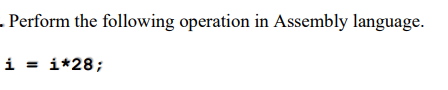
Perform the following operation in Assembly language. i = i*28;
Q: What strategic competitive advantages do you perceive in extranet use?
A: Introduction: Obtaining a competitive advantage is critical to success in today's global market. If…
Q: Not one of the following advantages of optimised bubble sort above other sorts for sorted elements.…
A: Answer c) Checks for input sorting
Q: What is the OWASP Zed Attack Proxy (ZAP) (formerly called WebScarab)? How does it fit into security…
A: OWASP( ZAP) is basically a security scanner and it is an open source application . This web…
Q: Topic: Assembly Language What will be the value of Auxillary Flag, Carry Flag, Parity Flag and Sign…
A:
Q: What element in the IP header can be used to ensure that a packet is forwarded through a maximum of…
A: Introduction: The header includes details such as IP version, source IP address, destination IP…
Q: Is there a computer hardware component in a personal computer that is absolutely necessary?
A: Introduction The physical components that a computer system requires to function are known as…
Q: What are the four different types of E-R diagrams that are created and analyzed during conceptual…
A: Introduction: Entity Relationship Diagram - (ER Diagram), also known as Entity Relationship Diagram…
Q: Fill in the gap to complete the code so that the program produces the expected output. Expected…
A: The solution to the given problem is below.
Q: Explain the significance of the Software Requirement Specification Document and the components of…
A: - We have to talk about the use and parts of SRS.
Q: Which Windows Server 2012 versions support a Server Core installation?
A: Introduction In Windows Server 2012 you can choose between a Server Core and Server with a GUI…
Q: What are the advantages and disadvantages of fiber-to-the-premises or fiber-to- the-business…
A: What is Fiber to the premises: With just a single laser, billions of bits per second can be…
Q: HOW TO KNOW IF MY INPUT/ STUDENT ID IS VERIFIED AND NOT VERIFIED, IF NOT, ASK THE USER AGAIN TO…
A: Modified code: student_213 = {} # dictionary of student information print…
Q: What are the computer hardware types?
A: Different types of computer hardware
Q: A computer's hardware is what makes it run.
A: Intro A computer's hardware is what makes it run.
Q: b. Suppose you are gifted a collection of 3" pokéballs; all of the the pokéballs have the same size…
A:
Q: Hardware is the phrase used to describe all of the input and output devices in a computer system.…
A: Hardware Fundamentals: Hardware: Hardware refers to all physical components or sections of a…
Q: How long ago was the first pocket calculator made?
A: Introduction
Q: To test a group of functions, we need to design test cases. The early document can help testers…
A: Introduction: Security testing gives a repeatable framework when using a recognized security testing…
Q: What are some of the reasons why website hacking is a problem?
A: The solution is as follows: There are many reasons why hacking a website is a concern.Because of a…
Q: When should a company use PaaS and when should they consider IaaS, according to you? Why?
A: Introduction: Platform as a Service (PaaS) enables software programmes to use cloud services. It…
Q: (a) Write a program to dynamically allocate memory to a one-dimensional array and find the second…
A: Dynamically allocate memory to a one-dimensional array to find the second largest element from the…
Q: Identify and differentiate the two basic storage device kinds.
A: 1) A storage device is a part of the computer system which is used to store the information and…
Q: Examine the many types of wireless LAN technology.
A: Introduction Types of Wireless Networks WLANs: Wireless Local Area Networks WLANs allow users in a…
Q: It is also known as a hub, repeater, firewall, T-connector, or bridge, depending on its function.
A: Introduction: Generally speaking, network devices are pieces of hardware that allow for the…
Q: One of the problems with computer security is that it is typically added after the fact rather than…
A: Introduction: Computer security, cybersecurity, or information technology security (IT security) is…
Q: Write a C program that inputs number of rows in a class room (r) and number of seats in the row (rs)…
A: Q: Program the given in C language
Q: What is the meaning and function of the central processing unit (CPU)? Explain YOUC point of view!
A: Introduction: The central processing unit (CPU) directs the computer's execution of the many…
Q: What are the best practices for lowering the energy usage of computer devices?
A: Please find the detailed answer in the following steps.
Q: Which memory type is utilized for primary storage?
A: Introduction: Here we are required to explain which memory type is utilized for primary storage.
Q: What is programming? Considerations in choosing a programming language
A: Programming is the process of performing a particular computation, usually by designing/building an…
Q: Discuss five security best practices for online applications.
A: Introduction: When it comes to business stack security, software applications are the weakest link.…
Q: What are the best practices for lowering the energy usage of computer devices?
A: Power is the food by which a computer system runs. To make a computer system power we can take many…
Q: Explain why encrypting the passwords on the router is necessary, and write down the relevant command…
A: Introduction: Encryption scrambles your password so that hackers can't read it or use it. That easy…
Q: * write a C program that inputs the old salary (os) and the new salary (ns) of an employee. Then it…
A: The flowchart is a diagram in which we represent the problem solution in a pictorial way by using…
Q: What effect does "Race Condition" have on a computer's operating system?
A: An Operating System is an interface between a computer user and computer hardware.
Q: Write a program to Calculate the sum of the given integers using while loop in C programming.
A: Write a program to Calculate the sum of the given integers using while loop in C programming.…
Q: What is server load balancing? What exactly is Link Efficiency, and how does it impact performance?
A: Find the answer given as below :
Q: Compare and contrast APIPA and DHCP in a few sentences.
A: APIPA and DHCP these two are network protocols.
Q: What is the meaning and function of the central processing unit (CPU)? Explain your point of view!
A: Introduction: We must describe the significance and function of the CPU in response to the query.…
Q: What element in the IP header can be used to ensure that a packet is forwarded through a maximum of…
A: INTRODUCTION: Field of time to live The time to live (TTL) is often referred to as the hop limit; it…
Q: When it comes to communication, what is the protocol?
A: The answer of this question is as follows:
Q: Software modelling and software development are two separate processes. Explain how each employee…
A: Introduction: The Methodology of a Software Development
Q: Discuss five security best practices for online applications.
A: Introduction: It is software programmes that are the weakest link in its security stack. According…
Q: Which computer architecture is often utilised in Smartphones? Give explanations.
A: Intro iOS, Android, Windows Phone, Windows RT, Bada, Blackberry OS/Blackberry 10; MeeGo; Firefox OS;…
Q: Explain how MIMO performs two key functions: spatial multiplexing and beamforming.
A: Intro Spatial multiplexing It is the multiplexing function performed by MIMO wireless communication.…
Q: A computer has two parts: the brain and the body.
A: - We have to talk about the two parts of computer in reference to the brain and body.
Q: What are the (correct minus wrong) results of the UP exercise "Design a subsystem": [Complete]…
A: Introduction: Subsystems can be used in various complementary ways, including partitioning the…
Q: Unsolicited commercial mass emailing systems are commonly referred to as spam. Some critics argue…
A: Introduction: There are five features of the emails that cause recipients to label them as "spam."…
Q: Multi-user multitasking is a term that refers to the ability for multiple users to work at the same…
A: Introduction: An operating system (OS) is a type of system software that is used to manage computer…
Q: What is the significance of cybercrime, and what is the literature review on it?
A: Introduction: Cybercrime law establishes rules of conduct and standards of behaviour for the use of…
Step by step
Solved in 2 steps

- In a C++ program, preprocessor directives begin with which symbol? (8)dont use others answers will rate! Thank you! Translate each of the following java statements into MIPS assembly language:Assume the following are given for each: a=$t0, b=$t1, c=$t2, d=$t3 11. d = a – b / c;solve in assembley language, MIPS Write an interactive program that inputs the coefficient of a quadratic equation, computes, anddisplays the roots of the quadratic equation. All input, computation, and output should be doneusing double-precision floating-point instructions and registers. The program should handle thecase of complex roots and displays the results properly
- JAVA and Netbeans Using Looping Statement, Create a simple Multiplication Table for user input number (same as below):Write the machine code version of the following assembly language program.dont use others answers will rate! Thank you! Translate each of the following java statements into MIPS assembly language:Assume the following are given for each: a=$t0, b=$t1, c=$t2, d=$t3 12. c = (a + 5) % b;
- Solve arithmetic expressions in MIPS assemblyUsing the MIPS arithmetic operations covered so far, a program can be created to solve equations. For example the following pseudo code program, where the user is prompted for anvalue of x and the program prints out the results of the equation 5x2 + 2x + 3.main{ int x = prompt("Enter a value for x: "); int y = 5 * x * x + 2 * x + 3; print("The result is: " + y);}Write the following statement in C, in Assembly language unsigned char i, j, m; if (i || j) { m = j - i; } // … rest of code … Answer:dont use others answers will rate! Thank you! Translate each of the following java statements into MIPS assembly language:Assume the following are given for each: a=$t0, b=$t1, c=$t2, d=$t3 8. b *= 15;
- Do not copy from other websites. Q. What are the design issues for logically controlled loop statements?dont use others answers will rate! Thank you! Translate each of the following java statements into MIPS assembly language:Assume the following are given for each: a=$t0, b=$t1, c=$t2, d=$t3 9. a = b * 4; (use addition)C++ Define a problem with user input, user output, Pointers, and Pointer Arithmetic. If no output explain the reason why and what you are going to do make sure it does not happen again aka learning from your mistakes.Problem:Design:Code:Output:



