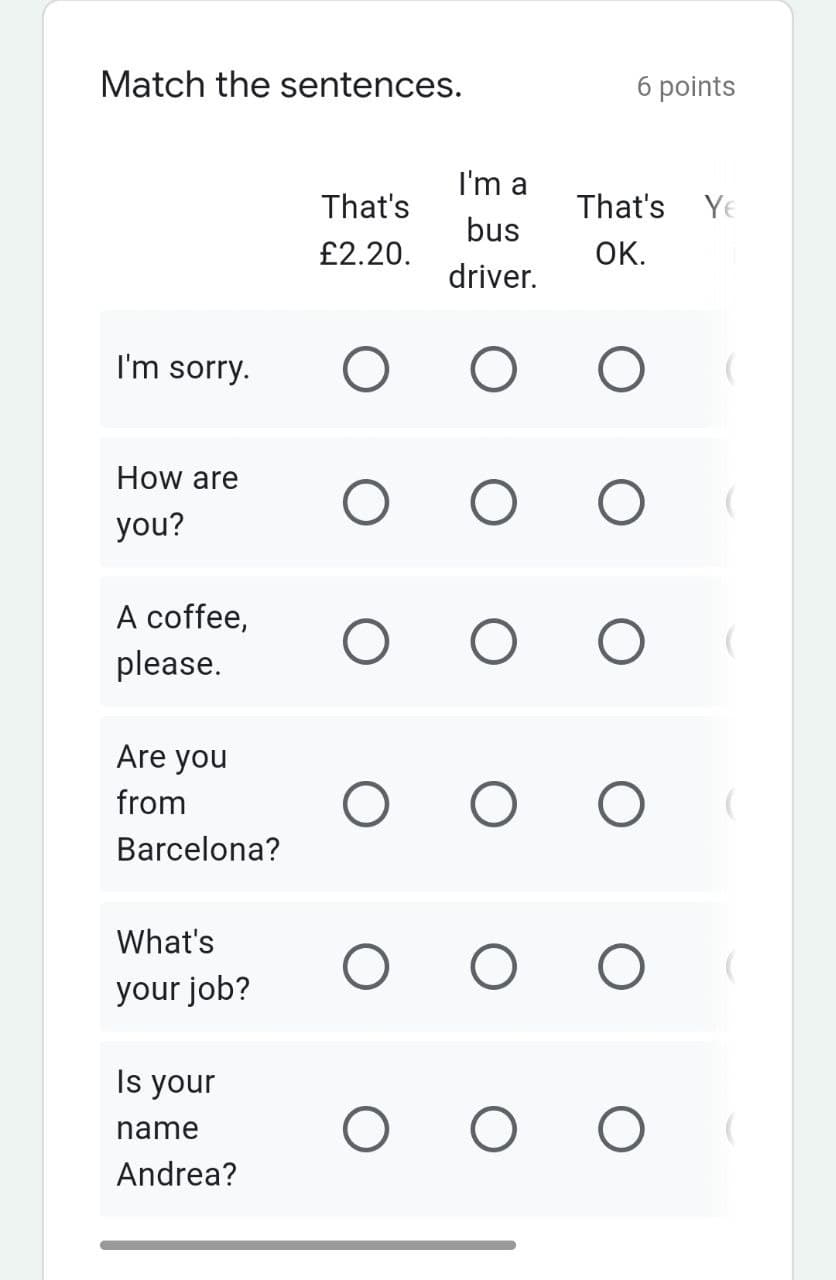
Match the sentences. 6 points I'm a That's That's Ye bus £2.20. OK. driver. I'm sorry. How are you? A coffee, please. Are you from Barcelona? What's your job? Is your
Q: When it comes to a processor's access to main memory, weigh the benefits of a loosely connected syst...
A: The major difference between a loosely linked and a symmetric multiprocessing system is that the for...
Q: Name two other major purposes of operating systems in addition to virtualization, concurrency, and p...
A: Here is the solution:-
Q: )a) Draw the given function in the MATLAB command line by following the steps below. 1. Time vector ...
A: code : Editable code : t=0:0.1:10; x=t.*exp(-t); plot(t,x) grid on; xlabel('t(time)'); ylabel('x...
Q: What are the major challenges in managing information systems? Explain the connection between the Fi...
A: What are the major challenges in managing information systems? Explain the connection between the Fi...
Q: ● Write TCP client and server that can communicate to each other saying “Hello I am client and My id...
A: The following code performs the above actions:
Q: Describe the common components needed to create a Web-based application.
A: Lets see the solution.
Q: The code has to be in C++, You are to use the started code provided with QUEUE Container Adapter...
A: Here is the solution with an output:-
Q: Why is HTML5 beneficial for developing mobile applications?
A: Lets see the solution.
Q: What is regression testing?
A: Regression testing means, testing the existing software application to ensure that the latest change...
Q: What are the three common types of cloud computing services?
A: Lets see the solution.
Q: ny is Access a better tool than Excel for keeping track of this information?
A: Given :
Q: A= B if and only if : * A is subset from B and B is not subset from A A is not subset from B and B i...
A: Find the answer with explanation given as below :
Q: Instructions: Analyze the program below and determine what are the identifiers in there. using Sys...
A: Identifiers are user defined words such as variable name, class name, method name, block name etc.
Q: Explain when to use different types of fileorganizations to store computer files.
A: Let's see the solution in the next steps
Q: What is regression testing?
A: Here is the solution with an explanation:-
Q: onvert the following mip C co high level languageli $s0, 10 li 5 mul $s2, $s0, $s1 li $v0, 5 la $t v...
A: Lets see the solution.
Q: Let a = 2. Given variables x and y as the inputs, write a MATLAB function to create: yx a Function e...
A: Find the required code in MATLAB and output:
Q: What exactly do you mean by "computer forensics"?
A: Below is the answer of computer forensics. I hope this will meet your requirements.
Q: Suppose that we have a byte-addressable computer with 16-bit main memory addresses and 32 blocks of ...
A: Introduction: The current computer system's memory hierarchy is a complicated arrangement of caches ...
Q: A virtual machine is created to serve a purpose, depending upon the available resources in the resou...
A: A VM provides an isolated environment for running its own OS and applications independently from the...
Q: The following equation estimates the average calories burned for a person when exercising, which is ...
A: As per the given problem, the formula for calculating the calorie is : Calories = ( (Age x 0.2757) +...
Q: A rotation cipher is one of the simplest, plain-text ciphers, known since at least the time of Juliu...
A: # define variables keep_going = True alphabet = 'abcdefghijklmnopqrstuvwxyz' while keep_going != Fa...
Q: The Python programming language is what I'm interested in."
A: A scripting language written in Python Because of its complexity, Python is referred to be a high-le...
Q: In what way did the computer get made?
A: Introduction: Computers store and process data using a binary system of ones and zeros. Computers a...
Q: Describe the whole process of designing address subblocks and back it up with an example of separati...
A: The given IP address is 10.10.10.0 /27 Here /27 means # of network ID bits is 27. Therefore number o...
Q: Write the code to find the count of the number of elements in x with a value less than 8.5, and then...
A: Given requirement, Write the code to find the count of the number of elements in x with a value less...
Q: After he came up with the world's fastest computer, Philip Emeagwali did it
A: Firstly let's talk about who is philip emeagwali . He is person from nigeria . He is person known to...
Q: For questions 2-4, please refer to the neural network equations below: "- xw "-(my -"wn -(") -E- ()-...
A: Let's see the solution in the next steps
Q: What is a run-time error?
A: Lets see the solution.
Q: Contrast the term SOAP; XSLT?
A: Two Dynamic Application communication protocols that transforms the objects from XML documents is ex...
Q: In which university did Grace Hopper do her undergraduate
A: In which university did Grace Hopper do her undergraduate
Q: What is the most suitable programming language used in software development? first generation langua...
A: Ans) third generation languages:- 3GLs are much more machine-independent (portable) and more program...
Q: Describe the difference between operators and punctuation symbols.
A: Introduction: A letter or symbol that performs operations on one or more operands is referr...
Q: Encryption protects secrecy, integrity, authenticity, and nonrepudiation in what ways? Give at least...
A: Encryption is a technique utilized in information security wherein a user has access to data through...
Q: Convert the following function to its corresponding canonical POS form using boolean algebra. Write ...
A: I have written solution below,
Q: Brief information about matlab software
A: MATLAB is a software package utilized by engineers all around the world to simulate & manage har...
Q: In what ways does von Neumann architecture differ from other styles of building?
A: Introduction: The Characteristics of Von Neumann Architecture: While architecture is most commonly ...
Q: Write an algorithm to find the maximum in an array
A: Dear student, As per guidelines, I can do only first question. Please re-post your pending question ...
Q: To facilitate access to external file systems, the Virtual File System layer was utilised. It did, h...
A: The primary goal of the virtual file system layer is to allow client programs to access various type...
Q: What components must a PHP program that enables a dynamic Web site contain?
A: Introduction: PHP stands for "PHP: Hypertext Preprocessor." PHP is a popular open-source programming...
Q: What was John von Neumann's home town?
A: Introduction: Who Was John von Neumann? John von Neumann was a child prodigy born on December 28, 19...
Q: Describe some of the notions that Ada Lovelace came up with.
A: Ada lovelace is considered to be the first programmer. She is known to be the first person to invent...
Q: What are the applications of Subneting?
A: According to the question the subnet allows to the community to carry out speedy and makes the commu...
Q: What are the problems involved with mixed data? Discuss with suitable examples four ways of converti...
A: Mixed data is a data that is created from multiple sources, each of which may have different attribu...
Q: |{1,1}x{2,3,4}| is : * O 5 O 6 O 4 Consider the sets: A = %3D {1,3,4,5,8,9} B = {1,2,3,5,7} and C ={...
A: Solution:
Q: What Are the Most Common Errors That Can Occur in Data Modeling?
A: Introduction: Inappropriate denormalization: This method should be utilized only when absolutely ess...
Q: If I have a file that contains a name and ID number and I would like to store them in a listed link ...
A: struct hub { int id;singe name[50];struct hub *next;} *head; struct hub *insert(struct hub * list, s...
Q: Contrast the differences between range control and referential integrity when controlling data integ...
A: Lets see the solution.
Q: Concisely define each of the following keydatabase design terms: relation, primarykey, functional de...
A: Lets see the solution.
Q: Why were computer programming languages invented?
A: Introduction: Why were computer programming languages invented? Understanding technology may be aide...
Step by step
Solved in 2 steps

- Solve all question in the picture, because I'ts despand on each others.dont dont psot copied one sure and strict doownvote sure sure dislikeWhat pictures do you associate with email? What happens to an email once it's sent? Make a list of what you know. Is there anybody who can explain these differences? Is each model complex?
- What type of mental pictures come to mind when you think about email? Where does an email really go after it's been sent? Get everything down on paper that you can think of right now. Is there anybody here who is aware of the causes of these variations, and if so, could you please enlighten me? Do your models all depict equally complicated scenarios?Do you plan to start using email within the next several years? An email's journey begins with the sender and finishes with the recipient. Record your findings in detail. Can the discrepancies be explained, and if so, how? Let's pretend there's a whole bunch of models, and they all have somewhat different difficulties (or abstraction).How do you see the information included in an email when you read it? Which of these methods is the best time- and resource-effective approach to forward an email? Make a list of everything you've learned along the road and everything you've picked up along the way. What differentiates them from other things, and why are they so widespread in the world today? How many distinct levels of detail are there in models, or alternatively, how many distinct levels of abstraction can be found in models?
- Question 6 sa Full explain this question and text typing work only thanksWhat comes to mind when you think about email? Which of these approaches to sending emails is the most efficient? Create a mental list of everything you've picked up thus far. What sets them apart from other things, and why are they so prevalent? What are the different degrees of detail (or abstraction) that may be found in models?When do you plan to start using email, and how soon do you anticipate starting? A linear path is followed by an email, starting with the sender and finishing with the receiver of the message. Your results should be documented in great detail. Are there any possible explanations for the differences, and if so, what are they? Imagine a varied collection of models, each of which presents its own unique set of difficulties (or abstractions).
- Computer Science What is the difference between implicit intent and explicit intent? Write code for sending User Name, User Email and User Age from Activity A to Activity B in android.is b the right answer???What thoughts do you have about the use of electronic mail? What are the stages that must be completed before an email may be sent from A to B? Make a mental note of your current level of comprehension. What exactly does it mean to differentiate between things, and why is doing so so vitally important? Consider the amount of fine detail that has been included into each of the models (or abstraction).

