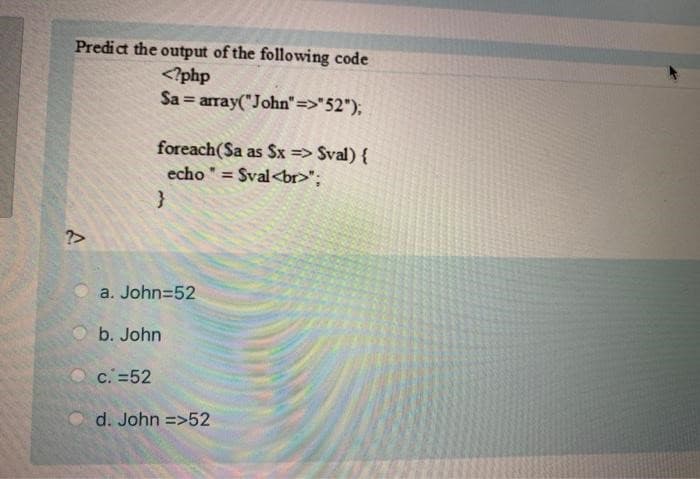
Predict the output of the following code "52"); ?> foreach(Sa as Sx => Sval) { echo = = Sval"; } a. John=52
Q: Compare the benefits and drawbacks of connectionless protocols against connection-based protocols.
A: To do: provide an explanation of the advantages and disadvantages of connectionless protocols.
Q: What is transfer function?
A:
Q: What elements influence the effectiveness of network communication?
A: Introduction: Bandwidth is a network's data transmission rate. Data types need varied bandwidth.…
Q: How many acknowledgements would the recipient need to receive before they could no longer receive…
A: Related to Acknowledgement of Recipient: The term "acknowledgment of receipt" refers to the process…
Q: The following five justifications highlight the relevance of standard software patches and updates:…
A: Introduction: These small pop-up windows may be familiar to you. They let you know that there are…
Q: LOOP LabelName ; 8 clock cycles Assume that the following code fragment is used to s ;initialize sum…
A: The answer is
Q: Is that correct? A binary search tree's overall balance is influenced by the order in which items…
A: In a balanced binary tree, the difference between the height of left-subtree and right-subtree at…
Q: A network must have both effectiveness and efficiency in order to function successfully. Please…
A: Network effectivness and efficiency is important factor for successful functionality
Q: what transport layer protocol is used by the point-to-point tunneling protocol?
A: There are two transport layer protocols in an OSI model , TCP and UDP , let's discuss which is used…
Q: 12. Report the names of the professors who supervise more than one student. 13. Report the names…
A: In order to find professors who supervise more than one student, we will need a COUNT() function on…
Q: A flowchart is precisely what?
A: A flowchart is a visual representation of the process of problem-solving and can be extremely…
Q: y leak" entail in terms of d
A: Solution - In the given question, we have to tell what does memory leak entails in terms of dynamic…
Q: What three qualities must a network have in order to function effectively and efficiently? For a few…
A: The solution to the given question is: The most important criteria are performance , reliability and…
Q: Which is better, the improved binary search tree or the conventional binary tree?
A: The above question is solved in step 2 :-
Q: If a binary search tree has n nodes, what are the lowest and highest nodes? Your answer should be…
A: Introduction: In a binary search tree, the left child of a node has a value that is lower than the…
Q: Can the four essential parts of any computer-based information system be summed up in a few words?
A: Computer Equipment: This is the information-using physical technology. Hardware may range in size…
Q: 4. What is clock synchronization? Synchronize the network given below when the server advances 10…
A: SOLUTION:- The Berkeley algorithm is a method of clock synchronization in distributed computing…
Q: Can the four essential parts of any computer-based information system be summed up in a few words?
A: The Computer Based Information System (CBIS) is an information system that is mostly relied on…
Q: Problem 1: Given the dataset produce the following tables: a. A table where all rows (samples) with…
A: According to the answering policy, I can answer only the first question. For the remaining questions…
Q: Where will the network's physical and virtual networking hardware be located?
A: A virtual network is one that connects all the devices, servers, virtual machines, and data centres…
Q: Let's say system A wants to transfer system B a huge file. Describe the end computer. The file is…
A: Definition: Say system termination A requests that system termination B send it a large file.…
Q: What is CMRR?
A:
Q: the use of transport layer protocols the issues posed by the use of TCP and UPD in modern networks.
A: The solution to the given question is: Problems with using TCP and UPD on modern networks:…
Q: What do the urlretrieve and urlopen functions do?
A: We need to discuss urlretrieve and urlopen functions.
Q: School Voting Age IN C# Problem Description The DPCDSB recently announced that all students who…
A: Algorithm: Start Read birthday and store it in the date variable Split date with space as a…
Q: What factors may cause a network to slow down?
A: Introduction: network : At least two computers are required to form a network linked to share…
Q: Why OPAMP called operational Amplifier?
A: The solution to the given question is: OP-AMP is abbreviated form of operational amplifier.…
Q: You may only use selectors and constructors (introduced above) for this question. You may also use…
A: Data Abstraction is an OOP concept that hides the background details. It shows only those pieces of…
Q: Why OPAMP called operational Amplifier?
A:
Q: Why is hashing passwords stored in files preferable than encryption?
A: Hashed passwords cannot be decrypted and require an attacker to guess them, which can be made hard.…
Q: Why are protocols necessary for network communication? Describe the protocols that are used in the…
A: Introduction: Consider the TCP protocol as an example, where reservations are made first and then…
Q: Write a program that would generate the following pattern. For example: Result 0-1-1-1-1-1…
A: Pattern printing:
Q: Why is it difficult for someone to understand the semantic importance of a scenario from a…
A: Given: In your own words, describe why it is challenging for a person to understand the semantic…
Q: Due to the coronavirus epidemic, face-to-face lessons have been canceled in Hong Kong, requiring…
A: Due to the coronavirus pandemic, Hong Kong educational institutions have been forced to suspend…
Q: The benefits and drawbacks of connection-based systems vs connectionless methods are compared and…
A: Introduction: All source-to-destination packets follow the same path.Not every sender-receiver…
Q: The OSI model's combined session, presentation, and application levels are referred to as the TCP/IP…
A: TCP/IP includes collection and techniques for coping with media access, session interaction, data…
Q: Write a complete C program that prompts the user to enter a series of integers terminated by a 0.…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: What are the World Wide Web's and the Internet's biggest distinctions?
A: Introduction: MAC addressesAn internet device may be identified by its IP address, which is a…
Q: 4. List comprehension. a) Implement a list comprehension that creates a list of all odd numbers…
A: “Since you have asked multiple question, we will solve the first question for you. If youwant any…
Q: HOW DOES A CLASS INHERIT THE CONSTRUCTORS OF ITS SUPER CLASS ?
A:
Q: Why OPAMP called direct coupled high differential circuit?
A: OPAMP is a small-sized integrated circuit that can be used as a linear amplifier. The direct-coupled…
Q: What use do coding conventions serve? Analyze the coding standards used by the Java programming…
A: We must compose a paper on the coding standard and study the coding notion in the java programming…
Q: The application layer is the fifth layer to receive data at device B when data is sent from device A…
A: - We have to verify the statement regarding IP stack.
Q: What are stress tests, and why are they required?
A: A stess test, also called an exercise strain take a look at, indicates how your coronary heart works…
Q: Because microprocessor CPUs do not understand mnemonics as they are, they have to be con
A: The answer is
Q: Why is HTTP used by network applications? What other elements are necessary to build a Web…
A: Introduction: A method for encoding and sending data or information between the User (web browser)…
Q: Identify 5 syntax errors from the following code and write the correct code in the word document.…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: Des risk management operate and what is it? ability identification makes it so crucial in risk
A: Summary Risk management:The process of identifying, evaluating, and controlling threats to an…
Q: HOW DOES A CLASS INHERIT THE CONSTRUCTORS OF ITS SUPER CLASS ?
A: In the Java language, classes can be derived from other classes, thereby inheriting fields and…
Q: What use do coding conventions serve? Analyze the coding standards used by the Java programming…
A: Introduction: Coding conventions improve the code's readability. Coding conventions are not rules,…
Step by step
Solved in 2 steps

- First, read in an input value for variable valCount. Then, read valCount integers from input and output each on the same line wrapped in curly braces. End with a newline. Ex: If the input is 3 75 -25 -55, the output is: {75}{-25}{-55} #include <iostream>using namespace std; int main() { int valCount; cin >> valCount; int inputNum; for (int i = 0; i < valCount; i++) { cin >> inputNum; cout << "{" << inputNum << "}" << endl; } return 0;} Input 3 75 -25 -55 Your output {75} {-25} {-55} Expected output {75}{-25}{-55} check2: Compare outputkeyboard_arrow_up Input 1 70 Your output {70} clear3: Compare outputkeyboard_arrow_up Output is nearly correct, but whitespace differs. See highlights below. Special character legend Input 4 15 40 50 10 Your output {15} {40} {50} {10} Expected output {15}{40}{50}{10} clear4: Compare outputkeyboard_arrow_up Output is nearly correct, but…int pid1 = fork(); int pid2 = fork(); printf("PID: %d %d\n", pid1, pid2); Output with explanationWhat is the probability of a mistake in the REpitition code, often known as the Huffman code?
- // This program displays every combination of three-digitsstart Declarations num digit1 = 0 num digit2 = 0 num digit3 = 0 while digit1 <= 9 while digit2 <= 9 while digit3 <= 9 output digit1, digit2, digit3 digit1 = digit1 + 1 endwhile digit2 = digit2 + 1 endwhile digit3 = digit3 + 1 endwhilestop Debugging 5-03 what needs to be fixed ?#include using namespace std; bool isPalindrome(int x) { int n=0,val; val = x; while(x > 0) { n = n * 10 + x % 10; x = x / 10; } } int main() { int n; cin >>n; if(isPalindrome(n)) { cout <ample code for the reader-writer: #include <pthread.h>#include <semaphore.h>#include <stdio.h> /*This program provides a possible solution for first readers writers problem using mutex and semaphore.I have used 10 readers and 5 producers to demonstrate the solution. You can always play with these values.*/ sem_t wrt;pthread_mutex_t mutex;int cnt = 1;int numreader = 0; void *writer(void *wno){ sem_wait(&wrt);cnt = cnt*2;printf("Writer %d modified cnt to %d\n",(*((int *)wno)),cnt);sem_post(&wrt); }void *reader(void *rno){ // Reader acquire the lock before modifying numreaderpthread_mutex_lock(&mutex);numreader++;if(numreader == 1) {sem_wait(&wrt); // If this id the first reader, then it will block the writer}pthread_mutex_unlock(&mutex);// Reading Sectionprintf("Reader %d: read cnt as %d\n",*((int *)rno),cnt); // Reader acquire the lock before modifying numreaderpthread_mutex_lock(&mutex);numreader--;if(numreader == 0) {sem_post(&wrt); //…
- please code in java.. dont use very advanced coding Double variable numFeet is read from input. Type cast numFeet to an integer.Ex. If the input is 52.5, then the output is:52Write code that outputs variable numMonths as follows. End with a newline. Ex: If the input is: 3 the output is: Months: 3 Phyton codeIn C++: Examine the code segment. What will be printed? If there are any errors indicate the nature of each error. int a[7] = {31, 12, 32, 14, 25, 16, 27}; int *ptr; ptr = & a[2]; for ( i=1; i<=5; i=i+2) cout << *(ptr +i); cout << a[0] << *ptr << *ptr - 2 << *(ptr -1)) << endl;
- Having trouble with this c++ homework question. void a(int n) { if(n<1) { cout << n*2 << " "; return; } cout << n*2 << " "; a(n-1);}1. Trace the function when n is 4.This Code print the first occurrences of x, Modify the code to print the last occurrences of x and print how many times it exists? ( with explanation for each line if possible) many thanks.Correct this code written in c. hint: the last ending (// calling function) #include<stdio.h>#include<math.h> function(float x, float y, int n){int i;float R,R_power_n=1,realpart,impart,theta;R=sqrt((x*x)+(y*y));theta = tan(y/x); // since tan inverse theta = y/x i.e., theta = tan(y/x) for(i=1;i<=n;i++) // loop for calculation of R power n value{R_power_n = R_power_n*R;} // R power n result stored in R_power_ntheta=n*theta; //calculating n thetarealpart=R_power_n*cos(theta); // Calculating real partimpart=R_power_n*sin(theta); // Calculating imaginary partprintf("\n%.2f + j%.2f", x,y);printf("\n\nPower of %d is %.2f + j%.2f\n\n", n,realpart,impart);}int main(){int main(){int n;float x;float y; // Because of real numbers, take x and y as float data typeprintf("\nEnter real values x:");scanf("%f",&x);printf("\nEnter real values y:");scanf("%f",&y);printf("\nEnter the n Value:");scanf("%d",&n);(x,y)=fuction(x,y,n); // calling function}

