Overview You will have to download the file input_data.txt from here: input data.txt ↓ You can copy/move it to the same folder as your PyCharms project or use the PyCharms editor to create a new file with the same name and copy/paste the data in. You will define a function called dictionary_maker that will take a path to a file as an argument and return a dictionary representing the data in the file. The file will always be in the key: value format. You will then write code that will ask the user for the name of the data file, send that name to dictionary_maker, and print the dictionary that is returned. Expected Output Example 1 What is the file with the data? input_data.txt {"first name': 'Donkey', 'last name': 'Kong", "height": '8 ft 3 in', 'weight': '1200 pounds'} Example 2 What is the file with the data? garbage.txt The file garbage.txt does not exist on this system {})
Overview You will have to download the file input_data.txt from here: input data.txt ↓ You can copy/move it to the same folder as your PyCharms project or use the PyCharms editor to create a new file with the same name and copy/paste the data in. You will define a function called dictionary_maker that will take a path to a file as an argument and return a dictionary representing the data in the file. The file will always be in the key: value format. You will then write code that will ask the user for the name of the data file, send that name to dictionary_maker, and print the dictionary that is returned. Expected Output Example 1 What is the file with the data? input_data.txt {"first name': 'Donkey', 'last name': 'Kong", "height": '8 ft 3 in', 'weight': '1200 pounds'} Example 2 What is the file with the data? garbage.txt The file garbage.txt does not exist on this system {})
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter7: File Handling And Applications
Section: Chapter Questions
Problem 1GZ
Related questions
Question
input.txt info:
first name: Donkey
last name: Kong
height: 8 ft 3 in
weight: 1200 pounds
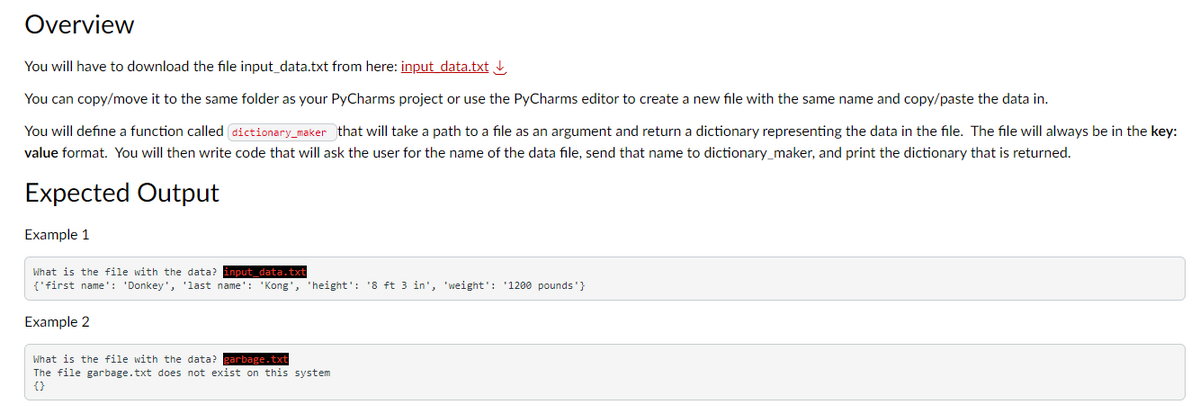
Transcribed Image Text:Overview
You will have to download the file input_data.txt from here: input data.txt
You can copy/move it to the same folder as your PyCharms project or use the PyCharms editor to create a new file with the same name and copy/paste the data in.
You will define a function called dictionary_maker that will take a path to a file as an argument and return a dictionary representing the data in the file. The file will always be in the key:
value format. You will then write code that will ask the user for the name of the data file, send that name to dictionary_maker, and print the dictionary that is returned.
Expected Output
Example 1
What is the file with the data? input_data.txt
{'first name': 'Donkey', 'last name': 'Kong', 'height': '8 ft 3 in', 'weight': '1200 pounds'}
Example 2
What is the file with the data? garbage.txt
The file garbage.txt does not exist on this system
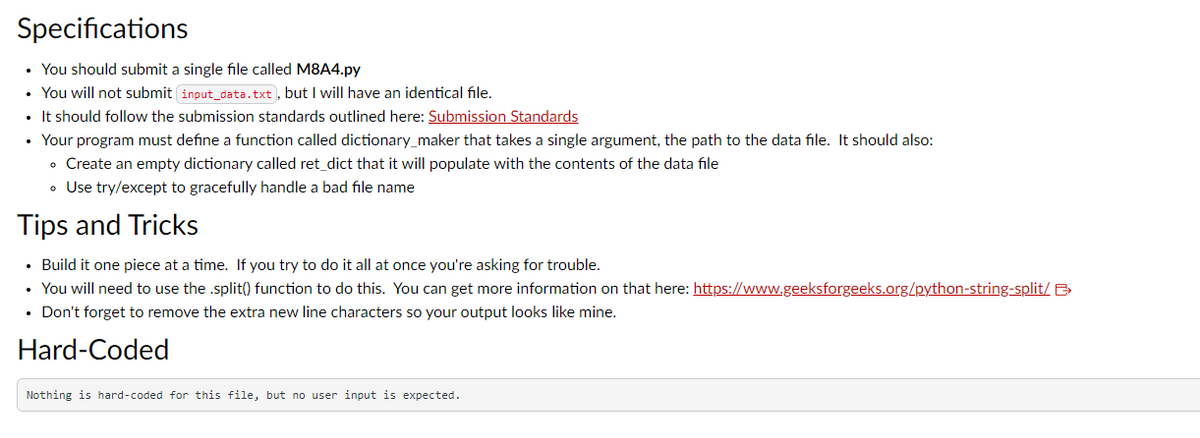
Transcribed Image Text:Specifications
• You should submit a single file called M8A4.py
• You will not submit input_data.txt), but I will have an identical file.
• It should follow the submission standards outlined here: Submission Standards
• Your program must define a function called dictionary_maker that takes a single argument, the path to the data file. It should also:
• Create an empty dictionary called ret_dict that it will populate with the contents of the data file
• Use try/except to gracefully handle a bad file name
Tips and Tricks
• Build it one piece at a time. If you try to do it all at once you're asking for trouble.
• You will need to use the .split() function to do this. You can get more information on that here: https://www.geeksforgeeks.org/python-string-split/ >
• Don't forget to remove the extra new line characters so your output looks like mine.
Hard-Coded
Nothing is hard-coded for this file, but no user input is expected.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage