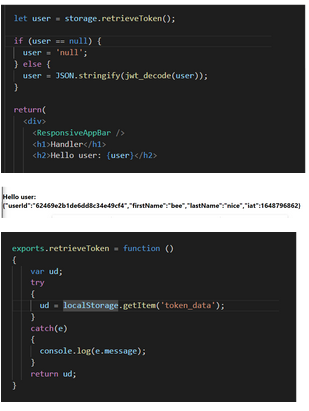
Need help!! I am trying to decode the JWT token, but I wanted it to show actually useriD instead of a long string. I have no idea how to solve it, can anyone help me fox this problem? and please explain what went wrong as well, thanks!!!
Q: What does a Repository and Data Dictionary mean in terms of computers?
A: Repository: In essence, a repository serves as a centralised site for the storage and upkeep of…
Q: For what reasons must the authentication procedure be performed? Examine how various authentication…
A: According to the information given:- We have to describe the reasons that the authentication…
Q: The internet activities of Mafiaboy should be probed. When and how did he enter these locations? How…
A: Introduction: On the internet, Michael Cale operated under the guise of Mafiaboy. In the year 2000,…
Q: Why must user-defined function prototypes be specified when a programme has user-defined functions
A: Please find the answer below :
Q: Firewalls, which are essential to network protection, are strongly reliant on network security and…
A: A firewall is software or firmware which are used that in order to prevents the unauthorized access…
Q: Linux provides a set of functions that ensure atomic operations on a variable in order to prevent…
A: Multiprocessor Systems: A system having more than one a processor is a referred to as a…
Q: What does "encapsulation" imply when used to object-oriented programming?
A: OOPs: A programming paradigm known as "object-oriented programming" is founded on the idea that…
Q: A programme slice: what does that mean? discussion of programme segmentation, both static and…
A: Answer is Explanation: Program slicing can be defined in such a way that it is a technique used…
Q: What are the two separate sorts of Internet-based services made accessible to mobile application…
A: Answer is
Q: Assess the risks and benefits of cloud security from a security standpoint. Transitioning from…
A: Cloud brings advantages such as flexibility and scalability cloud computing security risks are seen…
Q: Using the Internet for research When and how did his Mafiaboy Compromises adventures begin? The…
A: Was he searching the internet for information on Mafiaboy's adventures? When did he start…
Q: A user-defined functions programme must supply function prototypes.
A: User defined functions are those functions which are defined by the user according to it's need. A…
Q: Will you, as an IT manager, assign new systems analysts maintenance tasks? Why do you feel that way?
A: Answer: Yes, as an IT manager, assign new systems analysts maintenance tasks because the Systems…
Q: Is there a structural distinction between a catalog and a data dictionary
A: Introduction: A data catalogue is a tool that organises data and makes it possible for users to…
Q: What else should be considered about data backup and restoration
A: Answer:
Q: What are some of the most crucial factors that need to be taken into account while developing a…
A: Let's look out what factors need to be considered while designing a physical database
Q: IT security Compare these encryption products' CIA (Confidentiality, Integrity, Availability)…
A: The United States intelligence agency triad, often known as confidentiality, integrity, and…
Q: Describe delay and bandwidth. Think about how system performance is impacted by bandwidth and…
A: by Bartleby's Rules Please ask further questions separately as I can only handle three parts at…
Q: Clarifying firewalls' function in network security and protection is crucial. Don't forget to make…
A: the value of a firewallLet's start by asking, "Why firewall?"I have a computer, and it works well.…
Q: Give examples of the three most popular file management techniques
A: In the below step we have discussed the 4 most popular file management techniques. You can pick any…
Q: What decisions must be taken in order to define database field requirements?
A: The following judgements must be taken into account while creating the Field specifications:
Q: stalling RISC CPUs easier than installing CISC CP
A: Introduction: The terms RISC and Cisc are meaningless. What matters is creating a hardware and…
Q: What options are there in computer science for maintaining data integrity?
A: Introduction: The data developer must include aspects that improve the data's correctness and…
Q: How may interface designers do a hierarchical task analysis? Describe the seven-step procedure
A: Introduction: Hierarchical Task Analysis: This methodical, objective technique helps users define…
Q: consider data backup and recovery from several
A: the solution is an given below :
Q: Compile and present a list of the most urgent security problems specific to cloud computing, as well…
A: Start: Here, the primary security flaws specific to cloud computing are described, along with the…
Q: What steps are involved in getting data ready for input and categorizing it?
A: Data entry is a broad field with various needs based on the role, industry, and organisation. If you…
Q: The OSI model argues that most computer systems don't need as many layers as they really need,…
A: OSI: The Open Systems Interconnection (OSI) model outlines the proper channels for communication. On…
Q: What are the most essential aspects of data backup and recovery?
A: Introduction: It assumes a fundamental part to reestablish the data structure capacity with the goal…
Q: What are the most effective cloud-based data backup procedures?
A: You obviously need backups, if you ask the question. But it is advisable to create duplicates of…
Q: What is a pointer variable? Next, what? It is a dynamic array. What's the thing with pointers and…
A: A pointer is a type of programming object used to hold addresses rather than values. A pointer…
Q: Explain the practical use of a challenge-response authentication system. How does it make a system…
A: Intro A query and a response are the two main components of verification of a difficult answer. The…
Q: What are the advantages and disadvantages of using a service like Gmail for email? improving and…
A: Introduction In this question, we are asked What are the advantages and disadvantages of using a…
Q: What advantages do both vertical and horizontal partitioning offer?
A: The following is a list of benefits that may be gained from both vertical and horizontal…
Q: When attempting to migrate their organisation to a cloud computing platform, businesses often…
A: Answer : When organization migrate their organization to a cloud computing platform than the most…
Q: What is a file manager? Describe Windows Explorer. Include a few file and storage places. The…
A: File Manager: Every file management operation is supported (open, search, navigate directory, copy…
Q: What recommended best practises are there for managing firewalls? Explain.
A: In this question we need to explain the best practices we should maintain for managing firewalls.
Q: Why are packet losses more at the start of a transmission with the TCP Tahoe network configuration…
A: INTRODUCTION: Given that the TCP Tahoe configuration network is being utilised, why are packet…
Q: o consider data backu
A: Introduction: Data backup: Data backup refers to the process of making several copies of important…
Q: The process model for RAD Software is rapid development of software applications. Application…
A: Concept The life cycle of software development is a technique that outlines a series of procedures…
Q: Is the security of the cloud endangered by a data breach? What more can you tell me about…
A: Breach of data: Session Hijacking is an attack that enables unauthorized access to authorized…
Q: User-defined functions are preferred than those that are predefined.
A: INTRODUCTION: User-defined functions: Programmers rely on user-defined functions, often known as…
Q: What are the advantages and disadvantages of using a service like Gmail for email? improving and…
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: Do you have any knowledge of the most popular host software firewall programmes? Explain
A: Given: On a single machine, a host software firewall filters both incoming and outgoing traffic. It…
Q: What is the most efficient method for acquiring application software? If you want to make a claim,…
A: Given: Which approach is most effective for obtaining application software? You should provide an…
Q: What Advantages Does Data Cleaning in Computer Science Offer?
A: Let's discuss what Data cleaning is and what are it's advantages.
Q: As a result of the expansion of online apps, consumers may now access two separate kinds of internet…
A: Internet applications provide users with access to two sorts of Internet services. Need to…
Q: Suppose a sequence of numbers was sorted in the following steps. Which sorting algorithm was likely…
A: The correct answer is given below with proper explanation Also demo code and output screenshot is…
Q: What are the most important elements to keep in mind about data backup and recovery?
A: Introduction In this question, we are asked What are the most important elements to keep in mind…
Q: Will you change your behavior? Why or why not? If yes, in what ways?
A: I am not very confident in my own privacy after listening to the Darknet Diaries episode "Dark…
Step by step
Solved in 2 steps

- AVA PROGRAM ASAP Please modify this program ASAP BECAUSE it does not pass all the test caseswhen I upload it to hypergrade. Its says 0 out of 3 passed when i upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseCodeConverter { private static HashMap<Character, String> morseMap = new HashMap<>(); public static void main(String[] args) { loadMorseCodes(); Scanner scanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String input = scanner.nextLine().toUpperCase(); String morseCode = convertToMorse(input); System.out.println(morseCode); } private static void loadMorseCodes() { try (BufferedReader reader = new BufferedReader(new FileReader("morse.txt"))) { String line;…1. The append() method concatenates the string representation of any other type of data tothe end of the invoking StringBuffer object. It has several overloaded versions. Here are afew of its forms:StringBuffer append(String str)StringBuffer append(int num)StringBuffer append(Object obj)2. The result is appended to the current StringBuffer object.3. The buffer itself is returned by each version of append( ).4. This allows subsequent calls to be chained together, write java code for itWhat is printed to the console when the code that follows is executed? ArrayList<String> passwords = new ArrayList<>(); passwords.add("akjdk12"); passwords.add("buujl32"); passwords.add("chrcl92"); passwords.add("nnnii87"); passwords.set(2, "cb2kr45"); passwords.remove("akjdk12"); System.out.println(passwords.get(1));
- This code doesn't work, please help me. ----------------------------------- #include<iomanip> #include <fstream> using namespace std; class Taxi { private: string driver_name; string maker; string color; public: int calls; int passengers; static int Tpassengers; Taxi(string name, string maker, string color) { this->driver_name=name; this->maker=maker; this->color=color; this->passengers=0; this->calls=0; } Taxi(int pass) { this->passengers=pass; } int NPassenger() { int x = (rand()%10)+1; return x; } Taxi operator += (const Taxi x){ this->passengers +=x.passengers; this->calls+=1; return *this; } void write_Taxi_info() { ofstream outFile; outFile.open("CTC.txt", std::ios_base::app); outFile.close(); } }; int Taxi::Tpassengers{0}; int main() { srand((unsigned)time(0)); Taxi** taxis = new Taxi*[6]; taxis[0] = new Taxi("xyz qwe","erty","blue"); taxis[1] = new Taxi("xyz qwe","erty","blue"); taxis[2] = new Taxi("xyz…HERE'S MY CODE import Foundationclass Item{var name: Stringvar price: Doubleinit(_ name:String,_ price:Double){self.name = name;self.price = price;}}class ItemFruit: Item{var taste: Stringinit(_ name:String,_ price:Double,_ taste: String){self.taste = tastesuper.init(name,price);}}print("Enter 5 records:")var x = 0; var pricesTaste:[String: Double] = ["sweet":0,"sour":0,"bitter":0];while x < 5 {if let input = readLine(){let fullNameArr = input.components(separatedBy: ", ")if let price: Double = Double(fullNameArr[0]){let itemObj = ItemFruit(fullNameArr[1],price,fullNameArr[2])if let prevPrice:Double = pricesTaste[itemObj.taste] {pricesTaste[itemObj.taste] = prevPrice + itemObj.price}}}x = x+1} if let priceBitter:Double = pricesTaste["bitter"] {print("bitter fruit total price: \(priceBitter)")}if let priceSour:Double = pricesTaste["sour"] {print("sour fruit total price: \(priceSour)")}if let priceSweet:Double = pricesTaste["sweet"] {print("sweet fruit total price: \(priceSweet)")}…Debug // Program describes two files // tells you which one is newer and which one is larger import java.nio.file.*; import java.nio.file.attribute.*; import java.io.IOException; public class DebugThirteen1 { publicstaticvoidmain(String[] args) { Path file1 = Paths.get("/root/sandbox/DebugDataOne1"); Path file2 = Paths.get("/root/sandbox/DebugDataOne2.txt"); try { BasicFileAttributes attr1 = Files.readAttributes(file1, BasicFileAttributes.class); System.out.println("File: " + file1getFileName()); System.out.println("Creation time " + attr1.creationTime()); System.out.println("Last modified time " + attr1lastModifiedTime()); System.out.println("Size " + attr1.size()); BasicFileAttributes attr2 = Files.readAttributes(file2, BasicFileAttributes.class); System.out.println("\nFile: " + file2.getFileName); System.out.println("Creation time " + attr2.creationTime()); System.out.println("Last modified time " + attr2.lastModifiedTime()); System.out.println("Size " + attr2.size());…
- public getFuelLevel():double retrieves fuel level in gallons Precondition: fuel level is initialized Postcondition: no change in state Return: fuel level in gallons with decimal valuespublic getFuelTankSize():double retrieves fuel level in gallons Precondition: fuel level is initialized Postcondition: no change is state Return: fuel level in gallons with decimal valuespublic setUpTrip(double, double): void Car's state is set to hold the speed of travel and distance to travel at that speed Precondition: none Postcondition: Car's state holds information on distance to travel and speed to travel Parameters: Average Speed to be driven, Distance to driveDevelop and use an algorithm that calculates the amount of fuel used and the actual distance driven in the drive() method. The algorithm must use a formula or multiple formulas ( as a piecewise function) that gives proportionately poorer mileage when the Car is driven faster or slower than its optimal speed. When a new Car object…Focus on string operations and methodsYou work for a small company that keeps the following information about its clients: • first name• last name • a 5-digit user code assigned by your company.The information is stored in a file clients.txt with the information for each client on one line(last name first), with commas between the parts. For exampleJones, Sally,00345Lin ,Nenya,00548Fule,A,00000Smythe , Mary Ann , 00012Your job is to create a program assign usernames for a login system. First: write a function named get_parts(string) that will that will receive as its arguments a string with the client data for one client, for example “Lin ,Nenya,00548”, and return the separate first name, last name, and client code. You should remove any extra whitespace from the beginning and newlines from the end of the parts.You’ll need to use some of the string methods that we covered in this lessonYou can test your function by with a main() that is just the function call with the argument typed…Focus on string operations and methodsYou work for a small company that keeps the following information about its clients: • first name• last name • a 5-digit user code assigned by your company.The information is stored in a file clients.txt with the information for each client on one line(last name first), with commas between the parts. For exampleJones, Sally,00345Lin ,Nenya,00548Fule,A,00000Smythe , Mary Ann , 00012Your job is to create a program assign usernames for a login system. First: write a function named get_parts(string) that will that will receive as its arguments a string with the client data for one client, for example “Lin ,Nenya,00548”, and return the separate first name, last name, and client code. You should remove any extra whitespace from the beginning and newlines from the end of the parts.You’ll need to use some of the string methods that we covered in this lessonYou can test your function by with a main() that is just the function call with the argument typed…
- JAVA PROGRAM ASAP Please Modify this program ASAP BECAUSE it does not pass all the test cases when I upload it to hypergrade Please modify so it passes all the test cases because it says 0 out of 2 passed. The program must pass the test case when uploaded to Hypergrade. Thank you import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseCodeConverter { private static HashMap<Character, String> morseMap = new HashMap<>(); public static void main(String[] args) { loadMorseCodes(); Scanner scanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String input = scanner.nextLine().toUpperCase(); String morseCode = convertToMorse(input); System.out.println(morseCode); } private static void loadMorseCodes() { try (BufferedReader reader = new BufferedReader(new…Java OOP Write a complete address book maintenance application. The user of the program has four options: Add a new person, delete a person, modify the data of a person, and search for a person by giving the name. Use the AddressBook class, either the original one from the chapter or the modified one from the previous exercises. You have to decide how to allow the user to enter the values for a new person, display person information, and so forth.Fix the errors in the Customer class and the Program. #include <iostream>#include <fstream>#include <string>using namespace std; class Customer {// Constructorvoid Customer(string name, string address) : cust_name(name), cust_address(address){acct_number = this.getNextAcctNumber();} // Accessor to get the account numberconst int getAcctNumber() { return acct_number; } // Accessor to get the customer namestring getCustName(} const { return cust_name; } // Accessor to get the customer addressstring getCustAddress() const { return cust_address; } // Set a customer name and addressstatic void set(string name, string address); // Set a customer addressvoid setAddress(string cust_address) { cust_address = cust_address; } // Get the next account number for the next customer.static const unsigned long getNextAcctNumber() { ++nextAcctNum; } // input operatorfriend Customer operator>> (istream& ins, Customer cust); // output operatorfriend void operator<<…



