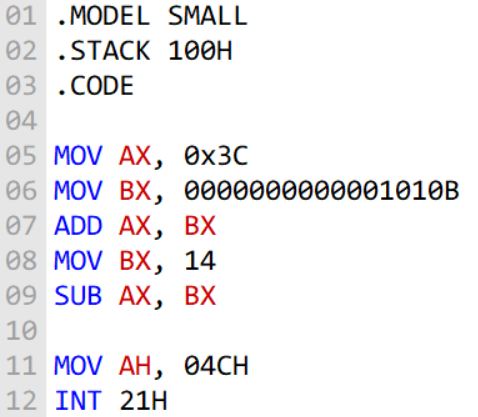
. MODEL SMALL - STACK 100H - CODE MOV AX, O×3C MOV BX
Q: Make a C program that checks if an alphabet or character entered is it a vowel or not. Example, if…
A: Given: C program that checks if an alphabet or character entered is it a vowel or not.
Q: Given a partial MIPS assembly code where only two instructions are explicitly given and the location…
A: According to the information given:- We have to follow the instruction to translate MIPS instruction…
Q: i) Write a Java program to find the number of loops in the array given below. A loop is defined as a…
A: Required:- ii) Write a Java program to find the number of loops in the array given below. A loop is…
Q: Which network topologies do you believe are conceivable, and which ones do you advocate as being the…
A: Introduction: A Network Topology is the configuration of computer systems or network devices about…
Q: 44. Suppose registers 'A' and 'B' contain 50H and 40H respectively. After instruction MOV A, B, what…
A: MOV INSTRUCTION: The MOV instruction are used to move data bytes between the two operands.In…
Q: What are the measures that can be taken by individuals and organizations to minimize the invasion of…
A: 1. Check social privacy settings If you have social accounts, those networks have a lot of…
Q: Proofs: Construct proofs to show that the following symbolic arguments are valid. Commas mark the…
A: Given, W → ∼U, W ∨ X, ∼T → (Z • U), X → ∼Z ∴ T This means, Premises : W → ∼U W ∨ X ∼T → (Z • U) X →…
Q: Write a Java Program to take 3 integers(a.b.c) from the user, print "Great Number" if one of b or c…
A: Required:- Write a Java Program to take 3 integers(a,b,c) from the user, print "Great Number" if one…
Q: Written In Python The amount of time students spent studying for an test is exponentially…
A: According to the information given:- We have to write python code by following the instruction and…
Q: Write the Student class so that the given code provides the expected output. 1. Create Student class…
A: The program is written in Python. Check the program screenshot for the correct indentation. Please…
Q: Assume register $t0 and $t1 contains 0X020A007E and 0XFFFFFFF0 respectively. The content of $t0…
A: The solution to the given question is: According to the information given: We have to find after…
Q: How is data sent from a device that only allows direct access to a device that only allows…
A: Introduction: As defined in your question, sequential access is a technique for retrieving data from…
Q: 20 7 15 10 12 27 30 10 22 25 12 15 17 What will the tree look like after we delete 25?
A: Given tree is B+ tree which is a type of tree data structures. In this tree, all the data values are…
Q: When it comes to routing, what precisely is it, and how does it work? In this post, we wil look at…
A: Introduction: Routing is selecting a path for traffic inside a network or between or across…
Q: i. Consider the free memory layout shown below (the blocks are ordered from top to bottom). Draw to…
A:
Q: where: a=2; and b=3; c1='A'; c2='a'; printf("The NUMERIC VALUE of %c is…
A: Ascii value of A=65 Ascii valued of a=97
Q: Write a Java Program to take 3 integers(a.b.c) from the user., print "Great Number" if one of b or c…
A: Java program: Java is a class based, high level object oriented programming language. Java is…
Q: Explain how a cloud storage program varies from traditional client storage software in terms of…
A: INTRODUCTION: Cloud storage enables users to exchange and access files remotely without requiring…
Q: (20 points) Consider the following function: 100(1 – 0.01x²)² + 0.02.a² (1 – x²)² + 0.1x² y(x) =…
A: % Script Description:Subplots with different plot schemes% Name :% Date…
Q: Describe the model that comes to mind when you hear the phrase "Verification and Validation Model."
A: Verification and Validation Model is also known as V-model.
Q: Computer Science A network uses 23 bits of network id and 3 bits of sub-net it. How many actual…
A: According to the information given:- we have to find the actual host can be on sub-net.
Q: Utilize a request for proposal to collect information on hardware and system software, as wel as to…
A: Introduction: A computer system is comprised of two distinct components hardware and software.…
Q: What is the function of cryptology in the field of information security?
A: Cryptography is a sort of data security approach that utilization codes to protect corporate…
Q: What are the advantages and disadvantages of caching write operations on a disk?
A: Below are the advantages and disadvantages of caching write operations on a disk
Q: How can i find the number of '!' chars in the user entered string. Programming language: JAVA
A: Step-1: Start Step-2: Declare a variable str and take input from user Step-3: Declare a variable…
Q: Can you explain why narrowing or widening conversions are never safe, or why they are safe in…
A: EXPLANATION: Widening conversions: The smaller variable is assigned to the more significant…
Q: Which network topologies do you believe are conceivable, and which ones do you advocate as being the…
A: Introduction: It's the most acceptable form of advocacy when people believe they can and want to…
Q: We would like to find the minimum number of steps required to get 0 from any number, when you can…
A: The code is given below.
Q: Discuss any ERP benefits when deciding to adopt an ERP system.
A: The solution to the given problem is below.
Q: Given the below Binary Search Tree, Answer the following questions: 100 70 212 22 99 166 300 63 150…
A: Predecessor: When you traverse the binary search tree using inorder traversal the node just…
Q: Which network topologies do you believe are conceivable, and which rou advocate as being the most…
A: Below network topologies do you believe are conceivable
Q: A 2 Mbyte memory system based on DRAM Model (256Kx8), to control the sequence operation of DRAM…
A: A 2 Mbyte memory system based on DRAM Model (256Kx8), to control the sequence operation of DRAM…
Q: Take a look at the advantages and disadvantages of open-source operating systems.
A: What is opensource operating system? The phrase "open source" refers to computer software or…
Q: public class Flowers public static void main(String[] args) { // Step 3: Create an array list of…
A: Sample output Screen shot:
Q: Particularly in the case of magnetized drives, some databases only utilise sectors in the outer…
A: Introduction: A database is a data structure for storing and organizing data. The majority of…
Q: I'm not sure what the point of routing is or how it works. Separate and contrast the differences…
A: In networking, routing is a process of moving data packet from source to destination. Routing is…
Q: Explain how a cloud storage program varies from traditional client storage software in terms of…
A: Introduction: Traditional storage is a kind of storage in which data is stored on local physical…
Q: L#14 Find the Factorial of any number 'n' Example : Factorial of 5 = 1x 2 x 3 x 4 x5 = 120 Sample…
A: Factorials are products of every whole number from 1 to n.
Q: Discuss a problem with concurrent processing in a computer operating system.
A: Answer :
Q: A machine cycle is a closed-loop process that has four parts. Describe why the machine cycle is so…
A: Introduction: Cycle of the machine The actions followed by the computer processor in response to…
Q: What elements should you take into consideration while weighing the advantages and disadvantages of…
A: Introduction: A data processing organization technique that uses a central computer in conjunction…
Q: I'm not sure what the Cybercrime Conceptual Framework is, or how it works. You should add references…
A: Introduction: Cyberspace, according to the internet theorists, allows for near-instant connections…
Q: 11 def methodA (self): х, у %3D 0,, 0 y = y + self.y x = self.y + 2 + self.temp 12 13 14 15 self.sum…
A: The answer is given below.
Q: Please offer an example of a computer-based system, as well as a summary of the features of that…
A: Introduction: Software, hardware, people, a database, documentation, and procedures are the…
Q: ay only tables within the system catalog that are of the type BASE TABLE. Display only the following…
A: MySQL It is a relational database management system based on the Structured Query Language, which…
Q: What is the code that causes the LCD text to blink three times only?
A: Answer is given below .
Q: An incident response (R) is a collection of operations that are carried out in the course of a…
A: An incident response (IR) is a collection of operations that are carried out in the course of a…
Q: When comparing and contrasting the characteristics of both, as well as the circumstances in which…
A: answer is
Q: sume register $t0 and $t1 contains 0×020A007E and 0XFFFFFFF0 respectively. The content of $t0 after…
A: the solution is an given below :
Q: Write a Java Program to take 3 integens from the user, one of them is small, one is medium and one…
A: Write a Java Program to take 3 integers from the user, one of them is small, one is medium and one…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- model small .stack .data string db "ODD EVEN$" string2 db "Input:$" .code org 100h start: main proc mov ax,03 int 10h mov ax,@data mov ds,ax mov ah,9 lea dx,string int 21h call nlcr mov ah,9 lea dx,string2 int 21h mov ah,1 int 21h mov dl,al mov ah,2 add dl,20h int 21h mov cx,25 y: mov ah,2 dec dl int 21h loop y mov ah,4ch int 21h main endp nlcr proc mov ah,2 mov dl,13 int 21h mov dl,10 int 21h ret nlcr endp end start What is the Output screenshotsWrite the code in assebly language code that can be read in LC3 simulators! .ORIG x3000 ; Set up the user stack: LD R6, STKBASE ; Sets up the stack by loading the base address into R6 ; Prompt for the first string: LEA R0, PRMPT1 ; Loads the address of PRMPT1 into R0 PUTS ; Call GETS to get first string: LEA R0, STRNG1 ; Loads the address of STRNG1 ADD R6, R6, #-1 ; Push the address to store the string at STR R0, R6, #0 JSR GETSP ; Call GETSP ADD R6, R6, #2 ; Clean up (pop parameter & return value) ; Prompt for second string: LEA R0, PRMPT2 ; Loads the address of PRMPT2 PUTS ; Call GETS to get second string: LEA R0, STRNG2 ; Loads the address of STRNG2 ADD R6, R6, #-1 ; Push the second address to store the string at STR R0, R6, #0 JSR GETSP ; Call GETSP ADD R6, R6, #2 ; Clean up (pop parameter & return value) ; Output both strings: LEA R0, OUT1 ; First string... PUTS LEA R0, STRNG1 PUTSP LD R0, LF ;…Complete the ARM Legv8 implementation of Main given C code. Do not implement return 0; in main(). Use Ldur,Stur,Stack if necessary, do not use MOV,LDR. X stored in X19,y in X20,w in X21,z in X22 int main() { int x, y; w = Sum(x, y); z = Dif(y, x); return 0; // Do not implement } LEGv8 code: Main: // Type your code here. B End // Procedure Sum (Do not modify)Sum: ADD X2, X0, X1 BR X30 // Procedure Dif (Do not modify)Dif: SUB X2, X0, X1 BR X30 End:
- This is a program to print fibonacci series in assembly. Can you explain it line by line? .MODEL SMALL .STACK 100 .DATANUM1 DB 01HNUM2 DB 01HL DB 00HVAL1 DB 00HVAL2 DB 00HNUM DB 0DH,0AH,'$' .CODE MAIN PROCMOV AX,@DATAMOV DS,AX MOV AH,01HINT 21HMOV CL,ALSUB CL,30HSUB CL,2 MOV AH,02HMOV DL,NUM1ADD DL,30HINT 21H MOV AH,09HLEA DX,NUMINT 21H MOV AH,02HMOV DL,NUM2ADD DL,30HINT 21H MOV AH,09HLEA DX,NUMINT 21H DISP:MOV BL,NUM1ADD BL,NUM2 MOV AH,00HMOV AL,BLMOV L,CLMOV CL,10DIV CLMOV CL,L MOV VAL1,ALMOV VAL2,AH MOV DL,VAL1ADD DL,30HMOV AH,02HINT 21H MOV DL,VAL2ADD DL,30HMOV AH,02HINT 21H MOV DL,NUM2MOV NUM1,DLMOV NUM2,BL MOV AH,09HLEA DX,NUMINT 21H LOOP DISP MOV AH,4CHINT 21H MAIN ENDPEND MAINUsing the attached program (AirportCombos.cpp), create a list of strings to process and place on a STL STACK container. The provided code is meant to be generic. Using the provided 3 char airport codes, create a 6 character string that is the origin & destination city pair. Create all the possible origin/destinations possible combinations from the airport codes provided. Load the origin/destination string onto a stack for processing. Do not load same/same values, such as DALDAL, or LAXLAX. See comments in the program from more details. After loading the values, Create a loop to display all the values in the container. This loop should inherently remove items as they are displayed. Deliverable is a working CPP program.Write a Java program to implement a stack by using array. o Define a Stack interface.o Define an ArrayStack class.o Define a Test class to test all methods first code package ArrayStack; public class ArrayStack <E> implements stack<E> { public static final int CAPACITY=1000; private E[] data; private int t = -1; public ArrayStack() { data = (E[]) new Object[CAPACITY]; } public ArrayStack(int capacity) { data = (E[]) new Object[capacity]; } public int size() { return (t + 1); } public boolean isEmpty() { return (t == -1); } public void push(E e) throws IllegalStateException{ if (size() == data.length)throw new IllegalStateException(); data[++t]=e; } public E top() { if(isEmpty( )) return null; return data[t]; } public E pop() { if( isEmpty( )) return null; E answer = data[t]; data[t] = null; t--; return answer; } } secound code package ArrayStack; public interface stack<E> { int size(); boolean isEmpty(); void push(E e); E…
- Run a programme to create a linked stack in order to verify that the following symbol pairs are balanced in a Pascal programme. The only input for the software is the name of the source Pascal programme.Symbols: start, stop, (), [], and.(i) Output mistakes resulting from symbol mismatches.(ii) Change the software to fix the mistakes.Consider the infix expression exp = ( ( 8 / 2 ) + 3 ) * 1 to solve the questions given below: a: Trace the process of converting the infix expression into It's postfix form. b: Evaluate the postfix expression you obtained in part a. *************************************************************************************** Note: Solve the question in your notebook. Draw two tables as shown below. Scan or take a picture, upload the file. a: Next token Action Content of stack Postfix expression b: Next token Action Content of stackdiscuss how to creat a non-executable stack and disuss the stack's exploitable weaknesses
- Write a program to implement a Stack using array. In order to implement the stack, programfor following stack operations has to be written: • void push(int): to insert data onto the stack.• Int pop(): to remove and return the last inserted element from the stack.• Int top(): Returns the last inserted element without removing it.• int Size(): Returns the number of elements stored in the stack.• int IsEmptyStack(): Indicates whether any elements are stored in the stack or not.• int IsFullStack(): Indicates whether the stack is full or not.The language a^n b^n c^n is not a CFL. Give a pushdown automaton with 2 stacks that accepts the language. (This shows that 2 stack PDAs are more powerful than a single stack PDA.)Your answer in table format must include the headings - state,stack 1,stack 2, new state, stack1 op, stack 2 op.ORIG x3000 ; Set up the user stack: LD R6, STKBASE ; Sets up the stack by loading the base address into R6 ; Prompt for the first string: LEA R0, PRMPT1 ; Loads the address of PRMPT1 into R0 PUTS ; Call GETS to get first string: LEA R0, STRNG1 ; Loads the address of STRNG1 ADD R6, R6, #-1 ; Push the address to store the string at STR R0, R6, #0 JSR GETSP ; Call GETSP ADD R6, R6, #2 ; Clean up (pop parameter & return value) ; Prompt for second string: LEA R0, PRMPT2 ; Loads the address of PRMPT2 PUTS ; Call GETS to get second string: LEA R0, STRNG2 ; Loads the address of STRNG2 ADD R6, R6, #-1 ; Push the second address to store the string at STR R0, R6, #0 JSR GETSP ; Call GETSP ADD R6, R6, #2 ; Clean up (pop parameter & return value) ; Output both strings: LEA R0, OUT1 ; First string... PUTS LEA R0, STRNG1 PUTSP LD R0, LF ; Print a linefeed OUT ; Write character to console (TRAP x21) LEA R0, OUT2 ;…











