many-many, many-one, and one-one erd relationship in sql tables? PLEASE USE SIMPLE CROWS FOOT ERDS!!!
many-many, many-one, and one-one erd relationship in sql tables? PLEASE USE SIMPLE CROWS FOOT ERDS!!!
Chapter13: Views
Section: Chapter Questions
Problem 2MC
Related questions
Question
Does anyone know how to type up a many-many, many-one, and one-one erd relationship in sql tables? PLEASE USE SIMPLE CROWS FOOT ERDS!!!! Also, in the screenshot provided below, my teacher says "FOREIGN KEY (e_ssn) REFERENCES employee (ssn)" at the bottom, what does that mean? If youre having trouble understanding the 1st part of my question, use 2nd shot for reference.
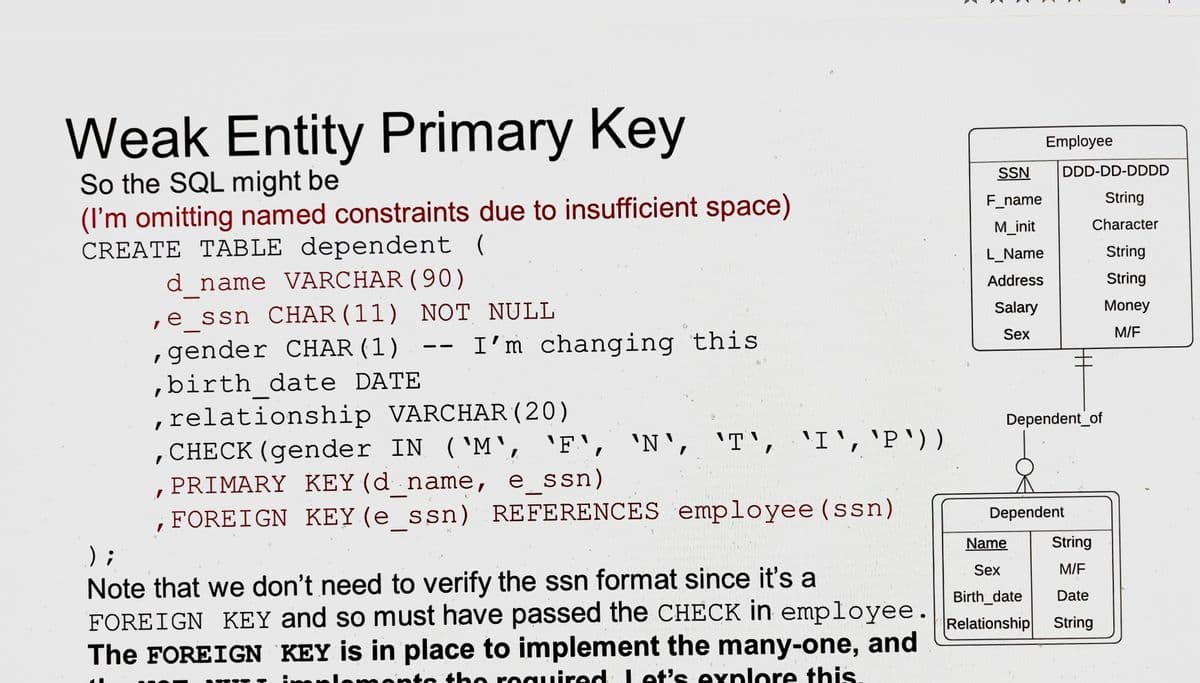
Transcribed Image Text:Weak Entity Primary Key
So the SQL might be
(I'm omitting named constraints due to insufficient space)
CREATE TABLE dependent (
d name VARCHAR (90)
e ssn CHAR (11) NOT NULL
,gender CHAR (1)
,birth date DATE
-
I
I'm changing this
,relationship VARCHAR (20)
, CHECK (gender IN ('M', 'F', 'N', 'T', 'I', 'P'))
PRIMARY KEY (d_name, e_ssn)
FOREIGN KEY (e_ssn) REFERENCES employee (ssn)
A
to th
the r
Note that we don't need to verify the ssn format since it's a
FOREIGN KEY and so must have passed the CHECK in employee.
The FOREIGN KEY is in place to implement the many-one, and
quired Let's explore this.
require
3
SSN
F_name
M_init
L_Name
Address
Salary
Sex
Employee
DDD-DD-DDDD
String
Character
Dependent_of
Name
Sex
Birth_date
Relationship
Dependent
String
M/F
Date
String
String
String
Money
M/F
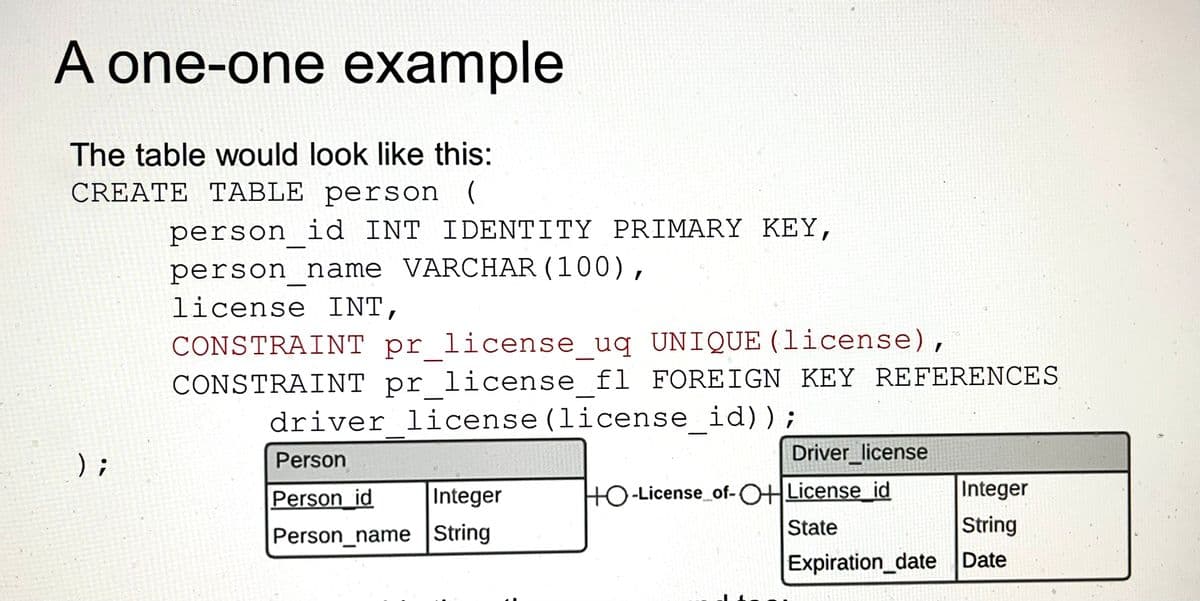
Transcribed Image Text:A one-one example
The table would look like this:
CREATE TABLE person
);
person id INT IDENTITY PRIMARY KEY,
person_name VARCHAR (100),
license INT,
CONSTRAINT pr_license_uq UNIQUE (license),
CONSTRAINT pr license f1 FOREIGN KEY REFERENCES
driver license (license id));
Person
Person id
Integer
Person_name String
Driver license
Integer
String
Expiration_date Date
HO-License_of-OH License_id
State
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you


Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning


Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning