NetBios Sdn. Bhd. is a local engineering company that has planned to expand their services and location in one of the branches (Ren in Johore. The KL HQ has simple network architecture. Clients' workstations are connected to an access switch, distributed switch and internal interface. Vlan technology has been deployed in both sites. The firewall's (DMZ_Router-Firewall) external interface connects directly to the internet service provider (ISP) router. The third interfa hosts a demilitarised zone (DMZ) hosting several servers. These servers include Web, DNS and FTP applications. Whereas in Johore r network administrator has planned to replace the current configuration with new VLAN design in order to make the network more enhance the security of the network especially in HQ branch in KL. For the new Remote Branch in Johore, the network administrator deploy WLC WLAN to ease the configuration of Wireless network and its access. In all the networks above the network administrator has noticed that Layer 2 defense has been compromised.
NetBios Sdn. Bhd. is a local engineering company that has planned to expand their services and location in one of the branches (Ren in Johore. The KL HQ has simple network architecture. Clients' workstations are connected to an access switch, distributed switch and internal interface. Vlan technology has been deployed in both sites. The firewall's (DMZ_Router-Firewall) external interface connects directly to the internet service provider (ISP) router. The third interfa hosts a demilitarised zone (DMZ) hosting several servers. These servers include Web, DNS and FTP applications. Whereas in Johore r network administrator has planned to replace the current configuration with new VLAN design in order to make the network more enhance the security of the network especially in HQ branch in KL. For the new Remote Branch in Johore, the network administrator deploy WLC WLAN to ease the configuration of Wireless network and its access. In all the networks above the network administrator has noticed that Layer 2 defense has been compromised.
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
don't copy plz
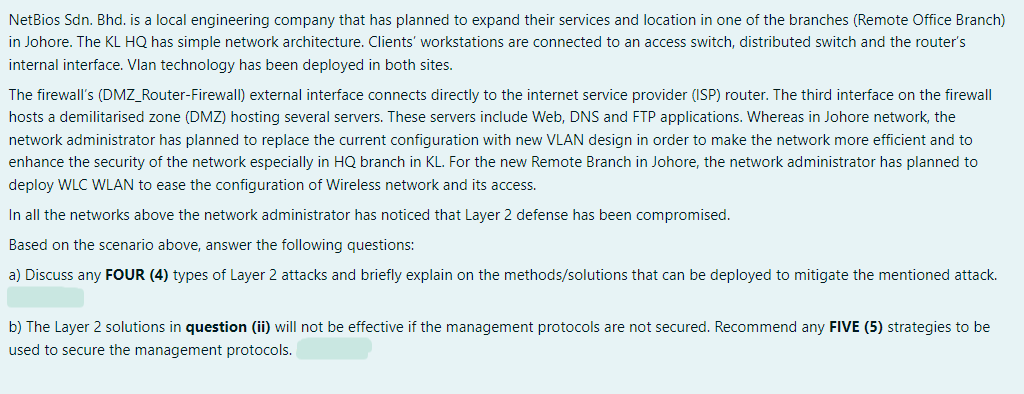
Transcribed Image Text:NetBios Sdn. Bhd. is a local engineering company that has planned to expand their services and location in one of the branches (Remote Office Branch)
in Johore. The KL HQ has simple network architecture. Clients' workstations are connected to an access switch, distributed switch and the router's
internal interface. Vlan technology has been deployed in both sites.
The firewall's (DMZ_Router-Firewall) external interface connects directly to the internet service provider (ISP) router. The third interface on the firewall
hosts a demilitarised zone (DMZ) hosting several servers. These servers include Web, DNS and FTP applications. Whereas in Johore network, the
network administrator has planned to replace the current configuration with new VLAN design in order to make the network more efficient and to
enhance the security of the network especially in HQ branch in KL. For the new Remote Branch in Johore, the network administrator has planned to
deploy WLC WLAN to ease the configuration of Wireless network and its access.
In all the networks above the network administrator has noticed that Layer 2 defense has been compromised.
Based on the scenario above, answer the following questions:
a) Discuss any FOUR (4) types of Layer 2 attacks and briefly explain on the methods/solutions that can be deployed to mitigate the mentioned attack.
b) The Layer 2 solutions in question (ii) will not be effective if the management protocols are not secured. Recommend any FIVE (5) strategies to be
used to secure the management protocols.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY