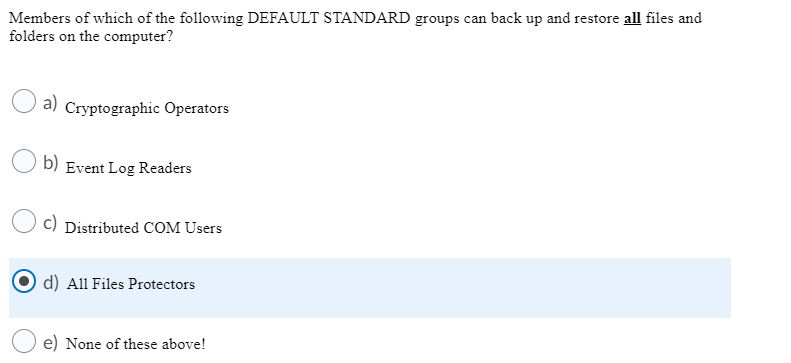
Members of which of the following DEFAULT STANDARD groups can back up and restore all files and folders on the computer? Cryptographic Operators b) Event Log Readers c) Distributed COM Users d) All Files Protectors e) None of these above!
Q: In which of the following authentication methods user needs to punch the card in the card slot or…
A: Given that In which of the following authentication methods user needs to punch the card in the card…
Q: In RBAC only administrators can modify an object's security label or a user's security clearance?…
A: Security: Security is an important aspect of any organization. Security plays an important role.…
Q: In MS Access, to ensure that a promised date valued entered must a future point in time,…
A: Now() function:The Now() function in Microsoft Access is used to return current date and time based…
Q: The administrator wanted to verify the password expiration of user "Ahmed." Write appropriate…
A: Dear Student, The Linux commands for each is given below - 1) command that is used to expire user…
Q: In Windows, the md command Lust be used to create a folder a. True b. False
A: In Windows, the Md command is not used to construct new files.
Q: Some files cannot be deleted using rm command because of the permissions associated with it.…
A: rm command In Unix/Linux operating system , the rm (referred as remove) command is a basic tool…
Q: Write a command to change the permission (others can read, owner can write, and group members can…
A: Basic File Attribute Plain file permissions have three basic attributes: read, write, and execute.…
Q: $ ls -l foo --Wx-w---x 1 uli101 users 813 Sep 13 20:30 foo What command line using octal method sets…
A: chmod Command: It is possible to modify a file's permissions using the chmod command. Changes to a…
Q: Which of the following cmdlets can you use to check if the Windows event log is running? a.…
A: Get-Member cmdlets can you use to check if the Windows event log is running.
Q: Which of the following tools can be used to encrypt a folder? Protect-Item PowerShell cmdlet…
A: Tools can be used to encrypt a folder
Q: Lli 4 The following code is true if you want to: Dim I as integer |= l+1 If password = "matrix" Then…
A: Here we have given the code and we have to tell which of the following statement is true according…
Q: Kerberos relies exclusively on __________ . A. symmetric encryption B. asymmetric encryption C.…
A: Asymmetric encryption: Asymmetric encryption is a public key encryption. It is a form of data…
Q: present a permissions number in the command chmod--filen.exe such that user ="rwx"'group=rx'others…
A: Chmod: it is command used to change the access permissions of file system objects. Here is the…
Q: Iba is modifying the basic NTFS permissions for a folder. She wants to enable the permission that is…
A: This mcq is based on NTFS permissions.
Q: def check_password exclusive(passwd: str) -> bool: **"An exclusive strong password has a length…
A: Please find the answer below :
Q: What permissions are granted to each class of users for a file with the following permissions?…
A: Different types of file permissions: --- no permission --x Execute permission -w- Write…
Q: Which of the following security attributes is required to ensure the data have not been changed or…
A: a. Authentication Authentication is the security attribute ensures that data have not been…
Q: With file protection, you can control how a user can work within worksheets.
A: The answer of this question is as follows:
Q: TEST CASES: You have an Active Voters account! Your full name is Juan Dela Cruz. You are 25 years…
A: Please find the answer below :
Q: pgrep -c kworker
A: The pgrep command: The pgrep command returns the process IDs of a functioning program based on the…
Q: 1) What is the command that is used to generate these key pairs? 2) Which system, SSH client or SSH…
A: According to the question we it is necessary to create both a public and a private key in order to…
Q: Which of the following statements is(are) true? (Check all that apply.) A. Symmetric encryption is…
A: There are two types of encryption one is symmetric encryption and other is asymmetric encryption
Q: Q) Which of the following functional component of AAA records what users do and what they access? O…
A: The correct option is Accounting.
Q: ???????? 2: Take the username and password from a user and check the validity of the password using…
A: Answer : Python code is # this functon convert lowercase to uppercasedef convert_to_lowercase(str):…
Q: In Unix Write down the related commands in the order the following steps: Step 1. Under your home…
A: Aim : Write the commands for given operations in Unix /Linux Solution: Step 1. Under your home…
Q: Unlike Command Prompt, PowerShell has a Updateable Help System, so we can use the Update-Help cmdlet…
A: We need to identify whether the given statement is True or False: Unlike Command Prompt, PowerShell…
Q: The application should support integrity verification. That is, your client and server will…
A: Find a code implementation below!
Q: administrator has gotten a call suggesting that following a password update, some users are…
A: Domain Controller: Domain controller is a server computer on Microsoft servers. The purpose of…
Q: Users with Print permission can view and manage the print jobs of other users. True False
A: File and Print administrations permit individuals to store, secure, offer, and print documents over…
Q: Which of the following software is loaded in the booting process? O . Database O b.Programming…
A: Booting: The process of starting a computer is referred as booting. Booting is of two types: Cold…
Q: 5. Write a script to add new user to a specific group (Exist and new group) and give an initial…
A: We need to write shell script to add a user with password. ***As per guidelines, only 1st question…
Q: if(firstpassword==secondpassword){return true; } else{ alert("password must be samel"); return…
A: In the given program segment, if statement compares first password and second password for equality.…
Q: 2. Create a new user named user 1 and assign a password to it. Also show how to disable and delete…
A: ADDING NEW USER ONE
Q: 2. Create a new user named (Your_Name) and assign a password (Your Roll_No.) to it. Also show how to…
A: Disclaimer: Since you haven't specified the operating system we are answering the question for…
Q: system Student 1. Login 2. Verify login 3. Wrong password 4.Borrow book- Alternative if (The book…
A: Answer : Explanation of first sequence diagram : Student first login the system by entering the…
Q: How many account records will be created by the given code? Account a = new Account(Name='Acme');…
A: According to the given code: We have to find out how many account records will created by mention…
Q: How many account records will be created by the given code? Account a = new Account(Name='Acme');…
A: The answer is
Q: Create a program that the user can log in and validate the credentials either valid or invalid…
A: I have designed a login form in Visual Studio 2015 using Windows Form Application with C# code,…
Q: Users can request certificates that aren't configured for autoenrollment by using the Certificates…
A: The given statement is true i.e. By using the snap-in Certificates, users can request certificates…
Q: Which of the following is not an authentication procedure for verifying the user credentials in the…
A: I have provided answer in step2
Q: The mode portion of the command format is made up of the following parts: Category of users you…
A: The mode portion of the command format is made up of the following parts: Category of users you are…
Q: def check_password_exclusive (passwd: str) -> bool: """An exclusive strong password has a length…
A: Python Code to form a strong password
Q: In which of the following authentication methods the user needs to enter a registered username and…
A: Username/Password Authentication Method : Every time you've signed up for a website, you've likely…
Q: Some files cannot be deleted using rm command because of the permissions associated with
A: Please find the answer below :
Q: The file inform has a numerical permission of 754. Consider the following questions: A) Who has…
A: If we used chmod 754 on a file it will have the following effect. User: the user will have all the…
Q: create a simple c++ code that seeks for users log in credentials (email and password) using try…
A: INTRODUCTION : A login page is a web page or an entry page to a website that requires user…
Q: A security group Users has Read Only NFTS Permissions access to a file. The same group has Full…
A: A security group Users has Read only NFTS Permission access to a file. The same group has Full…
Q: Based on your understanding which of the following statements describes the brute-forcible login…
A: Based on your understanding which of the following statements describes the brute-forcible login…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- ???????? 2: Take the username and password from a user and check the validity of the password using the following rules: 1. Password must contain at least 2 digits, at least one uppercase letter, at least one lowercase letter, and at least one of the special characters (*,_,%,$,#,@) in it. If one or more of these are missing, show which ones are missing. 2. The password must not contain the username in it. If it does, the password will be invalid. 3. The password must have a length of 8 or more. Sample Input 1: Username: IzukuMidoriya Password: izukuMidoriya24# Output1: Invalid Password: Password cannot contain username Sample Input 2: Username: IzukuMidoriya Password: Iamhere@12 Output2: Valid password Sample Input 3: Username: IzukuMidoriya Password: Ia4%Lp Output3: Invalid Password: Password too short Sample Input 4: Username: IzukuMidoriya Password: izuku@Midoriya24# Output4: Valid Password Sample Input 5: Username: IzukuMidoriya Password: Ia4%sahdvckgjp…make a code for this using c++ [A] – Accounts Registration //use function Account No. 0 Enter Username: nono Enter Password: 1234 Do you want to register another account? [Y]-yes [N]-no If yes account number will be 1 Account No. 1 Enter Username: nena Enter Password: 1234 Do you want to register another account? [Y]-yes [N]-no If no go back to homepage Account number is automatic starting from 0 Accounts must be directly added to the account list [B] – Login Enter account number: Enter username: Enter password: 3 Trial only after 3 trial go back to Homepage Username and password matched go to MENU [C] – Account List Account Number Username Password 0 nono 1234Select the best answers. The following are all cmdlet/alias/function for viewing the help files of cmdlets, except: Group of answer choices MAN Get-Help Help All of the above
- 8.18 (Regular Expression: Password Format Validator) Search online for secure password recommendations, then research existing regular expressions that validate secure passwords. Two examples of password requirements are: Passwords must contain at least five words, each separated by a hyphen, a space, a period, a comma or an underscore. Passwords must have a minimum of 8 characters and contain at least one each from uppercase characters, lowercase characters, digits and punctuation characters (such as characters in '!@#$%<^>&*?'). Write regular expressions for each of the two requirements above, then use them to test sample passwords.Complete the following function according to its docstring. def check_password_exclusive(passwd: str) -> bool: """ An exclusive strong password has a length greater than or equal to 6, and contains ONLY letters and numbers. Return True if and only if passwd is considered an exclusive strong password. >>> check_password_exclusive('I<3csc108!') False >>> check_password_exclusive('time2sleep4me') True """Users with Print permission can view and manage the print jobs of other users. True False
- An algorithm that validates username and pass- word. Here’s what the algorithm can do:(10pts) •The user has 3 chances, if username and password matches, display logged in, else, display account locked. • Assume that there is a list of username and their corresponding password. Each time the user enters a wrong credential, it should display what goes wrong(i.e. User does not exist, or Incorrect password)User Nurmeric notation, set the following permission on urname_file2 User:read ,write execute Group:write Other: read and writeInstructions: Circle T if the statement is true, F if the statement is false, or write the best answer in the space provided. A ____________can be added to a file or an e-mail message to verify the identity of the sender and guarantee the file or message has not been changed.
- Granting permissions one user at a time, how many times would you have to set Allow permissions for a user/folder combination (e.g. user1 for the Common folder, user2 for the same folder, etc.)? How did you calculate this? (Note that you do not have to count situations where you are not granting access, only when you are granting access.) Write youAccess Control List both the permission bits and octal notation for a file where: * The owner can read, edit, and execute the file * Users who are members of the owning group can read and execute the file * Other users can read and execute the file --- describe in letters. upvote for useful answer. Pls do not copy useless things here. Thanks for helpCreate a simple login form using Java Swing Create an RMI application with GUI that will allow users to log in and log out. Please store the credentials in a JSON file (username and password). The program will use this file to verify the user and allow them access to the application.

