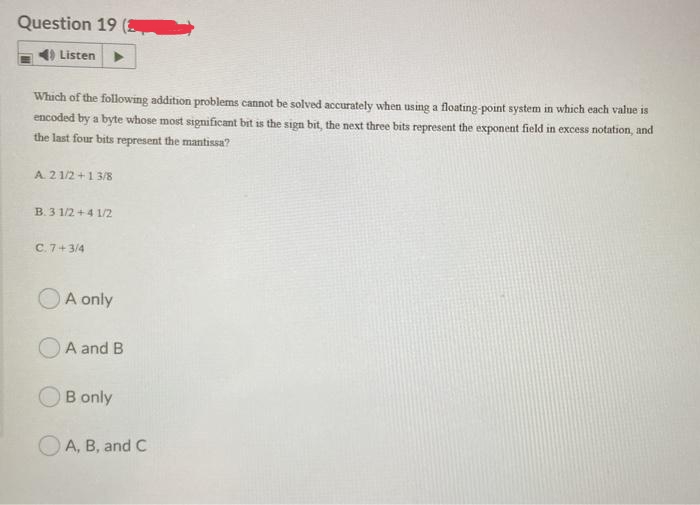
Listen Which of the following addition problems cannot be solved accurately when using a floating-point system in which each value is encoded by a byte whose most significant bit is the sign bit, the next three bits represent the exponent field in excess notation, and the last four bits represent the mantissa? A. 21/2+1 3/8 B. 3 1/2+4 1/2 C. 7+3/4 A only A and B B only A, B, and C
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: Advance Routing:- Advance routing is a type of Netcloud service platform. And this is available for…
Q: It is important to both describe and explain the major responsibilities associated with system…
A: Management of Information System(MIS): MIS is an acronym for Management of Information System. It…
Q: Which of the following addition problems cannot be solved accurately when using a floating-point…
A: Here mantissa is 4 exponential= 3
Q: 1. What is the output of this command 30:2:40
A: Here we are required to give the output of the command 30:2:40 The given command follows the…
Q: In your own words, explain the differences between EPROM, EEPROM, and Flash Memory.
A: Erasable Programmable Read-Only Memory is what is meant by the acronym EPROM. Electrically Erasable…
Q: Why is it a good idea to hash a password stored in a file before encrypting it?
A: Introduction: It is a good idea to hash the password contained in a file before encrypting the…
Q: A link editor's function is not entirely clear. Compared to a dynamic link library, how is it…
A: Editing links: It is a software used to connect the library and object codes. After the compilation…
Q: Maintain an accurate record of the most important steps taken throughout the installation and…
A: System evaluation tests: During system testing (also known as system-level tests or…
Q: It is well known that Linux and UNIX are command-line systems. Describe in detail how the command…
A: Introduction: Linux and UNIX are command-line system: A proprietary operating system is Unix. Unix…
Q: 2. The Lucas series is series based on adding two previous terms defined as ifn=0 ifn=1 L-1+L-2 ifn…
A: CODE TO COPY: #function definition def L(n): #if n is 0 return 2 if n==0: return 2 #if n is 1…
Q: "knowledge-based" agent is what? Give a thorough example to help.
A: The question is on the definition go "knowledge-based" agent and giving example.
Q: In System Design, you should be able to recognize four different models of design.
A: In system design, four design models are used: Architectural design: To characterize the system's…
Q: Define the different approach on how to attach
A: Q1)Define the different approach on how to attach events on Button view. Answer: There are following…
Q: benefits of using both Accessor and Mutator in Ja
A: SUMMARYIn Java accessories are used to determine the value of a private field and mutators are used…
Q: In conclusion, provide five examples of how fuzzy logic is employed in engineering (especially in…
A: In boolean logic, calculations have two possible outcomes: a 1 or a 0. However, fuzzy logic is used…
Q: Which among the following best describes encapsulation?
A: Encapsulation is an object oriented principle (OOP) concept which binds the data and methods into…
Q: What are some of the best techniques for managing firewalls? Explain.
A: Firewalls acts as a barrier for preventing the entry of traffic that might be intended to do some…
Q: Discuss the three Enterprise Architecture components at the data and information level. Justify the…
A: INTRODUCTION: Enterprise architecture (EA) is the process by which businesses plan to adopt and use…
Q: Plot a scatter graph showing “Seconds per insert” (Y-axis) vs. “Array length” (X-axis) using the…
A:
Q: When you put objects in Amazon S3, what is the indication that an object was successfully stored?
A: Answer: We need to write some point regarding Amazon S3
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: Wireless Networking ZRP is a hybrid routing system that employs both proactive and reactive routing…
Q: Explain what is meant by the zone routing protocol for advanced routing ?
A: Answer:
Q: The trade-offs between audio quality and file size for the MP3 digital audio data format are…
A: Sound Quality: The audio formats affect the audio quality of an audio stream. The quality and loss…
Q: I want Matlab programming definition
A: MATLAB MATLAB stands for the matrix laboratory that is developed by math work. It is the high level…
Q: How can you justify the usage of a request for proposal to gather information on hardware and system…
A: Given: The answer to the question is that a request for proposals is a business document that…
Q: Implement an algorithmic solution, indicating which states are valid and which are not, and model…
A: Let us break down the given situation to clearly understand wat is actually happening here so that…
Q: When you put objects in Amazon S3, what is the indication that an object was successfully stored?
A: The above question is solved in step 2 :-
Q: What exactly is a wifi evildirect attack, and how does it work? Please refrain from utilising…
A: Introduction: An EvilDirect may be created by setting a rogue GO running on the same channel as a…
Q: 1 1 1 12. Write a function harmonic (n) to return the sum 1+ + +...+ (These 2 3 n sums are known as…
A: Code: def harmonic(n): #function definition #declare sum variable s=0 #for range upto n+1 for i in…
Q: (Java) Identify the true statements, select all that apply: -Setters and getters are not…
A: 1. Setters and getters are not required for public instance variables. Expalnation: It is possible…
Q: A look at Windows Service Control Manager and its advantages will be discussed in this article.
A: Introduction: SCM is a Windows NT function that launches, stops, and interacts with Windows service…
Q: Make the programming easy Make the programming complex O Provide better features O Provide more…
A: Implementation complexity, efficiency, robustness, scalability, quality of service and experience…
Q: There is a distinct difference between methodologies and the software development life cycle,…
A: Given: The term "Software Development Lifecycle" (SDL) refers to a method that ensures the efficient…
Q: 2 [Classification-decision tree] 2- Consider two possible splits of training records during the…
A: Consider the Classifier in A:
Q: Organize the components of SCI according to their importance in the Software development. Justify…
A: It is defined as a set of activities dedicated to creating, designing, programming, documenting,…
Q: Organize the components of SCI according to their importance in the Software development. Justify…
A: Brief answer in second step:
Q: The function below implements Quicksort. void Quicksort(int first, int last) { int i = first+1, j =…
A: The correct option is C that is the worst-case time complexity of the given quick sort algorithm is…
Q: The Cupid matchmaking Service maintains two files - one for the male clients and another for female…
A: CODE - #include<iostream> #include<fstream> using namespace std; int main(){ ifstream…
Q: Pair programming is an agile software development technique in which two programmers work together…
A: Software engineering is refers to the branch of the computer science which deals with the designs,…
Q: 1. What is Accessor? a. Explain using a proper programming example and its output.
A: Assuming you mean an accessor method in Java: An accessor method is a method that a programmer…
Q: PS: Please upload the output and say the logic behind it. Thank you! 2. Create a class with a…
A: A year is considered a leap year if:i. It has an extra day i.e. 366 instead of 365.ii. It occurs…
Q: What methods are there for improving information privacy?
A: EXPLANATION: The technologies for enhancing information privacy utilize the various kinds of…
Q: 7. If Q(z) = 3z³ + 4z² - 7z+8, find Q(-5). If f(x) = x³ + 6x + 9, find f(x - 2). 8.
A: Answer: we need to describe the function and find out the result
Q: Why is testing insufficient to ensure correctness?
A: Introduction: Testing is the process of analysing a programme to see whether it is capable of…
Q: The "Inference rules" are what? With specific examples, define "ahead chaining" and "reverse…
A: Filters.(Proof theory, logic)A rule for truth-pressingly combining (modifying) well-formed formulas…
Q: In your own words, explain the differences between EPROM, EEPROM, and Flash Memory.
A: Three words for the digital system's memory are provided. Terms provided: Flash Memory, EEPROM, and…
Q: (Java) Write a program as follows: prompt the user to enter a positive value of type byte. cast…
A: Java programming code: import java.util.*; public class Main { public static void main(String[]…
Q: Q) BEZIER CURVE PRODUCED BY BERSTEIN BASES FUNCTION HAS LIMITED FLEXIBILITY. JUSTIFY THE STATEMENT.
A: Bezier Curve: French engineer Pierre Bezier makes the discovery of the bezier curve. These curves…
Q: The importance of the UNIX kernel cannot be overstated. Explain why this is the case and how it…
A: The Kernel is the fundamental core at the heart of any computer operating system (OS). The core…
Q: In AWS, which security aspects are the customer's responsibility?
A: Question is asking for security aspects in AWS.
1
Step by step
Solved in 2 steps

- Please answer both part a and b of this question. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent, and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this system if the storage is normalized? (Assume that no bits are implied, there is no biasing, exponents use two’s complement notation, and exponents of all 0s and all 1s are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative Why would you choose this bias?We are provided an FP prototype labeled: IEEE 754-2015 of 15 bits similar to IEEE 754, where the exponent has size 6 bits and fraction has size 8 bits, and 1 MSB for the sign. No guard or round bits are assumed. What is the bias of the system? Find the smallest and largest number that can be represented. Find the new representation of the decimal number you worked with earlier (e.g., the 0.012).2. (a) What is a single error and burst error? Explain with an example. (b) Find the Hamming code of the following bitstream using even parity. 11011111010111010101110111000010
- Suppose we are working with an error-correcting code that will allow all single-bit errors to be corrected for memory words of length 12. a) How long should the check bits and why? b) Code words are created according to the Hamming Algorithm presented in the text. We now receive the following code word: 0 1 1 0 0 1 0 1 0 0 1 1 0 1 0 0 1 Assuming even parity, is this a legal code word? If not, according to our error-correcting code, where is the error? PLEASE SHOW ALL WORKING UNDERSTANDABLE THANK YOUSuppose we are working with an error-correcting code that will allow all single-bit errors to be corrected for memory words of length 12. a) How long should the check bits and why? b) Code words are created according to the Hamming Algorithm presented in the text. We now receive the following code word: 0 1 1 0 0 1 0 1 0 0 1 1 0 1 0 0 1 Assuming even parity, is this a legal code word? If not, according to our error-correcting code, where is the error?Please solve only 4 part rest are already answered This problem covers floating-point IEEE 754 format. 1)List four floating-point operations that cause NaN to be created? 2) In the 32-bit (single precision) IEEE 754 format, what is the encoding for negative zero? 3) In the 32-bit (single precision) IEEE 754 format, what is the encoding for positive infinity? 4) Assuming 32-bit (single precision) IEEE 754 format, what decimal number is represent by this word: 1 01111101 00100000000000000000000
- a) Determine the 32-bit binary representation for floating point numbers in the form± I.F x be where I is the interger part,F is the fraction,b is the base, ande is the exponent.Using this format, represent the number -1.00011011101 x 225 as a 32 bit floating point number. b) During the process of digital sampling, data can be lost due to aliasing. Analyse this problem and provide at least two possible solutions. Also, determine the rate at which a signal should be sampled, if the highest frequency is 60MHz. c) In your own words, discuss the relationship between the hexadicimal number system and the binary number system. Use this relationship to convert the following hexadecimal values to binary.i) 5BC916 ii) 6EF816 iii) 8A4D16 iv) 9ED5164, in the fixed-point machine, the following statement is wrong ( ).A. In addition to the complement, the original code and the inverted code cannot indicate that the original code of −1 B. +0 is not equal to −0C. the inverse of +0 is not equal to the negative of −0 D. For the same machine word length, the complement code can represent a negative number more than the original code and the inverted code.Show Steps Please 18. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this?system if the storage is normalized? (Assume no bits are implied, there is no biasing, exponents use two's complement notation, and exponents of all zeros and all ones are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative? c) Why would you choose this bias?
- Question 23 options: Using the rules of the simple floating point model (1-bit sign, 5-bit biased exponent, 8-bit significand, and normalized such that the leftmost bit of the significand is always 1), the number 8.4375 (decimal) can be expressed as: (Do not use spaces or any English text. Provide only 14 bits.)Kindly answer the following questions. j. The one thing that causes the most trouble with 2's complement numbers is the special case of the negative number which consists of a 1 followed by all 0's (1000 ... 000). If this number is n bits long, what number does it represent and why? (It is not negative zero.) a. Represent 187 in BCD code, excess-3 code, 6-3-1-1 code, and 2-out-of-5 code.Suppose we are working with an error-correcting code that will allow all single-bit errors to be corrected for memory words of length 7. We have already calculated that we need 4 check bits, and the length of all code words will be 11. Code words are created according to the Hamming algorithm presented in the text. We now receive the following code word: 1 0 1 0 1 0 1 0 1 1 0 Assuming odd parity, is this a legal code word? If not, according to our error-correcting code, where is the error?

