Let U = {x e N:1
Q: What is the function of ergonomics in the computing field? Describe the ergonomics-recommended safet...
A: why ergonimics People spend most of the day in front of a computer without thinking about the impac...
Q: Design a brute-force algorithm for computing the value of a polynomial (in the image below) at a giv...
A: INTRODUCTION: Here we need to designed a algorithms of 0(n^2) and reduced it.
Q: There are various trade-offs and challenges to consider while shifting from a custom solution to an ...
A: Introduction: In corporate level solutions, individual users must have some control over their data.
Q: What was the motivation behind the development of computer programming languages?
A: Introduction: Language for showing a precise set of digital computer commands, such as computer prog...
Q: t is the largest decimal value it is able to sto
A: If a register has 9 bits, what is the largest decimal value it is able to store?
Q: What are the characteristics of Bluetooth
A: answer is
Q: all truth assignments. If it is satisfiable
A: Lets see the solution.
Q: How can you make Internet Explorer operate in Standards mode?
A: Introduction: Actually, the internet is a global network of computers that works much like the posta...
Q: How many cycles will it take to process all instructions
A: Instruction Meaning of Instruction L1: add $t1, $t2, $t3 $t1 <- $t2 + $t3 L2: sub $t2, $t...
Q: 1a) Pick any commercial CPUs available in state-of-the-art and identify their multilevel caches and ...
A: A central processing unit also know as central processor, the main processor is the electronic cir...
Q: If a software team is planning to develop a user interface on a smart phone, you must explain how di...
A: Introduction When a team started developing a software project, there is five tasks to implement use...
Q: Why is there a compromise on Data Integrity in File Management Systems but not in Database Approache...
A: Introduction: System for Organizing and Managing Files The file management system is used to store a...
Q: Alice and Bob want to play the following game by alternating turns: They have access to a row of n c...
A:
Q: What are the various methods for putting audio into PowerPoint slides?
A: There are three different ways to insert audio from the Audio menu. First, you need to click Insert ...
Q: What has changed in SE's requirements?
A: Introduction Requirement Change Management Techniques in Software Systems Requirement change: Req...
Q: What do you mean by subnet mask?
A: IP Address: Ip address stands for Internet Protocol address. An IP address is a unique number provid...
Q: Display a 64-bit instruction format with 64 instructions and the remaining bits reserved for address...
A: Introduction Instruction format depicts the inward constructions (format plan) of the pieces of in...
Q: what is IoT or internet of things
A: The solution to the given problem is below.
Q: rite a C program to implement clique problem. pls provide pseudocode and screen shot of the output.
A: #include <bits/stdc++.h>using namespace std; const int MAX = 100; int store[MAX], n; int graph...
Q: Give the appropriate approach for speedy development in SE, as well as the justification behind the ...
A: Introduction: Rapid Application Development (RAD) is a development strategy that favours rapid proto...
Q: Identify and explain the five features of an algorithm.
A: Introduction The following are the features of a good algorithm: Precision: a good algorithm must ...
Q: yntaxError: EOL when scanning strin reral
A: Given:
Q: What are hashes? Give an example.
A: Hashing is simply the process of running data through a formula that creates a result known as a has...
Q: List five Internet-based services that are not now accessible but that you believe will become avail...
A: The answer is given below:
Q: You need to take any graph and add apply Page algorithms till convergence. Take any document and que...
A: Lets see the solution.
Q: An airline firm LTd limited was looking for a solution that would allow them to dynamically bundle h...
A: Intro Actually, given information regarding airline company LTd
Q: Compare and contrast cache memory and magnetic disk storage in a computer system with respect to the...
A: Please find the detailed answer in the following steps. Note: As per the Bartleby guideline I can...
Q: Describe how the implementation of the following style rule differs between Internet Explorer operat...
A: Explanation: Internet Explorer shows a mild difference when running in Quirks mode and standard mod...
Q: Find as many errors as you can and rewrite the function correctly. void total (int valuel, value2, v...
A: Code of screenshot is given below-
Q: What steps would you use as a Malware Expert to analyse a portable executable (PE) and determine if ...
A: Intro According to the practices or reaction of some module or of the entire system, specialists b...
Q: from parsimonious import Grammar' must be used for your Python code I am currently still a beginner...
A: from pythonds.basic import Stackfrom pythonds.trees import BinaryTree def buildParseTree(fpexp): ...
Q: Write a program to evaluate a postfix expression. The string S input by user in the form of postfix ...
A: Program Explanation: Declare the required header files Define an array for stack implementation Def...
Q: Adjacency matrix. Given a relation relation (as a numpy.array, see example below) and number of node...
A: PROGRAM EXPLANATION Import the NumPy. Create the program as given in the question. Inside the adjac...
Q: 2. Create a program that implements all different kinds inhenitance. Use any object to represent you...
A: Introdution:There are 6 types of inheritance in total. Single inheritance Multi-level inheritanc...
Q: What is the distinction between an EISP and an ISSP?
A: The Answer is
Q: Explain the general concept of sensor clouds and the protocol architecture in the context of a block...
A: Introduction: A sensor is a device that recognizes and quantifies beneficial properties and data.Sen...
Q: hen we use the new operator to produce a String, where does it go? a. Stack b. String storage c...
A: Introduction: When we use the new operator to generate a String, the Java compiler will construct a ...
Q: The value of p after this command: A = [1:4; 5:8; 9:12]; p = size(A); O will be 12 will be a 3-by-4 ...
A: Below is the answer to above query. I hope this will be helpful for you...
Q: What are the most significant blockchain principles?
A: Introduction Blockchain technology is the change required in today's modern world. The data plays an...
Q: Use 8086 assembly language by using the EMU8086 - assembler and microprocessor emulator solve the pr...
A: Leap Year or Not: org 100h include 'emu8086.inc' mov cx, 04h inp: mov ah, 01hint 21h sub al, 30hmov ...
Q: 4. 1011012 = 10= _ 5. What is the gray code of 101011110010102? 16 6. Solve: ABF5H - 9CDFH
A: Ans:) This problem requires conversions from one base of another. The complete solution is given bel...
Q: Determine the components of the vectors [u1, u2] and [V1, V2] so that a[u1, U2] + [V1, v2] generates...
A: Here, I have to provide a solution to the above question.
Q: 56 ___ 31 == 39 Which operator would make this expression true?
A: Here in this question we have asked that 56 ___ 31 == 39 Which operator would make this expression t...
Q: Write a python program with three or more functions that uses three or more paramters, variables and...
A: Here is the detailed explanation of the program
Q: What is the procedure for locating a certain unit of data in a memory?
A: Introduction: Each bit of binary data is like stored on a semiconductor memory chip in a small circu...
Q: Is there a start codon other than AUG? What is it called, and what does it represent?
A: INTRO A reading frame includes a start codon and a stop codon.
Q: The variable t after these commands t = (16:-4:1) '.^ 2 will be O a 4-element vector a 4x4 matrix O ...
A: Answer:
Q: Describe how HDFS and MapReduce compliment one other.
A: Hadoop Distributed File System (HDFS): Hadoop Distributed File System (HDFS) is the primary data s...
Q: What Is A Symbol Table?
A: here is the solution. Symbol Table is an important data structure that is used in a Compiler.
Q: Data Structures and Algorithms is a course that teaches students about data structures and algorithm...
A: Introduction Stack is a dat structure which follows LIFO (Last In First Out) principle where the el...
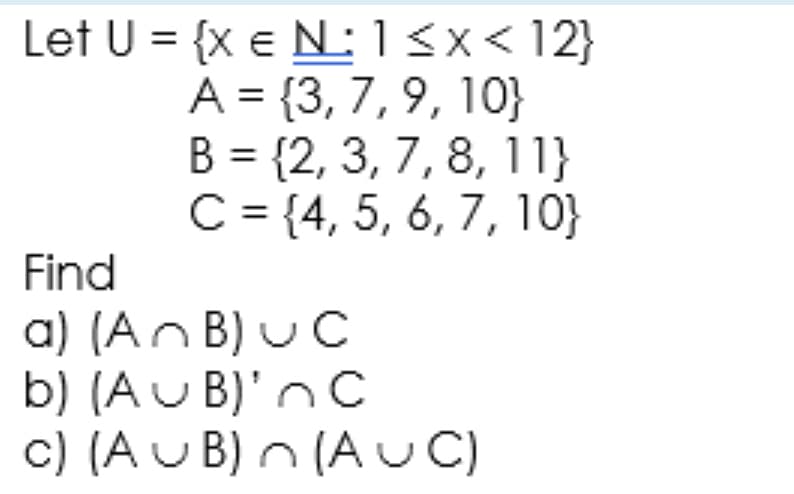
Step by step
Solved in 2 steps with 2 images

- The set of all non-negative integers x less than 16 such that x2 is an even integer can be described as the set: (Note: The required set must include as elements all non-negative integers x such that all the requirements for the set are met.) a. {x| x ∈ Z≥, x < 16, x2 = 2k for some k ∈ Z} b. {x| x ∈ Z≥, x < 16, x2 = 2k for some k ∈ Z+} c. {0, 2, 4, 16, 36, 64, 100, 144, 196} d. {0, 2, 4}Q. Given a 2d grid map of '1's (land) and '0's (water),count the number of islands.An island is surrounded by water and is formed byconnecting adjacent lands horizontally or vertically.You may assume all four edges of the grid are all surrounded by water. Example 1: 11110110101100000000Answer: 1 Example 2: 11000110000010000011Answer: 3""" def num_islands(grid): count = 0 for i in range(len(grid)): for j, col in enumerate(grid[i]): if col == 1: dfs(grid, i, j) count += 1 Please code it. .BEFPULSEMIN 70 75 80 82 65 75 74 73 65 67 80 72 69 81 82 83 68 73 74 76 81 64 85 65 66 62 81 82 74 71 72 76 79 80 84 85 73 68 68 67 68 75 77 72 76 78 82 67 80 76 74 77 73 74 72 76 74 81 75 70 TATISTICSSTUDENTSSURVEYFORR contains the column BEFPULSEMIN (a numerical variable that measures student pulses before completing an online survey). For education purposes, consider this dataset to be a sample of size 60 taken from a much wider population for statistics students. Use R to find a 99% confidence interval for the mean of the population. Choose the most correct (closest) statement below. a. Your confidence interval is (72.38912, 76.41088) beats per minute and it is narrower than a 90% confidence interval created from this data. b. Your confidence interval is (72.88831, 75.91169) beats per minute and is narrower than a 90% confidence interval. c. Your…
- True or false set{(x,x2):x∈Z}canbeseeasafunctionZ→Q. set{(x2,x):x∈Z}canbeseeasafunctionZ→Q.TODO 3: Invoke the gaussian() function, which accepts x_values, mu, and sig. Save the results in the variable y_values. # TODO 3 y_values = display(y_values) todo_check([ (y_values.shape == (120,),'y_values does not have the correct shape of (120,)'), (np.all(np.isclose(y_values,…PYTHON DATASET given x = np.array([i*np.pi/180 for i in range(60,300,4)]) np.random.seed(10) #Setting seed for reproducibility y = 4*x + 7 + np.random.normal(0,3,len(x)) Write a function inspired by sklearn’s polynomial preprocessing: (https://scikit-learn.org/stable/modules/generated/sklearn.preprocessing.PolynomialFeatures.html) your function should have: degree and include bias parameters only. For this assignment, assume that input is a 1-dimensional numpy array. For example, if an input sample is np.array([a, b]), the degree-2 polynomial features with "include_bias=True" are [1, a, b, a2, b2].
- GIVE authentic Answer: WEB TECHNOLOGIES Consider the Marks against each students in different subjects Student Names Database Tot Marks : 60 PF Tot Marks : 80 Marketing Tot Marks : 60 Irfan 56 45 59 Salma 67 56 52 Inayat 54 40 48 Basharat 56 53 51 Store these details in the Multidimensional Associative Array. Display the output as shown here S# Student Name Obt: Marks %age= (Obt:Marks / 200) * 100.0 Grade 1 Iranf 160 80 B 2 Salma 175 87 A 3 Inayat 142 71 C 4 Basharat 160 80 B A >80% B (71-80%) C (61-70%) D(51-60%) F<50% Grade Summary Total A Grade = 1 Total B Grade = 2 Total C Grade = 1 Total D Grade = 0 Total F Grade = 0 Add complete set of Screen Shots against all the steps…Q1. Srikanth is a school student. He studies in class 8th. One day his Math’s teacher came to the class and told them that he is going to start a new chapter “Measurement”. In order to give them a demo of that chapter, he told the students to find the volume of the class room using Volume( ). Input Constraint 15<=Length<=25 10<=Breadth<=20 20<=Height<=30 its the question to be solved in Dev C++A basic wooden railway set contains the pieces shown in figure below. It identifies the quantityof each type of piece denoted by ‘x’. Each piece is not uniquely identified by a primary keyvalue only labeled by type. i.e., Input information only states quantity of types such as twelvestraight pieces, two branch pieces, two merge pieces, and sixteen curve pieces. Pieces connect the knob to opening, with subtend curves extending the arc from start to end by45 degrees, and the pieces can be flipped over for track direction. The task is to connect these pieces into a railway that has no overlapping tracks and no looseends where a train could run off onto the floor. Question: Suppose that the pieces fit together exactly with no slack. Give a precise formulation of thetask as a search problem. Write a Java algorithm to assemble optimally solving the problem.
- (Use Dev C++) The combination of n objects k at a time can be defined as shown below. The equation tells us how many combination of n objects can be formed k elements at a time. P(n, k) = factorial (n) / (factorial (n − k) * factorial (k))A magic square is a square array of non-negative integers where the sums of the numbers on each row,each column, and both main diagonals are the same. An N × N occult square is a magic square with Nrows and N columns with additional constraints:• The integers in the square are between 0 and N, inclusive.• For all 1 ≤ i ≤ N, the number i appears at most i times in the square.• There are at least two distinct positive integers in the square.For example, the following is a 5 × 5 occult square, where the sums of the numbers on each row, eachcolumn, and both main diagonals are 7:0 0 0 3 42 4 0 0 10 0 3 4 05 0 0 0 20 3 4 0 0For a given prime number P, you are asked to construct a P × P occult square, or determine whether nosuch occult square exists.InputInput contains a prime number: P (2 ≤ P ≤ 1000) representing the number of rows and columns in theoccult square.OutputIf there is no P × P occult square, simply output -1 in a line. Otherwise, output P lines, each contains Pintegers…Using Java & Apache NetBeans Provide screenshots of the OUTPUT! Create a two-dimensional array of type double to contain the three different SD Marks (JD521, PRG521, and IP521) for six different students. A single array of type String must be used to store the student names (Maxwell, Carl, Gerhard, Paul, James, and Cena). Allow a user to enter in a number, ranging from 1 to 6, which will represent the student position in the table MCSD max and present the marks for each respecting module. The program can only stop when the user enter a number greater than 6. Printout the student name including the JD521, PRG521, and IP521 max, the total of marks and the average of all marks. Use a condition statement to decide that the student has passed or not (Pass rate is 70).

