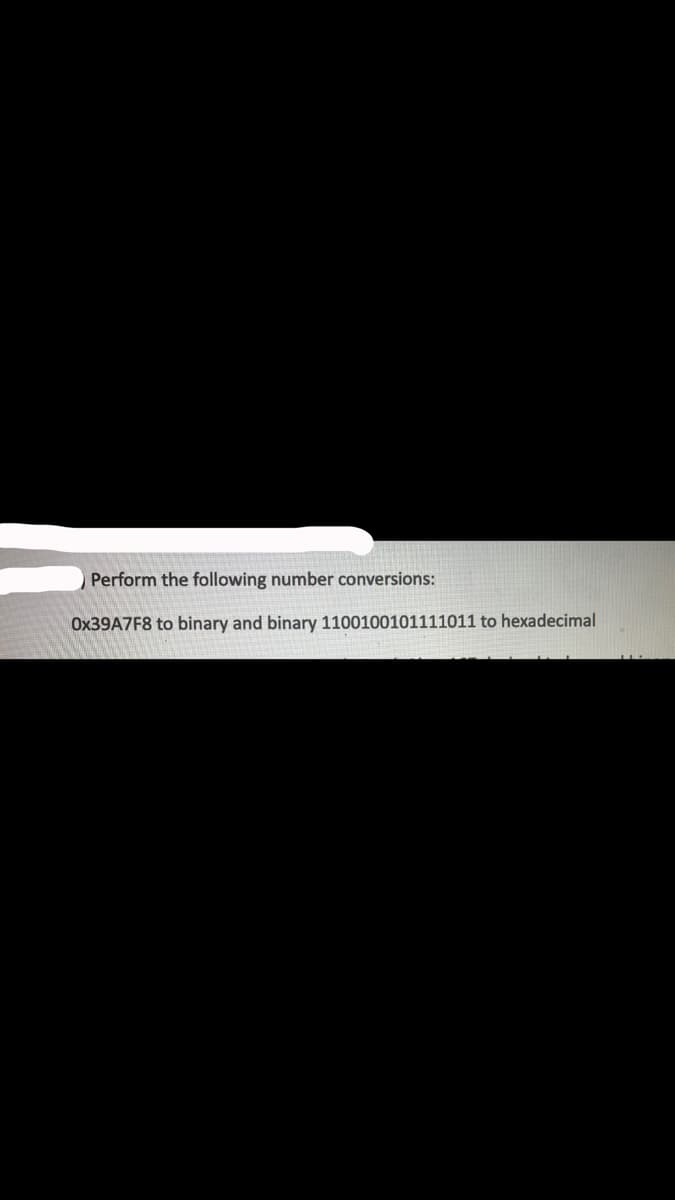
Perform the following number conversions: Ox39A7F8 to binary and binary 1100100101111011 to hexadecimal
Q: Why is encapsulation necessary in object-oriented development?
A: Encapsulation is a essential idea in Object-Oriented Programming (OOP). It refers to bundle related…
Q: What changes have been made to the technology that underpins each new generation of networking…
A: What is networking equipment: Networking equipment refers to the hardware devices and software…
Q: As you build the framework, consider the issues and problems you'll encounter with each solution.…
A: Given,As you build the framework, consider the issues and problems you'll encounter with each…
Q: Suppose you are creating a database for a library management system. Explain how you would create a…
A: create a database for a library management system.…
Q: How do the six DBLC stages affect the data dictionary?
A: The Database Life Cycle (DBLC) consists of six stages: Database planning, Database design, Database…
Q: How can one evaluate an ArrayList?
A: ArrayLists are a popular data structure in programming that provide dynamic and resizable arrays.…
Q: Please define "authentication challenge-response system" and provide examples. How is this approach…
A: A challenge-response authentication system is a type of authentication system in which the user is…
Q: Which aggregating operations are allowed for struct variables but not array variables, and which are…
A: In many programming languages, including C and C++, structs and arrays are both used to store…
Q: Summarise the top three virtualization software packages. Comparison is crucial.
A: 1. VMware Workstation: Foremost virtualization software wraps up, VMware Workstation is famous for…
Q: Linux rocketry apps.
A: According to the information given:-We have to define Linux rocketry apps.
Q: See how well the different security techniques handle the numerous security challenges.
A: Indeed, information technology and the Internet have simplified our lives. On the other hand, they…
Q: OS Questions: How might big-endian/little-endian CPU designs increase inter-process communication?…
A: What is computer architecture: Computer architecture refers to the design and organization of a…
Q: Which factors are most important to think about while developing a mobile app? What do you think…
A: The user experience is at the forefront of successful mobile applications. The application needs to…
Q: Include operating system services and their three user-reach channels.
A: Operating systems play a crucial role in managing computer hardware and software resources,…
Q: How does OLAP work?
A: OLAP, which stands for Online Analytical Processing, is a technology used for analyzing and…
Q: Why wouldn't email providers monitor client messages?
A: Email is used to send a lot of private, confidential, and professional information. Thus it ought to…
Q: Why is encapsulation necessary in object-oriented development?
A: Encapsulation is necessary in object-oriented development for data protection, modularity, code…
Q: Document hashing. Hash tables, collision detection, and temporal complexity. Hashing app. Any native…
A: What is hashing: Hashing is the process of converting data of arbitrary size into a fixed-length…
Q: While Modernizr adds a number of capabilities that browsers lack, it does not offer support for…
A: Modernizr is a JavaScript records that checks for hold up for advanced web technology, such as those…
Q: GSM networks' HLR and VLR serve what purposes? What attributes of mobile IP are like HLR and VLR?
A: In GSM (Global System for Mobile Communications) networks, the HLR (Home Location Register) and VLR…
Q: You shouldn't trust databases with private information. How frequently and do you have the right to…
A: The issue at hand deals with the importance of data privacy and the necessity to question the…
Q: Why do we need device drivers if the BIOS already lets the operating system talk to the hardware?
A: The BIOS (Basic Input/Output System) is firmware installed on a PC's motherboard. It is liable for…
Q: Which firewall architecture should a modern organisation use? Why? Explain.
A: Cloud technology is a prototype for delivering computing assets over the internet, such as servers,…
Q: Multiple users may access PC local administrative settings. Some users change security rules without…
A: In a shared computer environment where multiple users have local administrative access, unauthorized…
Q: Most popular server-side web programming language?
A: Server-side scripting is the code base that is kept on a remote server and is used to handle client…
Q: PointSource used IBM rational test workbench to construct the FIMC app. This technology allowed…
A: IBM Rational Test Workbench is a powerful technology that aids in the construction and testing of…
Q: Explain I/O. Explain how input and output devices work, including what they send and receive, what…
A: What is input and output devices: Input and output devices are components used in the interaction…
Q: Why do system developers need ISO?
A: ISO (International Organization for Standardization) is an international standard-setting body…
Q: Give six PLD programmable connection process technologies.
A: An electronic component that can be customized or programmed to carry out particular logic…
Q: Multiprocessor systems provide adaptability. Though advantageous, this feature increases system…
A: Systems with a lot of processors, from time to time called parallel computer or equivalent…
Q: Data dictionary: which DBLC phase?
A: The data dictionary is associated with multiple phases of the Database Life Cycle (DBLC), including…
Q: There are still a lot of unknowns about operating systems and how they do what they are supposed to…
A: What is an OS: An operating system (OS) is software that acts as an intermediary between computer…
Q: We must test a prototype to determine the mobile app's user interface design for will 4 live. User…
A: What is test a prototype: Testing a prototype involves evaluating its functionality, usability, and…
Q: What long-term planning may produce legacy systems? When
A: Long-term planning plays a crucial role in the development of systems and technologies, especially…
Q: Explain why object-oriented programming relies on encapsulation.
A: Encapsulation is a fundamental concept in object-oriented programming (OOP).
Q: Is cloud-based collaboration technology deployable in various settings? How can cloud collaboration…
A: Cloud-based collaboration technology refers to the use of cloud computing platforms and tools to…
Q: Your top three database administrator duties? Which LAN maintenance methods are best?
A: Top Three Database Administrator Duties: Database administrators are…
Q: Please compare and contrast the key memory limits of mobile devices and desktop PCs in your own…
A: Due to a number of factors, mobile devices primary memory is less than that of desktop computers.…
Q: Please explain the three types of local bank servers.
A: Local bank servers are critical components of a bank's infrastructure, facilitating various…
Q: Explain I/O. Explain how input and output devices work, including what they send and receive, what…
A: In computer science, Input/Output (I/O) refers to the communication between a computer system and…
Q: How unpredictable is PLD process technology price, and which PLDs are more variable?
A: The price of Programmable Logic Device (PLD) process technology can be somewhat unpredictable due to…
Q: LCD computer displays cannot have curved panels due to their technology.
A: Liquid Crystal Display (LCD) knowledge leverages the property of water crystals, which can modify…
Q: FTP port numbers are important. How did you come to the conclusion that FTP sends control data "out…
A: FTP is a standard network protocol that transfers computer files between a client and server on a…
Q: Which is the biggest difference between analytics and business intelligence?
A: The biggest difference between analytics and business intelligence is the focus of the analysis.…
Q: Cloud-hosted networks provide several benefits over on-premises ones.
A: Cloud-hosted Networks versus On-Premises NetworksCloud-hosted networks and on-premises networks…
Q: One must explain a variable's other traits before explaining it. Each variable has a data type and…
A: Variables are essential for storing and manipulating data in programming. A…
Q: Email providers that read client communications risk major penalties.
A: What is Email providers: Email providers are companies or organizations that offer email services to…
Q: Simulate in R the delta variation by SIR model. - Produce the code in R
A: Please check out the coding below
Q: 4.) Suppose that a sender and a receiver are using ARQ to perform reliable data delivery. If we…
A: GivenSuppose that a sender and a receiver are using ARQ to perform reliable data delivery. If we…
Q: BI implementation issues?
A: Implementing Business Intelligence (BI) systems is a complex undertaking that organizations face in…
Step by step
Solved in 4 steps

- Perform the following binary sums:a) 1101+1010b) 10111+01101Perform the following binary subtractions:a)1101-0100b)1001-0111Perform the following binary divisions, assuming unsignedintegers:1. a) 11111101 ÷ 10112. b) 110010101 ÷ 10013. c) 1001111100 ÷ 1100Convert each of the following hexadecimal values to binary.a) ABCD16 b) 1DEF16 c) 864516 d) 925A16
- Convert each of the following hexadecimal values to binary. i) AB1916 ii) 2DEF16 iii) 8A4516 iv) 9B5A16Convert decimal 123456 to binary, octal, and hexadecimal. Convert hex 0xffff tobinary, octal, and decimal.Convert the following decimal fractions to binary with a maximum of six places to the right of the binary point (show the steps): a) 34.79125, b) 219.01225, c) 170.786765, d) 16.1120244375
- Convert the following Hexa value (ABC)16 to Binary a. 101010111101 b. 101010111110 c. 101010111111 d. 101010111100Add the following unsigned binary numbers as shown. 01110101+00111011Multiply 166 by 105 using unsigned 8-bit binary multiplication to form a 16-bit result. Select the correct result here. a. 0100010000010110 b. 1100010000010110 c. 1011101111101001 d. 0011101111101001
- Perform the following operations on 8-bit unsigned numbers and indicate possible overflow 10110100 – 01101001= 01001011 00111000 + 11011101= 0100010101 10001011 + 01110101= 100000000 01110100 – 10001111= -011011Convert the following binary numbers to hexadecimal a) 11110000 b) 11111111 c) 01011010 d) 1001101101101Convert from binary to hexadecimal. 1. 1010 1011 in binary is _______ in hexadecimal 2. 101101 in binary is _______ in hexadecimal.

