ove employim
Q: What is the difference between a homogeneous DDBMS and a heterogeneous DDBMS? Which is the more diff...
A: Homogeneous DDBMS: All destinations are managed by a single database management system in a homogene...
Q: * To add a border to a picture a) Select picture then select Design tab b) Select picture then selec...
A: All answer must be resolved quicky Choose the correct answer: ADD BORDER TO A PICTURE ALL INPUT DATA...
Q: What makes using a VPN more secure than accessing the public internet is unclear. And how exactly do...
A: Introduction: There are several advantages to utilizing a virtual private network (VPN) rather than ...
Q: Explain with an example how packet switching works and how do routers assure that packets continue f...
A: Packet switching is the transfer of small pieces of data across various networks. These data chunks ...
Q: Q4) Creating fixed number of Sets and save in a Cell.
A: Please refer below for your reference: To create fixed number of cells one can use pivot tables to c...
Q: VPNs employ encryption techniques to ensure security and privacy when connecting remotely over a pub...
A: Introduction: VPN stands for "virtual private network," and it is a service that lets you keep your ...
Q: rce Python library that provides visualization tools. You can use the library to build either static...
A: _________ is an open source Python library that provides visualization tools. You can use the librar...
Q: There are n different sizes of boxes, from 1 to n. There is an unlimited supply of boxes of each siz...
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: What does it mean to encode a signal?
A: Hello student Greetings Hope you are doing great. Thank You!!!
Q: At the University of Technology and Applied Sciences, you were entrusted with developing an integrat...
A: Students may use their computer and technology skills to study and solve problems in the classroom v...
Q: s a student, how are you affected by the changes brought by Information Technology to your life
A: Perhaps the greatest test in instruction is dealing with every understudy in the homeroom. It's anyt...
Q: Give an explanation of what the difference is between NRZ-L and NRZI.
A: NRZ refers to a form of digital data transmission in which the binary low and high states, represent...
Q: ram with a great deal of flexibility. Is it possible for end users to access the database through th...
A: Access is a program with a great deal of flexibility. Is it possible for end users to access the dat...
Q: Identify and explain the Internet of Things (IoT) reference model. Fill in the blanks with the four ...
A: Introduction: In addition, the IoT reference model helps create and standardize IoT architecture and...
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A: Given binary number is 0011 1110 0110 1101 0000 0000 0000 0000 Total 32 bit number.
Q: a. What is the CPU utilization of the given process if cpu controlled time is 125ms? b. Ranked the s...
A: CPU Utilization: CPU utilization refers to a computer's utilization of processing resources, or the ...
Q: 1. Many languages distinguish between uppercase and lowercase letters in user-defined names. What a...
A: The following are some of the reasons why a language would differentiate between uppercase and lower...
Q: ITCS114 Assignment 2 - Arrays Part (1): Write a Java program to do the following: 1) Ask the user to...
A: Program Explanation: 1) Implement the header file. 2) Declare the main class. 3) Put the value of an...
Q: What core group of programs is in charge of controlling the internal operations of the computer's ha...
A: Introduction: Hardware shows to the physical components of a computer, such as the chassis, central ...
Q: Describe client/server design, including tiers, cost-benefit considerations, and performance.
A: Introduction: Client/server architecture Client/Server Architecture refers to systems that divide pr...
Q: are at any given ti
A: Here, SKU refers to the Stock Keeping Unit. It is the number which is used for the assigning for the...
Q: You could come across the term "inheritance" in current Windows network and operating systems from t...
A: Introduction: At the time of an individual's death, inheritance is the process of passing on private...
Q: When it comes to database architecture, why do you believe entity relationship (ER) diagrams are nec...
A: Introduction: An entity-relationship diagram represents a database's conceptual, graphical, and logi...
Q: ove semantic rules, give an evaluation of the expression ((4 ! 6) ! 1) (fully parenthesized to denot...
A: PREDICATES IN PROLOG: %1mymember(_, []):- false.mymember(X, [X|_]):- true.mymember(X, [_|Y]):- mymem...
Q: Why is web cilent referred to as a browser?
A: Introduction: A browser is a piece of software that is used to access the internet (world wide web)....
Q: Based on symmetric cryptosystem Data Encryption Standard, if the key is “UNITED A” and the cipher te...
A: Cipher text in the binary form: 01100010110011111001001111000111011000111111001001100000010010000
Q: If I want an interrupt to occur when the I/O pin PORT C pin 0 changes from high to low, which pin ch...
A: How many general purpose digital i/o ports are possible on ATmega328P? option (c-22) When used with ...
Q: Lab 10 Using an interface to share methods It is often the case that two or more classes share a co...
A: Creating ArrayList of Speakable objects and then adding Dog and Cat objects and then invoking speak ...
Q: Question 2 1- Add the following (98A8)h + (A8B9)h 2- Using First complement, Find (621)o - (211)h 3-...
A: Here, we are going to subtract Q3 value using 9's complement. In 9's complement: A-B = A+ (9's comp...
Q: sider a schedule with 3 transactions with 2, 3, and 4 operations respectively. Calculate the possibl...
A: Lets see the solution.
Q: To use MicroBit internal light sensor to detect the environment light intensity. Given speech and li...
A: - like sunlight sensor project this uses the microBit LED as a light sensor to measure how much ligh...
Q: Now convert the above into Third Normal Form. Indicate all primary keys and foreign keys.
A: Normalization is the term given to the process of organizing the data inside a given database. This ...
Q: List down ways to evaluate websites for reliability. Objectives: 1.) Determine the ethical dilemmas ...
A: Since you have asked multiple questions, we will answer the first question for you. If you want a sp...
Q: What are the advantages in implementing a language with a hybrid compiler?
A: the advantages in implementing a language with a hybrid compiler are
Q: Describe how motion input is used in the entertainment, military, athletics, and medical industries,...
A: Answer the above questions are as follows:
Q: U1 n=5 V1 V2 U5 U2 V5 U4 U3 V3 V4
A: A dominating set for a graph G = (V, E) is a subset D of V such that every vertex not in D is adjace...
Q: 2] contains `n-1` integer: An array A[0..n - to `n` in increasing order. (Thus one integ this range ...
A: the answer is an given below :
Q: The decimal equivalent of hex number 1B52 is O 6794 Skip O 6993 6949 O 6994
A: Actually, binary numbers are nothing but a 0's and 1's.
Q: A. ASCII В. ЕВCDIC C. Unicode D. ASCII 8. Bit map images are made up of A. phonemes B. vectors C. pi...
A: let us see the answer:- "Since you have multiple question i am solving first 2 for you if you want a...
Q: processed in a loop. The program should ‘dump’ the contents of the array before and after modificati...
A: 10. Write a program that modifies an array of 10 full words by replacing every negative value with...
Q: 8. Write C++ program to show that the sum of the infinite series, which is converges to In 2. N 1 T ...
A: Program code to copy: #include<iostream> using namespace std; int main() { // declaring a vari...
Q: Is it possible to classify the four most fundamental features of software development? Please let us...
A: Let's see the solution in the next steps
Q: Describe the many components of a computer.
A: We must first need to know what is computer ? Computer is an electronically programmable device tha...
Q: Undertake a research to examine one other organization relying on collaboration with international ...
A: Q1)a) Answer: Collaborative decision-making Based on information exchange, participating companies s...
Q: What are some of the most important aspects to consider when it comes to data backup and recovery?
A: Introduction : Planning is done throughout the data backup and recovery process to keep track of vit...
Q: eans that: Question 4 options: Not only SQL is us
A: Accessing Data with NoSQL Means that: Question 4 options: Not only SQL is used Only SQL is used No S...
Q: Connecting a new office computer in the SHSS to the internet and connecting a standalone computer in...
A: Introduction: The following sections detail the procedure for connecting the new office PC to the in...
Q: H.W Find the Adjoint to the following matrix 0.5 0.2 -0.1 X = 0.9 0.7 -0.6 -0.4 -1
A: Here in this question we have asked to find adjoint of the given matrix.
Q: ill the following code display in the lblSum control? Dim intSum As Integer Dim intY As I...
A: Lets see the solution.
Q: G) 15th Complement for (115)o H) 8th Complement for (96)h
A: G) Given number is, (115)o That means 115 is a octal number. The equivalent Hexadecimal number for 1...
Step by step
Solved in 4 steps

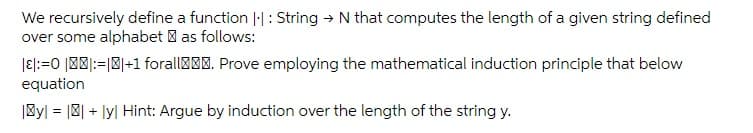
- The binomial coefficient C(N,k) can be defined recursively as follows: C(N,0) = 1, C(N,N) = 1, and for 0 < k < N, C(N,k) = C(N-1,k) + C(N - 1,k - 1). Write a function and give an analysis of the running time to compute the binomial coefficients as follows: A. The function is written recursively.Show Let f(.) be a computable, strictly monotonic function, that is, f(n+ 1) > f(n) for all n. Show B = {f(n) | n ∈ N} is recursive.Determine whether the proposed definition isa valid recursive definition of a function f from the setof nonnegative integers to the set of integers. If f is welldefined, find a formula for f(n) when n is a nonnegativeinteger and prove that your formula is valid. f(0) = 1, f(n) = −f(n − 1) for n ≥ 1
- The binomial coefficient C(N,k) can be defined recursively as follows: C(N,0) = 1, C(N,N) = 1, and for 0 < k < N, C(N,k) = C(N-1,k) + C(N - 1,k - 1). Write a function and give an analysis of the running time to compute the binomial coefficients as follows: A. The function is written using dynamic programming.Refine the is_palindrome function to work with arbitrary strings, by ignoring non-letter characters and the distinction between upper- and lowercase letters. For example, if the input string is "Madam, I’m Adam!" then you’d first strip off the last character because it isn’t a letter, and recursively check whether the shorter string "Madam, I’m Adam" is a palindrome. c++Determine whether the proposed definition isa valid recursive definition of a function f from the setof nonnegative integers to the set of integers. If f is welldefined, find a formula for f(n) when n is a nonnegativeinteger and prove that your formula is valid. Do NOT use proofs. f(0) = 1, f(n) = −f(n − 1) for n ≥ 1
- Give a recursive definition for the set of all strings of a’s and b’s that begins with an a and ends in a b. Say, S = { ab, aab, abb, aaab, aabb, abbb, abab..} Let S be the set of all strings of a’s and b’s that begins with a and ends in a b. The recursive definition is as follows – Base:... Recursion: If u ∈ S, then... Restriction: There are no elements of S other than those obtained from the base and recursion of S.For the problems given below, determine whether it is more efficient to use a divide and conquer strategy or a dynamic programming strategy, explain your reason. Give the recursion formula for each. (3*4=12) Find the average of a given set of unsorted numbers. Find whether there is a subset of integers in a given set that adds up to 8 Given a set of numbers, can they set be partitioned into two groups such that the sum of each group is equal; i.e 1,5,11,5 can be partitioned to 1,5,5 and 11Computer Science Let a M be a finite set of messages, and let S(M) denote the set of all permutations of M (all bijective functions f : M → M). We’ll assume that if given a description of σ ∈ S(M), both σ and σ −1 are efficiently computable. Suppose P ⊂ S(M) is such that ∀x, y ∈ M, ∃σ ∈ P such that σ(x) = y. (a) Show that |P| ≥ |M|. (This is easy, but makes sure you’ve parsed the definition.) (b) Show that if |P| = |M|, then the following encryption scheme is perfectly secure, provided you only use it once: 1 Key generation: select a random σ ∈ P; Encryption: m 7→ σ(m) Decryption: c 7→ σ −1 (c) (c) Show that the above is false if |M| < |P| < 2|M|. (d) Observe that for any finite group G and any g ∈ G, the map x 7→ gx is a permutation of G. By viewing G itself as a set of permutations of G in this way, show that the above property is satisfied (with M = P = G). (e) The traditional xor one time pad is a special case of the above. What is the finite group in this case?
- Recursively define the set P of strings (composed of lowercase letters) that have an even number of each vowel (i.e. a word with 2 a's and 4 e's is valid but not 1 a and 5 e's). Use set A to represent all alphabet characters, set V to represent all vowels.Let ∑={a,b} and T be the set of words in ∑* that have no consecutive a’s (i.e. there cannot be 2 or more a’s in a row). (a) Give a recursive definition for the set T. (b) Use your recursive definition to show that the string “abbaba” is in T. (c) Is your recursive definition uniquely determined? Explain why or why not.Please written by computer source Let x be a binary string. The minimal description of x, written d(x), is the shortest string ⟨M, w⟩ where TM M on input w halts with x on its tape. If several such strings exist, select the lexicographically first among them. The descriptive complexity, or Kolmogorov complexity, of x, written K(x), is K(x) = |d(x)|. Show that the function K(x) is not a computable function. HINTS: If K is a computable function, there is some TM which computes it. That TM can be used to find strings of large complexity. Try to design a program which outputs “complex” strings but which contradicts their supposed complexity, and even contradicting the supposed complexity of a single string suffices.











