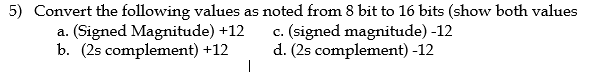
Magnitude) plement) +12 c. (signed magnitude) d. (2s complement) -12
Q: When it comes to communication, what role does information technology play in the organizations of…
A: Introduction: IT (Information Technology): Information technology, or IT for short, is the use of…
Q: Which TCP/IP tool would you use to illustrate the route that a web browser and web server…
A: To be determine: Which TCP/IP program would you use to show, on a map, the path that a communication…
Q: Explain the function of the directional and other keys. Describe the media and Internet control…
A: The above question is solved in step 2 :-
Q: In what ways are the connections between a kite and a spool of thread analogous to those that exist…
A: Relationship between object and reference variable: In Java, classes are developed and written,…
Q: Please provide an illustration of the internet of things. What are the key distinctions between the…
A: Required: Explain the internet of things What makes the industrial internet of things distinct? How…
Q: Suppose a Unix Inode has 10 direct disk block pointers, one single indirect block pointer, one…
A: We have 10 direct pointers that each point directly to a 4K data block, so we can point to 10 * 4K =…
Q: What kinds of things can you do to have a better handle on how much time you spend on the internet…
A: (1) Create a better communication platform: Hardware and software developments have made internal…
Q: Which command generates a complete list of all the files and their permissions in the current…
A: The ls command is used to list files or directories in Linux and other Unix-based operating systems…
Q: Define and describe "the TOR network"
A: Given: It is necessary for us to define and explain the term "TOR network." The Tor network was…
Q: Translate into English. Let p = "I am studying Java", q = "It is sunny", r = “I am at the beach" For…
A: According to the information given:- We have to translate into English.
Q: Find out how mobile devices and cloud computing are connected, and discover the most important…
A: The mobile phone has developed at a dizzying speed. It has evolved from a device used primarily for…
Q: Question 6 The following scenario is an example of which algorithm construct? A flowchart needs to…
A: Disclaimer: “Since you have asked multiple question, we will solve the first question for you. If…
Q: onsider the Qui finding a pivot el which contains th recursion tree for
A:
Q: Is there a difference between a system subsystem and a logical division?
A: According to the information given:- We have to difference between a system, subsystem and a logical…
Q: What is the distinction between bottom-up and top-down approaches to information security? Why is…
A: The following question is presented: What distinguishes a top-down approach to information security…
Q: What is an example for a cache hit? The cache hit refers to the data that is most popular, i.e.…
A: Cache Memory : Cache memory component is present between CPU and main memory of the computer. These…
Q: ecommendations do you hat modate mobile and wireless
A: Introduction: Computing gear that are interconnected and ready to impart assets and data to each…
Q: The use of cloud computing has the potential to have profound implications for society. Is it…
A: Cloud computing uses the internet to access resources such as programmes, servers (both real and…
Q: Exist any software engineering ideas that were not mentioned? Explain?
A: Given: Any set of executable instructions computes.Code, libraries, and documentation are…
Q: What type of network would you suggest for workers that operate remotely and mostly wirelessly?
A: The type of network we should be using for remote access is: Citrix Workspace Solution : It is a…
Q: I need a python code for the following phase: Phase 1: Convert the regular expression into NFA.…
A: from typing import NamedTuple def match(pattern, string): class Node(NamedTuple):…
Q: What is Network Address Translation (NAT) in computer networks?
A: Given: To be familiar with the NAT protocol in relation to networking.
Q: Assume a computer has two network interface cards, NIC1, a Wifi USB, and NIC2, an on-board Ethernet.…
A: The network interface card (NIC) enables computers to interact across a computer network via wired…
Q: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7,9 ?
A: To form a 3 digit number using 1,3,5,7,9. We know that all the 3 digit places are must be one of the…
Q: Assume a computer has two network interface cards, NIC1, a Wifi USB, and NIC2, an on-board Ethernet.…
A: The answer is given in the below step
Q: How can internet data be protected from hackers?
A: Ways to protect internet data from hackers:
Q: D- AND Enter the missing binary digits to complete this truth table for an AND gate. Input A Input B…
A: The AND gate is a basic digital logic gate that implements logical conjunction (∧) from mathematical…
Q: What are the benefits of networking software that permits communication between teachers and…
A: Answer: we need to write what are the benefit of networking that permits communication between…
Q: Write a PHP code to get the forbidden energy gap for an atom after taking the minimum band of…
A: Required:- Write a PHP code to get the forbidden energy gap for an atom after taking the minimum…
Q: What does the term Routing entail?
A: Given: Routers move data packets from source to destination.Routers function at OSI's network layer…
Q: Consider the significance of wireless networks in underdeveloped nations now. In numerous…
A: Start: Billions of people now have access to the Internet and can participate in today's digital…
Q: What does the word "Computer Forensics" mean?
A: Here in this question we have asked that What does this word "Computer Forensics" mean?
Q: Discuss the significance of networking and how it might be used in your organization. It is…
A: Networking is highly crucial for any business or organization since it enables the devices to…
Q: you will create a spell checker. The program will take three command line arguments: number of words…
A: Filename: main.cpp #include <iostream> #include <string> #include "QuadraticProbing.h"…
Q: You are working on a solution to add two 8 bit numbers, and encounter an error when you add 11111111…
A: Question 1 : Correct option is "Overflow". Explanation: We are adding 8-bit numbers and the range…
Q: What would happen if database referential integrity was not enforced? What are the most probable…
A: Please upvote. I am providing you the correct answer below. Please please please.
Q: What kind of information is essential for the ExitProcess method to have?
A: ExitProcess do: The ExitProcess function kills the current process, including the caller thread,…
Q: Kindly provide us with three specific examples of how the procedures involved in running a company…
A: Below are three examples where a company is benefitted from cloud computing. 1. Helps in scaling up…
Q: Software engineering approaches and techniques are often less expensive in the long term than…
A: Given: Explain in a few sentences why it is often more cost-effective to use the approaches and…
Q: What is accountability? Describe the many forms of traceability.
A: Traceability model: Model traceability refers to the capacity to track where a model has been and…
Q: In what way do you believe the use of wireless technology presents the greatest potential drawback?
A: Wireless Technology: Infrared and radio frequencies often interfere with the transmission of…
Q: Provide an explanation of what the internet of things is and how it operates. What makes the…
A: Technology: Technology is evolving at such a rapid speed that it appears to be moving faster than…
Q: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7,9 ?
A: To form a 3 digit number using 1,3,5,7,9. We know that all the 3 digit places are must be one of the…
Q: When it comes to selecting a physical network security solution, what factors should you consider?…
A: Given: Simply use Network safety Physical network topologiesA topology is a LAN's physical and…
Q: Do you know what distinguishes wireless internet connections from their wired counterparts in terms…
A: Given: Here, we will discuss wireless connectivity and their wired equivalents, as well as the…
Q: A GSM system uses 124 channels and each channel is divided into 6 time slots. What is the maximum…
A: Answer:-
Q: Describe how the Spiral Model and the V Model are used to manage the execution of projects, and…
A: Given: 1) Spiral Model is a key Software Development Life Cycle model for Risk Management. It's…
Q: DEFINE THE CONCEPT OF A UNIFIED MEMORY ARCHITECTURE.
A: Step 1 of 2:) Introduction: Unified memory is about reducing the duplication of data transferred…
Q: Why is RISC CPU installation simpler than CISC CPU installation?
A: Why is it simpler to install a RISC CPU than a CISC CPU: Reduced Instruction Set Computer (RISC):…
Q: (c) Given the code below please answer the questions. class Products extends CI_Controller { public…
A:
Step by step
Solved in 2 steps

- Using a 32-bit bitfield, assume two's complement encoding with a binary point between bits 23 and 24. | What is the largest possible number that can be expressed? What is the numeric precision of this format?FROM the LEFT, what are respectively the 2nd bit, 4th bit, and 6th bit if 150 base 10 is represented using 2’s complement? a. 0 1 1 b. 1 1 1 c. 1 0 0 d. 0 1 009. Show the 4B/5B encoding, and the resulting NRZI signal, for the following bit sequence: 1101 1110 1010 1101 1011 1110 1110 1111.
- 1. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 c. 0000 000 2. Using odd parity, add parity bits to the following bit patters: a. 0110 100 b. 1011 011 c. 0000 000True/False The number of distinct values represented in a 32-bit sign-magnitude binary representation is identical to the number of numbers represented in a 32 bit 2's complement notation.Convert 1, 9, and 1 into 8-bit ASCII characters usingeven parity. Convert this 24-bits digital data into digital signal using the following linecoding schemes:a) Bipolar AMIb) Polar NRZ-Lc) Polar differential Manchesterd) 2B1Qe) MLT-3If the bitrate is 1911*100 what will be required average bandwidth in these schemes.Comment about the DC component and baseline wandering nature of these schemes.
- Beginning with one start bit followed by 21 data bits, 2 parity bits and 1 stop bit: a) What are the total number of bits in the frame? b) What would the overhead and throughput be (answer in percent)?Kindly answer the following questions. f. If the word length is 6 bits (including sign), what decimal number does 1000002 represent in sign and magnitude? In 2's complement? In 1's complement? g. What is meant by an overflow? How can you tell that an overflow has occurred when performing 1's or 2's complement addition? Does a carry out of the last bit position indicate that an overflow has occurred?Hi I need help with this data encoding problem, no computer coding is involved. 6. Add the two's complement (16 bit) values as indicated, writing your answer in the space provided. Indicate whether there was 'Overflow' or 'No overflow' and 'Truncation' or 'No truncation as appropriate. Remember, each answer must have exactly 16 bits. 0001 0100 1000 1101 + 0100 0010 0010 0111= ______ Did overflow occur? Y or N Did truncation occur? Y or N
- How is it possible to distinguish between the least significant bits and the most significant bits?98. Usually, it takes 10-bits to represent one character. How many characters can be transmitted at a speed of 1200 BPS? a. 12 b. 120 c. 1200 d. 120001. Using 8-bits, convert -45 to excess-127 notation in binary. 2. If 1001 0110 is a binary number in excess-127 form, what is the decimal number? 3. Convert 97 to sign magnitude form using 8 bits. 4. Convert -97 to sign magnitude form using 8 bits. 5. Convert -97 to one’s complement form using 8 bits. 6. Convert -89 to two’s complement form using 8 bits. 7. If 1001 0111 is in two’s complement form, what is the decimal number? 8. Using two’s complement form with 8 bits, perform the following arithmetic. a. Add 34 and 27 b. Add 78 and 64 c. Subtract 45 from 78 d. Subtract -45 from 78 e. Subtract 45 from -78 f. Subtract -45 from -20 9. Convert -123.6875 to IEEE format. 10. Convert 458D A600 from IEEE format to decimal form.

