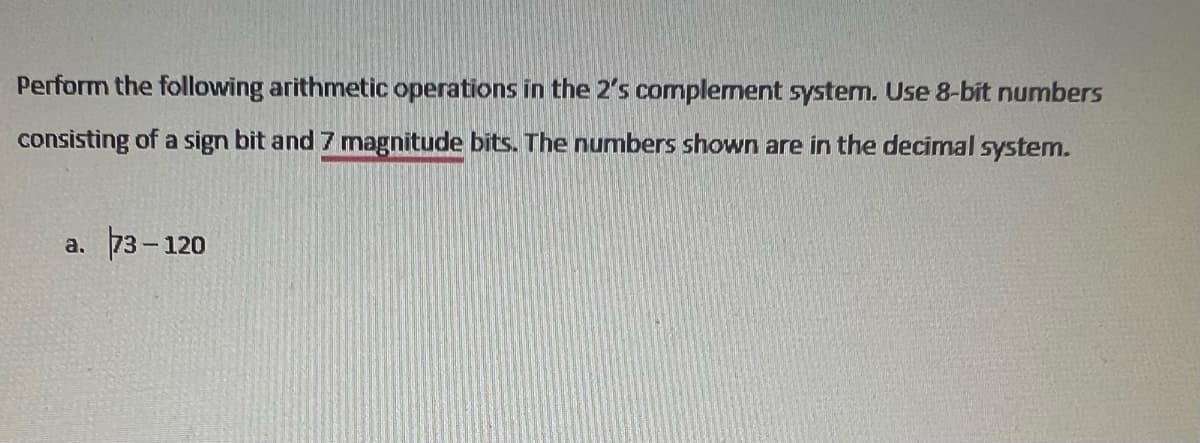
Perform the following arithmetic operations in the 2's complement system. Use 8-bit numbers consisting of a sign bit and 7 magnitude bits. The numbers shown are in the decimal system. a. 73-120
Q: Explain the architechure of a Servlet.
A: The question has been answered in step2
Q: 1. Use the bubble sort to sort 6, 2, 3, 1, 5, 4, showing the lists obtained at each step. Justify…
A: Given To know about the bubble sort .
Q: Explain what is the architecture of servlet.
A: Servlets are programs that run on the web or application server and act as the middle layer between…
Q: asymptotic estimate, using the e-notation.
A: Given :- In the above given question , the statement is mention in the above given question Need…
Q: ackage edu.umsl; interface Jumpman { void jump(); default void swingHammer() { // Code to swing…
A: The answer is given below.
Q: An explanation of how businesses use cloud computing to manage their available resources is followed…
A: Utilizing the Cloud It is defined as a distributed network for the simultaneous sharing and use of…
Q: How can one learn about mice in a variety of settings? What is the precise sequence of events? So as…
A: At this time, it's important to evaluate the mouse's resources: The mouse contains a chip inside…
Q: Tell us what you think about whether or not social media platforms like Facebook should provide law…
A: Facebook: College administrations and law enforcement agencies utilise Facebook, a social networking…
Q: State the functions of instruction register and instruction decoder.
A: Introduction: 3 Instruction Register and Decoder. To execute an instruction, the processor copies…
Q: What are the steps involved to make work a RMI program ?
A: Introduction Remote method invocation (RMI) allows a Java object to call a method on another…
Q: Why is combating cybercrime so important?
A: Given: The importance of data and information in today's environment has led to an increase in…
Q: Define Subroutine.
A: The question has been answered in step2
Q: There may have bugs from line 1 to 10. Please find bugs and change it or remove if the line has to…
A: Explanation: 1. open() takes in two parameters, the first being the file to be opened, and the…
Q: What does Connection pooling mean?
A:
Q: Explain what is the architecture of servlet.
A: In this question we need to explain the architecture of servlet in Java programming language.
Q: Do you believe it's fair for app makers to require you to provide your personal data before using…
A: Introduction: The software enables us to use computers for a variety of tasks. Unfortunately, some…
Q: (1) Prompt the user to enter a string of their choosing. Store the text in a string. Output the…
A: Since there are multiple subparts, the first three subparts are answered for you. If you want the…
Q: Our hash map wasn't made very well because all the data were thrown into one bucket. If so, describe…
A: Introduction: The Hash tables are collections of sorted things that make it possible to find them…
Q: implement java program to reads the URLs from this file and dissects them to show the various parts…
A: java program to reads the URLs from this file and dissects them to show the various parts of the…
Q: Write an application to test the HuffmanTree class. Your application will need to read a text file…
A: The answer provided below has been developed in a clear step by step manner.
Q: make a Algorithm to Expectiminimax using alpha-beta pruning and fail-soft enhancement.
A: introduction: Alpha–beta pruning is a search algorithm that seeks to decrease the number of nodes…
Q: In our inferior hash map, each value is contained in a single container. A hash map has successfully…
A: Introduction: Hash tables are collections of objects sorted in a way that makes it easy to find what…
Q: Solve In Python Provide Screenshots of Input and Ouput For this lab, you will modify your Lab 7 to…
A: Solution: Required language is python- Detailed solution from step-2
Q: How many different technological techniques are there for detecting network intrusions?
A: Introduction: Intrusion: Any illicit and unauthorized computer activity is referred to as intrusion.
Q: What is the use of PC register?
A:
Q: Please give a brief overview of memory addressing and explain why it is so vitally important.
A: Memory addressing A device or CPU uses a memory address as a specific identifier to track data. The…
Q: Think about how important wireless networks are in the still-developing nations of today. In a…
A: INTRODUCTION: Wireless networks: Wireless networking is a method that homes, telecommunications…
Q: capCount.py make a program called capCount.py that has a function that takes in a string and…
A: The complete python code is below:
Q: What are the steps involved to make work a RMI program ?
A: The question has been answered in step2
Q: What is the basic principle of RMI architecture ?
A:
Q: Load the JSON file below into Python as a dictionary; convert to a list and calculate the minimum…
A: ANSWER:-
Q: what is Leafleting
A: Leafleting Today we will define what a leaflet is. We'll describe its purpose as well as the…
Q: There are many advantages to using software that is hosted in the cloud as opposed to a…
A: Cloud storage is a service where data is remotely maintained, managed, and backup. The service…
Q: Wap shows the ComparatorDemo class, which populates an array of Student objects and then calls…
A: program is given in net step:
Q: An explanation of how businesses use cloud computing to manage their available resources is followed…
A: Introduction For small and medium-sized businesses, cloud computing has emerged as one of the more…
Q: Define timing parameters: tWR, tWC, tCO, tRD, tRC.
A:
Q: 2) Write a function named "number_square". The function should accept an argument and display the…
A: As no language is mentioned so I provide the code in python as well as in java. You can refer…
Q: Define - Moore's Law
A:
Q: Use the arrays below, X and w Calculate the dot product of X and w. Put the outcome inside the…
A: The following are steps that need to be taken for the given program: The NumPy library function…
Q: What is the role of stub in RMI ?
A:
Q: 14.28. Consider the relation R, which has attributes that hold schedules of courses and sections at…
A: Introduction Normalization: Data duplication could occur in a large database defined as a single…
Q: Rebuttal DEBATE TOPIC LESS MAY BE MORE! Too much Information Technology (IT) sophistication within…
A: Answer: We have explain what are the component to make the quality of services from the ethical and…
Q: Compare and contrast the significance of mobile and cloud computing. The usage of cloud computing…
A: Introduction: The mobile phone has progressed at a dizzying pace in recent years. From a device…
Q: Please read. It's Java. Write a client program and server program. The server uses a socket…
A: Step 1 Server Class /* package codechef; // don't place package name! */ import java.io.*; import…
Q: Look at the solutions individuals come up with to the problems you've observed them having with…
A: introduction: Contexts in which users take action in response to software problems People get…
Q: 10. Using the INDEX function only, write a formula in cell H10 to find the state name having the…
A: We need to write the formula in cell H10 to find the state name having the minimum "Sum of…
Q: Websites not only give us information, but they also inspire designers in their layouts,…
A: Explanation: Post the link to the webpage you're using for this activity, followed by your…
Q: Define what is a program Counter.
A:
Q: Question 10 Calculate the binary numbers: (a) 111+101+100 (b) 11101+10011+110111 a. b. - Check Check
A: We are asked to calculate the given binary numbers. Binary numbers are base 2 numbers and valid…
Q: How many elements are in the stack after the following code executes? (The stack is initially…
A: Introduction: In this question, we are asked to print the size of the final stack after executing…
Step by step
Solved in 2 steps with 1 images

- A(n) __________ is an integer stored in double the normal number of bit positions.A(n) _____ operation transforms a 0 bit value to 1 and a 1 bit value to 0.Data represented in ________ is transmitted accurately between computer equipment from different manufacturers if each computer’s CPU represents real numbers by using an IEEE standard notation.
- Perform the following arithmetic operations in the 2’s complement system. Use 8-bit numbers consisting of a sign bit and 7 magnitude bits. The numbers shown are in the decimal system.Perform the following arithmetic operations in the 2’s complement system. Use 8-bit numbers consisting of a sign bit and 7 magnitude bits. The numbers shown are in the decimal system. 37 + 25 85 + 40 95 – 63Assume numbers are represented in 8-bit twos complement representation. Show your solution in the following: 6 + 13 -6 + 13 6- 13 -6-13
- Perform the following operations involving four-bit 2’s complement numbers and indicate whether arithmetic overflow occurs. Verify your answers by converting to decimal sign-magnitude representation. (Convert to decimal number to verofy the answers).Show your work Using 7 bits to represent each number, write the representations of 23 and -23 in signed magnitude, 1’s complement and 2's complement integers.Using binary numbers of 8 bits each, convert to binary and solve the following arithmetic operations using two’s complement representation: (13)10 - (25)10 -(13)10 - (18)10
- Consider the following addition problems. Please first convert each decimal number into eight-bit twos-complement notation, perform the addition in twos-complement notation, then convert the results back to decimal numbers. Identify each case in which the answer is incorrect because of overflow. 23+45 23-45 -23-45 200+100Perform the arithmetic operations (36)10+(-41)10 and (-1F)16(-2D)16 in .A binary using 12-bit signed-2's complement representation for negative numbers. Convert the answers back to decimal and verify that they are correct Convert the decimal number to single precision IEEE 754 floating-point .B .representation. Show all your work1. Represent the following decimal numbers in 8 bits: (+94)10 and (–124)10 by (a) Sign-magnitude, (b) one’s complement, and (c) two’s complement representation 2. Express the following decimal numbers in Excess-3 code form: 24510, 73910, and 456710. 3. Express the following Excess-3 codes as decimals: 1000001101102 and 01111100100101102.

