lve please:
Q: DISCUSS REQUIREMENTS ELICITATION ANALYSIS.
A: Introduction: requirements elicitation : Based on information from important stakeholders, business…
Q: Explain the procedure creating the seven segment display on to the multi sim software to create a…
A:
Q: Q1) Which of the following options will return the last letter of the string "Carleton"? Try to…
A: Option(A) my_string = "Carleton"last = len(my_string) - 1print(last) Length of string is 8, since…
Q: run the SQL queries to return only the requested data. You must write only one SQL statement per…
A: NOTE: The database schema was not provided. So, a sample database is created. The SQL program for…
Q: Extract the addresses from this string: const str = "123 Redding Dr. 1560 Knoxville Ave. 3 // ["123…
A: Algorithm - Take input from user. Use the below logic --> const REGEXP =…
Q: I need to write a SELECT query in SQL using these instructions. Attached is the code that created…
A: Please refer to the following step for the complete solution to the problem above.
Q: Write types of Data flow diagram (DFD)
A: Introduction: A data flow diagram is a visual representation of data flow in a system (DFD). DFD can…
Q: Draw DFD Level 0 and 1 for Virtual Learning using Blackboard.
A: Solution: Given, 0 - Level Data Flow Diagram for Virtual learning-
Q: Write a function called makemat that will receive two row vectors as input arguments, and from them…
A: MATLAB which refers to the programming platform which are designed specifically for engineers and…
Q: Discuss importance of DFDS in a good software design.
A:
Q: Q. No. 4: Trace the following code. int main() { int [] values = {1, 3, 5, 7, 9, 11, 13, 15, 17,…
A: Trace the following code: int main() { int [] values = {1,3,5,7,9,11,13,15,17,19};…
Q: Discuss what is CASE tool and its scope.
A: Answer is
Q: This program requires the student to create a programming loop. The program's loop with loop between…
A: #include<stdio.h> int main() { int no_of_weeks,i=1; /* variable declaration */ float…
Q: 1. Aditya is a digital forensics specialist. He is investigating the computer of an identity theft…
A: Hello student
Q: the following Monster class: package comparators; public class Monster { private String name;…
A: Please find the answer below :
Q: can this be solved using logic laws?
A: yes it may be solved by using logic law.
Q: 19. Here are some programming questions to practice: a. Determine whether or not the phrase "hi" is…
A: Answer:
Q: Strony garda roughout the decade, progress toward achieving core objectives is tracked and reported.…
A: The question has been answered in step2
Q: Create a Python function called momo that takes a string of characters and returns a new string that…
A: Python:- The Python Foundation, a non-profit organization modeled after other non-profit…
Q: What is (a --> b) and (¬b --> c) and (¬ c↔¬b) logically equivalent to? Use logic laws and label them
A: Solution: In order to solve this question, first let's understand the neede truth table.
Q: b) Implement a stored PL/SQL function that finds a supplier who supplies the cheapest (lowest supply…
A: A stored procedure is SQL code prepared so that the code can be saved for repeated use. So if you…
Q: Given a sentence, create a function which shifts the first letter of each word to the next word in…
A: In this problem we need to design the js program logic - arr = str.split(' '); return arr.length…
Q: You may use a software to do calculations but you have to write down the details. The correspondence…
A: Given that, Cipher text= NUMBER Matrix= 21097
Q: IN C++ LIST STL INSERT NUMBERS FROM 14 to 27, THEN REVERSE THE LIST USING AND PRINT THE REVSERSED…
A: I have written the code below:
Q: What is a key feature of fifth normal form? A key step in this normal form has every…
A: Database Management System (or DBMS) Essentially nothing more than a computer-based data storage…
Q: What is test case generation case tool?
A:
Q: What is system software?
A: We need to discuss system software.
Q: Question: a) list some of the uses of Microsoft Excel reqiured: please answer this question by…
A: What is excel: A piece of software developed by Microsoft that employs formulas and functions to…
Q: What value do we get for res if we execute this code? s = "this is my string" res = s.split() res =…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: Let R and K be two relations under a join operation. Assume that m = |R| and n = IKI, then the…
A: Given that, R and K are two relations under a join operation m= |R|, number of rows in R n= |K|,…
Q: In Kerberos, Alice receives a reply, how does she know it came from Bob (that it's not a replay of…
A: Solution: Given, In Kerberos, When Alice receives a reply, how does she know it came from Bob…
Q: Write a program that displays the following pattern of prime numbers using a nested for loop: 2 2…
A: //note : since programming language is not specified, we are providing answer in cpp #include…
Q: Definition, purpose, and importance of SDG7
A: By 2030, everyone must have access to "cheap, reliable, sustainable, and contemporary energy." This…
Q: What is software analysis and design?
A:
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a…
A: Please find the detailed answer in the following steps.
Q: Public Key Infrastructure (PKI)-based authentication is a technology for authenticating users and…
A: Public Key Infrastructure (PKI) : This is a technology for authenticating users and devices in the…
Q: What is Repeatable and non-Repeatable software development organisation?
A: The question has been answered in step2
Q: 1.Describe the Linear Discriminant Analysis (LDA) method. 2. Explain how it is used for feature…
A: 1.Linear Discriminant Analysis method: It is one of the common dimensionality reduction techniques…
Q: Let R and S be two relations with the following schemas R (P.Q.R1,R2,R3) and S (P.Q,S1,S₂), where…
A: Join statement is used to combine data or rows from two or more tables based on a common field…
Q: Please help me solve this with java 1-method called printArray that takes an array of double…
A: Answer: We have done code in java programming language and also we have attached code and code…
Q: Indices can speed up query processing, but it's usually a terrible idea to index every attribute,…
A: Indices can speed up query processing, but it usually a terrible idea to index every attribute and…
Q: Write a java program that ask user to input number of bits, apply formula of calculating range in…
A: Answer is given below
Q: Which data model(s) introduced the use of a data manipulation language?
A: There are three data models:- Hierarchical - stores data in hierarchy. Uses tree structure.…
Q: In this assignment you will write your own square root function and a main program to test it. The…
A: I'll share the improved pseudocode in subsequent phases.
Q: Question 4 Text typing work only t
A: Solution- The complexity of above function is O(1) because constant operation are done so the…
Q: Consider the following disk characteristics: Average seek time = 8 msec Average rotational delay = 3…
A: Disk Characteristics:- Dimensional Features of Disks:- Every disc platter is flat and spherical.…
Q: Which of the following users architects the database? Database designer Database administrator…
A: Solution for given question, Which of the following users architects the database? Introduction:…
Q: What was the fifth generation of major data models created during the mid-1990s?…
A: A database management system (or DBMS). It is essentially just a computer-based data storage system.…
Q: Suppose a python program mycode.py contains the following main guard. if __name__ == "__main__":…
A: Introduction : __main__: The is the main python program part where the excutable code is need to…
Q: Question 1 We are given a tree of height larger than h. Write an algorithm that finds a tree…
A: Height of Tree:- The greatest number of edges along the route from a leaf node to a target node…
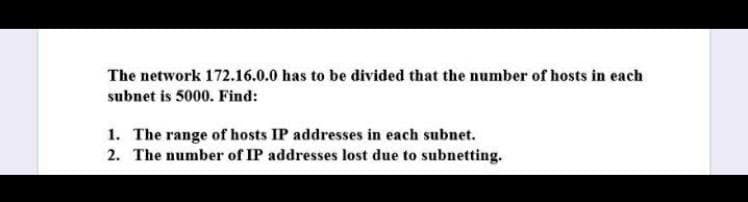
Solve please::-
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 3 images

- In a class A subnet, we know the IP address of one of the hosts and the subnet mask as given below: IP Address: 25.34.12.56 Subnet mask: 255.255.0.0 What is the first address (subnet address)? What is the last address?Q7. Suppose we have the following IP addresses for two different organizations, we have to create 5 networks having 30 hosts in it. Find first sub network ID, Fist address, Last address and Braodcast for each of the following given addresses.a. 17.23.120.8b. 252.5.15.111Suppose you have been given this classful IP address 130.1.1.8. You want to create a network of 1024 (assignable) IP addresses, what will be the length of network and host part?
- Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks? Let’s consider the above network. If you are using VLSM /CIDR, determine what subnet mask numbers allow therequired number of hosts.Suppose a user has a webserver running at a machine with the name nadir.edu.net.pk and IP address 10.10.10.10. The authoritative DNS address for this web server is with the name dns.nadir.edu.net.pk and with IP address 11.11.11.11. Write all the steps involved in retrieving the IP address of nadir.edu.net.pkQ2 Using this IP address 150.150.55.20 solve the following questions- Which Class this IP related to?- Suppose you use the following subnet mask 255.255.252.0 ,What is the number of hosts exist within a subnet?- What should you do to make each subnet have at least 200 hosts?
- Take the Class A address 10.0.0.0 and answer the following questions by typing those answers at the end of each question: What is the default subnet mask of a Class A IPv4 address? What is the first usable IP address of this “not-subnetted” network? What is the last usable IP address of this “not-subnetted” network? What is the broadcast address of this “not-subnetted” network? How many total hosts are allowed on this “not-subnetted” network? Let’s split this network into 4 subnets What is the new subnet mask? What is the first subnet address of your newly subnetted address? What is the first usable IP address of your newly subnetted address? What is the last usable IP address of your newly subnetted address? What is the broadcast address of your newly subnetted address? How many usable hosts on this subnet? Fill in the following information for the second, third, and fourth new subnets: Network (subnet) address Usable host range BroadcastSuppose a user has a webserver running at a machine with the name www.nadir.edu.net.pk and IP address 10.10.10.10. The authoritative dns address for this web server is with the name dns.nadir.edu.net.pk and with IP address 11.11.11.11. a. Write all the steps involved in inserting this webserver name in the DNS hierarchy. b. Write all the steps involved in retrieving the IP address of www.nadir.edu.net.pkWhat is the purpose of an IP address mask? Suppose an IP address is identified as 200.60.40.88/24. What is the network address in this case? What is the host address? How many hosts can this network address support? Repeat this exercise for the IP address 222.66.44.80/26.
- Assume that Computer A, which is connected through an Ethernet cable to the Switch S1, is just powered on. The user opens a browser and then types a website address to receive the website from the Server (as shown in Figure 1). Write down all the important protocols that come into play by the time the first frame containing HTTP request reaches R1. (Note: Before HTTP frame, other frames have already been sent by other protocol(s).) Write down all the protocols with reference to the TCP Model as follows? Application Layer: Transport Layer: Internet Layer: Link Layer:Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks?Find the class of the following two IP addresses (both are classful addresses),as well as their netid and hostid: a. 104.37.3.6 b. 208.34.54.12

