Language: C Find the maximal value of an array using pointers. To this end define the function that returns the pointer to the element with the maximal value of array, and takes as the input the pointer to the array, and the array size. Print the original array, and the value dereferenced from the returned pointer. Problem 3.
Language: C Find the maximal value of an array using pointers. To this end define the function that returns the pointer to the element with the maximal value of array, and takes as the input the pointer to the array, and the array size. Print the original array, and the value dereferenced from the returned pointer. Problem 3.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter10: Pointers
Section: Chapter Questions
Problem 4PP
Related questions
Question
100%
Language: C
Find the maximal value of an array using pointers. To this end define the function that returns the pointer to the element with the maximal value of array, and takes as the input the pointer to the array, and the array size. Print the original array, and the value dereferenced from the returned pointer.
Problem 3.
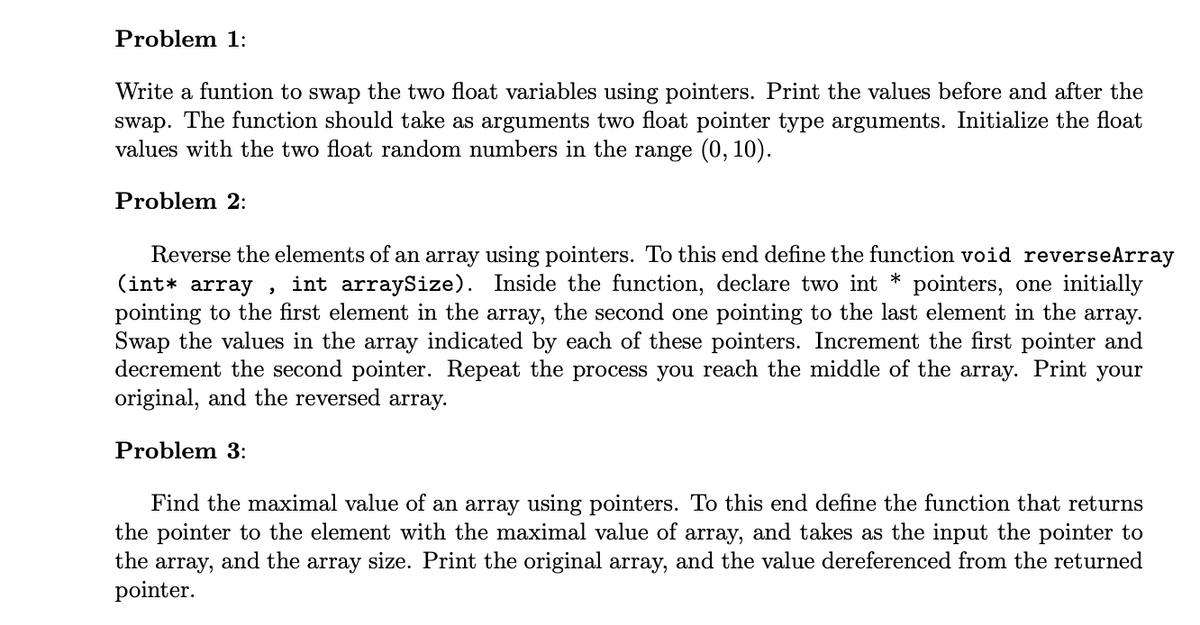
Transcribed Image Text:Problem 1:
Write a funtion to swap the two float variables using pointers. Print the values before and after the
swap. The function should take as arguments two float pointer type arguments. Initialize the float
values with the two float random numbers in the range (0, 10).
Problem 2:
Reverse the elements of an array using pointers. To this end define the function void reverseArray
(int* array,
int arraySize). Inside the function, declare two int * pointers, one initially
pointing to the first element in the array, the second one pointing to the last element in the array.
Swap the values in the array indicated by each of these pointers. Increment the first pointer and
decrement the second pointer. Repeat the process you reach the middle of the array. Print your
original, and the reversed array.
Problem 3:
Find the maximal value of an array using pointers. To this end define the function that returns
the pointer to the element with the maximal value of array, and takes as the input the pointer to
the array, and the array size. Print the original array, and the value dereferenced from the returned
pointer.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr