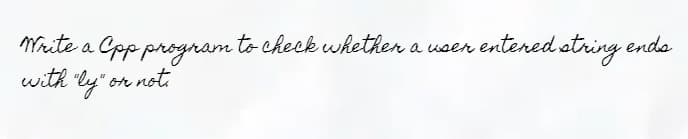
Mrite a Cpp program to check wkether a wsen entered otring endo with ly" on not
Q: Identify the task environment of 2 based on the following i)Fully/Partially Observable ii)Single or…
A: A fully observable environment is one where an agent sensor can perceive or acquire the complete…
Q: C. Refunds_697 REFUNDID ORDERID REFUNDDATE REFUNDAMOUNT 1 1 02-SEP-16 5 2 18-SEP-16 18 Refunds…
A: Given:
Q: Hardware is the phrase used to describe all of the input and output devices in a computer system.…
A: Computer hardware refers to all of the physical components of a computer, whether it's analogue or…
Q: Describe in your own words what is Fizzbuzz programming?
A: Given To know about the Fizzbuzz programming
Q: When it comes to communication, what is the protocol?
A: The answer of this question is as follows:
Q: 2. We learnt in class/Notes that A[x] → (Vx)A[x] is NOT a theorem if x indeed occurs free in A. Yet,…
A: The solution to the given question is:
Q: What exactly is a reverse proxy server, and why would you want to use one in your network…
A: Introduction : Server for Reverse Proxy : It manages traffic flowing from the external network or…
Q: In Pakistan, Google has opened a new office. There is an open position for you there. During the…
A: An integrated circuit, or microprocessor: The central processing unit of a computer does both logic…
Q: Explain why encrypting the passwords on the router is necessary, and write down the relevant command…
A: Introduction: When a person or device attempts to connect, it is asked for a password or network…
Q: What are the best practices for lowering the energy usage of computer devices?
A: Now a day every home or offices has a computer. To save the energy, you don't need the drastic…
Q: When it comes to processors, what's the difference between an Intel Celeron and a Pentium processor?
A: Introduction: I'll describe the difference between an Intel Celeron and a Pentium Processor in this…
Q: What is the definition of an entity? a person or thing that exists.
A: INTRODUCTION: Entity: The term "entity" refers to a physical object. It could be an individual, a…
Q: a) What is the meaning of the term "System Call"? What is the operating system's approach to this?
A: Required: a) What does the word "System Call" mean? How does the operating system handle this?…
Q: Discuss the future of artificial intelligence in light of its progress to this point.
A: Introduction: Artificial intelligence: It is changing the future of almost every sector and person…
Q: A string is given that contains digits only. Write a C++ function that takes a string as the…
A: Given: A string is given that contains digits only. Requirement: Write a C++ function that takes a…
Q: ain the weiler-atherton algorithm in the context of a polygon. Mention the technique in detail.
A: Explain the weiler-atherton algorithm in the context of a polygon. Mention the technique in detail.…
Q: What is the meaning and function of the central processing unit (CPU)? Explain your point of view!
A: Introduction: The central processing unit (CPU) directs the computer's execution of the many…
Q: What is the meaning and function of the central processing unit (CPU)? Explain your point of view!
A: Introduction: We must describe the significance and function of the CPU in response to the query.…
Q: Informal explanations of information system operations, as well as specific examples of how they are…
A: Introduction: For example, if you operate a firm that manufactures shoes and provides various other…
Q: John's barn has a fence consisting of N consecutive sections numbered from left to right from 1 to…
A: Program Explanation: The first input line contains the number T indicating the number of test cases.…
Q: In System Design, you should be able to identify four design models.
A: The answer of this question is as follows:
Q: If a GROUP BY clause is included in a SQL query, the characteristics that may be sought in the…
A: What is group by clause,? Grouping Result - ---> GROUP BY :- Basically, in the GROUP BY clause…
Q: A router, a firewall, a gateway, a modem, and a network adapter are all devices that are responsible…
A: What is Router: A Router is a device in a computer that moves data back and forward between the…
Q: In what ways are cloud computing and grid computing distinct from one another
A: In today's technologically advanced environment, cloud computing and grid computing are two…
Q: When there is a difference between a Copy Constructor and an Overloaded Assignment Operator, it is…
A: Introduction: Given that: The subject of the discussion is The Difference Between A Copy Constructor…
Q: What is the impact of a data leak on cloud security? What are some of the possible countermeasures?
A: Cloud data leak A data breach occurs when secure/confidential information is intentionally or…
Q: What is the significance of cybercrime, and what is the literature review on it?
A: Cybercrime : Cybercrime involves a computer, a network, or an organization. While most cybercrimes…
Q: A financial company hired a team to develop a new system that will help them improve their business.…
A: Correct Answer. tick a b and e
Q: What is the impact of a data leak on cloud security? What are some of the possible countermeasures?
A: Introduction: It's a collection of security measures for cloud-based infrastructure, apps, and data…
Q: Do you know what the difference is between a shallow copy and an in-depth сору?
A: Introduction: In computing, a shallow copy of an object is a bitwise duplicate in which a new object…
Q: What are the benefits of this file system against a sequential one?
A: Introduction: In a tiny amount of space, large quantity of information may be stored. Retrieve…
Q: A. What exactly is an antiviral program? B. As a user, you may have come across computers that have…
A: EXPLANATION: A. Antivirus Antivirus software, or a collection of software packages, identifies,…
Q: Discuss five security best practices for online applications.
A: Introduction: Here the security of the corporate stack, the software applications are the weakest…
Q: What Exactly Is a Mouse Cursor?
A: The Answer is in step2
Q: What is the fundamental building block for creating extremely vast networks?
A: Introduction: Building block : A building block is a collection of functionality that has been…
Q: LinkedList implementation 1. Create a linked list of type String Not Object and name it as…
A: The program for the above-given question is given below:
Q: When it comes to communication, what is the protocol?
A: Description in a formal way for digital message format and rules is known as communication protocol.
Q: Find out what each PC component's specs are.
A: Personal computer having the different components those are CPU, moniter, peripheral input and…
Q: 3. For the maze shown below, use graph theory to determine whether it is possible to get out from…
A: Introduction: The theory of the maze: The purpose and a choice of paths via the tunnel to the exit,…
Q: What are a genetic algorithm's primary operators?
A: Introduction: The genetic algorithms' primary operators are reproduction, crossover, and mutation.…
Q: What are the detrimental effects of video games on human health, and how is gaming linked to brain…
A: INTRODUCTION: The public is continuously concerned about the potential dangers of addiction to VGs,…
Q: What are the various tree trimming strategies (in data mining)? Explain everything in detail.
A: Introduction: In machine learning and data mining, tree pruning is a procedure that is linked to…
Q: Best effort is a feature of the Internet Protocol (IP) protocol. In terms of flow control, describe…
A: Services of IP protocol:The Internetwork Protocol (IP) provides a best effort network layer service…
Q: Explain why encrypting the passwords on the router is necessary, and write down the relevant command…
A: INTRODUCTION: We need to ascertain why encryption of passwords on routers is essential.Additionally,…
Q: 2. A network of cascaded inverters is shown in Figure 3-75. If a HIGH is applied to point A,…
A: 2. solution:
Q: List at least six disciplines that are considered to be foundational to the science of artificial…
A: Introduction: The disciplines that gave rise to AI are: Philosophy Logic/Mathematics Computation…
Q: Examine the many methods in which different businesses make use of information systems.
A: There are many types of information systems are available which are implemented in organization for…
Q: What exactly is multifactor authentication, and what are the advantages?
A: Multifactor Authentication: Multi-factor authentication is an electronic authentication procedure…
Q: Explain the weiler-Atherton algorithm in the context of a polygon. Give an example of the…
A: The wailer – Atherton method is a polygon clipping technique that is utilized in a variety of fields…
Q: HOW TO KNOW IF MY INPUT/ STUDENT ID IS VERIFIED AND NOT VERIFIED, IF NOT, ASK THE USER AGAIN TO…
A: Modified code: student_213 = {} # dictionary of student information print…
Step by step
Solved in 4 steps with 3 images

- (b) Prove partial correctness for the following while program. Note that you should clearly identify a loop invariant.a=x;y=1; while }(a>0){y∗=a;a−−;The precondition here isx≥0and postcondition isy=x!How many passes does the evaluation of infix expression algorithm makes through the input?a) Oneb) Twoc) Threed) FourDetermone whether the statement is true or flase. Prove directly from the definitions if its true, give a counter example if false. For all intergers a,b, and c if a|bc the a|b or a|c
- write C++ program to tead x and complute sin, cos , and tan of x .Design an algorithm that checks whether a point A having coordinates (xA, yA) is inside, on the boarder, or outside a square resulting from the intersection of four lines given by the equations:, , , and (as shown in the figure):asnwer a and b only.
- 2. Write a program to graph the following equation in the interval. The interval step size is 0.5. Calculate the values in main program. Write a function to print the output graph as follow. v = 75 * t * exp(-t); Sample output 0 10 20 30 40 -------------------------------------------- 0.0 * 0.5 * 1.0 * 1.5 * 2.0 * 2.5 * 3.0 * 3.5 * 4.0 * 4.5 * 5.0 * .........Karma dubike following. The integral part should.using c language and #include<stdio.h> must use loops only

