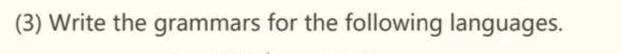
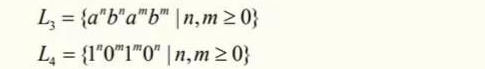
L₂ = {a"b"a"b" |n,m>0} L₁ = {1"0"1"0" |n, m≥ 0}
Q: What are Logical Disk Blocks ?
A: The size of the blocks used by the UNIX kernel to read or write files is known as the logical block…
Q: You have taken large number of photos during a family trip, and most of them are group photos (with…
A: Machine Vision: Machine vision (MV) is a field of computer science that focuses on providing…
Q: Implement the following: Given: item1 = "Pens" item2 = "Pencils" price1 = 0.99 price2 = 1.5…
A: An f-string is a literal string, prefixed with f in which contains expressions inside braces.
Q: Give output of this code: paragraph Text is with red border
A: Question wants output of the given code. Code is in HTML. Giving the output in next steps.
Q: What is streaming data?
A: Data Streaming: The term "streaming data" refers to data that is produced continually by thousands…
Q: Think about the standard TCP/IP ports. To correctly build security, businesses need to be aware of…
A: Launch: A PC network is a collection of PCs that communicate using a variety of standard protocols…
Q: A microprocessor scans the status of an output I/O device every 20 ms. This is accom- plished by…
A: Time to scan the device = Number of instructions x clock cycles per instruction Frequency of…
Q: mov ax, 387 shl al, 2 the values in AL, AH, and AX registers what? (in decimal) after executing…
A: Dear Student, mov instruction stores the value 387 in register ax. shl shifts operand1 left , where…
Q: Consider a floating-point format with 8 bits for the biased exponent and 23 bits for the…
A:
Q: Question 7 For a 4-variable logic function, a minterm/maxterm may have 3 variables. A) True B False
A: Introduction: In this question, we are asked to state true or false whether a 4-variable logic…
Q: An explanation of session hijacking attacks and suggestions for users on how to defend themselves…
A: We need to explain session hijacking and suggestions to defend against it.
Q: What is difference between batch processing and streaming process??
A: Batch processing 1. Data scope query or analysis applied to all or the majority of the dataset's…
Q: Considering a single linked list class, write a method to check whether it contains a number…
A: Please check the step 2 for solution
Q: (a) What services does the network layer provide to the transport layer? (b) Are data packets…
A: a) Network layer provides various services It is responsible for logical addressing of the packets…
Q: n correct remember else downvote Fgurantee.
A: I have used HTML to design this :
Q: The definition of luminance What are the main distinctions between brightness and radiance?
A: The definition of luminance: The quantity of light that is emitted from a surface in a certain…
Q: Statistics are often calculated with varying amounts of input data. Write a program that takes any…
A: Here I have created a list to store the elements entered by the user. Next, I have used a loop that…
Q: Which rules should effect exposed and traceable project components if a software industry uses…
A: The software industry: Uses the Software Development Life Cycle (SDLC) method to plan, create, and…
Q: Give a thorough explanation of the various security management ideas as well as the guiding security…
A: Security Management: Security policy and solution deployment include management ideas and…
Q: Write a note on Double Data-Rate Synchronous DRAM (DDR SDRAM). ?
A: DDR SDRAM operates under the tenet that data can be sent on both the rising and falling edges of a…
Q: Create a AWS glue job and write a python program to check if a given number is prime or not in AWS…
A: The above question is solved in step 2 :-
Q: Is there any legal repercussions to mobile phone usage that businesses should be aware of?
A: Legal Repercussions: The term "legal consequence" refers to the effect of an action that either…
Q: What Network Layer protocol is used for HTTP applications? IP BootP UDP TCP
A: Introduction: The Hypertext Transfer Protocol (HTTP) is a networking protocol for hypermedia…
Q: t and GUI interface needed. Take help
A: I have designed GUI below:
Q: A DMA module is transferring characters to memory using cycle stealing, from a device transmitting…
A: It is defined as Direct Memory Access is a technique for transferring data within main memory and…
Q: What information is required to be known a priori by the banker's algorithm in order to avoid a…
A: Here is the solution:
Q: Design a SOQL query to fetch all the permission sets and profile that have the Account, Contact and…
A: Introduction: Use the Salesforce Object Query Language (SOQL) to search your Organization's…
Q: (a) Where might a datagram be queued inside a router to wait for further processing? (b) How does…
A: The computer networks are the set of the computers that are interconnected with the transmission…
Q: A microprocessor scans the status of an output I/O device every 20 ms. This is accom- plished by…
A: A microprocessor is a computer processor where the data processing logic and control is included on…
Q: Describe any three appropriate sorts of challenges that may be implemented using reinforcement…
A: Given: The field of artificial intelligence known as reinforcement learning (RL) is concerned with…
Q: Label the Recursion Requirements. int fact (int n) ( int result; } if(n==1) return 1; result return…
A: According to the information given:- We have to label the recursion requirement and show the…
Q: Explain how each of the eight cost estimating methods may be used with different heuristic rules…
A: Database Management System: Database Management System (DBMS) software is used to store and retrieve…
Q: The significance of continuous event simulation, in addition to four justifications for why it…
A: There are four main reasons for the significance of continuous event simulation: An environment free…
Q: Suppose the page table for the process currently executing on the processor looks like the…
A: a) A Virtual address generated by the CPU is translated into physical main memory address by a…
Q: It is one of the reasons why Cleanroom Software Engineering is so effective because its core concept…
A: The question has been answered in step2
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: INTRODUCTION Memory capacity is how much memory that can be utilized for an electronic gadget like…
Q: Write detailed code for Fibonacci sequence number print in go programming language code and give…
A: Logic:- define a function for Fibonacci series display. Set p=0, q=1 and r=q display p, q use for…
Q: XTR2. FUL Write a program that reflect the cricket game by taking input of two teams having three…
A: Code is given below #include <stdio.h> #include<time.h> void batting_inning(int…
Q: Write a note on Storage Technologies ? Give some examples of storage ?
A: A space in a system or computer where data can be stored and retrieved later whenever required is…
Q: What is the language for the following Pushdown Automata? (a,s/A) (CE/E) 8 qo O A. O B. O C. O D.…
A: In this question we have to select the language for the given push down automata. Let's discuss and…
Q: any idea how to do this 1.Run a 100 user load test on the performetriks.com website
A: Answer:we need to write some point regarding the responsive website
Q: What advantages does utilizing virtual memory offer?
A: Virtual Memory:- Virtual Memory is a storage allocation scheme in which secondary memory can be…
Q: Java - How to make this a horizontal statement with a newline. Whenever I use System.out.println, it…
A: We need to find method of how to make a horizontal statement with a newline. If System.out.println…
Q: What is the equivalent regular grammar for the following context free grammar?. S→AB; A→aa;…
A: Two regular expressions R and S are equivalent if they describe the same language. In other words,…
Q: Suppose the page table for the process currently executing on the processor looks like the…
A:
Q: Cloud computing has had what, if any, effect on people's ability to work together well.
A: Introduction: Cloud computing is a catch-all term for any activity involving delivering hosted…
Q: Suppose the page table for the process currently executing on the processor looks like the…
A: (a) Split the binary address into a VPN and also an offset. Use VPN binary address as an index into…
Q: use c++ by Using dynamic arrays, implement a polynomial class with polynomial addition, subtraction,…
A: Code is given below #include <iostream> #include <cmath> #include <cstdlib>…
Q: (a) What different switching mechanisms exist to forward datagrams from an input port to an output…
A: a) There are 3 switching mechanisms that exist Circuit switching - creates a virtual network Packet…
Q: Alter the MAINTENANCE_TYPES table to include a new column named MAINTENANCE_PRICE of type FLOAT.
A: ALTER TABLE MAINTENANCE_TYPES ADD MAINTENANCE_PRICE float; Alter Query is used to change the DDL…
Step by step
Solved in 2 steps with 5 images

- INT_MIN = -32767 def cut_rod(price): """ Returns the best obtainable price for a rod of length n and price[] as prices of different pieces """ n = len(price) val = [0]*(n+1) # Build the table val[] in bottom up manner and return # the last entry from the table for i in range(1, n+1): max_val = INT_MIN for j in range(i): max_val = max(max_val, price[j] + val[i-j-1]) val[i] = max_val return val[n] # Driver program to test above functionsarr = [1, 5, 8, 9, 10, 17, 17, 20].Question 6 Let A = {a, b} and B = {c, d} and C = {0}. Compute the following sets: a. A X (B X C) b. A X C ..Q1. Srikanth is a school student. He studies in class 8th. One day his Math’s teacher came to the class and told them that he is going to start a new chapter “Measurement”. In order to give them a demo of that chapter, he told the students to find the volume of the class room using Volume( ). Input Constraint 15<=Length<=25 10<=Breadth<=20 20<=Height<=30 Note:- It needs to be solved in Dev C++ using #include<stdio.h>
- Q2. ""Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i. .True or false set{(x,x2):x∈Z}canbeseeasafunctionZ→Q. set{(x2,x):x∈Z}canbeseeasafunctionZ→Q.Count consecutive summers def count_consecutive_summers(n): Like a majestic wild horse waiting for the rugged hero to tame it, positive integers can be broken down as sums of consecutive positive integers in various ways. For example, the integer 42 often used as placeholder in this kind of discussions can be broken down into such a sum in four different ways: (a) 3 + 4 + 5 + 6 + 7 + 8 + 9, (b) 9 + 10 + 11 + 12, (c) 13 + 14 + 15 and (d) 42. As the last solution (d) shows, any positive integer can always be trivially expressed as a singleton sum that consists of that integer alone. Given a positive integer n, determine how many different ways it can be expressed as a sum of consecutive positive integers, and return that count. The number of ways that a positive integer n can be represented as a sum of consecutive integers is called its politeness, and can also be computed by tallying up the number of odd divisors of that number. However, note that the linked Wikipedia de0inition…
- equality (5)/(9)x+(0)/(2)>=(5)/(2)x+(1)/(6). Enter your answer using intDebug the following program and answer the following questions. #include <stdio.h> typedef struct node { int value; struct node *next; } node; int ll_has_cycle(node *first) { node * head = first; while (head->next) { head = head->next; if (head == first) return 1; } return 0; } void test_ll_has_cycle(void) { int i,j; node nodes[5]; for(i=0; i < sizeof(nodes)/sizeof(node); i++) { nodes[i].next = NULL; nodes[i].value = i; } nodes[0].next = &nodes[1]; nodes[1].next = &nodes[2]; nodes[2].next = &nodes[1]; printf("Checking first list for cycles. There should be a cycle, ll_has_cycle says it has %s cycle\n", ll_has_cycle(&nodes[1])?"a":"no"); printf("Checking length-zero list for cycles. There should be none, ll_has_cycle says it has %s cycle\n",…Write a classifier algorithm for p(Y |X,α)
- Edit this program so that it returns ecg data instead of heart beat in BPM. #include <ArduinoBLE.h> #define BLE_UUID_HEART_RATE_SERVICE "180D"#define BLE_UUID_HEART_RATE_MEASURMENT "2A37"#define ECG_SERV_UUID 0x2D0D#define ECG_MEAS_UUID 0x2D37#define ECG_NUM_CHANS_UUID 0x2D38#define ECG_SAMPLE_SETS_UUID 0x2D39#define ECG_COMMAND_UUID 0x2D3A #define HRM_VALUE_FORMAT_8BIT 0#define HRM_VALUE_FORMAT_16BIT 1#define HRM_SENSOR_CONTACT_NOT_DETECTED ( 2 << 1 )#define HRM_SENSOR_CONTACT_DETECTED ( 3 << 1 ) typedef struct {uint8_t flags;uint8_t heartRate;} heart_rate_measurment_t; union heart_rate_measurment_u{struct {heart_rate_measurment_t values;};uint8_t bytes[ sizeof( heart_rate_measurment_t ) ];}; union heart_rate_measurment_u heartRate = { .values = { .flags = 0, .heartRate = 0 } }; #define BLE_DEVICE_NAME "Arduino HRM"#define BLE_LOCAL_NAME "Arduino HRM" BLEService heartRateService( BLE_UUID_HEART_RATE_SERVICE );BLECharacteristic heartRateCharacteristic(…last 3 digits of enrolment number - 308 Let a, b and c denote the last three digits of your enrolment number (so for example with enrolment number 001054321, you would take a = 3, b = 2 and c = 1) and then take each of them (mod 2). So in the example above, a, b and c would become 1, 0, 1 respectively (each digit taken (mod 2)). Consider the polynomial . (a) Create a polynomial code of codeword length 8 from this generating polynomial. (b) Is your code cyclic? Justify your answer.int a[10] = {0,1,2,3,4,5,6,7,8,9};int *m = &a[0];int *p = &a[5];int *q = &a[1]; p = (int) m + (int) p - (int) q; what is the value of of *p



