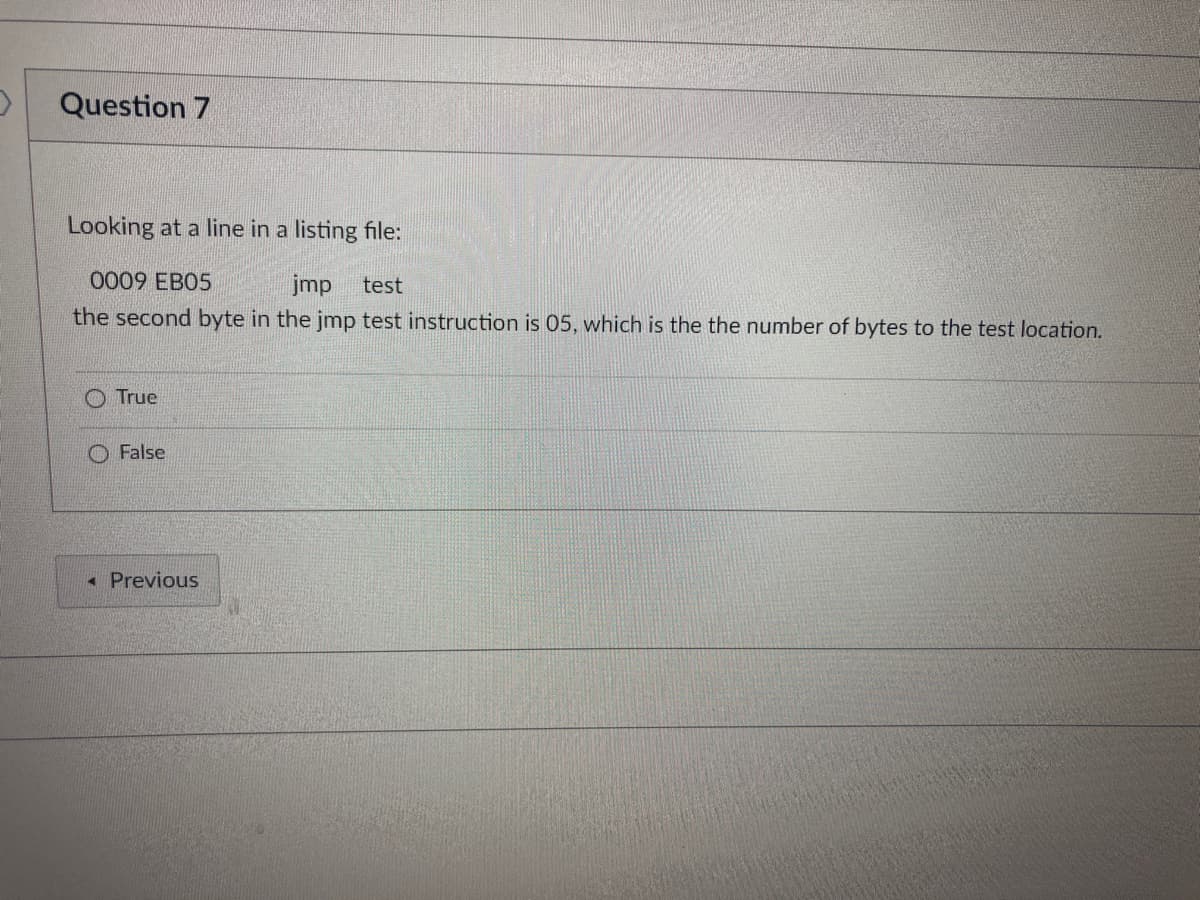
Looking at a line in a listing file: 0009 EB05 jmp test the second byte in the jmp test instruction is 05, which is the the number of bytes to the test location. True False
Q: What function does the internet play in the lives of individuals with disabilities, in your opinion?
A: They have the following alternatives on the web: Visually impaired or blind individuals may benefit…
Q: Q.2.5 Q.2.6 Identify four use cases that have the Consumer/Public as an actor and create a matching…
A: Answer 2.5 Behavioral relationship active relationships that are commonly utilized in the use case…
Q: Make an algorithm and flowchart of the following problem set. 5. Draw a flowchart that computes the…
A: For finding the factorial of a number, we have to multiply the number with the previous numbers up…
Q: describe how a company uses data as a predictive layer in decision-making
A: Data-driven decision-making (sometimes abbreviated as DDDM) is the process of using data to inform…
Q: Explain how things have changed throughout time. Interaction between human computer science and…
A: Human-Computer Interaction (HCI) is both a review and a practical effort. It involves comprehending…
Q: Could you solve it in python? Modify the code and show (in data table) and plot the of output…
A: import numpy as npimport matplotlib.pyplot as pltimport pandas as pd # output probability vs.…
Q: 30.2 LAB: Reverse a string Write a recursive function called reverse_string() that takes in a string…
A: The solution to the given problem is below.
Q: What are some of the numerous aspects of the process of designing software systems that need to be…
A: Process Of Creating Software: The Software Design Process (SDP) is a high-level,…
Q: X3 X2 X4 X1 X9 X10 X8 X5 X6 X7 X14 X15 X11 X16 X Assuming the graph given above is a valid Binary…
A: Here we are implementing this using python
Q: Please help me in creating any of the games or applications below using java. Both the list of the…
A: // A simple program to demonstrate // Tic-Tac-Toe Game. import java.util.*; public class GFG {…
Q: CloudFront geo restriction entail?
A: Introduction: Cloud front is a fully managed, fast content delivery network (CDN) service that…
Q: How do the advantages of cloud computing stack up when compared to one another? Cloud computing…
A: Given: Almost twenty years have passed since cloud computing was first made accessible. In spite of…
Q: 1)Provision a NoSQL database.
A: Note: As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: Create a two-dimensional array of type double to contain the three different SD Marks (JD521,…
A: import java.util.*;class Example { public static void main(String[] args) { Scanner sc=new…
Q: Rabenstein code was used to send a message with 4 information bits, you receiv
A: The answer is
Q: Explain In detail 1) User requirement in Webapp 1) System Requirement in Webapp
A: A web application (webapp) is an software program that is stored on a remote server and added over…
Q: mming: chess - pawn movement Input: s1, s2, x1, y1, pawn s1,s2 - horizontal size and vertical size…
A: It is defined as a powerful general-purpose programming language. It is used in web development,…
Q: What role do you think the internet has in the lives of individuals with disabilities? • What…
A: Start: People with disabilities benefit from the internet. They have the following alternatives on…
Q: A GSM system uses 124 channels and each channel is divided into 6 time slots. What is the maximum
A: The answer is
Q: Describe in detail the computing models of SaaS, PaaS, and IaaS Clouds. The following are three…
A: Consider the following three cloud computing models: IaaS, PaaS, and SaaS are three types of cloud…
Q: Question 11 Which lines contain a variable intialization in the following code? 1. public class…
A: INTRODUCTION: In Java, a variable is a data container that stores data values during the execution…
Q: Determine the sequence of execution of processing by computing for the need of each process, refer…
A: The Banker's algorithm is a method of deadlock avoidance when there are multiple instances of each…
Q: II. Solve the following problems applying the concept of Eulerian and Hamiltonian Graphs. Discuss…
A: The question is related to graph theory and finding route which will traverse all of the streets or…
Q: "Divide and conquer" is one of the most fundamental ideas that guides the practice of software…
A: Introduction: When people think of software engineering, they think of compound instructions,…
Q: Which problems were hoped to be remedied by the preliminary investigation conducted through the…
A: A preliminary investigation is a kind of investigation where police first respond to a report when…
Q: QUESTION: Given a list of students' CPA as shown in Table 1, write a C program to Read and Print the…
A: Code: #include<stdio.h>int main() { int n=5; float…
Q: Q21. Make two separate plots of the function f(x) = 0.6x² - 5cos(x) + sin(x²) + 3; the first plot…
A:
Q: Q1: Distinguish between Short jump and Long Jump of 8051 Micro Controller.
A: Many microcontrollers have this option. One is an instruction that is short and fast. That is a…
Q: What type is the most appropriate to use to represent the amount of money you have? double int…
A: We need to find the correct option.
Q: Regular Expression and DFA over set of strings {a,b} in which there is atleast one b is the length…
A: Here is the regular expression a the dfa for the given statement:
Q: Which of the following statements is NOT true, concerning the practice of cyber risk management?…
A: a) Risk appetite allows the organization to determine how much they are willing to take risks. Risk…
Q: Propose suitable information security mechanisms or techniques or methods based on the concept of…
A: This part talks about security arrangements with regards to prerequisites for data security and the…
Q: There are several disadvantages of cloud computing that are seldom highlighted.
A: Introduction: The phrase "cloud computing" refers to the process of storing and accessing data via…
Q: When setting up accounts for regular users, Windows administrators, and Linux root users on various…
A: Concerns to be Adhered to Manage Linux/Unix Accounts Proactively Implement Least Privilege.…
Q: How to make heart shape pattern with name in the middle
A: Explanation: // let's first including all the required libraries as #include <stdio.h>…
Q: What are the four most important characteristics that may be categorized as part of the software…
A: Answer: The study separates the 53 qualities into four categories, with the most fascinating in each…
Q: Explain what application virtualization is a
A: Q)Explain what application virtualization is? Answer: Application virtualization is technology that…
Q: G(V, E) is directed graph where every edge has weight as either 1, 2 or 5. What algorithm could be…
A: Option B is correct Breadth First Search is used to find the shortest path from source to…
Q: In linked list implementation of a queue, from where is the item deleted? *
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What other types of AI are there? Give instances of how artificial intelligence domains might be…
A: Introduction: The processes involved in human intelligence may be emulated by computers using the…
Q: Determine whether the following propositions is true or false. if 1+1=3, then 2+2=4
A: Dear Student, In if and then statements , it is true when the if statement and then statement is…
Q: Q1) Draw control flow graph for the following Java code. public class RangeExtraction { public…
A: Java compiler executes the code from top to bottom in a given order . Java provides a…
Q: Distinguish between the notions of user interface, UX, and UI design.
A: -The user interface: The user interface (UI) is the interface between a computer, a website, or an…
Q: In the context of technical writing, what do you see as the most important role that screencasting…
A: A major benefit of screencasting is that the viewer can watch the screencast at a time when it's…
Q: You are working on the Linux system and run the following commands: $ mkdir .new_stuff $ ls…
A: We need to answer questions related to Linux system.
Q: 1. In order to discourage excess electric consumption, an electrical company charges its customers a…
A: flowchart for problem 1 calculate electric bill
Q: How many different ways can you think of that you utilize computers and other information systems in…
A: Information systems in day-to-day life: Globally, the use of computers and information systems is…
Q: i=i+1 Start Declare name,scores each with 100 elements Initilize i=0,sum=0,n=100 i<=100 True 101…
A: Your algorithm of above flowchart is given below.
Q: inputs and outputs that should be considered throughout the software system design process?
A: Introduction: Input design : Input is the raw data that is processed to produce output. During the…
Q: In your perspective, what function does the internet serve to serve in the lives of persons who have…
A: They have the following alternatives on the internet: Visually impaired or blind people may benefit…
Step by step
Solved in 2 steps

- $readmemb is used to initialize memory from a text file in hexadecimal values. True False It is a keyword used in the HDL code to import the hexadecimal contents of a text file into a memory variable. "When iCE is disabled in the memory module, the output in the tWbus is zero." True False When iCE is enabled in the memory module, the output in the tWbus is the memory address." True False eg [6:0] Memory [0:16] means the memory contains ___ bits per address 17 7 6 16 When iCE is disabled in the memory module, the output in the tWbus is high impedance" True False NEED ANSWERS QUICK NO EXPLANATION NEEDEDSomeone has modified the utils.asm file to insert a PrintTab subprogram immediatelyafter the PrintNewLine subprogram as shown below (changes are highlighted in yellow).The programmer complains that the PrintTab command cannot be called using the "jalPrintTab" instruction. What is wrong, and how can this be fixed? Explain all theproblems in the code this programmer has written.# subprogram: PrintNewLine# author: Charles Kann# purpose: to output a new line to the user console# input: None# output: None# side effects: A new line character is printed to the# user's console.textPrintNewLine: li $v0, 4 la $a0, __PNL_newline syscall jr $raSomeone has modified the utils.asm file to insert a PrintTab subprogram immediatelyafter the PrintNewLine subprogram as shown below (changes are highlighted in yellow).The programmer complains that the PrintTab command cannot be called using the "jalPrintTab" instruction. What is wrong, and how can this be fixed? Explain all theproblems in the code this programmer has written.# subprogram: PrintNewLine# author: Charles Kann# purpose: to output a new line to the user console# input: None# output: None# side effects: A new line character is printed to the# user's console.textPrintNewLine: li $v0, 4 la $a0, __PNL_newline syscall jr $ra .data __PNL_newline: .asciiz "\n"PrintTab: li $v0, 4 la $a0, tab syscall jr $ra.data tab: .asciiz "\t"
- A fragment of code is given to compare text in the field alpha with a text in the field beta: .data alpha db 12 dup(?) beta db ’abrakadabra’, 0 ; ::: .code ; ::: mov esi, 0 mov ecx, 12 ns: mov dl, alpha[esi] cmp dl, beta[esi] jne wrong ;=====MISSING==== loop ns ; ::: wrong: Choose missing instruction to insert in the code line marked by the comment “MISSING”.need a new java .asm file and fill it with all of the required directives. Next, write a program that does the following: Create two variables with any names and initial values. One must be type "DWORD" and the other must be type "SBYTE". Set the value of the EAX and EBX registers to any numbers of your choice. Add EAX to your DWORD variable. The result should remain in the variable (not the register). Add EBX to your DWORD variable. The result should remain in the variable. Set the value of the CL register to any number of your choice (since it is only byte sized the upper limit for the number is 255) Subtract the CL register from your SBYTE variable three times. The result should remain in the variable. You can debug your program to verify that the arithmetic is performed correctly.Write an algorithm of a program to read from a file. The user should be able to get the option to input the file name. He is supposed to read first 100 bytes from the file. After the reading is done, the file should be closed. If the file is not available, the program should be closed immediately. You should mention "System call" beside each instruction which are supposed to use a system call function.
- =>which of the following represent valid use cases of the ANSI C register storage class specifier? A)A for loop in which the loop index is declared in the initialization. B)A short int inside a block which will be passed by pointer to another function. C)An unsigned short defined inside a function combined with other quantities as a bitmask. D)A parameter list of an external function declared in a header file. E)A char array declare at file scope to be used by all functions defined in the file. =>Memory has been dynamically allocated in the C++ statement below: char* str = new char[20]; Which of the following statements can be used to free the memory? A)delete[] str; B)delete str[]; C)delete char* str; D)delete *str; E)delete str[20];Write an ARM assembly program to convert temperatures from Celsius to Fahrenheit or from Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable to read and store values, you can initialize any integer value into the variables (Do not expect decimal results we are only doing integer operations). C = 5 × (F − 32) / 9 F = (9 × C / 5) + 32 Name the file TempConvert.s add the below commenting statements in the program ;Name: ;Date: ;Give which expression you use Please use LDR/STRuse MIPS instruction only please test the file with any text file yoi have. wirte comments and make it simple please Thanks
- Question 3: Replicate any 4 functions of your choice from the Irvine32 library using the interrupt 21h for the MS-DOS environment. Provide a single .asm file encapsulating the 4 functions you have replicated and a program utilizing themWrite an ARM assembly program to convert temperatures from Celsius to Fahrenheit or from Fahrenheit to Celsius. Here are the two formulas for your reference. Use variable to read and store values, you can initialize any integer value into the variables (Do not expect decimal results we are only doing integer operations). C = 5 × (F − 32) / 9 F = (9 × C / 5) + 32 Name the file TempConvert.s add the below commenting statements in the program ;Name: ;Date: ;Give which expression you usegiven a file(use any text file) write MIPS instruction(assembly language) to count all words in that file. note: A single letter is counted as a word for example assume this sentence written in txet file : "bartleby is a website" please do your best i need this the output should be: word count = 4



