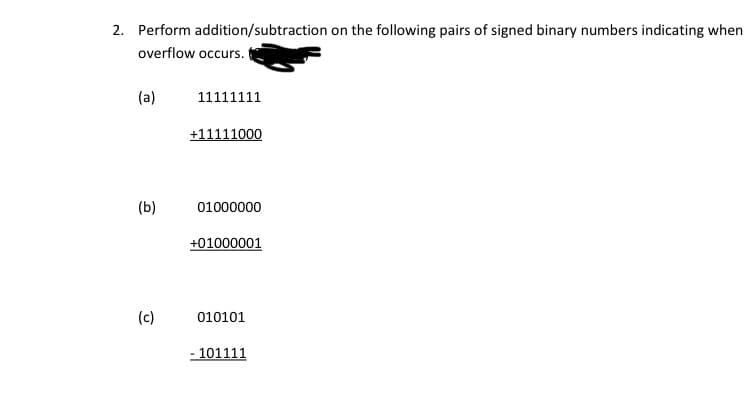
Perform addition/subtraction on the following pairs of signed binary numbers indicating when overflow occurs. (a) 11111111 +11111000 (b) 01000000 +01000001 (c) 010101 - 101111
Q: Name all member functions of all classes visible through temp1 in the main function? Name all member...
A: A class is a blueprint for a certain logic. A class may be parent, child, derived, abstract, virtual...
Q: What is Enumerated Integer providing an example to illustrate your point? Assure uniqueness, qua...
A: The solution to the given problem is below.
Q: TCn)= 8n -27 Ten
A: The Code is : int quiz_5(int array[] ,int n) { int i,count=0,x=array[5]; for(i=5;i<=n;i++) { if(a...
Q: Discuss the various scheduling strategies in terms of (a) waiting time, (b) hunger, (c) turnaround t...
A: The process of determining which process will have exclusive use of the CPU while another is paused ...
Q: Obtain the 5's complement of (543210)Base6?
A:
Q: An error obtained when numbers having limited significant figures are used to represent exact number...
A: The answer is Round off errors. Round off error is an error obtained when numbers having limited sig...
Q: Why is KM such a multidisciplinary area? What challenges does this present?
A: KM is known to be a multidisciplinary field and contributing disciplinary areas are: Management sci...
Q: e CPU is tasked to read data "X" from
A: Access the value stored at a location 0xc7fff and store it in a variable ‘x’ then replace the value ...
Q: What is the next step in the GPO deployment process now that it has been created?
A: Introduction Following are the procedures to deploy a GPO (Group Policy Object) once created.
Q: How can I find out the Wifi security for the type of security: It's possible to use WPA2-enterprise ...
A: According to the question the 10 November 2021 update apply to the windows 10 after this you cannot ...
Q: Make sure you know the difference between fixed and movable slots. W on the architocture of warohouc...
A: Lets see the solution.
Q: Software that runs on the internet is known as web-based application software.
A: Introduction: Web-based application software: As computer hardware has progressed, so has the relat...
Q: Create the following SQL queries, referencing the university schema as a starting point. Find the lo...
A: Introduction: A query is a statement or inquiry regarding a collection of data. We retrieve meaningf...
Q: When it comes to corporate organisations nowadays, what are the most prevalent forms of computer-bas...
A: Throughout decades, computer-based information systems, like the mainframe and its underlying infras...
Q: What do algorithmic "optimal solutions" entail?
A: Algorithm: In normal terms, an algorithm can be defined as a set of rules that need to be followed f...
Q: Explain the phrase "balanced scorecard" in just a few words. What role does it play in the operation...
A: Operation of the Business: The everyday actions of a firm that help it build its worth and earn prof...
Q: int quiz-I Cint n) f int ij, sum = o; for li-2;, i en; i#) {. for Cjpe; je is; j#){ Sum"? sum ?; TG)...
A: Te answer is given below:--
Q: What part does database technology play in an organization's data management?
A: Data management is the process of ingesting, storing, organizing, and maintaining the data created a...
Q: USING PYTHON show the fliw diagram, the code and the output
A: Coded using Python 3.
Q: Write a program that asks the user for a starting value and an ending value and then writes all the ...
A: The while loop in the program iterate through all the values between s and e. The complete program p...
Q: Consider there are 4 stations in the token ring. There is only one packet in the ring. Suppose if th...
A: The given case is of delayed token transmission, where the transmitter or sender is sending the mess...
Q: NIMS has both strengths and weaknesses when it comes to crisis communication. No, I can't think of o...
A: Introduction: NIMS (National Event Management System) is a comprehensive, logical approach to incide...
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Information, consumers, and organizations must be protected against data theft, business disruption,...
Q: When utilizing a logic programming language such as Prolog to tackle computing problems, what are th...
A: Logic programming is a type of programming that is based on logic. This means that a logic programmi...
Q: (i) All comparison based sorting algorithms have the same worst case running time.
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other questions ...
Q: g S and outputs its reverse For example the reverse of ‘pots&pans’ would be ‘snap&stop’ programming...
A: Lets see the solution.
Q: able called Exercise with two fields: Type_of_Exercise and Calories_Burned. How would you calculate ...
A: Lets see the solution.
Q: Is it possible to define the aim of application software?
A: Yes it is possible to to define the aim of application software.
Q: Instructions MovieQuotelnfojava 1 class MovieQuoteInfo { public static void main(String[] args) { //...
A: Here, I have to provide a java solution to the above question.
Q: When was the first time an algorithm was used?
A: According to historical records and archeology, the first visible algorithm was probably created by ...
Q: write c++ program to input a year and to check whether it is a leap year or not
A: The above question that is leap year pogram in c++ is written below
Q: What part does database technology play in an organization's data management?
A: Database technology is used to store the information, organizing the data and also process it. This ...
Q: In healthcare, how can staffing models and labor-optimization algorithms help to efficiency?
A: With the introduction of computer software, major organisations with a high number of people (for ex...
Q: Microsoft Word 2016 has a number of new and improved features. Which feature in Word 2016 do you thi...
A: Here, I have to give an explanation to the above-given question.
Q: Write a function "DivRemain" that will return both the dividend and the remainder from dividing two ...
A: #include <stdio.h> void DivRemain(int one , int two){ int Dividend =0; int Remainder =0;...
Q: Instruction: Identify if the following is UNIQUE IDENTIFIER or NOT. Member ID ID number Name
A: - We need to check if the attributes provided are unique or not.
Q: Which NOS-Network Operating System providers do you know of?
A: Please check the step 2 for solution
Q: How can I find out the Wifi security for the type of security: It's possible to use WPA2-enterprise ...
A: INTRODUCTION: WiFi security is the protection of devices and networks connected in a wireless enviro...
Q: How can I find out the Wifi security for the type of security: It's pos Windows 10 computer when the...
A: Lets see the solution.
Q: 3. Write an algorithm and draw a flow chart to accept the weight and the height. Then calculate the ...
A: BMI ( body mass index ) is a measurement to check if a person is healthy, overweight, or underweight...
Q: What would be the entries on the Truth Table
A: SUMMARY: - Hence, we discussed all the points.
Q: when the statement is executed by the Python interpreter. ...
A: value = 4.6666666667. data type = double. value=1. data type =integer. value=11 data type=i...
Q: What is the operation of SETI?
A: Introduction The Search for Extraterrestrial Intelligence (SETI) is a general abbreviation for the s...
Q: a Cybersecurity expert has determined ICS vulnerability would destroy 50 percent of the process asse...
A: I have answered this question in step 2.
Q: Make a list of three topics covered by the RIM program's aims and objectives.
A: RIM PROGRAM: It stands for record informat...
Q: data science evolving over the next 10 to 20 years. It could be in the fields of healthcare. Start w...
A: The domain of data science is defined as the field that does the analytics, statistics, predictions,...
Q: Assume youre working on a new Word processor With more functionality thán any of your rivals. What i...
A: The most effective methods for intermittent users to remember all of the commands are
Q: What is the RAND Corporation's Report? Why was it created? What was in RAND Report R-609?
A: What is RAND report? RAND reports present research findings and objective analysis that address the ...
Q: True or false? An organization should periodically conduct an inspection of its systems and practice...
A: Hello student, hope you are doing good. This is an objective question and the answer is provided bel...
Q: Discuss the various scheduling strategies in terms of (a) waiting time, (b) hunger, (c) turnaround t...
A: Algorithm for Scheduling There are several scheduling algorithms in use today, and they are used to ...
Step by step
Solved in 2 steps with 5 images

- Carry out the following binary subtraction operators on signed values ( each stored in a single byte) by adding the 2's complement of the subtrahend to the minuend. Indicate if an overflow happens a) 10010100 - 11110000 b) 00010100- 01110000 c) 1010001 - 00000111 d) 00100001 - 10000111 e) 00010100 - 10000111CCTT211 Assignment: 1. Normalize the following binary floating-point numbers. Explicitly show the value of the exponent after normalization.a. 0.1011.1 * 26b. 1101.11 * 2-2 2. Convert the following numbers in 32-bit IEEE format.a. 16.25b. -12.75 3. Convert the following decimal integers to sign-and-magnitude with 8-bit allocationa. 45b. -78 4. One method of representing signed numbers in a computer is one’s complement representation. In this representation, to represent a positive number, we store the binary number. To represent a negative number, we apply the one’s comple- ment operation on the number. Store the following decimal integers to one’s complement with 8-bit allocation.a. 63b. -63 Note: For the problems, follow the instructions and provide the answers in the required format. Show your work and any calculations needed to arrive at the final answer.To express the decimal number 30 as an 8-bit binary number, try the following: complement a) the antonym; complement b) Excess-M;?
- Add the following twos complement binary numbers of 8 bits and also express the answer in decimal. Identify each case in which the answer is incorrect because of overflow. 00001111 + 10011001 11111000 + 111011118) Obtain the 1’s and 2’s complements of the following binary numbers correctly:(a) 10010000(b) 00000000(c) 11011010(d) 10101010(e) 10100101(f) 11111111 9) Convert decimal +49 and +29 to binary, using the signed-2’s-complementrepresentation and enough digits to accommodate the numbers. Thenperform the binary equivalent of (+29) + (-49), (-29) + (+49), and (-29) + (-49). Convert the answers back to decimal and verify that they are correct.1. Suppose we use six bits to represent a two’s complement binary number. Perform thefollowing subtractions, indicating when overflow occurs:(a) 010101 (b) 100000 (c) 010101 (d) 100110- 001101 - 110011 - 101111 - 11111131
- What are the 16-bit 1’s and 2’s complements of the following binarynumbers? c. 0100111000100100We can perform logical operations on strings of bits by considering each pair of corresponding bits separately (called bitwise operation). Given two eight-bit strings A = 10110001 and B = 10101100 , evaluate the eight-bit result after the following logical operations: OR1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?

