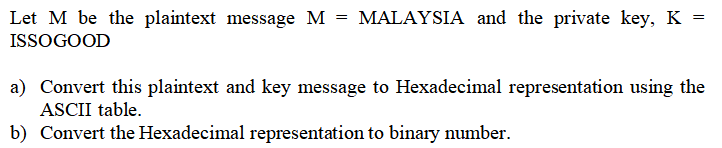
Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD a) Convert this plaintext and key message to Hexadecimal representation using the ASCII table. b) Convert the Hexadecimal representation to binary number.
Q: What are binary values?
A: Binary Value:-
Q: write Program: encrypt the text by caeser algorithm.plaintext:Ali K=3
A: Below is the required python program: - Caeser algorithm: - Input the string as the plain text. An…
Q: The number of rounds in AES is variable and depends on the length of the key and AES uses 10 rounds…
A: AES stands for Advanced Encryption Standard AES uses symmetric key encryption, which involves the…
Q: 1. Let x be the first two digits of your matric number (group leader), y be the last two…
A:
Q: 24. Refer to Table 6–2. Determine the string of ASCII codes for the following message including the…
A: Answer for the first Question. Please find the ASCII codes of each character. C- 01000011 A-…
Q: Construct a DFA defined as L = { w = {0,1}*: w, when interpreted as a binary number is divisible by…
A:
Q: Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD Convert this…
A:
Q: How many eight-bit binary strings contain exactly 3 1s? How many eight-bit binary strings contain…
A: The question has been answered in step2
Q: and bl, 1101 1111B is to a. clear bl b. store 'B' in bl c. store 0010 0000 in bl d. leave bl…
A: According to the question
Q: Bit strings consist of 0 and 1. How many bit strings of length 7 either start with “1” or end with…
A: Answer: D. 16
Q: Use C++
A: The answer to the following question:-
Q: What is the minimum number of bits that are needed to represent 2050 different values?
A: The question is what is the minimum number of bits that are needed to represent 2050 different…
Q: a. Decode the encoded message by using the key matrix [1222] 27 28 48 56 9. 18 38 38 33 54 28 28…
A: Encoded message matrix [27 48 9 38 33 28 28 56 18 38 54 28] Let the above…
Q: limit? What is the expected error with this optimum value? (b) Consider the expression 1020 + 424 –…
A: Answer: I have given answered in the handwritten format in brief explanation.
Q: Assume that the payload contains the 8-bit ASCII code for the string "DOG". Recall that the ASCII…
A:
Q: Suppose the prime p = 251 and base s = 53 are %3D establish an 8-bit keyword for binary Vigenère en…
A: Please find the solution below in second step:- Kindly upvote if you find the answer helpful.
Q: A sender needs to send the four data items 0x1236, OXABCC, OX03BC, and 0XEEEE. To avoid confusion,…
A: The answer is
Q: Give a code example (by listing its codewords) which is uniquely decodable but not a prefix code
A: Let us consider the following code 00 01 10 11 Let us have each two digit refers to some block in…
Q: III. Encode the following messages using the given message and the value of r.
A: Here we have given the solution for the given source encoding with r value to channel encoding
Q: Solve this attachment.
A: 1.Little Endian :It is used to store the multi data type binary numbers .In LE format , the…
Q: Q/ Write Program to lind the maximum element for malrix (3||3] the first element of the first row…
A: Solution: 1. This question based on assembly language 2. we have to find maximum element for…
Q: (1) Find a quote that you like. Make sure that the total number of characters is at least 50 and no…
A: GHIHQG WJH HDVW ZDOO RI WKH FDVWOH Julius Caesar (100 BC - 44BC) could have sent this message!…
Q: 1.2-2 Find the first 5 digits of .1 written as an octal fraction, then compute from it the first 15…
A: Given decimal .1 we have find the octal formation
Q: Q3) ● Construct the Hamming codeword for the message 0011. Decode the received Hamming codeword…
A: Dear Student, In our message number of data bits is 4 ie 0011 . Now I am constructing the hamming…
Q: 2. Decode (get base 10 value of) the following bit patterns using the floating-point format…
A:
Q: or AX, set bits b3, b5, b13, complement even bits of
A: 1)AX, set bit b3,b5,b13 Before execution Before execution AH…
Q: Find the domain and range of these functions. Note that in each case, to find the domain, determine…
A: Solution a: The number of ones minus number of zeros in a bit string is always an integer.…
Q: Question 3: Present the following decimal numbers in a Signed Form Binary Numbers. Note: Signed…
A: Actually, binary numbers are nothing but a 0's and 1's.
Q: y A = 52 and Bob sends public key E
A: Actually, given that parameters p=71,α = 7 public key A=52, Bob sends public key B=37.
Q: Tou are given a string that was encoded by a Caesar cipher with an unknown distance value. The text…
A: Printable ASCII characters range from 32 (decimal value) to 126 (if we consider spaces, otherwise…
Q: Using ROT13, the character 'C' will be encrypted as. O a. R O b. Q O c. P O d. O
A: Rot13 is a simple "encryption" algorithm designed to make text illegible, but very easily…
Q: Why do we use binary encodings to represent information in the computer? What would be the pros and…
A: Binary codes: A binary code is a method of representing text or computer processor instructions…
Q: 1. Write the converse of the following: If you are happy, then you will sing. b) Convert (94A8)16 to…
A: The above question is solved in step 2:-
Q: Given 01010101 and 10101010, provide the following: a.AND b. OR c.XOR d. NOT (per individual…
A: Given: Given 01010101 and 10101010, provide the following: a.AND b. OR c.XOR d. NOT (per…
Q: [29 481 56 76 58 78 Decode the matrix L7 12 J using the inverse of the matrix L3 a MEZQUITE b…
A: 1. Take the string of coded numbers and multiply it by the inverse of the matrix that was used to…
Q: (n integer; fleld should be the primary key) Author name (short text/120 characters) Book name…
A: Actually, given question regarding book table.
Q: Write Shariq Ahmad in ASCI, i.e., each letter in Shariq Ahmad should be written as the ASCII code…
A: ASCII stands for American standard code for information interchange. Here each character,special…
Q: Fill in the Blank Convert the following cyphertext to plaintext. Let N = 125 and k = 46. Use the…
A: According to given scenario K=46 N=125 ciphertext c=71 decrypted message is given by…
Q: The following table shows the number of symbo occurrence in a message:
A: Huffman coding creates a tree using the frequency of the symbols. encoding and decoding are done…
Q: v [ Choose ] obsolete from the 1970's; uses just one 56-bit key symmetric algorithm; supports 128,…
A: DES Data Encryption Standard
Q: Encode the message by using a cyclical alphabetic encrypting code that shifts the message the stated…
A: The cyclical alphabetic encrypting code is also called as Caesar code which shifts the given plain…
Q: (a) Take the last 8 digits of your student number and take mod 2 of each digit. (b) Convert your row…
A: (a) To get the mod value we have to divide the number and the remainder we get is the mod…
Q: 2933 (for decrption) Assuming a=01, b=02, . , z=26, and we group the digits in groups of three. (ii)…
A: The answer is
Q: 2. Let C = {000, 001,010, 011}. Determine the error patterns that C will correct using the IMLD…
A: We know that the syndrome of a received vector is equal to the syn-drome of the error pattern. If r…
Q: will dislike A) 1.0 x 2^127 is the largest absolute number that can be represented in the 32-bit…
A: A) 1.0 x 2^127 is the largest absolute number that can be represented in the 32-bit representation…
Q: These are the Base64 encodings for characters H, E, L, P, 0, 1, 2, 3: H 000111 E 000100 L 001011 P…
A: We have to encrypt the message HELP with the one-time pad 0 1 2 3,using bitwise exclusive or and…
Q: 3. The following hexadecimal strings represent floating-point numbers in 32-bit IEEE standard.…
A: BD680000 Above Hex value is converted to Binary then, Binary value will be B D 6 8 0 0 0 0 1011…
Q: a sequence is encoded using lz77 algorithm that c(a)=1, c(e')=2, c(r)=3, c(t)=4 then decode the…
A: Greetings. In the LZ77 compression algorithm, the triples carry the following meaning :
Step by step
Solved in 2 steps with 1 images

- Practice using multiplicative ciphers to encode and decode a message: 1. Find quote that you like. Make sure that the total number of characters is at least 50 and no more than 100. 2. Then pick an acceptable number (not every number between 1 and 26 is acceptable) that is between 3 and 25 as your multiplicative key. Share this key. 3. Create a table of correspondence of 26 alphabets in plaintext and the ciphertext. (4) Use the table of correspondence to encode the quote you found in Part (1). Post the encrypted message in groups of three letters in the discussion forum. For example, here is another quote from John Dewey Education is not preparation for life; education is life itself. We will use multiplicative key 17. The table of correspondence between plaintext and ciphertext is as follows. (image attached Thus the encrypted message is GPS YQB WUD WKD UBL TGL QTQ BWU DXU TVW XGG PSY QBW UDW KVW XGW BKG VX (5) Pick an encrypted message from your classmate and try to decrypt…1. Find quote that you like. Make sure that the total number of characters is at least 50 and no more than 100. 2. Then pick an acceptable number (not every number between 1 and 26 is acceptable) that is between 3 and 25 as your multiplicative key. Share this key. 3. Create a table of correspondence of 26 alphabets in plaintext and the ciphertext. (4) Use the table of correspondence to encode the quote you found in Part (1). Post the encrypted message in groups of three letters in the discussion forum. For example, here is another quote from John Dewey Education is not preparation for life; education is life itself. We will use multiplicative key 17. The table of correspondence between plaintext and ciphertext is as follows. (image attached) Thus the encrypted message is GPS YQB WUD WKD UBL TGL QTQ BWU DXU TVW XGG PSY QBW UDW KVW XGW BKG VX (5) Pick an encrypted message from your classmate and try to decrypt it. Remember in this discussion question, you will have the…p and q are two prime numbers. p=3 and q=11. take public key e=3. if original message is 00111011,then what will be cipher text value &private key valus according to RSA algorithm? Again calculate plain text value from cipher text
- The following message uses a direct mapping of letters to numbers (i.e. A-1, B=2, c-3, etc.).Using the values D=17 and m=21, decrypt the following message:10 15 12 18 1 3 17 14 7 18 14 17 17 9 18 14Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD. Using the appropriate steps of DES operation, get the final output of the key for round 1 with the permutation compression (PC) table provided below, In round 1, get the output for the XOR operation of plaintext and the key, according to the DES operation. a) Based on the output above, explain the next process using the S-box table, and show the output from this operation.lice and Bob shares a secret 8-bits key “10110110” for encryption using XOR. Alice wishto encrypt the following message to Bob: “NOMEETING”Refer to UTF-8 encoding to get the binary code for the letters, and then apply the key to each letter. Write the corresponding ciphert text in binary.
- Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD. Using the appropriate steps of DES operation, get the final output of the key for round 1 with the permutation compression (PC) table provided below, In round 1, get the output for the XOR operation of plaintext and the key, according to the DES operation. a) Based on the output above, explain the next process using the S-box table below, and show the output from this operation. DO NOT COPY and PASTE! I asked four times already!Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD. Using the appropriate steps of DES operation, get the final output of the key for round 1 with the permutation compression (PC) table provided below, In round 1, get the output for the XOR operation of plaintext and the key, according to the DES operation. a) Based on the output above, explain the next process using the S-box table below, and show the output from this operation. DO NOT COPY and PASTE!The message "KRUDEYZMSYIOEAAUONYRYEEFJVDZ" was encoded using a transposition cipher with column order 3, 1, 2, 4. Decode the message. Enter it in all caps, with no spaces. Include any extra filler letters that were added at the end of the message.
- Assume p=11 and q=17, e=7 and M=2. Find the private key d, sign and verify the message using RSA signature.Let M be the plaintext message M = MALAYSIA and the private key, K = ISSOGOOD Using the appropriate steps of DES operation, get the final output of the key for round 1 with the permutation compression (PC) table provided below, For round 1, get the output for the XOR operation of plaintext and the key, according to the DES operation. Based on the output above, explain the next process using the S-box table, and show the output from this operation. Based on the output of of 4(a), explain the next process using a straight permutation table, and show the output from this operation.N blocks of plaintext (P1 to PN) are being encrypted in CFB mode into ciphertext (C1 to CN). Assume that two bits of C3 are erroneous (their binary values have flipped). What bits of C3, C4, and C20 are erroneous?

