor, when…
A: Answer: We need to write the what will be the memory address of the next instruction executed by the…
Q: Control of Quality: Document the Use of GIT and GitHub.
A: GIT quality control : Git is a very well-known version control system that has been around since…
Q: What is the time complexity for the following code/program?
A: The time complexity here simply depends on the number of times the loop is going to execute which is…
Q: One of the purchasing managers is interested in the impact of product prices on the sale of products…
A: Given: One of the purchasing managers is interested in the impact of product prices on the sale of…
Q: During the process of connecting devices, there are four potential problems you should anticipate.
A: When relationships combine, four challenges arise, and their resolution is as follows: A…
Q: This section covers the aspects of ATM traffic management that may be utilized to either prevent or…
A: the main goals of traffic management in ATM networks are to protect users and the network in order…
Q: X marks the spot! Arr! Did you think that just because we’re pirates, we wouldn’t ask the Coding…
A: Algorithm: Step-1: StartStep-2: Declare variable sailor and take input from userStep-3: If sailor…
Q: When anything is authenticated, what are the advantages? What are the pros and cons of the many…
A: Start: The process of identifying users who wish to access a system, network, or device is known as…
Q: Write a function to determine whether a string is a permutation of a palindrome given a string. A…
A: Answer: Algorithms: Step1: we have initialized the string as st Step2: Then we have initialized the…
Q: Based on the names of the classes, which of these Derived Class - Base Class pairs makes the most…
A: The solution is given below with explanation
Q: Information technology's short- and long-term effects on people, groups, and communities Is it not…
A: Definition: Information Technology: Impacts on Society and Our Daily LivesPresent arguments from…
Q: When talking about Al, what exactly does the term "agent" refer to?
A: Please find the answer below :
Q: In comparison to other symmetric encryption methods, what are some of RSA's benefits?
A: RSA:- Modern computers employ the RSA (Rivest-Shamir-Adleman) method to encrypt and decrypt…
Q: Consider the value of good communication skills and the opportunities they present as you prepare…
A: Introduction: In daily life, communication skills including speaking, listening, walking, and…
Q: Suppose a 2D bounding box is given by (≤ is "less than or equal to"): -1 ≤ x ≤ 1 -10 ≤ y ≤ 10…
A: Here is your solution step by step -
Q: Suppose we removed line # 10 in the program above (Uno.__init__(self, leaf)) Fill in the blank on…
A: Introduction We can access all the methods and variables in the Uno class if it was inherited by the…
Q: Q.4 Each of the following addresses belongs to a block. Find the first and the last address in each…
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: What are the various forms of cyberattacks, and what do they hope to achieve?
A: What is a Cyber Attack? An intentional attack on computer systems, tech-dependent businesses, or…
Q: Put up a list of all the web resources that facilitate your interaction. You just have a few phrases…
A: People use the Internet's services to talk to each other, do business, market their products,…
Q: 7.4 LAB: Soccer team roster (Arrays) This program will store roster and rating information for a…
A: Step-1: StartStep-2: Declare an constant MAX_PLAYER with value 5Step-3: Define an structure Player…
Q: Please solve using C language The function get_tokens gets a string str, and a char delim, and…
A: Answer :
Q: The operation code must be separated from the operands.
A: Each conference language statement is broken down into an operator and an op code in accordance with…
Q: Kindly define assembler, compiler, and interpreter in your own words.
A: Introduction: A translator is crucial to the conversion of languages. It serves as an intermediary.…
Q: An organization is granted a block of addresses with the beginning address 18.29.89.0/26. The…
A: Given: We have to design the subblocks for the organization that needs to have 3 subblocks of…
Q: In comparison to connection-based protocols, what benefits and drawbacks do connectionless protocols…
A: Introduction: A few protocols can function without a network connection. A message may be…
Q: What do scientists studying Al want to accomplish? Give two examples from each of the categories it…
A: INTRODUCTION: Artificial intelligence, or AI, machines (typically computers) attempting to mimic…
Q: Consider the following graph: a d 1. What is the type of given graph? 2. What is the in-degree of…
A: Given: We have to discuss the following Graph.
Q: What is the time complexity for the following code/program? for (int i = 1; i = 1; k--){ sum = i…
A: for the above program lets split the complexity of each lloop for i loop ==> as i is…
Q: JAVA Using a text editor write a "Hello World" program in Java. This should produce a .java text…
A: 1. creating a java file containing the Hello world helloWorld.java file class HelloWorld {…
Q: Detail the features and potential applications of the network monitor 3.1 program. What additional…
A: The network monitor 3.1 software is a powerful tool that is used to monitor and troubleshoot many…
Q: If you can think of at least two, please list them below, that can be utilized to create visual…
A: Introduction : Visual media aids readers in conveying and comprehending material since they may form…
Q: ased on the names of the classes, which of these Derived Class - Base Class pairs makes the most…
A: Dear Student, The answer of your question with required explanation is given below -
Q: bytes and finds a block of size mm, if m > nm>n then
A: Dear Student, The answer to your question is given below -
Q: d be caused b
A: What potential problems could be caused by splitting a vertical connection?
Q: Consider the following tree: Node 1. Perform the post-order tree traversal. 2. Complete the…
A: - We have a tree provided and we need to give post-order traversals and complete the table provided.…
Q: Give a real-life illustration of how a template could be put to use.
A: Introduction: A template is a form, mould, or pattern that is used to direct the production of…
Q: My name is Omar. I am an array of integral numbers. People divide me according to the position they…
A: #include<stdio.h> #include<conio.h> int main(){ printf("Input 10 Numbers\n");…
Q: Assuming that a class with the main method exists and a reference variable and object have been…
A: Assuming that a class with the main method exist and a reference variable and object have been…
Q: It takes your firm 2 days to prepare and mail out the monthly statements to your customers. On…
A: Given: Time taken by the firm = 2 days Mailtime between the firm and customer = 4.5 days Customer…
Q: Sorry if I want the code read the numbers straight from the file, what should I do? or change. plz…
A: The JAVA code is given below with output screenshot Step by Step Algorithm: 1. Create a Scanner…
Q: What are some applications of teamwork conducted in the cloud? The advantages of collaborative cloud…
A: Corporate collaboration includes cloud collaboration. lets workers work together on documents and…
Q: To "explain?" is to be recognized as someone who can motivate technical experts to give their…
A: Introduction: You are regarded as explain when you have the ability to motivate technical people to…
Q: There are numerous choices available for machine learning. Give some real-world applications of Al…
A: Introduction: Artificial intelligence is the emulation of human intellectual functions by computers.
Q: Consider the potential fallout if anything catastrophic happened to the cloud computing sector. In…
A: "Cloud computing" describes web-based processing administrations. When you access the cloud, it's…
Q: Developing Web Apps in Python Using Flask and Consuming REST API
A: Introduction: Python is quickly becoming a popular programming language for developing apps.…
Step by step
Solved in 2 steps with 1 images

- ISP- Java A pedometer treats walking 2,000 steps as walking 1 mile. Write a program whose input is the number of steps, and whose output is the miles walked. Output each floating-point value with two digits after the decimal point, which can be achieved as follows: System.out.printf("%.2f", yourValue); Your program must define and call a method: public static double stepsToMiles(int userSteps) Ex: Ex: If the input is: 8790 the output is: 4.40Java Programming. Needs to be done with loops. Define a public static method called printPyramid(). This method should have publicstatic as its visibility modifiers. It should not return a value. It has a single integer parameter.When printPyramid() is called with an integer value, it should print a pyramid with a heightof that value.For example, if we call printPyramid() with an integer value of 5, then the following shouldbe displayed in the output console.** ** * ** * * ** * * * *You will have to use multiple for loops (consider nested for loops) to write this method.❏ In your main method, you should ask the user for the desired height of the pyramid. The usershould provide a value greater than 1. If the user does not provide a valid value, you should forcethe user to continue entering values until they enter a correct one.Then, call the printPyramid() method with the height given by the user.in java Write a program to calculate item’s sale price 1)Ask user to enter the name of item e.g t-shirt 2)Ask user to enter the color of the shirt they want to buy 3)Ask user to enter the item’s price e.g 10, 100, 200 4)Write a method to calculate discounted price 1)If item’s price is more than or equal to 100, get 10% discount 2)Item’s color must be ‘blue’ 3) Return discounted price 4) If less than 100 or not blue, no discount 4) Mainline should display, item name, color and the discounted price
- IN java explain: Define a method named coinFlip that takes a Random object and returns "Heads" or "Tails" according to a random value 1 or 0. Assume the value 1 represents "Heads" and 0 represents "Tails". Then, write a main program that reads the desired number of coin flips as an input, calls method coinFlip() repeatedly according to the number of coin flips, and outputs the results. Assume the input is a value greater than 0. Ex: If the random object is created with a seed value of 2 and the input is: 3 the output is: Heads Tails Heads Note: For testing purposes, a Random object is created in the main() method using a pseudo-random number generator with a fixed seed value. The program uses a seed value of 2 during development, but when submitted, a different seed value may be used for each test case. The program must define and call the following method:public static String coinFlip(Random rand) code provided: import java.util.Scanner;import java.util.Random; public class…Solved in Java Write a method maxMagnitude() with two integer input parameters that returns the largest magnitude value. Use the method in a program that takes two integer inputs, and outputs the largest magnitude value. Ex: If the inputs are: 5 7 the method returns: 7 Ex: If the inputs are: -8 -2 the method returns: -8 Note: The method does not just return the largest value, which for -8 -2 would be -2. Though not necessary, you may use the absolute-value built-in math method. Your program must define and call a method:public static int maxMagnitude(int userVal1, int userVal2) import java.util.Scanner; public class LabProgram { /* Define your method here */ public static void main(String[] args)…A pentagonal number is defined as n(3n−1) ∕ 2 for n = 1, 2, . . ., etc.. Therefore, the first few numbers are 1, 5, 12, 22, . . . . Write a method with the following header that returns a pentagonal number:public static int getPentagonalNumber(int n) For example, getPentagonalNumber(1) returns 1 and getPentagonalNumber(2) returns 5. In Java, Write a test program that uses this method to display the first 100 pentagonal numbers with 10 numbers on each line. Numbers are separated by exactly one space.
- ISP- JAVA A “jiffy” is the scientific name for 1/100th of a second. Given an input number of seconds, output the number of "jiffies." Output each floating-point value with two digits after the decimal point, which can be achieved as follows: System.out.printf("%.2f", yourValue); Your program must define and call a method: public static double secondsToJiffies(double userSeconds) Ex: Ex: If the input is: 136 the output is: 3600.0A regular polygon is an n-sided polygonin which all sides are of the same length and all angles have the same degree (i.e.,the polygon is both equilateral and equiangular). The formula for computing thearea of a regular polygon is given below: Write a method that returns the area of a regular polygon using the following header:public static double area(int n, double side)Write a main method that prompts the user to enter the number of sides and theside of a regular polygon and displays its area. Here is a sample run: Enter the number of sides: 5 ↵EnterEnter the side: 6.5 ↵EnterThe area of the polygon is 72.69017017488385basic java please Write a method called findTip that finds the value of a meal as a double after adding the tip to the cost. Then return this value to the calling function. For example findTip(120.10, 5) would 126.105 because that is a 5% tip. While findTip(48.0, 15) would return 55.2 because that is a 15% tip. Note that the bill is a double while the tip is an int. Don’t worry about rounding to two decimal places, just return the full value as a double.
- Write a Java program that randomly generates a three-digit lottery number and prompts the user to enter a three-digit number. Each digit in the number is in the range between 0 to 9 with both 0 and 9 possible numbers. Write a method named getPrize() to determine which prize the user wins following the rules shown below. The method getPrize() should return an integer representing which prize was won such as 1 for first, 2 for second, etc. It should return -1 if no prize was won.Writing Methods that Return a Value in Java In this lab, you complete a partially written Java program that includes a method that returns a value. The program is a simple calculator that prompts the user for two numbers and an operator ( +, −, *, /,or% ). The two numbers and the operator are passed to the method where the appropriate arithmetic operation is performed. The result is then returned to the main() method where the arithmetic operation and result are displayed. For example, if the user enters 3, 4, and *, the following is displayed: 3.00 * 4.00 = 12.00 The source code file provided for this lab includes the necessary variable declarations, and input and output statements. Comments are included in the file to help you write the remainder of the program. Instructions Write the Java statements as indicated by the comments. Execute the program Tasks Defined performOperation() Input / output tests Multiplication input / output test Division input / output test Subtraction…Writing Methods that Return a Value in Java In this lab, you complete a partially written Java program that includes a method that returns a value. The program is a simple calculator that prompts the user for two numbers and an operator ( +, −, *, /,or% ). The two numbers and the operator are passed to the method where the appropriate arithmetic operation is performed. The result is then returned to the main() method where the arithmetic operation and result are displayed. For example, if the user enters 3, 4, and *, the following is displayed: 3.00 * 4.00 = 12.00 The source code file provided for this lab includes the necessary variable declarations, and input and output statements. Comments are included in the file to help you write the remainder of the program. Instructions Write the Java statements as indicated by the comments. Execute the program USE THE GIVEN CODE // Calculator.java - This program performs arithmetic, ( +. -, *. /, % ) on two numbers // Input: Interactive. //…



