MOV R1, #0xF3 MOV RO, #0x00 LOOP LSRS R1, R1, #0x01 ADC RO, RO, #0x00 R1, #0x00 LOOP END CMP BNE The value of RO after iteration 1: The value of RO after iteration 2: The value of RO after iteration 3: The value of RO after iteration 4: The value of RO after iteration 5:
Q: Private cloud services: what's different? What's best for the company? Be yourself.
A: What is services: Services refer to a set of operations or tasks that are performed to fulfill a…
Q: In order to demonstrate how this component of information security operates, please provide some…
A: Information security is a broad and multifaceted discipline that involves many components working…
Q: Which network enables serverless resource and peripheral exchange between a small number of PCs?…
A: The network that enables serverless resource and peripheral exchange between a small number of PCs…
Q: WebScarab was changed to OWASP Zed Attack Proxy (ZAP). How is it used when checking authenticity?…
A: OWASP Zed Attack Proxy (ZAP) is a popular open-source web application security testing tool that…
Q: As a result, modelling of business processes should extend beyond IT solutions. modelling of logical…
A: Business process modelling is an essential activity in the field of business analysis. It involves…
Q: ased" mean when refe
A: A batch operating system is a sort of operating system that handles and executes numerous jobs,…
Q: Please provide an explanation, using your own words, as to why "expandability" is such a crucial…
A: The world we live in today is increasingly reliant on technology, and gadgets have become an…
Q: To begin, let's discuss what the concept of virtualization entails. Then, we'll disassemble it into…
A: Virtualization is a concept in computer science that involves creating virtual versions or…
Q: Acquiring a comprehensive understanding of the concept of challenge-response authentication is…
A: Challenge-response authentication, often known as CRA, is used to verify a user's identity before…
Q: What exactly does it mean to have a tunnel going in both directions at the same time? Why is it…
A: What is network: A network is a group of connected devices that can share data and resources.…
Q: Cybercrime: how common is it?
A: 1) Cybercrime is a type of criminal activity that is carried out using the internet or other digital…
Q: Why is Python a good choice for a coin that can be used in the cloud? When it comes to cloud…
A: Python is a high-level programming language that has gained immense popularity in the field of cloud…
Q: Determine the point at which interpolation can provide a means for function estimation. Multiple…
A: The question 1 asks at which point interpolation can provide a means for function estimation, and…
Q: Explore data retrieval options for social media?
A: Data retrieval in social midway refers to accessing and extract data from various social media…
Q: How are the requirements of a system different from those of a user, and what kind of relationship…
A: Given, How are the requirements of a system different from those of a user, and what kind of…
Q: How many bits, in terms of computer architecture, make up a Nibble?
A: Information is represented in binary form in the fields of computer architecture and digital…
Q: In what specific ways might CPU Scheduling contribute to the overall performance improvement of an…
A: The answer is given below step.
Q: What is the key difference between having "many threads" running concurrently and having "many…
A: Concurrency : Concurrency is an important aspect of modern computing, allowing multiple tasks to be…
Q: How can you trust internet information?
A: In today's digital era, we have easy access to vast amounts of information thanks to the internet.…
Q: What is it about computer science that appeals to people from all ages and backgrounds? The…
A: Computer science is a field that has gained immense popularity in recent years, attracting people…
Q: What kinds of things do people who study computers perform with compilers?
A: Compilers are essential tools for software development and are used to create a wide range of…
Q: Wireless networks are in high demand in developing nations. Wireless networks are increasingly…
A: Wireless networks are in high demand in developing nations due to the ease and cost-effectiveness…
Q: Why is Python a cloud computing cryptocurrency? How is Python better for cloud computing than other…
A: Python is a popular high-level programming language that is widely used in many fields including…
Q: our computer is insulated from potential risks that might emanate from the rest of the world as a…
A: In the field of computer science, network security is of paramount importance to protect computer…
Q: Determine the appropriate value for the decision parameter p to use in the Bresenham's circle…
A: Bresenham's circle drawing technique is a popular algorithm used to draw circles efficiently on a…
Q: How many ways do computer networks address?
A: 1. MAC Address: A MAC (Media Access Control) address is a unique identifier assigned to network…
Q: What happens to Data Definition Language definitions? How may this be done differently? How can I…
A: Data Definition Language (DDL) information are a subset of prepared Query words (SQL) used to create…
Q: Kindly explain to me why it is a good idea to make use of the software that is already installed on…
A: What is an OS: An operating system (OS) is software that manages computer hardware and provides…
Q: Investigate if the use of software to manage projects will help you save expenses.
A: Project management is used to plan , organize and allocate the resource for the managing project ,…
Q: You should start by making a list of the problems you'll face while building the framework. Then,…
A: What is computing: Computing refers to the use of computer technology for processing, managing, and…
Q: Here are some examples of versions, releases, and baselines of software.
A: In the world of software development, different terminologies are used to refer to specific…
Q: Wireless networks have a smaller capacity, which contributes to their slower speed compared to wired…
A: The answer is given below step.
Q: Is there any kind of link or connection between this relationship and the way databases are…
A: 1) Databases are organized collections of data that are designed to be easily accessed, managed, and…
Q: Can internet research discern reality from fiction?
A: The Internet is a global network of interconnected computers and servers that allows for the…
Q: Describe the procedure that is used to build software using an agile methodology. I would appreciate…
A: Agile software development Agile software development is the methodology which is best known for…
Q: Which applications are most suited to make use of the SSH protocol?
A: The SSH protocol, or Secure Shell protocol, provides a secure and encrypted channel between two…
Q: Can you apply the philosophers' dilemma to computer science?
A: What is computer: A computer is an electronic device that can accept input, process data, and…
Q: 3 in duodenary (base 12) is to be added to C10 in tre undinary (base 11). What is the difference in…
A: The answer is
Q: Please don't leave us hanging; instead, supply us with a detailed graphic that explains how each…
A: Operating systems (OS) are the backbone of any central giving out unit system, responsible for…
Q: List all required equipment for a distributed system.
A: Using distribution middleware to link a group of autonomous computers forms a distributed system.…
Q: What separates Linux clones from UNIX processes and threads?
A: The process and the thread architectures of the Linux and the UNIX are the two widely used…
Q: Online identity concealment affects traffic.
A: Online identity concealment, also known as online anonymity or privacy, is the ability to hide one's…
Q: When trying to find a solution, you should give serious attention to employing both the…
A: The answer is given below step.
Q: Is anything wrong
A: In this conversation, we have discussed various topics related to computer science and programming.…
Q: Could you please comment on the reasons why it is very necessary for systems analysts to always have…
A: User requirements documents in the system analysis are comprehensive documents that capture the…
Q: How can scalable shared memory multiprocessors avoid coherence issues? What's bad?
A: 1) Scalable shared memory multiprocessors are computer systems that consist of multiple processors…
Q: Using the C programming language, create a simple automated teller machine.
A: Here, I will write a simple ATM machine program in the C programming language. The answer includes…
Q: an you provide an explanation of the concept of a challenge-and-response authentication mechanism…
A: In today's digital age, authentication mechanisms have become a crucial aspect of cybersecurity. A…
Q: Where, specifically, do these two concepts vary from one another most substantially with regard to…
A: Computer Architecture and Computer Organisation are two fundamental concepts in computer science.…
Q: Should we have a discussion about how crucial it is for companies to create backups of their data…
A: Certainly! It is crucial for companies to create backups of their data, and cloud storage offers…
Computer Science
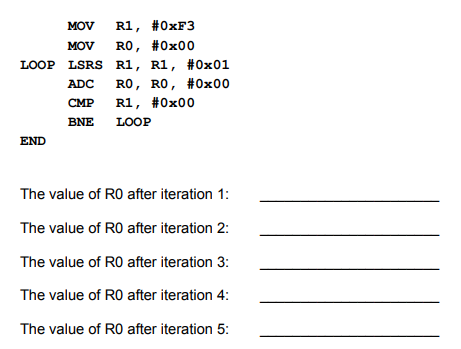
The script below demonstrates a very basic loop structure. Indicate the value of R1 after 5 iterations of the loop. (Given the very first line of code, you can assume R1 starts out as 0x00)
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Please run this on linux, compile and look at the placement for row "Tangent". Match the numbers below tangent and make sure all the other row numbers are lining up with the other headings main.c #include <stdio.h>#include <math.h> #define M_PI 3.14159265358979323846 /** * Given a incrementVal value, this function will print a table of trigonometric values * from 0 to 360, in increments of the incrementVal value. * For example, if the incrementVal value is 90, the table will print values for 0, 90, 180, 270 and 360. * incrementVal - the degree value to use for the increment*/void displayTriTab(int incrementVal) { //Display the header for the table printf("\n\t--- TRIGONOMETRIC TABLE ---\n\n"); // Display the column headings for the table printf("%3s%10s%10s%10s%10s\n", "Degrees", "Radians", "sine", "cosine", "tangent"); printf("%3s%10s%10s%10s%10s\n", "-------", "-------", "------", "-------", "-------"); //Declare variables for radians, sine cosine,…You have been provided with a QTCreator project called Project12 _ Student. Open the project in QTCreator and make the necessary changes to the main.cpp and infostation.cpp / h files. The class InfoStation contains 3 public methods namely : float getTemp ( ) ; - Returns a random temperature between 1 and 100 ( In float format ) float getHour ( ) ; - Returns a random hour between 1 and 24 ( In float format ) string getDay ( ) ; - Returns a random day between 1 and 10 ( In string format ) Using the class InfoStation fill the provided multidimensional array named WData[10][4] with values in the main function. The first 3 columns in WData should contain a temperature a hour and a day generated using the InfoStation class. Column 1 - temperature retrieved using getTemp ( ) from the InfoStation class. Column 2 - hour retrieved using getHour ( ) from the InfoStation class. Column 3 - day retrieved using getDay ( ) from the InfoStation class. Column 4 - no value at this stage will be…You have been provided with a QTCreator project called Project12 _ Student. Open the project in QTCreator and make the necessary changes to the main.cpp and infostation.cpp / h files. The class InfoStation contains 3 public methods namely : float getTemp ( ) ; - Returns a random temperature between 1 and 100 ( In float format ) float getHour ( ) ; - Returns a random hour between 1 and 24 ( In float format ) string getDay ( ) ; - Returns a random day between 1 and 10 ( In string format ) Using the class InfoStation fill the provided multidimensional array named WData[10][4] with values in the main function. The first 3 columns in WData should contain a temperature a hour and a day generated using the InfoStation class. Column 1 - temperature retrieved using getTemp ( ) from the InfoStation class. Column 2 - hour retrieved using getHour ( ) from the InfoStation class. Column 3 - day retrieved using getDay ( ) from the InfoStation class. Column 4 - no value at this stage will be…
- The FKGLF is: 0.39(totalWords/totalSentences) + 11.8(totalSyllables/totalWords) - 15.59Using the FKGLF and your knowledge of how to input and output text files with Java, write an application that will: Take in a text file (anyText.txt), Correct the spelling then save to another file (anyTextCorrected.txt), Calculate the grade level. Outputs. Your solution needs to return: the number of words in the text, the number of spelling errors corrected with the misspelled words listed, the number of sentences in the text, the number of syllables in the text, and the Flesch-Kincaid Grade Level. One assumption you can make is the accuracy of SpellChecker(). You have access to the Java method SpellChecker that takes in a string, assumed to be a word, and returns a correctly spelled word. (Note: If the word returned is different than the word input, then there was a spelling error.) One Constraint: This program requires two classes: GradeLevel and GradeLevelTest. GradeLevel will be the…#4. Task Programming Language and Technologies▪ C# Programming Language.▪ Visual Studio 2019. Build a method called Encrypt to receive a string and return another string.The method will be a static.Build a method called Decrypt to return original string.The encryption method will be a very simple one: to encrypt add 1 to eachcharacter and to decrypt subtract 1 to each character.Note: we do not need to create any object of type Encrypter..Each of the following files in the Chapter.07 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugSeven1.cs will become FixedDebugSeven1.cs. a. DebugSeven1.cs b. DebugSeven2.cs c. DebugSeven3.cs d. DebugSeven4.cs
- This is the code that needs to be updated: .ORIG x3000 LD R0, NUM LD R1, DEN JSR GCD ADD R4, R1, #0 ADD R1, R2, #0 JSR DIVIDE ST R2, NUM ADD R0, R4, #0 JSR DIVIDE ST R2, DEN HALT; you can try other values for NUM and DEN by replacing these values in the simulatorNUM .FILL #10 DEN .FILL #3 ; Divide R0 by R1, putting quotient in R2 and remainder in R3DIVIDE ; Euclid's algorithm for GCD of R0 and R1, result in R2GCD .ENDUsing C# create a console app doing the following Write a method that takes two integers and displays their sum. Write a method that takes five doubles and returns their average. Write a method that returns the sum of two randomly generated integers. Write a method that takes three integers and returns true if their sum is divisible by 3, false otherwise. Write a method that takes two strings and displays the string that has fewer characters. Write a method that takes an array of doubles and returns the largest value in the array. Write a method that generates and returns an array of fifty integer values. Write a method that takes two bool variables and returns true if they have the same value, false otherwise. Write a method that takes an int and a double and returns their product. Write a method that takes a two-dimensional array of integers and returns the average of the entries.public setUpTrip(double, double): void Car's state is set to hold the speed of travel and distance to travel at that speed Precondition: none Postcondition: Car's state holds information on distance to travel and speed to travel Parameters: Average Speed to be driven, Distance to drive Develop and use an algorithm that calculates the amount of fuel used and the actual distance driven in the drive() method. The algorithm must use a formula that gives proportionately poorer mileage when the Car is driven faster or slower than its optimal speed. When a new Car object is instantiated, it is initialized with an optimal speed variable. Your fuel usage algorithm should set limits on how poor of MPG your car will get. You may add other methods and fields as needed. When a new Car object is created, the car’s odometer is set to a random number between 0.0 and 5.99, the car’s trip odometer is set to 0.0, its best fuel economy (MPG) is set to a random number between 15.0 and 54.99, its…
- (In Java) Mathletes Game! With the introduction of loops, we now know enough about programming to begincreating simple games. Our first game (sponsored by the KSU College of Science and Mathematics)will test your ability to solve multiplication problems.Your game will first ask the player if they want to play on easy or hard mode. Save their response inan appropriate variable (you will reference it later). Then, you will randomly generate two numbersand display them to the player in the form of a multiplication problem. The possible numbers willrange between -255 and 255.You will ask the player to solve the equation. You will keep creating multiplication questions until theplayer wins or loses.Based on whether the player chose “hard” or “easy” mode, the game will play a little differently.Refer to the following rules for the difference:Easy Mode Hard ModePlayer only has to answer 5 questions Player has to answer 10 questionsPlayer can try again if they get a question wrong(up to two…Java Proram ASAP Please look closely at the circled parts in the failed test case. It says 1 out of 4 passed. Improve and adjust the program which is down below with the futher moddifications because it does not pass the test cases in Hypergrade. Please remove /n from the program and for test case 4 after this line: Please re-enter the file name or type QUIT to exit:\n quitENTER there needs to be nothing. Also, I do not need file quit is no found in the program. import java.io.*;import java.util.Scanner;public class ConvertText { public static void main(String[] args) throws Exception { Scanner sc = new Scanner(System.in); System.out.println("Please enter the file name or type QUIT to exit:"); while (true) { String input = sc.next(); if (input.toUpperCase().compareTo("QUIT") == 0) { break; } else { // Get the absolute path of the current directory String filePath = new…I having troubles running this C linux program. please use my code to fix any errors that need to be removed or added.If it needs sin() cos() tan() - Please adddisplayTriTab • Receive an integer called degrees that represents the number of degree for incrementation and return nothing. • Display the heading “--- TRIGONOMETRIC TABLE ---” center over the table •A blank line • Display the column headings as sown on the output. • A blank line. • Produce a table based from 0 to 360 degrees in increments based on the users input. • The table columns will be as follows: 1. Degrees ( Format: Right justified, no decimal places) 2. The radian value for the number of degrees in column 1 3. The sine value for the degrees in column 4. The cosine value for the degrees in column 5. The tangent value for the degrees in column 6. Tangent values for 90 and 270 will be infinity • The 360 degrees row will always be the last row even if the increment value entered would not [Bold] the code I do not…





