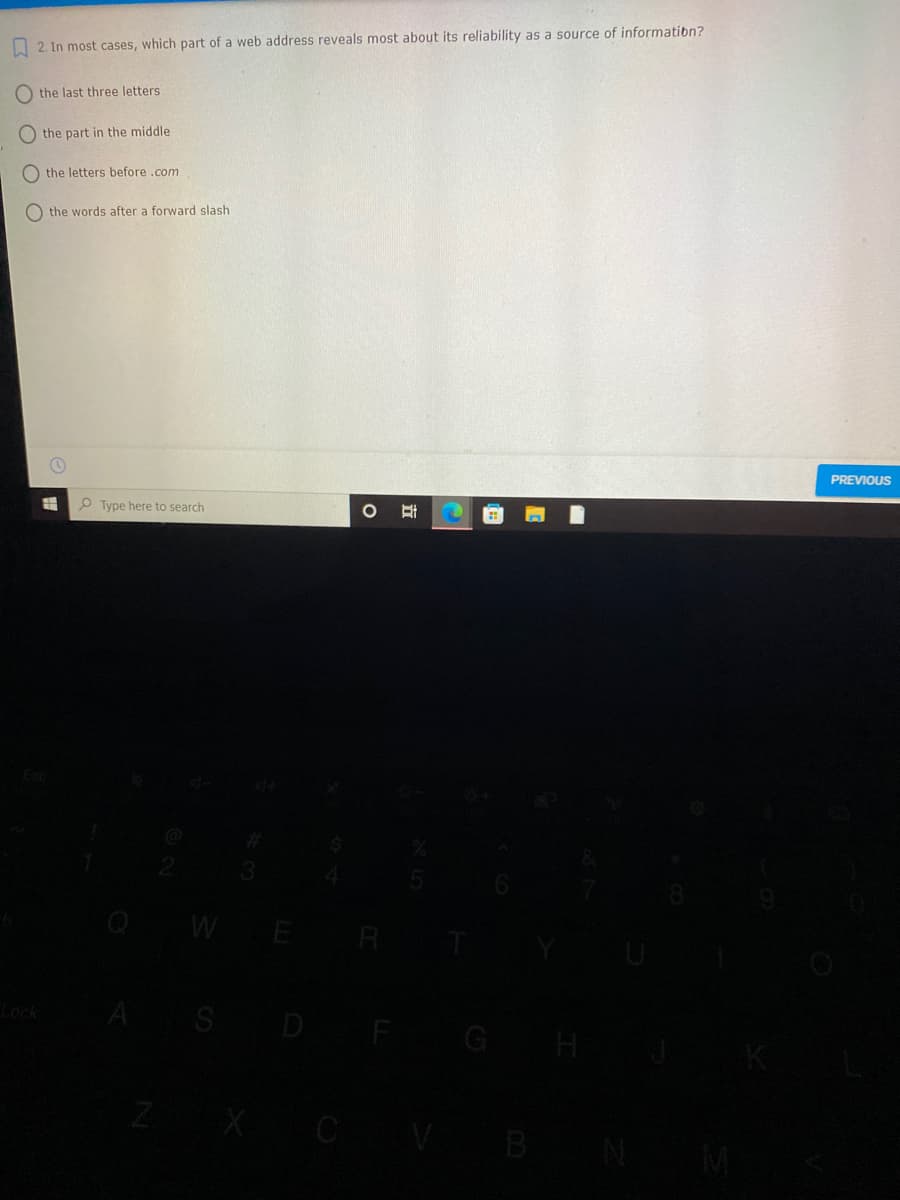
O 2. In most cases, which part of a web address reveals most about its reliability as a source of informatibn? O the last three letters the part in the middle O the letters before .com the words after a forward slash
Q: 2. Which of the following do you protect by implementing Secure Real-Time Protocol (SRTP)? A. Remote…
A: This question comes from which is a paper of Computer Science. Let's discuss it in the next section…
Q: 4.Which of the following gives the path for CGI script? a. remote_host b. remote_addr c.…
A: Question 4. Which of the following gives the path for CGI script? a. remote_host b. remote_addr c.…
Q: A famous enterprise blog was hacked, can you figure out how it was hacked?
A: Cyber-crime is criminal activity that either targets or uses a computer, a computer network or a…
Q: 172.16.0.0 (class B IP address) into four subnets.
A: The answer is
Q: Q1: (A) State if each of the following statements is true or false. Give explanations for incorrect…
A: The question is to find true or false statements with respect to the given statements.
Q: What is the cause? SSL certificate is invalid or self-signed User needs to change the URL to http://…
A: According to the asked question, the solution is given below with a proper explanation.
Q: Block Address : 192.168.16.0/24 LAN1 Usable #of Hosts: 100 Users Network Address; ? |
A: The answer is...
Q: What is an IP address used for? a.) to identify another computer on the interenet b.) to identify…
A: To do: IP address used for
Q: Question: 17 You've been asked to filter and block certain sites for your younger sister. Which of…
A: Answer : Proxy settings
Q: 18.Which of the following uses a set of rules to send and receive messages at the Internet address…
A: Answer to the above question is in step2.
Q: The Internet Engineering Task Force is the standards agency fo the Internet. Its standars…
A: question 3 TCP / IP Model consist of following layer :- Application Transport Internet Network…
Q: Host A sends a 1500-byte packet to Host B.
A: The answer is
Q: Refer to the below Ngure, Hot A Ir e milcating with Hot B using Chat program. PC-PT HostA Höst B…
A: During sending message from Host-A to Host-B , the message passes through 7 layers with different…
Q: Q2. How DNS works? Configure forward lookup zone and reverse lookup zone by taking an example.
A: Answer the above question are as follows
Q: 1. Cliend A:(in mainland China) Client B:(overseas connection). To make a lossless low letency…
A: The correct answer is d) QUIC (Quick UDP internet connection)
Q: Q. Explain the difference between SSL connection and sess
A: Required: Q. Explain the difference between SSL connection and session?
Q: Which of the following is an example of a client-server model? a. FTP b. DNS c. TELNET d. All of the…
A: Client-server model is a distributed application structure It divides task between server and…
Q: Syslog can be transported over: | UDP O SH O TCP O Telnet SSL
A: Here, Multiple options are given.
Q: The ID that represents an address for the Internet connection is: Select one: a. the Ports Number…
A: Actually, IP stands for Internet protocol.
Q: Name types of Web testing security problems? ii. Some common problems faced in Web testing? iii.…
A: Q9. i. Name types of Web testing security problems? Answer i. Some Web testing security problems…
Q: 23. Which of the following protocols cannot be used by a user agent to retrieve email messages from…
A: your question is Which of the following protocols cannot be used by a user agent to retrieve email…
Q: 7. HTTP stands for: A. Hyper Test Task Protocol B. Hyper Transfer Text Protocol C. Hyper Text…
A: To find the solution for: 7.HTTP stands for 8.To answer the “why” question: 9.To download files…
Q: What kind of service is best placed in a DMZ? a. FTP and SMTP b. Internal DNS server c.…
A: Actually, given information regarding DMZ
Q: 9. Which one the following is a specific address of a web page? A. Web address B. Email address C.…
A: 1 and 2. CPU is considered as the brain of the computer. CPU performs all types of data processing…
Q: QUESTION 13 Which is true about a ping sweep? O MAC addresses are pinged for availability. O A user…
A: Ping sweep: It is used to identify which hosts are alive available in the network using their IP…
Q: Wireshark lab Homework & Lab Assignment > Take screenshot for every answer you provide Repeat the…
A: -> Take screenshot for every answer you provide-> Repeat the steps on your local machine and…
Q: dnsrecon -d cuny.edu returns few IP addresses. Is 128.228.1.10 a Start of Authority address? a. True…
A: An IP address recognizes a computing device among millions of devices connected via a large network.…
Q: Alice (You) = @hello.ac.id Bob = @gmail.com How does DNS work on your computer to get IP mail…
A: As you have posted multiple questions, we will solve the first question for you. Name-Address…
Q: lease circle different types of Cyberattacks: A) A) Man in the Middle B) Ninja C) Phishing…
A: Please circle different types of Cyberattacks: A) A) Man in the Middle B) Ninja C) Phishing…
Q: 5- Which one of the following is not a network topology?" O All options O Bus O Client Server O Star
A: In the given question types of topology are bus topology, ring topology, star topology, mesh…
Q: Which of the following standards provide guidelines for hardening a Webserver? International…
A: the answer is given below:-
Q: Which of the following does a web browser NOT do Lütfen birini seçin: O A. protect against network…
A: Almost ( at present) all of the browser protect against network sniffing of HTTP…
Q: 1. What do the first six characters of the MAC address indiciate ? A. The device ID assigned by the…
A: Multiple questions are asked so first three questions will be answered. 1. The MAC address is a…
Q: A network administrator subnets the 192.168.10.0/24 network into subnets with /30 masks. How many…
A: Introduction: A network administrator subnets the 192.168.10.0/24 network into subnets with /30…
Q: Q. When we talk about IPsec there are two protocols providing different service models A. What are…
A: Encapsulating Security Protocol (ESP) and Authentication Header (AH) are the two types of protocols…
Q: Block Address : 192.168.16.0/24 LAN1 Usable #of Hosts: 100 Users Network Address; ?
A: The answer is as follows
Q: 2. Net surfing is done with the help of web page. 3. Plug-in is software used to insert multi- media…
A: 2. Net surfing is done with the help of a web page. TRUE 3. Plugin is software used to insert…
Q: 10. Which service is used to translate IP address into domain name? a. Reverse DNS lookup
A: 10. Which service is used to translate IP address into domain name? a. Reverse DNS lookup b.…
Q: Match the tool with the use. 1. Sniffing network traffic aircdecap-ng 2. Scanning the network Hydra…
A: Airdecap-ng is a network software suite that can decrypt WEP/WPA/WPA2 capture files. As well, it can…
Q: To help hide your IP address as you surf the Internet, it would be helpful to use: A. Network…
A: Two types of addresses are used to uniquely identify a computer viz. MAC address and IP address. IP…
Q: Apache is a popular example of networking software of what type? a. Web server b. Browser c.…
A: Networking software: It will help admins to deploy, manage and also monitor the network.
Q: Which of the following is a true statement about peer to peer network? All computers are on equal…
A: Find the true statement about the peer-to-peer network. a. All computers are on equal status and can…
Q: How to get around website block?
A: Geo-Location Many Services prefer use of geo-blocking tools to restrict access to certain content…
Q: QUESTION 2 Use internet protocol to attach a file to the email. O a. HTTP O b. FTP OC. SMTP O d.…
A: The answers to these questions are explained and answered as follows:
Q: The Protocol that responsible to transfer the Files between networks? O TPF O HTTP O FTP O TCP
A: As per Bartleby guidelines we are supposed to answer only one question at a time from a post. Here…
Q: What are the range for IPv4 Address classes (tip: class A, B...)?
A: Given: 1.What are the range for IPv4 Address classes (tip: class A, B...)?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Write a small program/script to resolve all DNS hostnames of Southeastern's ranging from 0 to 255 for the third and fourth octet in 147.174.$i.$j/16. Use any language you like (Bash, PowerShell, Python, Java). Paste the contents of your program below.a) A nonpersistent web page with 13 items will load in ____ ms. RTT=9ms; Object Transmission Time=2*RTT). (ms answer) b) For a persistent connection, what would the computation yield? c) Does the computation incorporate all delays? Give reasonsA.Which of the following protocols keeps all potential paths active while managing the flow of data across the paths to prevent loops? 1.TRILL 2.CARP 3.SPB 4.RSTP
- Which of the following is NOT an argument against using static routing? O. There is no need for more resources, such as additional CPU or bandwidth. O.b. The routing tables are rather compact, and the amount of maintenance required is low. O.c. If the topology is altered in any way, the configuration will be impacted. The path to the goal does not ever diverge from its usual course.1. Persistent HTTP requires?a. 2(round trip times) + file transmission timeb. as little as two RTT for all the referenced objectsc. one file transmission timed. as little as one RTT for all the referenced objects 2. UDP has no connection between client & server?a. RCVR extracts sender IP address and portb. sender explicitly attaches IP destination address and portc. three other answers are incorrectd. no handshaking before sending data 3. A socket in computer networks is correctly defined as?a. A combination of IP address and port number, connected by a "/" symbolb. sender explicitly attaches IP destination address and portc. RCVR extracts from the socket, sender IP address and portd. A combination of IP address and port number, connected by a"." symbol 4. The data link layer provides?a. the functional and procedural means to transfer data between network entities and the means to detect and possibly correct errors that may occur in the link layer.b. the functional and procedural…The text below shows a reply sent from the server in response to a http GET message. What are the first 5 bytes of the document retrieved? HTTP/1.1 200 OK<cr><lf>Date: Tue, 07 Mar 2008 12:39:45GMT<cr><lf>Server: Apache/2.0.52 (Fedora) <cr><lf>Last-Modified: Sat, 10 Dec2005 18:27:46 GMT<cr><lf>ETag: “526c3-f22-a88a4c80”<cr><lf>Accept- Ranges: bytes<cr><lf>Content-Length: 3874<cr><lf> Keep-Alive: timeout=max=100<cr><lf>Connection: Keep-Alive<cr><lf>Content-Type: text/html; charset= ISO-8859-1<cr><lf><cr><lf><!doctype html public “- //w3c//dtd html 4.0 transitional//en”><lf><html><lf> <head><lf> <meta http-equiv=”Content-Type” content=”text/html; charset=iso-8859-1”><lf> <meta name=”GENERATOR” content=”Mozilla/4.79 [en] (Windows NT 5.0; U) Netscape]”><lf> <title>CMPSCI 453 / 591 / NTU-ST550A…
- Write a script to find and print a "ping sweep"? Use the following code: import os my_ip="192.168.10.103" # sub your ip address os.system('ping -n 4 {}'.format(my_ip))Which one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of code that has the potential to compromise the security of an Internet user b. A cookie gains entry to the user’s work area through an HTTP header c. A cookie has an expiry date and time d. Cookies can be used to track the browsing pattern of a user at a particular siteQuestion 1 Full explain this question and text typing work only thanks TRUE/FALSE part A,B C solution sent me with explain A. An Extend Access List is created when you choose 100 - 199* False True B . To assign an access list to an interface type ip access-group 100 out* False True C. A Named Access List is created when you choose 1-99* True False
- Which of the following is not an issue addressed by Spanning Tree Protocol? Select one: a. Gateway redundancy b. Broadcast storms c. Constant updating of the MAC filter table d. A device receiving multiple copies of the same frame1- What is the error message that occurs when the manager sends Set_Request to a read-only object? Also, list out any three error messages in SNMP v1. 2- What kind of network management protocols are available? What information can these protocols provide? Explain it with example. 3- Encode 32-bit INTEGER 12 in TLV format? What is the broadband communication system and how broadband network support quality of service (Qos)?Assume that it is on a networka DNS server (DNS)a Host (H) with a browser clientand a Web server called www.olles.se (Links to an external site.) (S)From the host's browser, a request is sent to www.olles.se (Links to an external page.)Which packages are sent and in which order(1) (2) etc. indicates the order(nothing is cached)Group of answer options (1) H to DNS, (2) DNS to H, (3) H to S, (4) S to H (1) H to DNS, (2) DNS to S, (3) S to H (1) H to DNS, (2) DNS to S, (3) S to DNS, (4) DNS to H (1) H to DNS, (2) DNS to H, (3) H to S, (4) S to DNS (5) DNS to H

