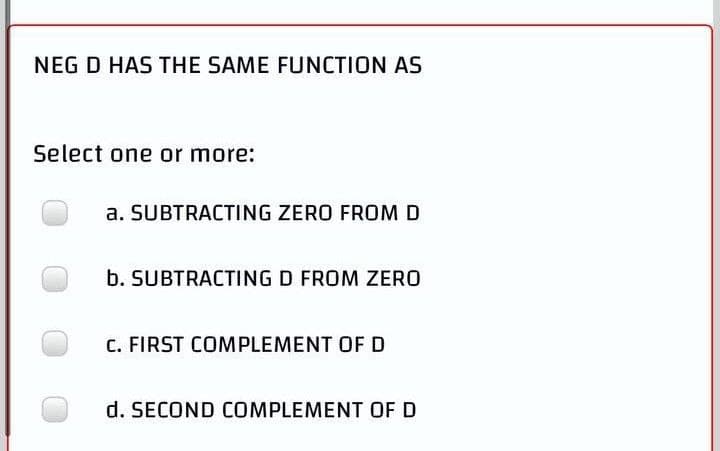
NEG D HAS THE SAME FUNCTION AS Select one or more: a. SUBTRACTING ZERO FROM D b. SUBTRACTING D FROM ZERO C. FIRST COMPLEMENT OF D d. SECOND COMPLEMENT OF D
Q: Write a java program according to these output results: Outout ***Booking Details*** Name of…
A: Solution: Java Program: import java.util.*; // Booking class class Booking { // Declare…
Q: Consider the following relations. • Student (zno, sname, age) · Enroll (zno, cno) • Course (cno,…
A: Here is the solution for the above program.
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: The Answer is in step2
Q: Q2: Write a program in the C++ language to print the even numbers in descending order from 16 to 2.
A: Answer the above program are as follows:
Q: In an Android-based system, what is the function of Middleware?
A: Middleware:- Security authentication, transaction processing, message queues, application servers,…
Q: GSM time slot is 577 s (microseconds) in duration and includes far more than a snapshot of each…
A: The answer is
Q: In your own words, go through the pitfalls newcomers to the area of machine learning should be aware…
A: Describe in detail the errors that newcomers to the area of Machine Learning should avoid: The first…
Q: Accumulator bit number4 in the read interrupt mask contains M7.5 P5.5
A: let us see the answer:- The correct answer is b) i.e.P5.5
Q: Is there a reason why threads are called "light-weight" processes? When a new thread is created,…
A: Light-weight: A lightweight thread is a computer programme process, often a user thread, that may…
Q: In order for a computer science stalemate to exist, four requirements must be satisfied.
A: Given: The study of algorithms and data structures, computer and network architecture, modelling…
Q: Write a program that takes input of a list of text, numbers, etc., and outputs that list in reverse.…
A: I give the code in Python along with output and code screenshot
Q: Explain what "using dummy data in a specific run" means in a few words.
A: A dummy data set contains records that have the same content and layout as a real production data…
Q: There are pros and downsides of using wireless networking. Should wireless networking be the…
A: Answer : pros of wireless networking. Accessibility: Wireless networks do not require cables or…
Q: Explain the differences between a monolithic kernel and a microkernel approach to operating system…
A: Monolithic Kernel: This is a sort of operating system architecture in which the complete operating…
Q: The mean of a list of numbers is its arithmetic average. The median of a list is its middle value…
A: Start enter 9 number by defining median `calculate median calculate mean and print it
Q: What are the implications for computer scientists of learning Boolean algebra?
A: Intro: Boolean algebra is important for computer scientists because it is a key tool for…
Q: Compare Friedman's "Globalization 3.0" notion to the digital divide's Nielsen empowerment stage.
A: Globalization: It refers to integrating commodities, services, and culture among nations worldwide.…
Q: What are the various operators of pointer? Describe their u How will you declare a pointer in C++?
A: Lets see the solution.
Q: What difficulties may develop if an operating system does not include a mechanism for synchronising…
A: The goal of process synchronization is to synchronize the execution of processes so that no two…
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: Intrusion detection systems primarily use two key intrusion detection methods. Signature based…
Q: Describe the strengths and shortcomings of each thread implementation, as well as their advantages…
A: Given: A modern system can manage both user and kernel threads. Programmers will employ user threads…
Q: How can an interactive system be designed to be user-friendly? Give an example to illustrate your…
A: According to the information given:- We have to define the an interactive system be designed to be…
Q: List and discuss ten worldwide computer science and information technology organizations.
A: Information Technology/Computer Science: In general, computer science is concerned with the design…
Q: Consider AES with 128-bit block length and 128-bit key length. What is the output of the first round…
A:
Q: likes(John, C++). likes(Bob, C#). likes(John, Java) likes(Bob, Lisp). likes(Julia, Python).…
A: likes(John, C++). likes(Bob, C#). likes(John, Java) likes(Bob, Lisp). likes(Julia, Python).…
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: IDPs:- (Intrusion Detection and Prevention System) Intrusion detection is the act of continuously…
Q: What is the order of the five stages of each instruction in a RISC processor? Decode, Fetch,…
A: None of the Options are correct Basic five-stage pipeline in a RISC machine (IF = Instruction…
Q: H7. a) Identify and explain the key functions of Information technology applications used in…
A: Let us see the answer: "Since you have asked multiple questions I am solving the first part for you…
Q: rch with clustered files degrades the perform
A: T or F. The B+ tree search with clustered files degrades the performance for a range query.
Q: Wireless networks raise a slew of questions due to their inherent characteristics. Using your own…
A: Piggybacking: If you don't safeguard your wireless network, anybody within range of your access…
Q: Discuss the types of graphics security methods employed at AIT (KCCentryway, )'s which might be…
A: Despite the fact that the COVID 19 pandemic is still in its early stages, the newest monitoring…
Q: Given the following matrices: 2 1 4) A=| -3 p 2 1-2 5) 0 1 B= q 3 4 0 Find AB. O A q+ 16 AB=-3q+8 -…
A:
Q: Explain TWO (2) requirements for secure use of symmetric encryption.
A: We are going to understand what are the two main requirements for the secure use of symmetric key…
Q: 2. Consider the following operation: Z = AB · BC а. Write out the truth table for the given…
A:
Q: Comparatively discuss the operationalization differences between objective and abstract variables.
A: Variables are required in every programming: language to store specified values during the execution…
Q: 1. Consider the relational schemas given below and the respective sets of functional dependencies…
A: Answer
Q: Two separate processes and two separate threads in the same process are compared. Doing something is…
A: Processes are large-scale activities. Threads are procedures that are less in weight: Switching…
Q: define the following (Subject: Human Computer Interaction) 1. User Assistance 2. menus and…
A: Note: Due to company policies I am compelled to solve only the first three sub parts of the…
Q: Which code is used to solve the ?system of linear equation: A.(x^2)= B A = 1 4 B=1 2 1 4 1 2 sqrt([1…
A: Which code is used to solve the ?system of linear equation: A.(x^2)= B
Q: Select one: is a variable supplied to a different module. a. variable b. constant c. global variable…
A: Given: A parameter is a kind of variable or formal argument that has a specific meaning. Input code…
Q: witching communication ne
A: Solution - In the given question, we have to explain how circuit-switching and packet-switching…
Q: What are some characteristics of TCP? Reliable Less overhead than UDP Congestion control…
A: TCP is reliable Protocol. so, First Option is CORRECT. TCP has less overhead than UDP . so, Second…
Q: Create a c++ program using any conditional statements that will determine the zodiac sign of your…
A: Given: We have to write a c++ program using any conditional statements that will determine the…
Q: Does machine learning no longer utilize algorithms and data structures?
A: Algorithms and Data Structures: Data structures are the structure squares of reality. "We can…
Q: sumed by a process depend on the number of active threads? What is the connection between the amount…
A: Below the connection between the amount of memory consumed by processes and the number of active…
Q: Make a point to discuss the scheduling of processes and threads.
A: The answer of this question is as follows:
Q: Can unethical and illegal behaviour be avoided in the area of computer science
A: Answer :
Q: An organization has a class C network 196.10.10 and wants to form subnets fc departments, which host…
A: The answer is
Q: Why are performance and scalability quality properties for large information systems mportant. What…
A: Please find the answer below :
Q: It's important to weigh the benefits and drawbacks of wireless networking before using it. Should…
A: Wireless local area networks (Lawns) transmit: We need to discuss whether or not wireless networking…
Step by step
Solved in 3 steps

- Could you help me find a complete trace of this function? Please explain each step in order. Thank youHi, This is what I have, but I am stuck with what to write and not sure if my function is even correct, to begin with. Can someone show me a walk-through solution? MUST USE postgreSQL CREATE TABLE instructor_course_nums (ID VARCHAR(25), name VARCHAR(25), tot_courses VARCHAR(25)); CREATE OR REPLACE PROCEDURE calculate_instr_course(ID VARCHAR(25), name VARCHAR(25), tot_courses VARCHAR(25))LANGUAGE plpgsqlAS$$BEGIN END;$$;Want in detail please
- Given prompt and response below.Properly Answer plzzWhich of the given assertion are true? a. The MIN function can be used only with numeric data. b. The MAX function can be used only with date values. c. The AVG function can be used only with numeric data. d. The SUM function can't be part of a nested function.
- Thank you, can you answer the last subparts of the questions 'g','h', and 'i'Do not provide me copied answer.Identify what type of sequence is the one below and supply the sequence with the next two terms: 4. 56, 46, 36, 26,___,___ ? Type of Sequence: ____________________ 5. 2, 20, 200, 2000,___,___ ? Type of Sequence: ____________________

