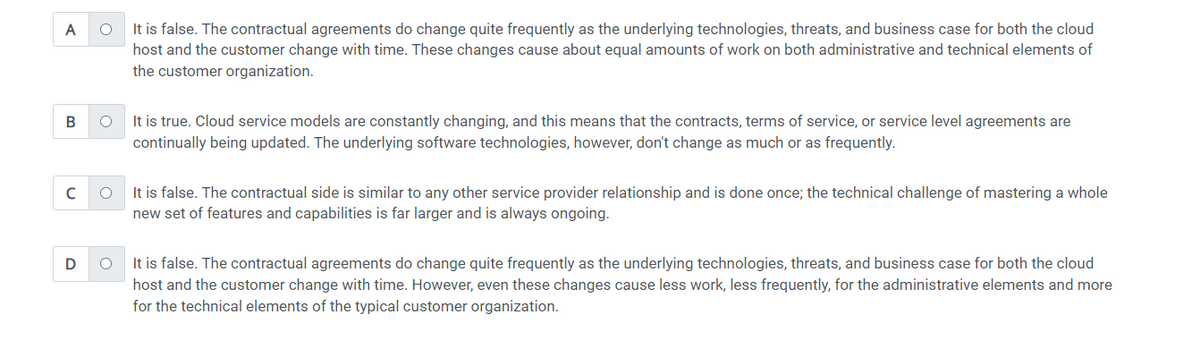
"maintaining or improving information security while migrating to the clouds is more of a contractual than technical problem to solve".which statement best shows why this is either true or false?
"maintaining or improving information security while migrating to the clouds is more of a contractual than technical problem to solve".which statement best shows why this is either true or false?
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter4: Software And Mobile Applications
Section4.3: Application Software
Problem 2CTQ
Related questions
Question
"maintaining or improving
Transcribed Image Text:A
B
с
D
O
It is false. The contractual agreements do change quite frequently as the underlying technologies, threats, and business case for both the cloud
host and the customer change with time. These changes cause about equal amounts of work on both administrative and technical elements of
the customer organization.
O It is true. Cloud service models are constantly changing, and this means that the contracts, terms of service, or service level agreements are
continually being updated. The underlying software technologies, however, don't change as much or as frequently.
O
It is false. The contractual side is similar to any other service provider relationship and is done once; the technical challenge of mastering a whole
new set of features and capabilities is far larger and is always ongoing.
O
It is false. The contractual agreements do change quite frequently as the underlying technologies, threats, and business case for both the cloud
host and the customer change with time. However, even these changes cause less work, less frequently, for the administrative elements and more
for the technical elements of the typical customer organization.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning