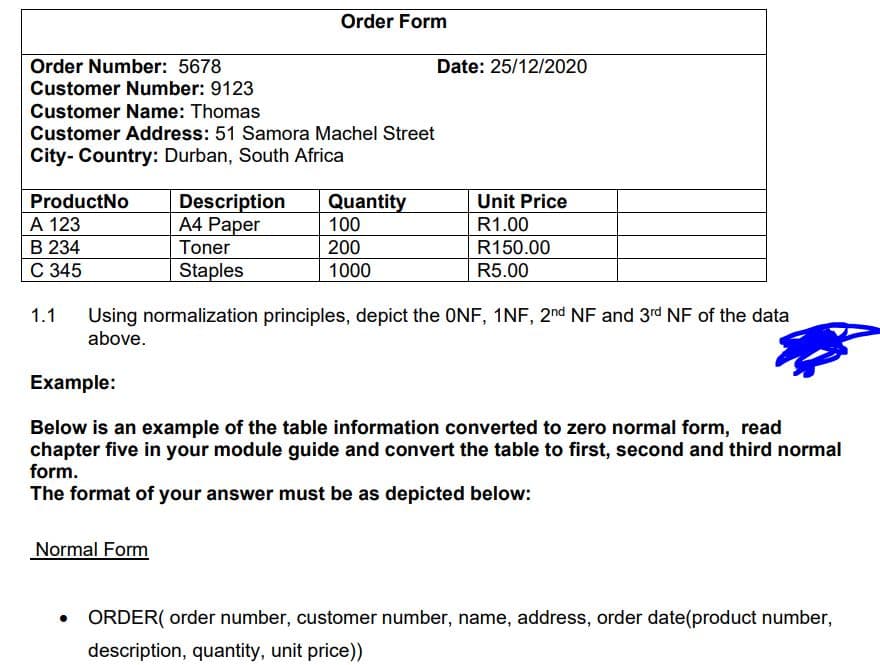
Order Number: 5678 Customer Number: 9123 Customer Name: Thomas Customer Address: 51 Samora Machel Street City- Country: Durban, South Africa ProductNo A 123 B 234 C 345 1.1 Description A4 Paper Order Form Toner Staples Quantity 100 200 1000 Date: 25/12/2020 Unit Price R1.00 R150.00 R5.00 Using normalization principles, depict the ONF, 1NF, 2nd NF and 3rd NF of the data above.
Q: Q.2) A communication source emits from three states the messages AB, BC and The transitional…
A: The given problem involves a communication source emitting messages from three different states: AB,…
Q: Show how the Structured Programming Theorem may eliminate GOTO uncertainty and simplify spaghetti…
A: What is Structured Programming Theorem: The term "Structured Programming" refers to a programming…
Q: What kinds of services are available at the network layer?
A: The net layer stands one of the seven levels of the OSI (Open Approaches Interconnection) exhibit.…
Q: Excel Question: How can cell ranges be spread throughout a worksheet?
A: In spreadsheet applications, such as Microsoft Excel or Google Sheets, cell ranges are a fundamental…
Q: In a diagram, what icon is used to show the state of a selection structure?
A: In computer science, selection structures are essential programming constructs used to make…
Q: vide examples of situations where you believe Information Literacy skills can benefit you in your…
A: As asked I have only solved the question that is given.Information literacy skills refer to the…
Q: What does the balanced scorecard have to do with getting the best possible return on investment?
A: Relationship between the balanced scorecard and achieving the best possible return on investment…
Q: Instead of merely performance, please explain why programmers prefer deep access.
A: In the context of programming and data structures, "deep access" and "shallow access" are terms used…
Q: Data mining impacts privacy and security.
A: Data mining is a formidable technique with great potential to extract helpful information concealed…
Q: How can we keep our information safe by combining the "Principle of Confidentiality" with a…
A: "Principle of Confidentiality" with a "Cryptographic Technique" can help keep information safe. The…
Q: Which Intel CPU socket's load plate is bolted?
A: CPU sockets, or CPU slots, serve as the connector interface on a computer motherboard. The CPU hole…
Q: BISQUE and NIQE image processing differences? explain the formula for
A: BISQUE and NIQE are two different image quality assessment algorithms used in image processing.They…
Q: The invisible web: how big?
A: As we navigate the expansive realm of the internet, it's easy to assume that search engines have…
Q: PointSource used IBM rational test workbench to find and fix various software bugs before deploying…
A: IBM Rational Test Workbench is an included suite that allow engineers to do various Type of testing,…
Q: Don't just say that deep access is better because it works better; explain why deep access is better…
A: As a programmer, one is often faced with the task of accessing and manipulating data within various…
Q: Explain three transport layer security technologies.
A: three different transport layer security technologies and their functionalities. Transport layer…
Q: How do you deal with scope and scope creep in computer forensics?
A: In computer forensics, scope refers to the defined boundaries and objectives of an investigation or…
Q: Suppose we have the following code: public class Foo { public Foo() { ... } public void first() {…
A: In this solution, we use two CountDownLatch objects: latch1 and latch2. Each latch has an initial…
Q: When a business uses BI tools and data, what kinds of ethics and security problems could it face?
A: When a business utilizes Business Intelligence (BI) tools and data, there are several ethics and…
Q: What are the problems with putting internet trade into place?
A: Internet trade or e-commerce has revolutionized the way trade operates. It provide business with a…
Q: Why didn't Target have a Chief Information Security Officer before their data breach?
A: What is Chief Information Security Officer: A Chief Information Security Officer (CISO) is a senior…
Q: When you turn off a computer at night, the date is lost, so you have to type it in again in the…
A: When you turn off a computer at night and the date is lost, it indicates that the computer's…
Q: Briefly explain what a DBA has to do with setup control.
A: A DBA (Database Administrator) is responsible for managing and maintaining a database system. One of…
Q: Ethics advise on what is ethically good to retain, whereas laws impose security requirements.…
A: The balance between ethics and laws often raises questions about what is considered ethically good…
Q: Explain how Software Engineering Methodologies fit within the SDLC.
A: Software Engineering Methodologies and the Software Development Life Cycle (SDLC) are intertwined…
Q: As an IT worker, is it possible to act legally without acting ethically?
A: What is IT worker: An IT worker refers to an individual who is employed in the field of Information…
Q: Why is it expensive and dangerous to switch from old systems to new ones?
A: Migration from old system to new ones is needed to uphold an organization's competitiveness. But, it…
Q: Which technology would you modify and why?
A: The technology that I would choose to modify is the blockchain. This spread ledger technology, most…
Q: Before releasing the FIMC app, PointSource utilised IBM's rational test workbench to find and fix…
A: Before releasing the FIMC app, PointSource utilized IBM's Rational Test Workbench, a testing tool,…
Q: How should a DBA maintain a DBMS after selection
A: DBA stands for Database Administrator. A DBA is a professional responsible for managing and…
Q: Explain why software developers prefer deep access over shallow access, not merely performance
A: Deep access refers to a high level of control and visibility into the underlying system components…
Q: A user that inputs 1 and 2 into the following code will result in what output? int col; int row;…
A: Declare variables row and col to store the user's input for the selected row and column.Create a…
Q: Examine electronic payment system features to allow m-commerce and e-commerce.
A: Electronic sum systems have been a basic constituent in the evolution of m-commerce (mobile…
Q: How can "Principle of Confidentiality" and "Cryptographic Technique" secure our data?
A: Cryptographic techniques refer to the methods and processes used in encryption, decryption, key…
Q: In the ANSI SPARC design, what role does data freedom play?
A: The ANSI SPARC architecture, otherwise called the three-schema architecture, is a conceptual…
Q: What does the database management system driver actually do?
A: A database management system (DBMS) driver, also known as a database driver or database connector,…
Q: A model is a form of representing something: 1-Briefly and in your own words, write about different…
A: BPMN, which stands for Business Process Model and Notation, is a standardized graphical notation…
Q: Write a JavaScript code with the following three different conditions: • Create the HTML document…
A: <!DOCTYPE html><html><head><title>Change Image…
Q: Explain wrapper classes for non-object data types to develop wrapper methods to combine non-object…
A: Wrapper Class:Java provides wrapper classes that allow non-object data types, such as int, float,…
Q: What are the problems with using internet commerce?
A: Internet commerce known as e-commerce, has transformed the way we do business by allowing us to buy…
Q: Find a business chance in the current situation in Malaysia?
A: What is business: A business is an entity engaged in commercial activities with the primary…
Q: What laptop software or hardware stops shoulder surfing?
A: Shoulder surfing refers to the act of someone observing your computer screen or keyboard to gain…
Q: What are the main challenges and potential solutions in developing secure and privacy-preserving…
A: Developing secure and privacy preserving algorithms for decentralized blockchain networks presents…
Q: Please do not give solution in image format thanku Createa file named method_override.py and follow…
A: I have done the code using Python 3. Make sure you are on latest version of Python. Please copy the…
Q: Using Hamming(7.4) 1. Check if code 1101001 has errors and if so, indicate the position of the…
A: Hamming refers to a family of error-correcting codes developed by Richard Hamming in the 1940s.…
Q: Staggered disc addressing reduces rotational latency.
A: The process of identifying and locating data on a disk storage device, such as a hard disk drive…
Q: What must an organisation have before installing a SIS?
A: What is Student Information System (SIS): A Student Information System (SIS) is a software…
Q: Differentiate twisted-pair cable, coaxial cable, fiber-optic cable, and wireless communication?
A: In computer science, communication between devices and networks is essential for transmitting data.…
Q: Explain the difference between ASCII and Unicode.
A: ASCII (American Standard Code for Information Interchange) and Unicode are character encoding…
Q: What's the difference between overlapped and separate constraints?
A: Constraints in databases are specific rules that guide the definition - What a database Really…
Step by step
Solved in 3 steps

- customer1.txt line 1: Ana customer2.txt line 1: Avi customer3.txt line: Mia Grey code lines (Start-9 & 14-end) can NOT be edited. New JAVA code must go inbetween lines.CUSTOMERColumns = 7, Rows = 10 CustomerID LastName FirstName Address ZIP Phone Email 1 Shire Robert 6225 Evanston Ave N 98103 206-524-2433 Robert.Shire@somewhere.com 2 Goodyear Katherine 7335 11th Ave NE 98105 206-524-3544 Katherine.Goodyear@somewhere.com 3 Bancroft Chris 12605 NE 6th Street 98005 425-635-9788 Chris.Bancroft@somewhere.com 4 Griffith John 335 Aloha Street 98109 206-524-4655 John.Griffith@somewhere.com 5 Tierney Doris 14510 NE 4th Street 98005 425-635-8677 Doris.Tierney@somewhere.com 6 Anderson Donna 1410 Hillcrest Parkway 98273 360-538-7566 Donna.Anderson@elsewhere.com 7 Svane Jack 3211 42nd Street 98115 206-524-5766 Jack.Svane@somewhere.com 8 Walsh Denesha 6712 24th Avenue NE 98053 425-635-7566 Denesha.Walsh@somewhere.com 9 Enquist Craig 534 15th Street 98225 360-538-6455 Craig.Enquist@elsewhere.com 10 Anderson Rose 6823 17th Ave NE 98105 206-524-6877 Rose.Anderson@elsewhere.com EMPLOYEEColumns = 5, Rows = 5 EmployeeID LastName FirstName…CUSTOMERColumns = 7, Rows = 10 CustomerID LastName FirstName Address ZIP Phone Email 1 Shire Robert 6225 Evanston Ave N 98103 206-524-2433 Robert.Shire@somewhere.com 2 Goodyear Katherine 7335 11th Ave NE 98105 206-524-3544 Katherine.Goodyear@somewhere.com 3 Bancroft Chris 12605 NE 6th Street 98005 425-635-9788 Chris.Bancroft@somewhere.com 4 Griffith John 335 Aloha Street 98109 206-524-4655 John.Griffith@somewhere.com 5 Tierney Doris 14510 NE 4th Street 98005 425-635-8677 Doris.Tierney@somewhere.com 6 Anderson Donna 1410 Hillcrest Parkway 98273 360-538-7566 Donna.Anderson@elsewhere.com 7 Svane Jack 3211 42nd Street 98115 206-524-5766 Jack.Svane@somewhere.com 8 Walsh Denesha 6712 24th Avenue NE 98053 425-635-7566 Denesha.Walsh@somewhere.com 9 Enquist Craig 534 15th Street 98225 360-538-6455 Craig.Enquist@elsewhere.com 10 Anderson Rose 6823 17th Ave NE 98105 206-524-6877 Rose.Anderson@elsewhere.com EMPLOYEEColumns = 5, Rows = 5 EmployeeID LastName FirstName…
- GIFT MINRETAIL MAXRETAIL--------------- ---------- ----------BOOKMARKER 0 12BOOK LABELS 12.01 25BOOK COVER 25.01 56FREE SHIPPING 56.01 999.99 CREATE SEQUENCE data above for ocale sqlQ3 a part Please provide detailed solution with explanation and justification asap to get a upvote for Each part please for a partExplain this code detail by detail like putting comments private void table_update() { int CC; try { // It is for SOMETHING ETC.*** Class.forName("com.mysql.jdbc.Driver"); con1 = DriverManager.getConnection("jdbc:mysql://localhost/linda","root",""); insert = con1.prepareStatement("SELECT * FROM record"); ResultSet Rs = insert.executeQuery(); ResultSetMetaData RSMD = Rs.getMetaData(); CC = RSMD.getColumnCount(); DefaultTableModel DFT = (DefaultTableModel) jTable1.getModel(); DFT.setRowCount(0); while (Rs.next()) { Vector v2 = new Vector(); for (int ii = 1; ii <= CC; ii++) { v2.add(Rs.getString("id")); v2.add(Rs.getString("name")); v2.add(Rs.getString("mobile")); v2.add(Rs.getString("course")); }…
- Open your text editor and create a new document named model.php model.php will contain functions that will connect to a database potentially return PDO statementobjects to the controller for processing. updateMessagesfunction updateMessages($id)This method will take a single parameter of id which is the saved id from the last or latest message displayed. It will conditionally select from the table “messages”, id, name, message, and time. The condition is that the field id is greater than the parameter for id. The return is the PDOStatement object with the row data from the query.# Begin constantsCOLUMN_ID = 0COLUMN_NAME = 1COLUMN_HIGHWAY = 2COLUMN_LAT = 3COLUMN_LON = 4COLUMN_YEAR_BUILT = 5COLUMN_LAST_MAJOR_REHAB = 6COLUMN_LAST_MINOR_REHAB = 7COLUMN_NUM_SPANS = 8COLUMN_SPAN_DETAILS = 9COLUMN_DECK_LENGTH = 10COLUMN_LAST_INSPECTED = 11COLUMN_BCI = 12 INDEX_BCI_YEARS = 0INDEX_BCI_SCORES = 1MISSING_BCI = -1.0 EARTH_RADIUS = 6371 # Sample data for docstring examplesdef create_example_bridge_1() -> list:"""Return a bridge in our list-format to use for doctest examples. This bridge is the same as the bridge from row 3 of the dataset.""" return [1, 'Highway 24 Underpass at Highway 403','403', 43.167233, -80.275567, '1965', '2014', '2009', 4,[12.0, 19.0, 21.0, 12.0], 65.0, '04/13/2012',[['2013', '2012', '2011', '2010', '2009', '2008', '2007','2006', '2005', '2004', '2003', '2002', '2001', '2000'],[MISSING_BCI, 72.3, MISSING_BCI, 69.5, MISSING_BCI, 70.0, MISSING_BCI,70.3, MISSING_BCI, 70.5, MISSING_BCI, 70.7, 72.9, MISSING_BCI]]] def create_example_bridge_2() ->…Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: Transaction SQL Statement Retrieve the flight number, departure and arrival airports of all British Airways. Retrieve the name of every passenger together with their flight number and the associated company. Retrieve all flights departed from all airports in London. Retrieve the ticket numbers…
- Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions:1. Retrieve all rows in Airport table for all the airports in London city.2. Retrieve all British and German passengers.3. Retrieve all names of all the passengers.4. Retrieve the flight number, departure and arrival airports of all British Airways.5. Retrieve the name of every passenger together with their…Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: Transaction SQL Statement Retrieve all rows in Airport table for all the airports in London city. Retrieve all British and German passengers. Retrieve all names of all the passengers. Retrieve the flight number, departure and arrival airports of all British Airways. Retrieve the name of…Course: Database *(SQL)* Please excute the given SQL script (https://drive.google.com/file/d/1zxe_aOhERjVCL54_zbgSLkFTRHYQhOPW/view?usp=sharing) for accessing the data. The data is described in the following relation schemas: Airport (airportID, name, city) Passenger (ticketNo, name, nationality, flightNo, seatNo)FK: flightNo references Flight (flightNo)FK: seatNo references Seat (seatNo) Flight (flightNo, flightCompany, departAirport, arrivalAirport)FK: departAirport references Airport (airportID)FK: arrivalAirport references Airport (airportID) Seat (seatNo, flightNo, class)FK: flightNo references Flight (flightNo) #Construct the SQL statements based on following transactions: please if you could give all the sql statements needed i will appreciate that, and i promise to put thump up Transaction SQL Statement Retrieve all rows in Airport table for all the airports in London city. Retrieve all British and German passengers. Retrieve all names of all the passengers.…



