lement Bubble sort !
Q: What are the two kinds of IP security measures you may take?
A: The answer of the question is given below
Q: Which shortcomings are there in the Whetstone, Dhrystone, and Linpack benchmarks, and how do they…
A: Introduction: Dhrystone is a synthetic computing benchmark software that was built in 1984 by…
Q: When will the inevitable glitch occur? What's the deal with context switching in all of this?
A: In the Operating System, there are cases when you have to bring back the process that is in the…
Q: Give an explanation as to why it is preferable to make use of the batch processing method rather…
A: An operating system is software which act as an intermediate between user and computer hardware.
Q: In moving from a serial processing system to a batch processing system, what do you think is the…
A: Answer:
Q: What exactly does it mean when someone asks about the core service set configuration of a wireless…
A: Introduction: Wireless network: It is a kind of computer network in which wireless data channels are…
Q: It is impossible to get a digital certificate for a single public key without revealing the…
A: Public key: A public key is a large number used in cryptography to encrypt data. A software program…
Q: Using a static route would be suitable in what sorts of situations, and when?
A: The Answer is given below step.
Q: Which architectural pattern is the most suitable for software systems in which one component creates…
A: The architectural pattern captures the design structures of various systems and elements of…
Q: Given: 13-Node Graph O 75 ΑΠ 118 T Z M to B-241 O to B-380 P to B-100 RV to B-193 140 S to B-253 T…
A: Please refer below for your reference: The A* algorithm helps us in searching for the shortest path…
Q: What is the most crucial aspect of the transition from serial to batch processing?
A: Introduction: The most important change that came about as a result of switching from serial to…
Q: How many 2-line-to-4-line decoders are required for a 1-line-to-16-line decoder?
A: Option C is correct : 5
Q: What does "out of band" mean? In symmetric encryption, why is it necessary to swap keys out of band?
A: Introduction Out of band is the capacity to interface with far-off frameworks like switches,…
Q: Problem No.4 Given: 13-Node Graph 0 A 75 118 DZ T E 140 70 75 D 151 OM S 120 80 D 8 99 RV 5 146 138…
A: to calculate greedy best first search for the graph.
Q: Why is exploratory data analysis necessary? You may question why we can't simply get directly into…
A: Introduction: Exploratory data analysis, often known as EDA, is a kind of data analysis that…
Q: What is the difference between a digital signature and other authentication methods?
A: A digital signature is a kind of authentication that enables the message's sender to append a…
Q: Which aspects of security do various methods of authentication strengthen and which do they weaken?
A: Answer:
Q: nces of deadlocks that are not related with a computer system environment are sho
A: Introduction: Below describe the Three instances of deadlocks that are not related with a computer…
Q: It has been determined what first gave rise to the hierarchical structure of the file space.
A: Digital information is arranged and structured on a computer using a hierarchy of folders and…
Q: In your opinion, which of the following aspects of transitioning from a system that processes data…
A: Transitions in a System: A transition system is a notion that is used in the study of computing…
Q: What are the exact objectives of authentication? Compare and contrast the pros and cons of different…
A: INTRODUCTION: Different certificates may be connected in a certificate chain. When a certificate…
Q: Under what circumstances are threads running at the user level preferable to those running at the…
A: Thread: A thread is a flow of execution through the process code. It has its own programme counter…
Q: Discussion 4.1 I/O Devices List all the criteria you consider in choosing peripheral devices for…
A: Following factors can be considered while selecting peripheral device for a computer 1.Hardware…
Q: Symmetric encryption has both benefits and drawbacks. What factors need to be taken into account…
A: Synchronous encryption: As opposed to symmetric encryption, asymmetric encryption does not need the…
Q: Describe some of the elements that make up an algorithm.
A: An algorithm is a method that describes a series of steps that must be followed in a precise…
Q: Talk about how processes and threads compare and contrast with one another, as well as the…
A: PROCESS THREAD Processes are heavyweight operations. Threads are lighter weight operations. Each…
Q: Can you think of a decent implementation of the Boyer-Moore string search algorithm in the…
A: Given: Boyer-Moore-Horsepox is an algorithm for identifying substrings inside strings. This…
Q: What precisely is meant by the term "routing," and how does the process work? Describe in great…
A: The central point around which: The whole of IP availability revolves is routing. At its most…
Q: Adding modules from the highest level to the lowest level is known as "top-down programming," and…
A: Likewise called "stepwise refinement," a product improvement method forces a progressive structure…
Q: An algorithm is the name given to the detailed set of instructions that may be followed to solve a…
A: Having said that: An "algorithm" is the term given to the series of step-by-step instructions that…
Q: What's the difference between a web app and a desktop app when it comes to testing?
A: The answer to the question is given below
Q: A discussion of the distinctions between threads and processes, as well as the scheduling of…
A: Threads and process are very important entities while executing a program.
Q: a distinct difference between subqueries correlated and uncorrelated
A: Solution :- In the above question, the statement is mention in the above given question Need to…
Q: The Boolean expression for the output f of the following combinational logic circuit Q OR R R Select…
A: According to the information given:- We have to choose the correct option to satisfy the expression…
Q: The analytical method relies heavily on the use of data modelling. In order to build a model, we'll…
A: Regarding data modelling, it specifies how data should be employed to meet the customer-specified…
Q: When comparing TCP and UDP, what's the difference? These two methods vary in four important way
A: Answer : TCP : 1) Connection oriented protocol 2) It is slow . 3) It guarantee to send the data to…
Q: What precisely does it mean to schedule anything "preemptively"?
A: This inquiry is related to anticipatory scheduling: Making a Plan in Advance One process will…
Q: Consider a database system that is impenetrable by failures. Do I need a recovery manager to use…
A: Consider a database system that is impenetrable by failures. Do I need a recovery manager to use…
Q: i would appreciate it if you could help me out with the image above. thank you!!!!
A: create process hook create function processhook and add parameters to them. then run function…
Q: The term "positive testing" refers to the process of ensuring that newly developed software does, in…
A: Testing is one of the most crucial stages in case of a software development.
Q: What exactly does it mean to work on an algorithm?
A: INTRODUCTION: The word Calculation implies ” A set of rules to be taken after in calculations or…
Q: how do i get the sqrt of 2223423422
A: The long division method is used for finding the square root of large numbers. 1) Place a bar over…
Q: What will the future of AI be like? Do we have AI software? How scary is AI?
A: AI software: Artificial intelligence is an area of computer science that develops intelligent…
Q: Digital certificates and digital signatures are not the same thing.
A: A digital signature and a digital certificate are different in that a certificate links a…
Q: What aims does the authentication procedure serve? Differentiate the benefits and drawbacks of…
A: Authentication is determining whether a person or object is actually who or what it claims to be.…
Q: When and why would one choose to use the time-sharing processing method rather than the batch…
A: Batch processing is a method for automating and processing multiple transactions collectively. Batch…
Q: In other areas than systems analysis, such as engineering and manufacturing, see whether Structured…
A: Systems Analysis It is a process of collecting and interpreting facts, identifying the problems, and…
Q: The D flip-flop consists of two cascaded D-Latch has Select one: O Q2' feeds the input D1 O Q1'…
A: 1-c 2-c 3-a
Q: Within the context of a three-tier architecture, the phrase "third tier" refers to the layer that…
A: "third tier" refers to the layer that serves as an intermediate between the client servers and the…
Q: In what ways do the SPEC CPU benchmarks improve upon the weaknesses of the Whetstone, Dhrystone, and…
A: SPEC CPU benchmarks: A computer benchmark for CPU integer processing speed is called SPECint. The…
Implement Bubble sort !
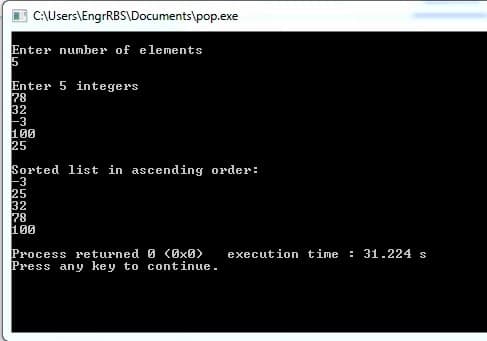
Step by step
Solved in 3 steps with 3 images

- C++ Quadratic Probing: You have a file called athletes.txt Jamie, basketball Justine, soccer Ned, badminton Shelley, hopscotch etc... The file contains 9 athletes. The user will specify the size of the hash table. Write a function that keeps track of the total number of collisions and searches into the hash table. Each index is assigned hash_index = i % table_size where "i" is an int in a for loop up to table_size If the table is full then: int t = (hash_index + i* i) % table_size; Display the number of collisions and searches.Which of the basic data structures is the most suitable if you want to be able to insert elements in the middle in (assume you have already known the location for insertion)? A. Array B. Queue C. Linked list D. Stackdef delete_item(...): """ param: info_list - a list from which to remove an item param: idx (str) - a string that is expected to contain an integer index of an item in the in_list param: start_idx (int) - an expected starting value for idx (default is 0); gets subtracted from idx for 0-based indexing The function first checks if info_list is empty. The function then calls is_valid_index() to verify that the provided index idx is a valid positive index that can access an element from info_list. On success, the function saves the item from info_list and returns it after it is deleted from info_list. returns: If info_list is empty, return 0. If is_valid_index() returns False, return -1. Otherwise, on success, the function returns the element that was just removed from info_list. Helper functions: - is_valid_index() """
- Create the bfree (p, n) procedure to release any block of characters between p and n into the free list that is kept up to date by mal10c and free. A user can at any moment add a static or external array to the free list by using the bfree command.Consider a list named NUM which elements are [3, 12, 5, 6, 8], which code will delete element last? a. NUM.append(8) b. NUM.pop() c. NUM.remove() d. NUM.insert()Code an application program that keeps track of student information at your college. Include their names, identification numbers, and grade point averages in a fully encapsulated, homogeneous sorted singly linked list structure. When launched, the user will be asked to input the initial number of students and the initial data set. Once this is complete, the user will be presented with the following menu: Enter: 1 to insert a new student's information, 2 to fetch and output a student's information, 3 to delete a student's information, 4 to update a student's information 5 to output all the student information in sorted order, and 6 to exit the program. The program should perform an unlimited number of operations until the user enters a 6 to exit the progrqm Please use java use deep copy
- Which of the basic data structures is the most suitable if you only need to insert the elements in the back and to extract elements from the front? A. Array B. Queue C. StackWrite a program that creates a linked list to represent details of students. The following details must be kept for each student: SID (for Student ID) Name Address Age Gender Your program must also display a menu to perform the following tasks: Create a linked list. Note: The method to create a linked list makes use of the method insertFirst() or insertLast() or insertOrdered() Insert new nodes to the linked list. Search for details pertaining to a particular student. Delete details of a particular student. Find number of nodes in the linked list. Display information pertaining to all students. The menu options should be as follows: Create linked list Add new student Search for a student Delete a student Find number of students Print student details Exit YOU SHOULD CREATE YOUR OWN NODE CLASS, AND YOU MUST NOT USE JAVA LINKED LIST LIBRARY.130. The linked list formed by the deleted records is called as ______ a. Delete list b. Free list c. Null list d. Non-existent list
- in c++ Create a single linked list that contains the data (age) of your friends. Perform basic operations including insertion, deletion, searching and display. The insertion operation should only allow a friend’s data to be inserted in sorted order only.PYTHON PROGRAMMING Given: courses = ['tech-100', 'mt-900', 'ee-101', 'arch-111']avgs = [86.75, 73.64, 96.87, 85.21] 1) Create a dictionary, courseAvgs by using the two given lists above.2) Use a loop to print all keys and values in the dictionary courseAvgs.3) Print the dictionary courseAvgs. Make sure to precisely match the output format below. Example OutputTECH-100: 86.75 | MT-900: 73.64 | EE-101: 96.87 | ARCH-111: 85.21 | {'tech-100': 86.75, 'mt-900': 73.64, 'ee-101': 96.87, 'arch-111': 85.21}Linked list consist of items such that each item could have different data type Select one: True False

