Logical address converted into linear address using then into physical address on memory using. A is a logically self-contained unit of code that receives a list of parameters and performs computation, and returns results The combines your program's object file created by the assembler with libraries to produces an executable program
Logical address converted into linear address using then into physical address on memory using. A is a logically self-contained unit of code that receives a list of parameters and performs computation, and returns results The combines your program's object file created by the assembler with libraries to produces an executable program
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Topic Video
Question
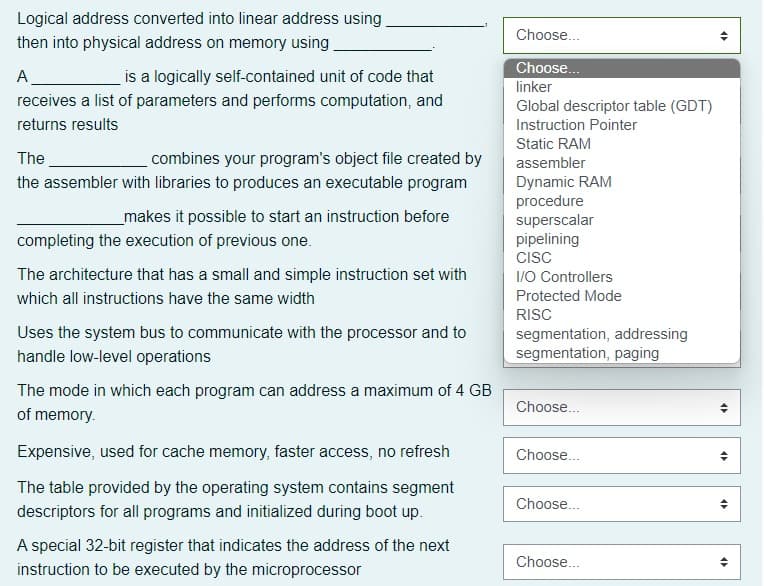
Transcribed Image Text:Logical address converted into linear address using
then into physical address on memory using.
A
is a logically self-contained unit of code that
receives a list of parameters and performs computation, and
returns results
The
combines your program's object file created by
the assembler with libraries to produces an executable program
makes it possible to start an instruction before
completing the execution of previous one.
The architecture that has a small and simple instruction set with
which all instructions have the same width
Uses the system bus to communicate with the processor and to
handle low-level operations
The mode in which each program can address a maximum of 4 GB
of memory.
Expensive, used for cache memory, faster access, no refresh
The table provided by the operating system contains segment
descriptors for all programs and initialized during boot up.
A special 32-bit register that indicates the address of the next
instruction to be executed by the microprocessor
Choose...
Choose...
linker
Global descriptor table (GDT)
Instruction Pointer
Static RAM
assembler
Dynamic RAM
procedure
superscalar
pipelining
CISC
I/O Controllers
Protected Mode
RISC
segmentation, addressing
segmentation, paging
Choose...
Choose...
Choose...
Choose...
4
•
45
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education