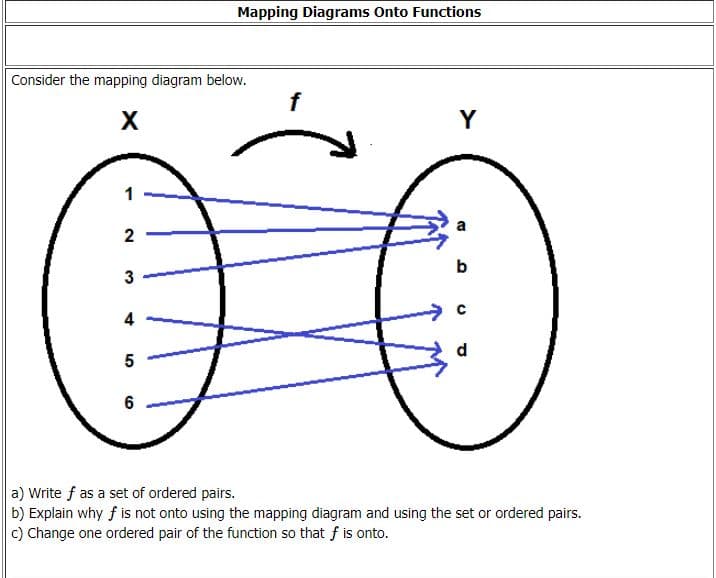
Mapping Diagrams Onto Functions nsider the mapping diagram below. X Y 2 b 4 d 5 6 Write f as a set of ordered pairs. Explain why f is not onto using the mapping diagram and using the set or ordered pairs. Change one ordered pair of the function so that f is onto.
Q: Define the concept of a unified memory architecture.
A: The goal of unified memory is to reduce data redundancy by copying data between separate areas of me...
Q: What is data mining and how does it work? Compile a list of data mining tasks?
A: Introduction: Data mining is the process of collecting information from data by identifying patterns...
Q: please code in python You are given an array of strings arr. Your task is to construct a string fro...
A: Here I have created the function named finalString(). In this function, I have extracted the length ...
Q: Use the following tree to indicate the order that nodes are expanded, for different types of search....
A: Use the following tree to indicate the order that nodes are expanded, for different types of search....
Q: Given an Array A = what will be the updated array A after we run some partition (A, 1 , 5) some pa...
A: Lets trace the partition procedure on A = <5,4,3,2,1>partition(A,1,5)partition(a,p,r)a= <5,...
Q: Generate orthogonal codes for use in this system. Use the minimum possible number of chips per bit.
A: Walsh codes are orthogonal codes used extensively in cdmaOne and cdma2000. Spread factor or process ...
Q: Create a recursive function and program for following equation using C++ f(5) = 5*(4/2)*3*(2/2)*1 ...
A: A recursive function consists of 2 cases: 1. Base case(i.e condition where recursion stops) 2. Recur...
Q: What is the difference between an argument and a return value? How many arguments can a method c...
A: Argument in JAVA: An Argument is a value passed to a function when the function is called . Return v...
Q: Explain how the Internet of Things works.
A: Introduction: Devices and items with built-in sensors are connected to an Internet of Things platfor...
Q: GetConsoleScreenBufferInfo method description.
A: Answer: Character and colour data are stored in a screen buffer, which is a two-dimensional array.M...
Q: What is the Maple command all about exactly?
A: Explain Maple command all about exactly?
Q: Fault management, performance management, and security management are all terms that are used interc...
A: INTRODUCTION: FAULT MANAGEMENT: It is the fault management's role to identify and disconnect faulty ...
Q: Explain what happens at the client when a DNS server returns multiple IP addresses for a given query...
A: When a DNS server returns IP addresses for a query, it often returns multiple IP addresses. When thi...
Q: Give ReadFromFile a name and a description.
A: Introduction: The ReadFromFile method reads from a file the value of a string or binary field.
Q: A number 428 in duodenary (base 12) is to be added to C10 in tredenary (base 13), what is their diff...
A: Here in this question we have given two number in base 12 and 13 i.e (428)base12 (C10)base13 and we ...
Q: write a shell program to get mark details of a student and display total and grade?
A: Shell program to get mark details of a student and display total and grade echo ------------------...
Q: Basic concepts and benefits behind computer networks (Discuss the basic concepts behind compute...
A: Basic concepts and benefits behind computer networks are
Q: In a three-tier design network where would access points be placed? a. Wireless Layer b. Access Laye...
A: Given: We have to discuss In a three-tier design network where would access points be placed.
Q: Is it feasible to store a HashMap with a duplicate key?
A: Introduction: A hashmap is a data structure that stores data as a pair of keys and values.
Q: IDPSS have been added to IDS systems by a number of companies. Describe them.
A: Answer: In data centres, the cloud, and in the workplace, McAfee Network Security Platform (NSP) s...
Q: What is the catastrophe recovery process's principal objective?
A: Introduction: Catastrophe recovery/ Disaster recovery: Disasters such as fire, flooding, terrorist a...
Q: 2. Impact Assessment Consider the simplified model for risk shown in class. Assume the following par...
A: Answer :-
Q: Which of the following are true (mark all that apply)? O His a leaf and a child of D. O Eis the chil...
A: It is true because H has no children so it is a leaf node and H is the subnode of D.
Q: What is the hash function's purpose? What's more, how does it work?
A: Introduction: A hash function turns a numerical input number into another compressed number value. T...
Q: Which of the following are elements of a good Mobile Device Management (MDM) policy? Select all that...
A: To find elements of a good Mobile Device Management (MDM) policy.
Q: What is 5113439150942 in mantissa x base ^ exponent notation, to 4 significant digits using the ties...
A: According to the information given:- We have to find out the mantissa x base ^ exponent notation, to...
Q: Explain why it is important that software products are developed and delivered quickly ?
A: Whenever a firm pays a service request, then sides agree on the project's timeline.
Q: create a complete program that will accepts string of characters or sentence and print each word in ...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read a string Split...
Q: Complete the following table, stating the start and end times for each process using the Shortest-Jo...
A: Shortest Job next is a non preemptive CPU scheduling algorithm where process with shortest service t...
Q: average(double X, double y, double 2), returning he average of the arguments
A: Given 1. Write the following methods and provide a program to test them . b. double average(double x...
Q: Write a PYTHON Script to find y from the below equations depending on your entry. tan(4)-cos (0) sin...
A:
Q: Give Description for ReadKey
A: Description for ReadKey
Q: Write a python code to build regression models using the following learning algorithm
A: import matplotlib matplotlib.use('GTKAgg') import matplotlib.pyplot as plt import numpy as np f...
Q: Write a single if else if statement with the following criteria: reading -10 to -1 output Fails the ...
A:
Q: Provide an explanation for ReadDec
A: Introduction: The Read Dec method takes a 32-bit unsigned decimal integer from the keyboard and conv...
Q: Computer Science T(n) = T(n-3) + n using chip and conquer method
A:
Q: The ubiquitous nature of mobile phones today brings tremendous convenience to our lives, but will mi...
A: In today's world of advanced information and technology, mobile phones and devices are being extensi...
Q: re how to use test-path, we look at its syntax in the Help file. Using the first syntax example give...
A: test-path Cmdlet Syntax: This cmdlet is used to test now not most effective a record exists however...
Q: Give an explanation for the method GetNumberOfConsoleMouseButtons.
A: Introduction : This line pertains to the capability of your mouse's scroll wheel, and in my instance...
Q: uppose we are told that the plaintext breathtaking when ecrypted, the ciphertext becomes: RUPOTE...
A: The Answer is as follows.
Q: In PYTHON, write a code that allows the user to input two non-negative number sequences in increasin...
A: the answer is given below:-
Q: EXERCISE 15 Write a function Your first name_Last name_Ex15 with three variables x, y, and z as inpu...
A: ANSWER:-
Q: 4. Complete the following truth table by finding the truth values of the Boolean expressions for all...
A: operators used in given expressions: && :And operator p && q is: true when both p an...
Q: Using C (not C++ or C#) I need help in solving the following problem. So I have the persisting code ...
A: Your C code is given below as you required with an output.
Q: Employee class is having three properties known as name, EmployeeID, address. Write a Java program t...
A: Algorithm: Start Create a class named Employee with name, EmployeeID and address as its attributes ...
Q: Explair
A: given - explain briefly how the switch dynamically build the MAC address table (learn process)
Q: Fast Food Restaurant Make a program that has several food items on the menu with prices. The use...
A: Note: Code runs successfully as the above problem describe. I am using the c++ language to do this p...
Q: The Z-pattern layout is typically used on pages that are not content heavy. Its design mimics the ro...
A: (a). Answer: A Z-Pattern design traces the route the human eye travels when they read left to right,...
Q: What does the Maple command mean?
A: Introduction: Maple command: The maple command is used to automatically finish the work of specific ...
Q: Write a Python program that will ask the user to input a string(containing exactly one word).then yo...
A: Algorithm: Start Read a word 's' Iterate through the loop from i=0 to i=len(s)-1 Inside the loop, p...
Step by step
Solved in 2 steps with 2 images

- Access PyCharm. Then, demonstrate how to work with the complex objects as outlined below. Take appropriate screenshots (with descriptions) as needed. Create functions that take five arguments and multiplies them according to the type of object they are: Scalar Vector Matrix Plot each of the functions that you have constructed.A) quadrant [★★] Complete the quadrant function below, which should return the quadrant of the given x, y point according to the diagram on the right (borrowed from Wikipedia). Points that lie on an axis do not belong to any quandrant. Hints: (a) define a helper function for the sign of an integer, (b) match against a pair. type quad = I | II | III | IV type sign = Neg | Zero | Pos let sign (x:int) : sign = ... let quadrant : int*int -> quad option = fun (x,y) -> match ... with | ... -> Some I | ... -> Some II | ... -> Some III | ... -> Some IV | ... -> None B) quadrant when [★★] Rewrite the quadrant function to use the when syntax. You won’t need your helper function from before. let quadrant_when : int*int -> quad option = function | ... when ... -> Some I | ... when ... -> Some II | ... when ... -> Some III | ... when ... -> Some IV | ... -> None please use Ocaml for the codeWrite a struct ‘Student’ that has member variables: (string) first name, (int) age and (double) fee. Create a sorted (in ascending order according to the age) linked list of three instances of the struct Student. The age of the students must be 21, 24 and 27. Write a c++ function to insert the new instances (elements of the linked list), and insert three instance whose member variable have age (i) 20, (ii) 23 and (iii) 29. Write a c++ function to remove the instances from the linked list, and remove the instances whose member variables have age (i) 21 and (ii) 29. Write a c++ function to count the elements of the linked list. Write a c++ function to search the elements from the linked list, and implement the function to search an element whose age is 23. Write a c++ function to print the linked list on the console.
- Complete the docstring below using the helper function and information attached: def get_last_syllable(word_phonemes: PHONEMES) -> PHONEMES: """Return the last syllable from word_phonemes. The last syllable in word_phonemes is formed from the last vowel phoneme and any subsequent consonant phoneme(s) in word_phonemes, in the same order as they appear in word_phonemes. >>> get_last_syllable(('AE1', 'B', 'S', 'IH0', 'N', 'TH')) ('IH0', 'N', 'TH') >>> get_last_syllable(('IH0', 'N')) ('IH0', 'N') >>> get_last_syllable(('B', 'S')) () """Write the query for implementing the following functions: MAX(),MIN(),AVG(),COUNT() Write the query to implement the concept of Intergrity constrainsT or F -Functions are considered to be objects in JavaScript because they contain three critical attributes: data, methods that act on the data, parameters for passing the data also known as awareness. -A recursive function is a function that calls itself and eventually returns default value to break out of the recursion. -A function that is used to create a new object is called an anonymous function. -Attributes define additional characteristics or properties of the element which is the same as for the start tag. -Javascript is similar to the Java programming language
- Please use DrRacket to program: - make-object: creates and returns a rudimentary "object" as a closure over an associative list containing attributes. The returned closure (i.e., function) responds to three "messages": get, set, and update. get takes an attribute key, whose value is returned (if it exists). set takes an attribute key and value, which are used to update the associative list update takes an attribute key and a function which is used to update the associative list by applying it to the current value make-object takes one argument, the initial name of the object (associated with the attribute key 'name). starter code: (define (make-object name) void)Please answer in SCHEME ony. Define the function (bubbleLst lst). This function should resolve to a list of sublists, where each sublist holds a single element from lst. For example: (bubbleLst '( 1 2 (3 4)) ) resolves to '((1) (2) ((3 4))).1.14 Explain what the map function does in a functional language. How does it provide additional abstraction capability in a programming language?
- Write a struct ‘Student’ that has member variables: (string) first name, (int) age and (double) fee. Create a sorted (in ascending order according to the age) linked list of three instances of the struct Student. The age of the students must be 21, 24 and 27. Write a function to insert the new instances (elements of the linked list), and insert three instance whose member variable have age (i) 20, (ii) 23 and (iii) 29. Write a function to remove the instances from the linked list, and remove the instances whose member variables have age (i) 21 and (ii) 29. Write a function to count the elements of the linked list. Write a function to search the elements from the linked list, and implement the function to search an element whose age is 23. Write a function to print the linked list on the console. Consider the Student struct as defined above. Create a stack of 5objects of the class. Implement the following (i) push an element to the stack (ii) pop an element from the stack (iii) get the…data strcture using JAVA i need the codes for all the following functions Requested work : 1. Define a function newList to create a new empty linked list. 2. Define a function sizeList to return the size of a given linked list 3. Define a function displayList to display the content of all nodes of a given linked list. 4. Define a function addNodeHead to add a new node on the head of a given linked list. 5. Define a function addNodeQueue to add a node on the queue of a given linked list. 6. Define a function delNodeHead to delete a node from the head of a given linked list. 7. Define a function delNodeQueue to add a node from the queue of a given linked list. 8. Define a function insertNodePos to add a new node on the given position of a given linked list. 9. Define a function delNodePos delete a node from a given position of a given linked list. 10. Test all previously defined functions in the main method.Define the function print_trophic_class_summary(tli3_values) that accepts a list of trophic level index values and prints a summary outlining the number of lakes in each trophic classification, in order from highest trophic classification to lowest. See the examples for the required format. Notes: Your function must print the summary, not return it. In each state line, the initial number should be formatted with width 3. (Hint: :3 will be helpful) All possible states must be included in the output, even states with zero lakes. The following list will be helpful: ['Hypertrophic', 'Supertrophic', 'Eutrophic', 'Mesotrophic', 'Oligotrophic', 'Microtrophic', 'Ultra-microtrophic'] You must include and use one of your number_in_trophic_class functions (take your pick!), plus your trophic_class function. Basically, you can start with your answer to Question 5 or 6 and add your print_trophic_class_summary function definition after your previous definitions. For example: Test Result…

