Matlab code Problem 3 Create a MATLAB Script File using a WHILE LOOP or For loop to plot the following function, Make sure to use enough points to create smooth curves. Provide a plot title, labels for the axes, and a legend for the two curves. 8.6 Create a function called g that satisfies the following criteria: For x < -#, For x2- and xs, For x> #, g(x) = -1 g(x) = cos(x) g(x)=-1 Plot your results for values of x from -27 to +2#. Choose your spacing to create a smooth curve.
Matlab code Problem 3 Create a MATLAB Script File using a WHILE LOOP or For loop to plot the following function, Make sure to use enough points to create smooth curves. Provide a plot title, labels for the axes, and a legend for the two curves. 8.6 Create a function called g that satisfies the following criteria: For x < -#, For x2- and xs, For x> #, g(x) = -1 g(x) = cos(x) g(x)=-1 Plot your results for values of x from -27 to +2#. Choose your spacing to create a smooth curve.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section: Chapter Questions
Problem 7PP: (Numerical) Heron’s formula for the area, A, of a triangle with sides of length a, b, and c is...
Related questions
Question
Transcribed Image Text:Matlab code
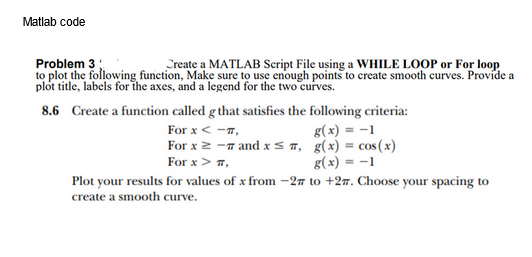
Problem 3
Create a MATLAB Script File using a WHILE LOOP or For loop
to plot the following function, Make sure to use enough points to create smooth curves. Provide a
plot title, labels for the axes, and a legend for the two curves.
8.6
Create a function called g that satisfies the following criteria:
For x < -#,
For x ≥ - and x≤,
For x > #,
g(x) = -1
g(x) = cos(x)
g(x) = -1
Plot your results for values of x from -27 to +27. Choose your spacing to
create a smooth curve.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L