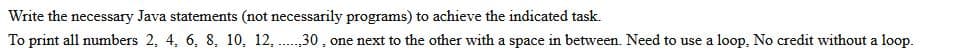
mts (not necessari 19. 12. 30
Q: When do you think it would be suitable to start using brouter on your network?
A: A router is a device that associates at least two packet switched networks or subnetworks. It serves…
Q: Is the issue with the computer's hardware or its software when you power it on for the first time…
A: Computer's hardware: Computer hardware consists of the physical components a computer system needs…
Q: It is important to determine the fundamental components that make up an information system. What…
A: Information system components: A system is the collection of interrelated components that produce…
Q: Explain in three points why the spiral model is preferable than the waterfall model. Describe how…
A: Introduction: The SDLC methodology really introduces spiral and waterfall models. A project is…
Q: 1. Finite Automata Let us consider the following -NFA defined over the alphabet >= {0,1}. 0,1 0,1…
A: Given ε-NFA contains, Set of states= {A, B, C} Set of input alphabets={0, 1} Initial state=A Final…
Q: Write the exact output that you expect to see on nt x=35, y=4, Z; = x*y; witch (z) { case 0: x=x+1;…
A: Lets see the solution.
Q: Are the terms World Wide Web and Internet interchangeable?
A: Please find the detailed answer in the following steps.
Q: Iterative-and-incremental and the waterfall approach have a lot of similarities, but how do they…
A: The waterfall model is one of the most common and straightforward models used in software…
Q: Give an explanation of what the GRANT declaration is capable of doing and how it influences the…
A: It is used to grant permissions to a specific user or role or to all users to conduct operations on…
Q: design a complete MIPS Processor(Datapath+Control Unit) for the following subset of MIPS…
A: We are able to illustrate the design of a single-cycle CPU for a subset of the MIPS commands. those…
Q: In addition to network-based firewalls, are there any others?
A: This question covers different types of firewalls outside network-based firewalls. Routers (without…
Q: What are the FOUR (4) benefits of using the Incremental Model as opposed to the Waterfall Model?
A: Definition: The first model in the software development life cycle was the waterfall model. The…
Q: Explain both the positives and the negatives associated with the various Wi-Fi security methods.
A: Given WIFI security. And know their pros and cons. Different WIFI security methods: No wires…
Q: answer the following questions: 1: A dictionary is an unordered collection of key-value pairs. True…
A: answer along with output screenshot is given
Q: When you switch on your computer, you are greeted with the whirring sound of the fans that are…
A: The system unit is part of the computer that houses the primary hardware devices to do critical…
Q: What are the characteristics of a computer's central processing units, and how may they be applied…
A: Introduction: All sorts of computer devices, including tablets, PCs, and laptops, include a central…
Q: Research memory manufacturers, and note which brands receive better ratings overall, and how…
A: Research memory manufacturers, and note which computer brands receive better ratings overall. Some…
Q: To better understand the distinction between ethics in engineering and ethics in computing, please…
A: Start: Ethics is a collection of moral rules that regulate an individual's or a group's conduct. The…
Q: What does a firewall do, and how can it benefit your company?
A: In answer to your query, A firewall is a security system that prohibits unauthorized access. It…
Q: How do you define the word "ethics"? Are there any instances when freedoms (negative rights) and…
A: Ethics: "involves systematizing, defending, and proposing conceptions of good and wrong action,"…
Q: Should we use a synchronous or asynchronous bus to link the central processing unit to the memory?…
A: Synchronous buses are timed, and each direction is executed as the clock ticks.The ticking of the…
Q: Difference between wired and wireless internet?
A: there are 2 types of networks: (a) Wire Network: As we all know, “cable” refers to any visible…
Q: Is there a non-free Linux firewall mentioned in the presentation that you can explain in a few…
A: A firewall is a part of software or firmware that prevents users from accessing a network without…
Q: What are the stages of the Iterative Waterfall Model? It is also possible to use the Iterative…
A: Iterative Waterfall Model: One of the software development models is the iterative model. In this…
Q: Create a table that differentiates between the functional and non-functional needs of the…
A: The answer is that any information system must pass two types of tests. There are two distinct…
Q: Provide an explanation of how you may defend your home network using personal firewalls in addition…
A: Answer:
Q: Which of the following categories of services does the Internet provide its consumers in the form of…
A: Internet providers let us access text, images, music, and programmers online. VTC Video conferencing…
Q: Write the precondition & postcondition for each method.
A: We are required to trace the code for the given values and define the pre and post conditions for…
Q: Is there a significant difference between the World Wide Web (WWW) and the Internet (Internet)?
A: In step 2, I have provided difference between www and internet.
Q: Sequential access and direct access are the two methods that may be used to locate data in memory.…
A: Launch: Instead of needing to re-read data from the beginning, direct access data is read…
Q: Create an AVL Tree by inserting the following elements one at a time: 35, 55, 25, 45,50 Note: Don't…
A:
Q: Consider the following 5 x 5 image pixel values. 6 6 6 3 2 4 5 6 5 4 2 4 2 1 2 2 1 3 2 5 1 6 5 a.…
A: Given matrix contains, 5*5 matrix indicates the pixel values that includes 1, 2, 3, 4, 5, 6. a. The…
Q: What are some suggested firewall setting practices?
A: The following best practices are advised for operating a firewall:
Q: How would you go about altering the structure of a table via SQL? What broad categories of shifts…
A: A table structure contains information such as field names, sizes, and data kinds. Adding and…
Q: The job of the systems analyst in the development of information systems is to describe what such…
A: A system analyst is a person who utilizes information technology to solve business challenges using…
Q: What kinds of network topologies can really be implemented, and which do you think are the best?
A: The physical network topology refers to the actual connections of how the network is arranged.
Q: 4. For each of the following, match the values on the left to those on the right. g. CAFE 16 h.42…
A: Your answer is given below.
Q: How can a network possibly achieve success and maximize its potential if three conditions aren't…
A: INITIATION: Successful networking partnerships display a genuine interest in their contacts and…
Q: int x = 25; while (x > 0) { System.out.println("Hello"); x = 10; }
A: Write the exact output that you expect to see on the screen when the indicated statements are…
Q: Describe the four different parts that make up an information system.
A: Information System: A formal, sociotechnical, organisational system intended to gather, process,…
Q: Defects in wireless networks might cause issues. Explain how three of these problems influence the…
A: Wireless networks are susceptible to faults that cause issues. Describe how three of these problems…
Q: Should we connect the CPU to the RAM via an asynchronous or synchronous bus? Please include an…
A: A bus is a type of communication link that uses a collection of wires to connect multiple…
Q: ect to see on the
A: Solution - In the given question, we have to tell the exact output of the given program.
Q: One aspect of a simulated annealing cooling schedule is the temperature. i. Explain the effect of…
A: Answer
Q: Other than those that are based on networks, what other kinds of firewalls are there
A: Firewalls monitor traffic and assist in preventing unwanted traffic from entering your network,…
Q: Write a program in MATLAB to find the value of x in the following equation X+c=a*x-12
A: Equation is X+c=a*x-12. Hence to find the value of x, simplify the equation with respect to x,…
Q: Q2/Rewrite the Programmed by using "spc" Private Sub Command1_Click() Font.Name = "times new roman":…
A: Statistical technique manipulate (SPC) is described as using statistical techniques to control a…
Q: What is a mantrap? A fake network set up to lure in and catch a hacker A trap…
A: According to the information given:- we have to choose the correct option to satisfy the statement.
Q: Consider how important wireless networks are in poor countries. Why do some companies choose…
A: Start: Families with many electronic devices, such as PCs, laptops, and other mobile devices, are…
Q: Message authentication may occur in a number of ways.
A: Message authentication Message authentication is said to safeguard the "integrity" of messages,…
Step by step
Solved in 2 steps with 2 images

- Write a java program to add two numbersentered by the user in reversed order. Theprogram should be terminated only if the userselects to exit. Example: Input: 25 32 Expected output: 75this is a java program Complete the task and using for each loop , give me the code here and a screenshot of the outputWrite a program in java to to find the value of log(x) + log(y) and you must take these x and y from user and print the results.
- I need help with this HW question Create a program in Java that outputs ALL of the numbers whose digits add to 73 and which are factors of 73.It's common to print a rotating, increasing list of single-digit numbers at the start of a program's output as a visual guide to number the columns of the output to follow. With this in mind, write nested for loops in Java to produce the following output, with each line 60 characters wide:Create a Java program that loops around getting two fractions from the user,output their sum, and state whether or not they are equal. Keep looping untilthe first fraction entered is a zero fraction.
- write a code using java to run the program belowMake simple Java program (different from the screenshot below) that uses a while-loop to read only five float values from userInput. Ask the user to enter the five values, then print data below: Total, Max, Min, Avg, Interest (for total is 20%). - Please only include the screenshots of the code, input, and outputUsing modulus operator (%), Create a java program that will convert an input time(integer in seconds) to its equivalent in Hours, Minutes, and seconds Using BufferedReader to get input from the user, and System.out to output theresult

